Introduction
In today’s digital age, cybersecurity plays a crucial role in protecting our sensitive information from malicious actors. As technology continues to advance, so too does the sophistication of cyber threats. One concept that has gained significant attention in the realm of cybersecurity is Tactics, Techniques, and Procedures, commonly referred to as TTP.
TTP encompasses the strategies and methods employed by cyber attackers to gain unauthorized access, steal data, disrupt systems, or engage in other malicious activities. Understanding TTP is essential for cybersecurity professionals as it allows them to detect, prevent, and mitigate cyber threats effectively.
In this article, we will explore the concept of TTP in cybersecurity, its three main components, and the framework used to analyze and respond to TTP-based attacks. Additionally, we will examine common TTPs employed by cybercriminals and discuss techniques for detecting and preventing them.
By gaining a comprehensive understanding of TTP, both cybersecurity experts and individuals can enhance their knowledge and awareness, thus contributing to a safer digital environment. So, let us delve into the world of TTP in cybersecurity and discover the key insights that will help us better protect our data and systems.
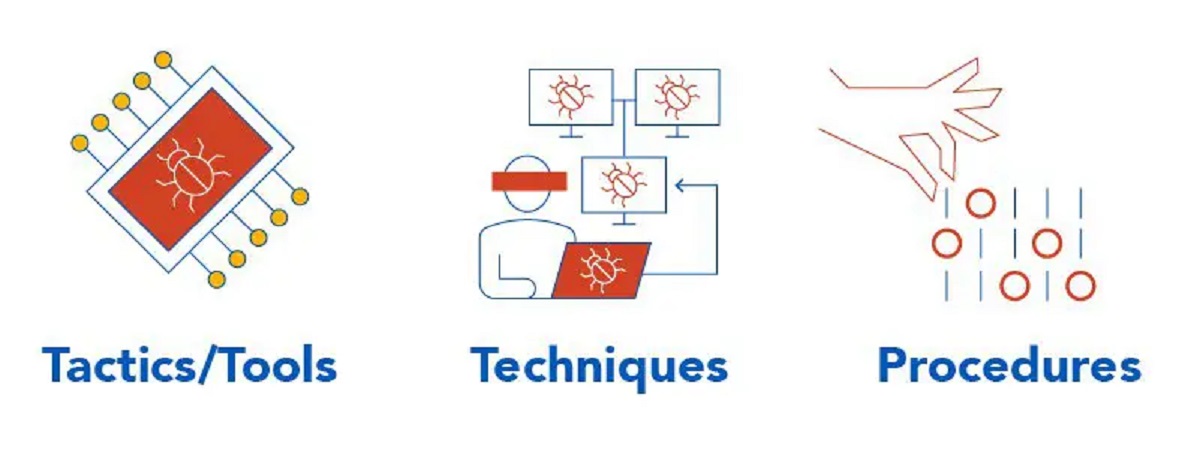
Definition of TTP in Cybersecurity
Tactics, Techniques, and Procedures (TTP) is a term commonly used in cybersecurity to describe the various strategies, methods, and operational processes employed by cyber attackers. TTP encompasses the entire life cycle of a cyber attack, from the planning and reconnaissance stages to the actual execution and exploitation.
Tactics refer to the high-level goals and objectives that attackers aim to achieve during an attack. These goals can range from gaining unauthorized access to a system, exfiltrating sensitive data, disrupting services, or deploying malware to compromise targeted networks. Understanding the tactics employed by attackers helps security professionals identify the overall objective of an attack and devise effective countermeasures.
Techniques, on the other hand, are the specific methods and procedures that cybercriminals use to carry out their attacks. These can include exploiting vulnerabilities in software systems, utilizing social engineering tactics to trick unsuspecting users, employing sophisticated malware or ransomware, or using techniques like phishing or spear phishing to gain access to sensitive information.
Procedures, the final component of TTP, refer to the step-by-step processes and sequences followed by attackers in executing their attacks. It includes the tools and resources they employ, the infrastructure they leverage, and the order in which actions are taken. Understanding these procedures helps cybersecurity professionals identify patterns, indicators of compromise, and potential vulnerabilities within their systems.
TTP serves as a framework for analyzing and responding to cyber threats. By understanding the tactics, techniques, and procedures utilized by attackers, security teams can enhance their incident response capabilities, improve threat detection systems, and effectively mitigate attacks.
In the following sections, we will explore the three components of TTP in detail, examine common TTPs used by cybercriminals, and discuss techniques for detecting and preventing them. By gaining a comprehensive understanding of TTP, organizations can bolster their cybersecurity defenses and minimize the risk of falling victim to cyber attacks.
The Three Components of TTP
TTP is composed of three main components: tactics, techniques, and procedures. Each component plays a crucial role in understanding and countering cyber threats effectively.
1. Tactics: Tactics refer to the overarching goals and objectives of an attacker. Understanding the tactics employed by cybercriminals helps security professionals identify the motive behind an attack and anticipate the potential consequences. For example, an attacker’s tactics may involve infiltrating a network to steal confidential data, disrupting critical services to cause financial loss, or exploiting vulnerabilities in a system to gain unauthorized access. By understanding the tactics, organizations can develop targeted defense strategies to mitigate these threats.
2. Techniques: Techniques encompass the specific methods and procedures utilized by attackers to achieve their tactics. These techniques can vary widely depending on the attacker’s skill level, resources, and objectives. Examples of common techniques include SQL injection, phishing, social engineering, malware propagation, and denial-of-service attacks. Cybercriminals continually evolve their techniques to exploit new vulnerabilities and evade detection. Security professionals must stay up-to-date on emerging techniques and leverage effective security measures to counteract them.
3. Procedures: Procedures outline the step-by-step processes and sequences followed by attackers during an attack. This includes the tools, resources, and infrastructure they employ, as well as the order in which actions are taken. Understanding the procedures used by attackers provides valuable insights into their methodologies, allowing security teams to detect patterns and indicators of compromise. By analyzing these procedures, organizations can identify vulnerabilities in their systems, strengthen their defense mechanisms, and respond more effectively to cyber threats.
By studying the tactics, techniques, and procedures employed by attackers, security professionals gain a holistic understanding of the threat landscape. This knowledge enables proactive threat hunting, the identification of potential vulnerabilities, and the development of robust defense strategies. By implementing comprehensive security measures, organizations can better safeguard their valuable data, protect their systems, and minimize the risk of falling victim to cyber attacks.
In the following sections, we will delve deeper into the TTP framework, explore common TTPs used by cybercriminals, and discuss techniques for detecting and preventing these threats.
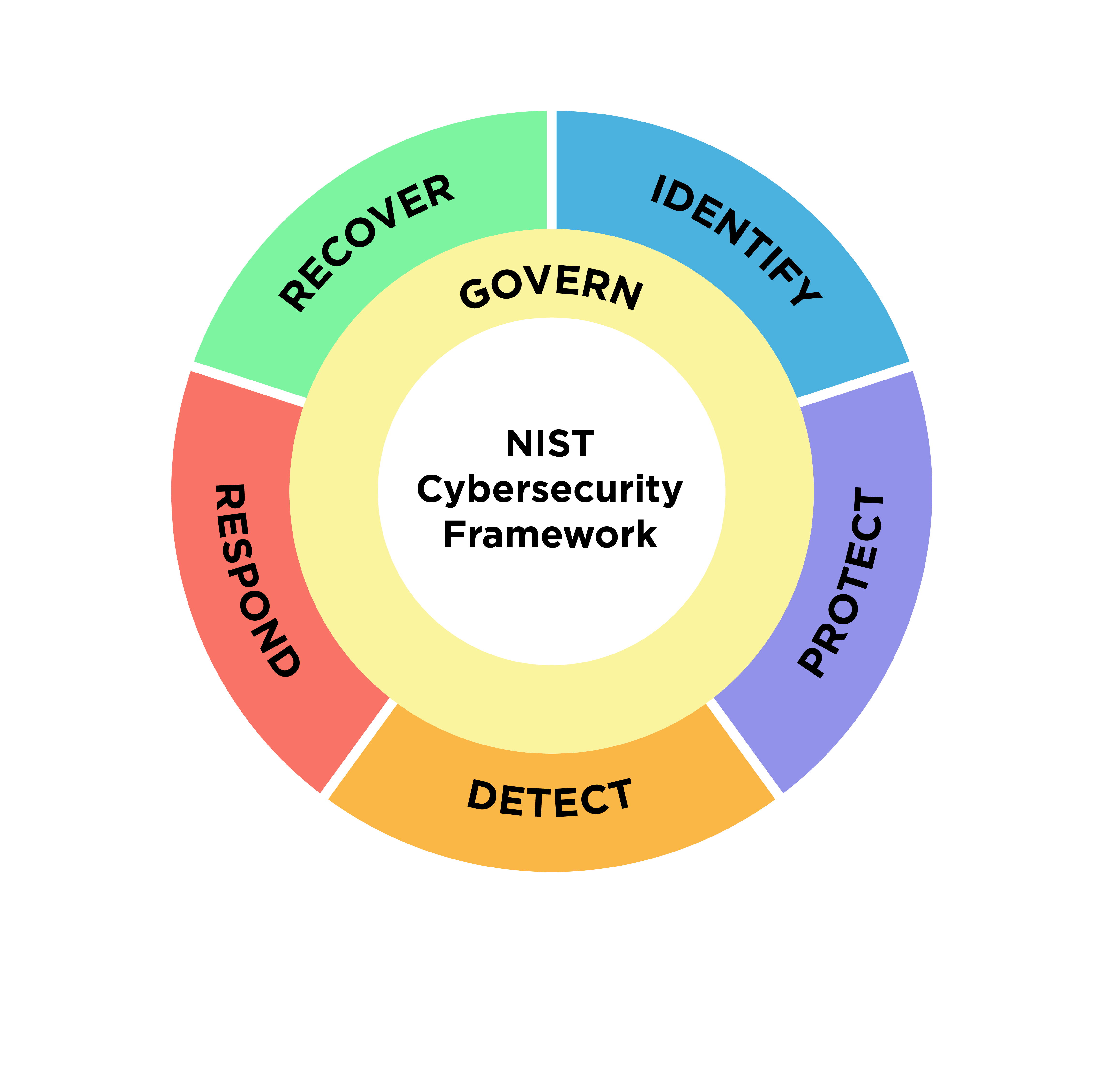
TTP Framework
The TTP framework provides a structured approach for analyzing and responding to cyber threats. It allows cybersecurity professionals to understand the tactics, techniques, and procedures employed by attackers, enabling them to develop effective defense strategies. The framework consists of several key steps:
1. Identification: In this initial phase, security teams gather intelligence to identify potential threats. This involves monitoring network activity, analyzing system logs, and staying updated on the latest threat intelligence feeds. The goal is to detect any suspicious behavior or indicators of compromise that could indicate an ongoing or imminent attack.
2. Analysis: Once a potential threat is identified, it is essential to analyze the gathered information in more detail. This includes investigating the tactics, techniques, and procedures used by the threat actor. By understanding how attackers operate, security professionals can assess the level of risk and prioritize their response efforts.
3. Mitigation: The next step involves implementing measures to mitigate the identified threats. This can include patching vulnerable systems, strengthening access controls, monitoring network traffic, and deploying advanced threat detection and prevention solutions. The goal is to minimize the attack surface and prevent unauthorized access or data exfiltration.
4. Response: In the event of a confirmed attack, an effective incident response plan is critical. This involves containing the incident, investigating the extent of the compromise, and restoring systems to a secure state. Communication and coordination are crucial during this phase to ensure a timely and efficient response.
5. Lessons Learned: After an incident is resolved, it is essential to conduct a thorough post-incident analysis. This includes evaluating the effectiveness of the response measures taken and identifying areas for improvement. Lessons learned from each incident can guide future security enhancements and help organizations better prepare for future attacks.
The TTP framework provides a systematic approach to understanding, responding to, and mitigating cyber threats. By following this framework, organizations can enhance their security posture, minimize the impact of attacks, and improve overall resiliency.
In the following sections, we will explore common TTPs used by cybercriminals, discuss techniques for detecting and preventing them, and examine real-life examples of TTPs employed in cyber attacks.
Common TTPs Used by Cybercriminals
Cybercriminals employ a wide range of tactics, techniques, and procedures (TTPs) to carry out their malicious activities. Understanding these common TTPs is crucial for organizations to detect, prevent, and respond effectively to cyber threats. Here are some of the most prevalent TTPs used by cybercriminals:
1. Phishing: Phishing is a social engineering technique in which attackers send fraudulent emails or messages pretending to be from trusted sources. The goal is to trick recipients into clicking on malicious links, revealing sensitive information, or downloading malware. Phishing attacks often target individuals or organizations with the intent of gaining unauthorized access or stealing valuable data.
2. Malware: Malware, short for malicious software, refers to any software designed to disrupt, damage, or gain unauthorized access to a computer system. Common types of malware include viruses, worms, trojans, ransomware, and spyware. Attackers use various techniques, such as email attachments, infected websites, or disguised downloads, to infect systems and exploit vulnerabilities.
3. Exploitation of Vulnerabilities: Attackers actively seek out vulnerabilities in software, networks, or applications to gain unauthorized access or carry out data breaches. They exploit these weaknesses by launching attacks such as SQL injection, cross-site scripting (XSS), or remote code execution. Organizations must promptly patch or update systems to protect against known vulnerabilities.
4. Remote Access Tools (RATs): Remote Access Tools are software tools that allow attackers to gain unauthorized access and control over a victim’s computer or network. Attackers can use RATs to install additional malware, exfiltrate data, or carry out surveillance, all while remaining undetected.
5. Credential Theft: Attackers employ various techniques to steal user credentials, such as usernames and passwords, allowing them to gain unauthorized access to systems or accounts. Methods include brute-force attacks, keylogging, credential phishing, and credential stuffing (using stolen credentials against multiple accounts).
6. Distributed Denial of Service (DDoS): DDoS attacks involve overwhelming a target’s network or website with a massive volume of fraudulent traffic, causing it to become unavailable to legitimate users. Attackers typically harness botnets, armies of compromised devices, to carry out these attacks, disrupting services and potentially extorting organizations.
7. Insider Threats: Insider threats involve malicious actions or unintentional mistakes made by authorized individuals within an organization. Insiders may abuse their privileges, leak sensitive information, or engage in sabotage activities. Organizations must implement proper access management controls and monitoring systems to detect and prevent insider threats.
These are just a few examples of the common TTPs employed by cybercriminals. However, it is important to note that attackers continually adapt their techniques, making it crucial for organizations to stay informed about evolving threats and implement a multi-layered security strategy.
In the next section, we will discuss techniques for detecting and preventing TTPs, enabling organizations to proactively defend against cyber threats.
Techniques for Detecting and Preventing TTPs
Detecting and preventing TTPs (Tactics, Techniques, and Procedures) is a critical aspect of effective cybersecurity. By employing the following techniques, organizations can enhance their ability to identify and mitigate cyber threats:
1. Security Awareness Training: Educating employees about cybersecurity best practices is crucial for preventing TTP-based attacks. Regular training sessions can help employees recognize phishing attempts, avoid clicking on suspicious links or downloading malicious attachments, and report any suspicious activity promptly.
2. Network Monitoring: Implementing robust network monitoring tools allows organizations to detect unusual patterns, indicators of compromise, or malicious activities. Intrusion detection systems (IDS) and intrusion prevention systems (IPS) can identify potential attacks and take immediate action to mitigate them. Network traffic analysis can also help identify unusual or unauthorized behavior within the network.
3. Endpoint Protection: Deploying endpoint protection solutions, such as antivirus software, firewalls, and host intrusion prevention systems, is essential for safeguarding individual devices and preventing TTPs. These tools can detect and block malware, unauthorized access attempts, and other common attack vectors.
4. Vulnerability Management: Regularly scanning and patching vulnerabilities in software and systems is vital for preventing TTP-based attacks. By staying updated with the latest patches and conducting security audits, organizations can minimize the risk of exploits and strengthen their defenses against TTPs.
5. Threat Intelligence: Subscribing to threat intelligence feeds and staying informed about emerging TTPs and attacker strategies can help organizations proactively identify and respond to potential threats. These feeds provide valuable information on new malware strains, attack vectors, and other TTPs, empowering organizations to adjust their security measures accordingly.
6. Incident Response Planning: Developing a comprehensive incident response plan is essential for effectively dealing with TTP-based attacks. This includes defining roles and responsibilities, establishing communication channels, and conducting regular drills to ensure readiness. A well-prepared incident response plan minimizes response time and reduces the impact of attacks.
7. Security Information and Event Management (SIEM): SIEM tools aggregate and analyze security event logs from various sources, enabling organizations to identify potentially malicious activities and threats. SIEM can correlate event data and threat intelligence, providing a holistic view of an organization’s security posture and aiding in early detection and response to TTP-based attacks.
By implementing these techniques, organizations can significantly improve their ability to detect and prevent TTP-based attacks. However, it is important to note that cybersecurity is an ongoing process, requiring continuous monitoring, updates, and adaptations to counter the evolving threat landscape.
In the next section, we will explore real-life examples of TTPs used in cyber attacks, providing further insights into the importance of understanding and addressing these tactics effectively.
Real-Life Examples of TTPs Used in Cyber Attacks
Understanding the real-life examples of Tactics, Techniques, and Procedures (TTPs) used in cyber attacks provides valuable insights into the evolving nature of cyber threats. Here are a few notable examples:
1. Advanced Persistent Threats (APTs): APTs are sophisticated, long-term targeted attacks carried out by well-funded and highly skilled threat actors. In the case of the Stuxnet worm, widely attributed to a joint effort by the United States and Israel, the attack targeted Iran’s nuclear facilities. The TTPs employed included exploiting zero-day vulnerabilities, utilizing stolen digital certificates, and leveraging personalized spear-phishing emails.
2. Ransomware: Ransomware attacks have become increasingly prevalent, targeting individuals and organizations worldwide. Notable examples include the WannaCry and NotPetya attacks. These attacks utilized vulnerabilities in the Windows operating system to propagate across networks and encrypt victims’ data, demanding ransom payments in exchange for decryption keys. The TTPs involved exploiting unpatched systems, leveraging worm-like capabilities, and employing network scanning techniques.
3. Business Email Compromise (BEC): BEC attacks involve impersonating high-level executives or trusted parties to trick employees into wiring money or disclosing sensitive information. In one high-profile case, the cybercriminal group known as “The Carbanak Gang” targeted financial institutions worldwide, resulting in the loss of over a billion dollars. Their TTPs included spear-phishing, gaining unauthorized access to internal systems, and conducting extensive reconnaissance to identify the most lucrative targets.
4. Supply Chain Attacks: Supply chain attacks involve compromising a company’s trusted vendors or suppliers to gain unauthorized access to their targets. In 2017, the NotPetya attack highlighted the risk of a compromised software supply chain. Attackers breached a Ukrainian accounting software company, which unknowingly distributed a malicious update to its customers. This resulted in the widespread dissemination of the NotPetya ransomware and caused significant financial damage worldwide.
5. Social Engineering: Social engineering attacks often exploit human psychology and trust. One notable example is the Twitter spear-phishing attack in July 2020, where attackers targeted high-profile accounts to promote a Bitcoin scam. By compromising employee credentials through spear-phishing, the attackers gained access to internal tools, allowing them to hijack accounts and post fraudulent messages. This type of attack highlights the effectiveness of social engineering in compromising even well-known platforms.
These real-life examples illustrate the diverse range of TTPs employed by cybercriminals. They emphasize the need for organizations and individuals to stay vigilant, update their security measures, and educate themselves about emerging threats.
By analyzing and understanding these TTPs, organizations can enhance their detection capabilities, develop targeted defense strategies, and implement necessary countermeasures to minimize the risk of falling victim to cyber attacks.
In the concluding section, we will summarize the key insights gained from exploring TTPs in cybersecurity.
Conclusion
In today’s interconnected digital world, understanding and addressing Tactics, Techniques, and Procedures (TTPs) used in cyber attacks is crucial for effective cybersecurity. By comprehending the tactics employed by attackers, organizations can better anticipate their motives and adjust their defense strategies accordingly. Techniques and procedures shed light on the methods and processes used by cybercriminals, allowing security professionals to identify vulnerabilities and develop appropriate countermeasures.
Throughout this article, we explored the definition of TTP in cybersecurity and its three main components: tactics, techniques, and procedures. We also examined the TTP framework, which provides a structured approach for analyzing and responding to cyber threats. By following this framework, organizations can enhance their incident response capabilities, detect threats more effectively, and mitigate attacks.
We discussed common TTPs used by cybercriminals, such as phishing, malware, exploitation of vulnerabilities, and insider threats. Understanding these TTPs empowers organizations to develop targeted defense strategies, implement robust security measures, and educate employees to recognize and avoid potential threats.
Furthermore, we highlighted techniques for detecting and preventing TTPs. These techniques include security awareness training, network monitoring, endpoint protection, vulnerability management, threat intelligence, incident response planning, and the use of security information and event management (SIEM) tools. By combining these approaches, organizations can proactively defend against TTP-based attacks and minimize their impact.
Lastly, we examined real-life examples of TTPs used in cyber attacks, demonstrating the evolving nature of cyber threats and the importance of staying informed and adaptive. These examples showcased the sophistication and ingenuity employed by threat actors, emphasizing the need for continuous monitoring, updating security measures, and fostering a strong cybersecurity culture.
As cyber threats continue to evolve, organizations must remain vigilant, proactive, and adaptable in their approach to cybersecurity. By understanding and addressing TTPs effectively, organizations can build robust defenses, protect valuable assets, and mitigate the risk of falling victim to cyber attacks.
Remember, cybersecurity is a collective effort. It requires collaboration between individuals, organizations, and society as a whole to create a safer digital environment for everyone.