Introduction
With the rise of online privacy concerns and the need for secure internet connections, Virtual Private Networks (VPNs) have become increasingly popular. A VPN allows users to establish a secure and encrypted connection to the internet, ensuring that their online activities are private and protected.
But what exactly is a P2P VPN? P2P, or Peer-to-Peer, refers to a decentralized network architecture where computers and devices on the network can act both as clients and servers. In the context of VPNs, P2P VPNs utilize this architecture to create a network where users can directly connect with each other, bypassing the need for a central server.
P2P VPNs offer several advantages over traditional VPNs. They provide enhanced privacy, as they don’t rely on a central server that can potentially log or monitor user activities. Additionally, P2P VPNs can offer faster speeds and better reliability as they distribute the connection load across the network rather than relying on a single server.
In this article, we will delve into the ins and outs of P2P VPNs, exploring how they work, their benefits, and common use cases. We will also highlight some popular P2P VPN providers in the market today. So, let’s dive in and discover the world of P2P VPNs!
What Is a VPN?
A Virtual Private Network (VPN) is a technology that creates a secure and encrypted connection between a user’s device and the internet. It acts as a tunnel that protects the user’s data and online activities from prying eyes, ensuring privacy and security.
When you connect to a VPN, your internet traffic is encrypted and routed through a server located in a different geographical location. This masks your IP address and makes it appear as if you are browsing from the server’s location, providing an additional layer of anonymity.
VPNs are commonly used for various reasons:
- Online Privacy: VPNs prevent your Internet Service Provider (ISP), government agencies, or even hackers from tracking and monitoring your online activities. They ensure that your personal information, such as browsing history and passwords, remains private.
- Secure Connection: VPNs encrypt your internet traffic, making it unreadable to third parties. This protects your sensitive data, such as credit card information or login credentials, from being intercepted by hackers on public networks.
- Access Geo-restricted Content: VPNs allow you to bypass geographic restrictions and access content that may be blocked in your region. By connecting to a server in a different country, you can access region-specific streaming services, websites, or social media platforms.
- Remote Work: With the increasing trend of remote work, VPNs provide a secure connection for employees to access company resources and communicate with colleagues. This is especially important when connecting to public Wi-Fi networks or unsecured connections.
Overall, VPNs are an essential tool for maintaining online privacy, security, and freedom. They give users control over their internet connection, ensuring that their data and activities remain private and protected from prying eyes.
What Is P2P?
P2P, or Peer-to-Peer, is a network architecture that allows devices on a network to directly communicate with each other without the need for a central server. In a P2P network, each device can act as both a client and a server, sharing resources and information with other devices on the network.
The concept of P2P networking gained popularity with the rise of file-sharing applications like Napster and BitTorrent. These applications allowed users to share files directly with each other, bypassing the traditional client-server model.
In a P2P network, there is no single point of failure or bottleneck as the network’s resources are distributed among multiple devices. This decentralization provides several advantages:
- Redundancy: With no central server, P2P networks are resilient to failures. Even if one device goes offline, other devices can still communicate with each other.
- Scalability: P2P networks can easily scale to accommodate a large number of devices since every device can act as a peer, sharing its resources with others.
- Improved Performance: By distributing the workload across multiple devices, P2P networks can achieve faster download and upload speeds compared to traditional client-server networks.
- Shared Resources: In a P2P network, devices can share not only files but also processing power, storage, and bandwidth, allowing for efficient resource utilization.
P2P technology is not limited to file sharing. It has been adopted in various applications and industries, such as content distribution, streaming services, and even cryptocurrency networks like Bitcoin.
While P2P networks offer many benefits, they also have certain challenges. Due to the decentralized nature of P2P, it can be difficult to enforce centralized control, regulate content, or ensure the security and privacy of users.
With a basic understanding of P2P, we can now explore how P2P and VPNs come together to form P2P VPNs, revolutionizing the way we connect to the internet and ensuring enhanced privacy and security.
Understanding P2P VPNs
P2P VPNs, also known as Peer-to-Peer VPNs or PeerVPN, are a specialized type of VPN that utilize the P2P network architecture to establish secure and private connections between users. Unlike traditional VPNs that rely on centralized servers, P2P VPNs allow users to connect directly to other users’ devices, creating a decentralized network of VPN nodes.
The primary goal of a P2P VPN is to provide users with a secure and private internet connection while leveraging the benefits of P2P architecture. By distributing the connection load across multiple devices, P2P VPNs can offer faster speeds and improved reliability compared to traditional VPN services.
One of the key advantages of P2P VPNs is enhanced privacy. With traditional VPNs, users typically connect to a server operated by the VPN provider. While most reputable VPN providers have strict privacy policies, there is still a level of trust involved. In contrast, P2P VPNs eliminate the need for a central authority, reducing the risk of potential logging or monitoring of user activities.
P2P VPNs also offer a greater level of anonymity. With traditional VPNs, users might get assigned an IP address associated with the VPN server they connect to. But with P2P VPNs, users can connect directly to other users’ devices, making it much harder to trace their online activities back to a specific IP address.
It’s worth noting that not all VPN services support P2P connectivity. P2P VPNs require specific protocols and configurations that allow users to establish direct connections with each other. Therefore, when selecting a VPN service, it’s essential to ensure that it supports P2P usage if that is a requirement.
Overall, P2P VPNs combine the power of P2P networking with the privacy and security features of a VPN. They offer users the ability to create a decentralized network of VPN nodes, enhancing privacy, improving connection speeds, and providing a reliable and secure internet connection.
Advantages of P2P VPNs
P2P VPNs, or Peer-to-Peer VPNs, offer several advantages over traditional VPNs. These advantages stem from the unique characteristics of the P2P network architecture that P2P VPNs leverage. Let’s explore some of these advantages:
- Enhanced Privacy: P2P VPNs provide a higher level of privacy compared to traditional VPNs. By eliminating the need for a central server, P2P VPNs reduce the risk of potential logging or monitoring of user activities. Users connect directly to other users’ devices, minimizing the chances of their online activities being tracked or traced back to a specific server.
- Improved Connection Speeds: The P2P network architecture allows P2P VPNs to distribute the connection load across multiple devices. This decentralized approach helps to minimize congestion and offers faster connection speeds. Since users connect directly to other users’ devices, there is no bottleneck caused by a single server that needs to handle all the incoming and outgoing traffic.
- Increased Reliability: With traditional VPNs, if the chosen server becomes overloaded or experiences technical issues, it can lead to degraded performance or even connection failures. P2P VPNs eliminate that risk by allowing users to establish direct connections with multiple devices on the network. If one node goes offline or experiences issues, users can easily switch to another available node, ensuring uninterrupted connectivity.
- Flexibility and Scalability: P2P VPNs offer flexibility in terms of network size and scalability. Since every device can act as both a client and a server, P2P VPN networks can easily expand to accommodate more users and devices. This makes them suitable for various use cases, from small-scale personal networks to large-scale corporate networks.
- Decentralization: P2P VPNs operate on a decentralized network architecture, meaning there is no single point of failure. If one node goes down, the remaining nodes can still communicate with each other. This decentralized approach also makes it challenging for potential attackers to disrupt or compromise the network, enhancing overall security.
By taking advantage of the P2P network architecture, P2P VPNs offer enhanced privacy, faster speeds, improved reliability, flexibility, scalability, and decentralization. These advantages make P2P VPNs a compelling option for users seeking a secure, private, and efficient way to connect to the internet.
How Do P2P VPNs Work?
P2P VPNs, or Peer-to-Peer VPNs, work by leveraging the peer-to-peer network architecture to create a secure and private internet connection between users. Instead of relying on a central server, P2P VPNs allow users to connect directly to each other’s devices, forming a decentralized network of VPN nodes.
Here’s a step-by-step breakdown of how P2P VPNs work:
- Node Discovery: When a user connects to a P2P VPN, the VPN software initiates a process called node discovery. This process involves finding other devices on the network that are currently available for connections.
- Authentication: Once the available nodes are discovered, the VPN software authenticates the user’s device and establishes trust between the connecting nodes. This authentication process ensures that only authorized devices can join the P2P VPN network.
- Establishing Connections: After authentication, the user’s device establishes direct connections with other nodes on the network. These connections create a virtual tunnel through which the user’s internet traffic is encrypted and routed securely.
- Peer-to-Peer Communication: With the connections established, users can now communicate with each other directly, exchanging encrypted data packets without going through a central server. This direct communication helps to improve connection speeds, reduce latency, and enhance overall network performance.
- Data Encryption: To ensure privacy and security, P2P VPNs utilize robust encryption algorithms to encrypt the data transmitted between nodes. This encryption shields the user’s internet traffic from potential eavesdroppers, making it unreadable by unauthorized entities.
- Traffic Routing: As users browse the internet or use online services, their data is encrypted and routed through the established P2P VPN connections. This routing ensures that the user’s IP address is masked, making it difficult for third parties to track or trace their online activities.
It’s important to note that each P2P VPN implementation may have slightly different variations in how they establish connections, authenticate users, or handle encryption. However, the underlying principle remains the same: creating a peer-to-peer network of connected devices to provide secure and private internet access.
By leveraging the power of P2P networking, P2P VPNs enable users to establish direct connections, encrypt their data, and route their internet traffic securely. This decentralized approach offers enhanced privacy, faster speeds, and improved reliability compared to traditional VPN services.
Key Features of P2P VPNs
P2P VPNs, or Peer-to-Peer VPNs, offer unique features that differentiate them from traditional VPNs. These features are tailored to take advantage of the P2P network architecture and provide users with a secure, private, and efficient internet connection. Let’s explore some of the key features of P2P VPNs:
- Decentralized Network: P2P VPNs operate on a decentralized network architecture, eliminating the need for a central server. This decentralization improves security, as there is no single point of failure or control. Users connect directly to other users’ devices, creating a peer-to-peer network of VPN nodes.
- User-to-User Connectivity: P2P VPNs allow users to establish direct connections with each other’s devices. This direct connectivity bypasses the need to route internet traffic through a central server. It enables faster connection speeds, reduces latency, and improves overall network performance.
- Enhanced Privacy: P2P VPNs provide enhanced privacy by eliminating the need for a central server that can potentially log or monitor user activities. Users connect directly with each other, making it harder for third parties to track or trace their online activities. The encryption used by P2P VPNs ensures that user data remains private and secure.
- Distributed Load Balancing: P2P VPNs distribute the connection load across multiple devices on the network. This distributed load balancing ensures faster speeds and improved reliability as the workload is shared among multiple devices. It helps prevent congestion and bottlenecks that can occur with traditional VPNs.
- Dynamic Network Routing: P2P VPNs utilize dynamic network routing to establish the most efficient paths for transmitting data between nodes. This adaptive routing ensures that data packets take the most optimal route, minimizing latency and maximizing network performance.
- Scalability: P2P VPNs are inherently scalable due to the peer-to-peer network architecture. As more users join the network, the VPN can easily scale by utilizing the computing power and resources of the new devices. This scalability makes P2P VPNs suitable for both small-scale personal networks and large-scale corporate networks.
- Multi-Platform Support: P2P VPNs are designed to support various platforms and devices, including desktop computers, laptops, smartphones, and tablets. Users can connect their devices regardless of the operating system or hardware they are using.
These key features make P2P VPNs a powerful alternative to traditional VPN services. They offer enhanced privacy, increased speed, improved reliability, and the flexibility to scale to accommodate different network sizes and device types.
Common Uses of P2P VPNs
P2P VPNs, or Peer-to-Peer VPNs, serve a variety of purposes and are used in various scenarios where secure and private internet connectivity is paramount. Let’s explore some of the common uses of P2P VPNs:
- File Sharing: P2P VPNs are often utilized for secure and private file sharing. Users can connect directly to each other’s devices, allowing them to transfer files without relying on a central server. This decentralized approach ensures faster transfer speeds, increased privacy, and reduced reliance on third-party file-sharing platforms.
- Remote Work: With the rise of remote work, P2P VPNs are an essential tool for employees who need secure access to their company’s resources. P2P VPNs can establish a direct connection between the employee’s device and the company’s network, ensuring that sensitive data remains protected while working remotely.
- Online Gaming: P2P VPNs can enhance online gaming experiences by reducing latency and improving connection stability. By connecting directly with other players in the game, P2P VPNs help gamers enjoy smoother gameplay and reduce the chances of network-related disruptions.
- Anonymous Browsing: P2P VPNs provide users with a high level of anonymity by hiding their IP addresses and encrypting their internet traffic. This anonymity is valued by individuals who want to browse the internet privately and access content without their activities being tracked or monitored.
- Geo-restricted Content Access: P2P VPNs can help users bypass geographic restrictions imposed on certain online content. By connecting to a VPN node in a different location, users can gain access to region-specific streaming services, websites, or social media platforms that may be blocked in their own region.
- Protection on Public Wi-Fi: Public Wi-Fi networks pose security risks as they are often unsecured. P2P VPNs provide a secure and encrypted connection, protecting users’ data from potential eavesdroppers and hackers who may be trying to intercept their internet traffic.
- Circumventing Internet Censorship: In regions where internet censorship is prevalent, P2P VPNs can help users bypass restrictions and access uncensored information. By connecting to a VPN node outside the censored region, users can browse the internet freely and securely.
These are just a few examples of the common uses of P2P VPNs. Whether it’s for file sharing, remote work, online gaming, anonymous browsing, accessing restricted content, or protecting data on public Wi-Fi, P2P VPNs offer a versatile and secure solution for various internet connectivity needs.
Popular P2P VPN Providers
As the demand for P2P VPNs continues to grow, several providers have emerged in the market, offering reliable and feature-rich services. Let’s take a look at some popular P2P VPN providers:
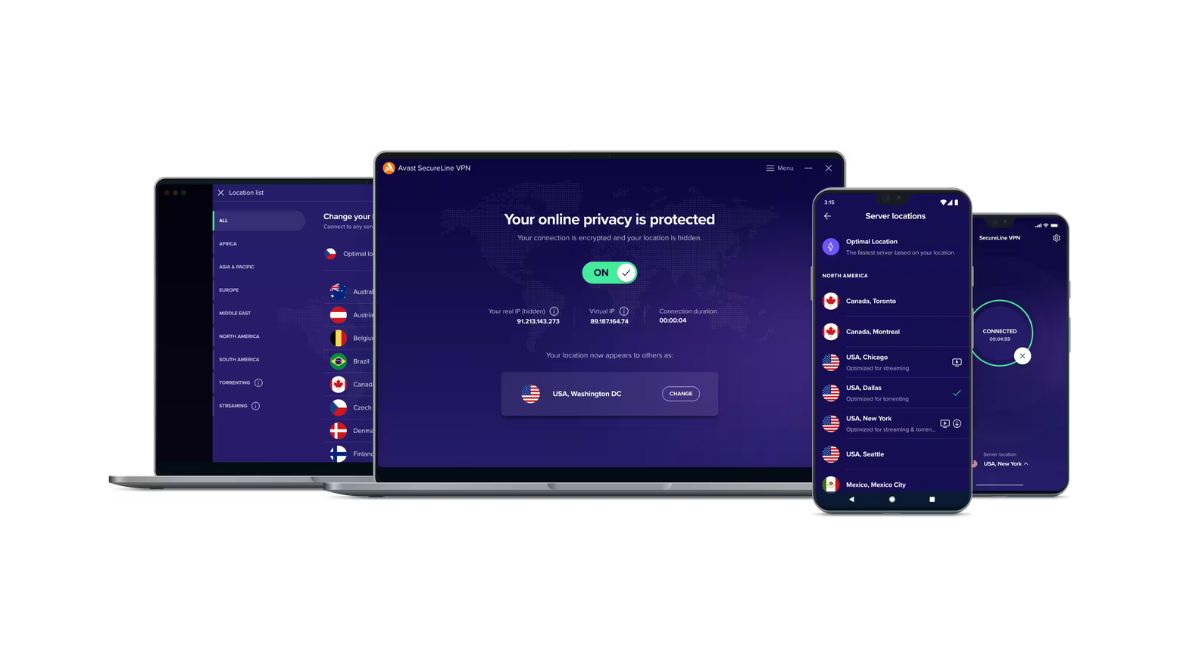
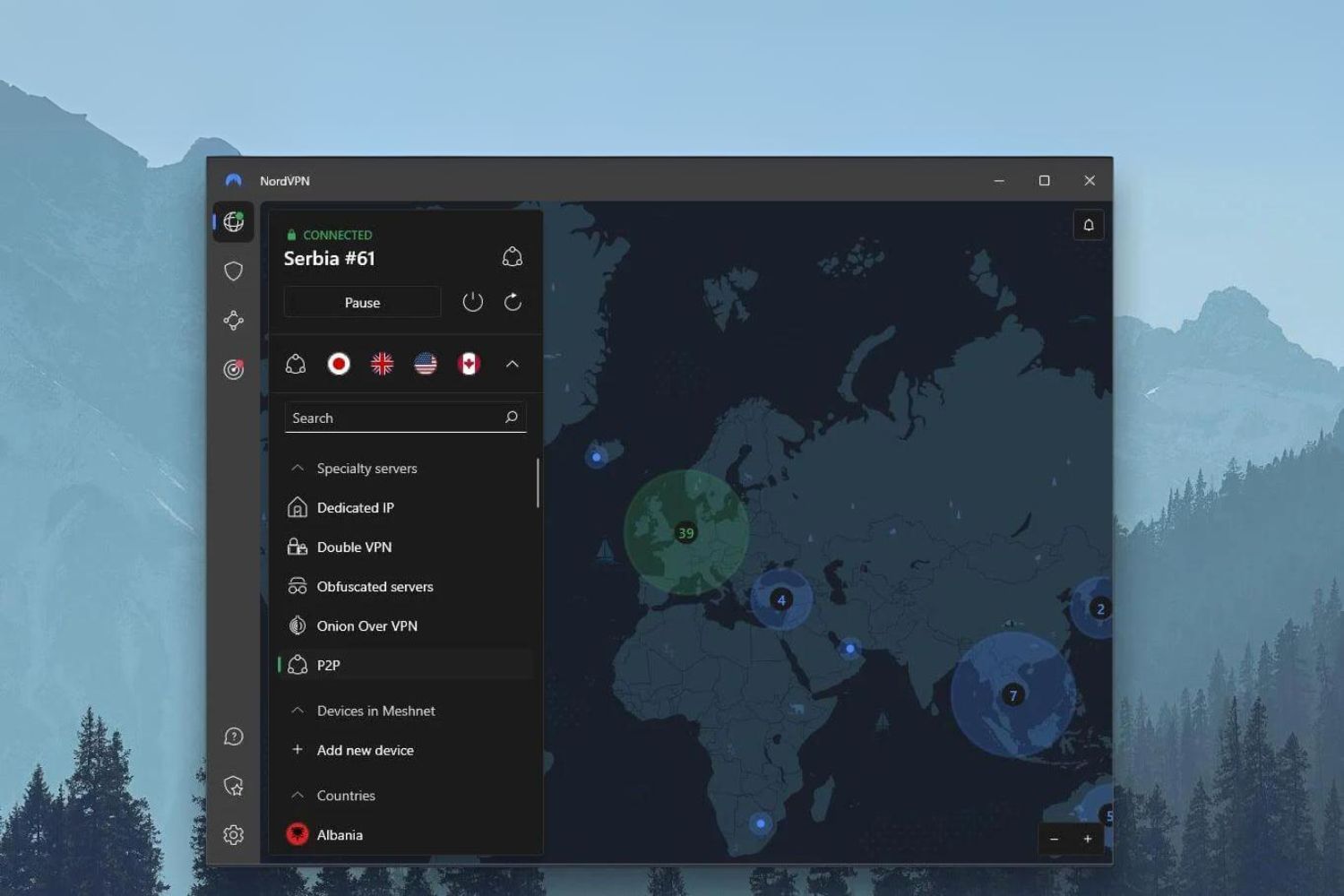
- NordVPN: NordVPN is widely recognized for its strong commitment to user privacy and security. It offers a dedicated P2P server category, optimized for file sharing and torrenting activities. With a large network of servers across various countries, NordVPN ensures excellent performance and a high level of anonymity for P2P users.
- ExpressVPN: ExpressVPN is known for its fast and reliable service, making it an excellent choice for P2P users. It offers unlimited bandwidth and allows torrenting on all its servers. ExpressVPN utilizes strong encryption and has a strict no-logs policy, ensuring user privacy and security.
- CyberGhost: CyberGhost is a P2P-friendly VPN provider that offers specialized servers for secure and anonymous torrenting. Its user-friendly interface and automatic kill switch feature make it an attractive option for users looking for a hassle-free P2P VPN experience.
- Surfshark: Surfshark is a relatively new player in the VPN market but has gained popularity for offering unlimited simultaneous connections. It allows P2P traffic on all its servers and provides strong encryption, a kill switch, and DNS leak protection for enhanced security.
- Private Internet Access (PIA): PIA is a well-established VPN provider known for its strong commitment to privacy. It offers dedicated P2P servers and supports port forwarding, making it an excellent choice for users who engage in file sharing activities.
These are just a few examples of popular P2P VPN providers, each with its own unique features and strengths. When choosing a P2P VPN provider, it’s important to consider factors such as speed, server locations, encryption protocols, privacy policies, and customer support to ensure it aligns with your specific needs.
It’s worth noting that while these providers support P2P activities, it is essential to review and comply with their respective terms of service to avoid any potential misuse or violation of their policies.
By selecting a reputable and reliable P2P VPN provider, users can enjoy a secure and private internet connection, optimized for their file-sharing and torrenting needs.
Conclusion
P2P VPNs, or Peer-to-Peer VPNs, offer a unique and decentralized approach to secure and private internet connectivity. By leveraging the P2P network architecture, P2P VPNs provide users with enhanced privacy, faster speeds, improved reliability, and the flexibility to scale to accommodate different network sizes and device types.
With P2P VPNs, users can establish direct connections with each other’s devices, eliminating the need for a central server and reducing the risk of potential logging or monitoring of user activities. This decentralized approach enhances privacy and anonymity, making it harder for third parties to track or trace users’ online activities.
Furthermore, P2P VPNs distribute the connection load across multiple devices, improving connection speeds and ensuring better performance. This distributed load balancing ensures faster transfer speeds and reduces latency, providing an optimal user experience.
Common uses of P2P VPNs range from secure file sharing and remote work access to anonymous browsing, accessing geo-restricted content, and protecting data on public Wi-Fi networks. P2P VPNs provide individuals and businesses with a secure and private internet connection, regardless of their location or the network they are connected to.
Popular P2P VPN providers like NordVPN, ExpressVPN, CyberGhost, Surfshark, and Private Internet Access (PIA) offer reliable and feature-rich services specifically designed for P2P users. When choosing a P2P VPN provider, it’s important to consider factors such as speed, server locations, encryption protocols, privacy policies, and customer support to ensure the best fit for individual needs.
In conclusion, P2P VPNs are an innovative and efficient way to establish secure and private internet connections. By leveraging the power of the peer-to-peer network architecture, P2P VPNs offer enhanced privacy, faster speeds, improved reliability, and flexibility, making them a valuable tool for individuals and businesses seeking a secure and seamless online experience.