Introduction
RFID (Radio Frequency Identification) locks are becoming increasingly popular for their convenience and security. These locks use radio waves to communicate between a card or fob and the lock, eliminating the need for a physical key. While this technology offers numerous benefits, there may be situations where you find yourself without access to your RFID card or fob, needing to open the lock.
In this article, we will explore how to open an RFID lock without a key. Before we dive into the techniques, it is important to note that attempting to bypass or manipulate RFID locks may violate legal and ethical boundaries. This article is intended for educational purposes only, and we recommend using these methods responsibly and with the owner’s permission.
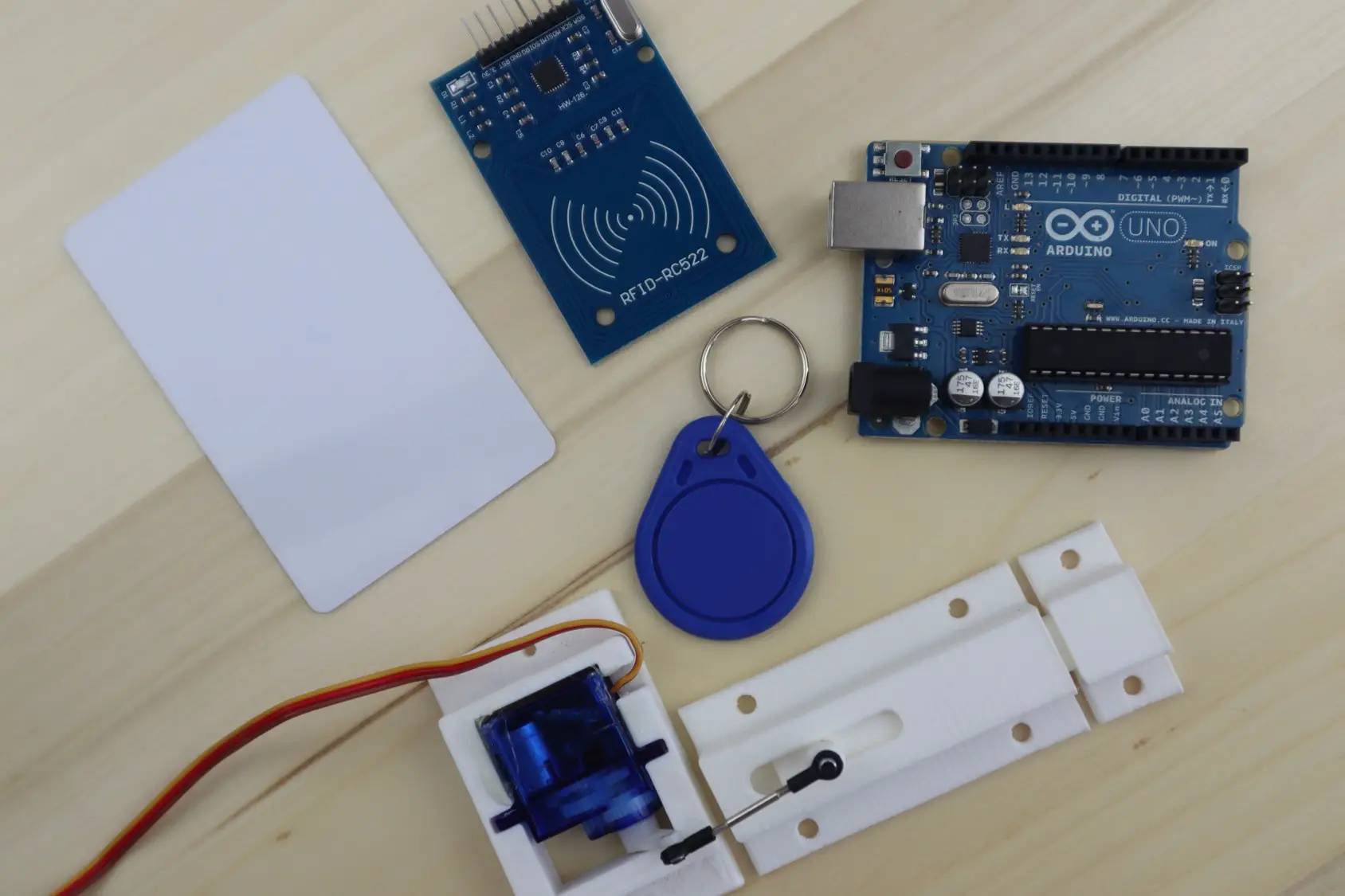
Understanding the workings of RFID locks is crucial before attempting to open them without a key. RFID locks consist of two main components: the lock itself and an RFID reader. The lock receives signals from the reader, which is typically in the form of an RFID card or fob. When the correct signal is received, the lock disengages, allowing access.
To successfully open an RFID lock without a key, you will need a few specialized tools and a good understanding of the lock’s vulnerabilities. It’s important to note that not all RFID locks can be easily bypassed, as some are designed with advanced security features. However, we will explore several methods that can be effective in certain scenarios.
By following the steps outlined in this article, you will gain insights into the techniques used to open RFID locks without a key. It empowers you to approach this challenge with knowledge and a problem-solving mindset. Remember, though, always use this knowledge responsibly and in alignment with legal and ethical guidelines.
Understanding RFID Locks
Before we delve into the methods of opening RFID locks without a key, let’s take a closer look at how these locks work. RFID locks use radio frequency technology to communicate between the lock and an RFID card or fob. The lock itself contains an antenna and a receiver, while the card or fob carries a small chip with unique identifying information.
When the RFID card or fob is brought into proximity with the lock, usually within a few inches, the lock’s antenna captures the radio waves emitted by the card. The receiver in the lock then analyzes the data received from the card’s chip, verifying its authenticity and granting or denying access accordingly.
To enhance security, RFID locks use different frequencies for communication. The most commonly used frequencies are low frequency (LF), high frequency (HF), and ultra-high frequency (UHF). Each frequency range has its own advantages and limitations, so understanding the frequency used by your RFID lock is crucial when attempting to bypass it without a key.
Additionally, RFID locks may utilize various protocols, such as ISO/IEC 14443 and ISO/IEC 15693, to ensure secure communication between the lock and the card or fob. These protocols define the standards for data transmission and encryption, further enhancing the security of the system.
It’s important to note that not all RFID locks are created equal. Some locks may have additional layers of security, such as encrypted data transmission or biometric authentication, making them more challenging to bypass without a key. However, many RFID locks in use today still employ basic technology, leaving room for potential vulnerabilities.
Understanding the inner workings of RFID locks is crucial when attempting to open them without a key. By familiarizing yourself with the underlying technology, frequency used, and potential vulnerabilities, you’ll be better equipped to explore the methods we’ll discuss in the following sections.
Preparing the Necessary Tools
Before attempting to open an RFID lock without a key, it is essential to gather the necessary tools. While the specific tools may vary depending on the method you choose, here are some common tools that can be useful in bypassing RFID locks:
- RFID Reader: An RFID reader is a device used to communicate with RFID cards or fobs. It allows you to read the data stored on the card’s chip and potentially clone or emulate the card’s signals. Different RFID readers support different frequencies and protocols, so ensure that you have a reader compatible with the lock you are working on.
- RFID Writer: In some cases, you may need an RFID writer to clone or modify the data stored on an RFID card. This tool enables you to replicate the card’s information onto a new card or manipulate the data to gain access to the lock.
- Antenna: An antenna can help boost the range and signal strength between the RFID reader and the lock. This can be especially useful if you are attempting to open a lock from a greater distance.
- Software: In addition to hardware tools, specific software applications or programming skills might be required to interact with the RFID reader, capture card data, or modify card information.
- Lock Picks: While not directly related to RFID locks, lock picks may come in handy if you need to resort to alternate methods, such as physically manipulating the lock or accessing the lock control panel.
It’s important to note that obtaining and using these tools ethically and legally is crucial. Misuse of these tools to gain unauthorized access to property or information is illegal and may result in severe consequences. Always ensure that you have the owner’s permission and use these tools responsibly and within the boundaries of the law.
Once you have gathered the necessary tools, you will be ready to proceed with the methods we will explore next. Remember to exercise caution and discretion while attempting to open an RFID lock without a key, and prioritize safety and ethical considerations throughout the process.
Finding the Vulnerabilities
Before attempting to open an RFID lock without a key, it’s crucial to identify any potential vulnerabilities inherent in the lock’s design or implementation. By understanding these vulnerabilities, you can find weaknesses that may allow you to bypass the lock system successfully.
One common vulnerability is the use of weak or easily guessable key codes. Some RFID locks utilize basic key codes, such as sequential numbers or easily deducible patterns. If you have access to the lock’s key codes, you may be able to brute force or systematically try different combinations until you find the correct one.
Another potential vulnerability arises from the card or fob’s storage and transmission of data. Some RFID locks may use encryption or specific encoding methods to protect the data exchanged between the card and the lock. However, there are instances where the implementation of these security measures may have weaknesses, which can be exploited to gain unauthorized access to the lock.
Additionally, physical inspection of the lock can reveal vulnerabilities. Look for exposed wires or connectors that may be used to bypass the RFID reader or directly connect to the lock’s control panel. These physical vulnerabilities can provide alternative methods to open the lock without relying solely on the RFID card or fob.
Furthermore, it’s worth exploring if the lock system has any known vulnerabilities or exploits documented by security researchers. Check online forums, blogs, and security advisories to see if any weaknesses related to the specific lock model or brand have been identified and disclosed. These insights can serve as a valuable starting point in your attempt to open the RFID lock without a key.
Remember, when exploring vulnerabilities, it’s crucial to stay within legal and ethical boundaries. Ensure that you have permission from the lock’s owner before attempting any techniques to bypass the lock, and refrain from circumventing security measures without appropriate authorization.
By identifying and understanding the vulnerabilities of the RFID lock, you can strategize and focus your efforts on the most promising methods for successfully opening the lock without a key.
Identifying the Appropriate Frequency
When attempting to open an RFID lock without a key, it’s crucial to identify and understand the frequency at which the lock operates. RFID locks utilize different frequency ranges for communication, including low frequency (LF), high frequency (HF), and ultra-high frequency (UHF).
The first step in identifying the appropriate frequency is to examine the RFID card or fob used with the lock. Look for any markings or labels on the card that indicate the frequency range. In some cases, the frequency may be printed or engraved on the card itself. If there are no visible indicators, you can refer to the lock’s documentation or contact the manufacturer for information regarding the frequency used.
If these options are not available or yield no results, you may need to use an RFID frequency detector or scanner. These devices can identify the frequency emitted by an RFID card or fob. Place the card or fob near the scanner and observe the output to determine the frequency. Ensure that the scanner supports the frequency ranges commonly used for RFID locks, such as LF, HF, or UHF.
Once you have determined the frequency, you can proceed with selecting the appropriate tools and methods specific to that frequency range. Keep in mind that different frequencies may require different types of RFID readers, as well as specialized techniques for cloning or emulating the card’s signals.
It’s important to note that some RFID locks may operate on multiple frequencies, allowing for compatibility with a wider range of RFID cards and fobs. In such cases, you may need to experiment or gather more information to pinpoint the exact frequency used by the lock.
Remember, when attempting to identify the appropriate frequency, always ensure that you have the necessary permission and authorization to interact with the RFID lock. Respect the legal and ethical boundaries associated with accessing and tampering with the lock system.
By accurately identifying the frequency, you will be one step closer to successfully opening the RFID lock without a key, as you can now focus your efforts on techniques and tools specifically designed for that particular frequency range.
Utilizing an RFID Reader
When opening an RFID lock without a key, an RFID reader is an essential tool that allows you to interact with the lock system and potentially gain unauthorized access. An RFID reader is designed to communicate with RFID cards or fobs by sending and receiving radio waves at specific frequencies.
To utilize an RFID reader effectively, follow these steps:
- Select a Compatible RFID Reader: Choose an RFID reader that supports the frequency used by the RFID lock you are attempting to bypass. Different locks may operate at different frequencies, such as low frequency (LF), high frequency (HF), or ultra-high frequency (UHF). Ensure that the chosen reader is compatible with the lock’s frequency range to establish successful communication.
- Power Up the RFID Reader: Connect the RFID reader to a reliable power source, such as batteries or a power adapter, depending on the model and specifications of the reader. Activate the reader and ensure it is ready for use.
- Place the RFID Card or Fob: Position the RFID card or fob within the effective range of the reader’s antenna. The precise positioning may vary depending on the reader and the lock. Experiment with different angles and distances to achieve the best signal reception.
- Capture the Card’s Data: Use the RFID reader to capture the data transmitted by the card. The reader will read the unique identifier stored on the card’s chip and display or record it, depending on the reader’s capabilities. This data may be useful for cloning or emulating the card’s signals later in the process.
- Clone or Emulate the Card’s Signals: If necessary, utilize an RFID writer or programming software compatible with the reader to clone or modify the captured card’s data. This process allows you to create a replica of the card or alter the card’s information to gain access to the RFID lock system.
- Test and Validate: Once you have cloned or modified the card’s data, test its effectiveness by positioning the cloned or modified card near the RFID lock. If successful, the lock should respond as if the original card were being used, granting access without the need for a physical key.
It’s essential to exercise caution and adhere to legal and ethical guidelines when utilizing an RFID reader to bypass RFID locks. Always ensure that you have proper authorization and permission from the lock’s owner before attempting to interact with the lock system.
By effectively utilizing an RFID reader, you can gather the necessary data from the original card and potentially clone or emulate its signals, providing you with a means to open the RFID lock without a physical key.
Spoofing the RFID Card
One method of opening an RFID lock without a key involves spoofing the RFID card or fob that would typically be used to access the lock. By spoofing the card, you can emulate the signals it would transmit, tricking the lock into granting access.
To successfully spoof an RFID card, follow these steps:
- Acquire the Required Equipment: Obtain an RFID writer compatible with the frequency used by the RFID lock, as well as blank RFID cards or writable RFID key fobs. Ensure that the RFID writer supports the necessary features for cloning or modifying the card’s data.
- Read the Original Card’s Data: Use an RFID reader to capture the unique identifier or data transmitted by the original RFID card. This data will serve as the basis for cloning or modifying the spoofed card.
- Clone or Modify the Card’s Data: Utilize the RFID writer and appropriate software to clone or modify the captured card’s data onto a blank RFID card or key fob. This process replicates the signals and identifying information of the original card.
- Test the Spoofed Card: Position the spoofed card within range of the RFID lock and test its effectiveness. If the spoofing process was successful, the lock should respond to the spoofed card’s signals, granting access without the need for the original card or a physical key.
It’s important to note that spoofing RFID cards may not be possible with all types or models of RFID locks. Some locks employ advanced security measures, such as encrypted data transmission or mutual authentication, making them more resistant to spoofing attempts. Therefore, it’s crucial to assess the lock’s security features and the compatibility of the spoofing technique before proceeding.
Additionally, it is vital to consider the legal and ethical implications of spoofing RFID cards. Ensure that you have proper authorization and permission from the lock’s owner before attempting to clone or modify an RFID card. Unlawful or unauthorized use of this technique can result in severe consequences.
By successfully spoofing the RFID card, you can emulate its signals and identification data, tricking the RFID lock into granting access. This method can provide an effective means of opening an RFID lock without a physical key.
Exploring Other Methods
In addition to utilizing an RFID reader and spoofing the RFID card, there are other methods you can explore when attempting to open an RFID lock without a key. These alternative methods may be effective depending on the specific lock’s vulnerabilities and your level of skill and expertise.
1. Physical Manipulation: Some RFID locks may have physical vulnerabilities that can be exploited to gain access. This method involves manipulating the lock mechanism itself, bypassing the need for an RFID card or key. Physical manipulation techniques may include lock picking, shimming, or using unconventional tools to manipulate the lock’s internals.
2. Accessing the Control Panel: In certain situations, gaining access to the lock’s control panel can allow you to manipulate its settings or override the authentication process. This method typically requires advanced knowledge of the lock’s design and control systems, as well as physical access to the lock’s internals.
3. Brute Force Attacks: Although time-consuming and not guaranteed to work, brute force attacks involve systematically trying different combinations until the correct one is discovered. This method is only applicable if the lock uses weak or easily guessable key codes.
4. Exploiting Software Vulnerabilities: Some RFID lock systems utilize software components or interfaces that may have vulnerabilities that can be exploited. This method requires a deep understanding of the lock’s software and may involve programming or hacking techniques to manipulate the system.
It’s important to note that these alternative methods may pose legal and ethical concerns, and their success will heavily depend on the specific lock’s vulnerabilities and your expertise. Always ensure that you have the necessary permission and authorization from the lock’s owner before attempting any of these techniques.
Remember, exploring alternative methods should be done responsibly and within the boundaries of the law. Choosing the appropriate technique requires careful analysis of the lock’s vulnerabilities and an understanding of the potential risks and consequences.
By exploring these alternative methods, you can expand your options and increase your chances of successfully opening an RFID lock without a key in a variety of scenarios.
Conclusion
Opening an RFID lock without a key requires a combination of technical knowledge, specialized tools, and a deep understanding of the lock’s vulnerabilities. While attempting to bypass or manipulate RFID locks may be necessary in certain situations, it’s essential to prioritize legality, ethics, and safety throughout the process.
In this article, we explored various methods for opening RFID locks without a key. Understanding the inner workings of RFID locks, identifying vulnerabilities, choosing the appropriate frequency, utilizing an RFID reader, and spoofing RFID cards are just a few techniques that can be employed to gain access to these locks.
However, it’s important to note that attempting to open RFID locks without proper authorization may violate legal and ethical boundaries. Always ensure that you have the necessary permission from the lock’s owner before proceeding. Engaging in any unauthorized entry or tampering may have severe legal consequences.
Additionally, it’s crucial to evaluate the security measures employed by the lock system. Advanced RFID locks with encryption and sophisticated authentication mechanisms may be significantly more challenging to bypass without a key. Understanding the limitations and potential risks associated with each method is essential for successful and responsible implementation.
Lastly, we must emphasize the importance of utilizing these techniques responsibly. The information provided in this article is intended for educational purposes only. Unauthorized access or malicious intent can harm individuals or compromise security systems. By using this knowledge responsibly and ethically, we can ensure the integrity of RFID lock systems while continuing to explore innovative solutions to security challenges.