Introduction
Smartphones have become an integral part of our lives, containing valuable personal information and acting as a gateway to our digital world. However, there are individuals with malicious intent who seek to exploit vulnerabilities in our devices for their own gain. One such vulnerability lies in Android phones, which can be hacked by sending a simple link. In this article, we will delve into the world of hacking Android phones and discuss the various methods used to accomplish this nefarious task.
Understanding how hackers gain access to Android phones is essential in ensuring the security of our devices. By arming ourselves with knowledge about these hacking methods, we can take the necessary precautions to protect our personal information and maintain the integrity of our devices.
Before we explore the different methods used to hack Android phones, it is important to note that the intention here is to raise awareness and educate readers on the potential risks they might encounter. It is crucial to obtain proper legal authorization before attempting any hacking techniques. Unauthorized access to someone else’s device is a violation of privacy and against the law.
Now, let’s delve into the fascinating yet concerning world of hacking Android phones and explore the various methods used by hackers to gain unauthorized access to these devices.
Understanding the Basics
Before we discuss the methods used to hack Android phones, it’s important to have a basic understanding of the underlying principles. Android is an open-source operating system developed by Google, which allows for flexibility and customization. However, this openness also makes it susceptible to security vulnerabilities.
Hackers take advantage of these vulnerabilities to gain unauthorized access to Android phones. They exploit weaknesses in the software, hardware, or user behavior to achieve their malicious goals. This can range from stealing personal information, including passwords and credit card details, to remotely controlling the device.
One common method used by hackers is social engineering, which involves manipulating individuals to gain access to their devices. This can be achieved through phishing emails, fake websites, or malicious apps that trick users into providing sensitive information or granting unnecessary permissions.
Another common attack vector is malware, which refers to malicious software designed to perform unauthorized actions on a device. Hackers often disguise malware as legitimate apps, enticing users to download and install them. Once installed, malware can perform various actions, such as recording keystrokes, accessing personal files, or even taking control of the device.
Understanding these basic concepts is crucial in protecting ourselves from potential attacks. Vigilance, regular software updates, and cautious app installation are key to maintaining the security of our Android phones.
Choosing the Right Method
When it comes to hacking an Android phone, there are several methods that hackers can employ. The choice of method depends on various factors, including the hacker’s skill level, the targeted device’s vulnerabilities, and the ultimate goal of the attack.
Here are some of the most common methods used to hack Android phones:
- Social Engineering: This method involves manipulating individuals to divulge sensitive information or grant access to their devices. Hackers may use tactics such as phishing emails, fake websites, or fraudulent phone calls to deceive users into providing their login credentials or downloading malware.
- Malware: A common approach is to infect an Android device with malware, which can be disguised as legitimate apps or downloaded from untrustworthy sources. Once installed, the malware can potentially gain full control of the device, allowing hackers to access personal information, record keystrokes, and even take screenshots remotely.
- Exploiting Vulnerabilities: Android devices, like any software, may contain vulnerabilities that hackers can exploit. They can take advantage of weaknesses in the operating system or specific apps to gain unauthorized access. This method often requires advanced technical knowledge and is typically used by more sophisticated hackers.
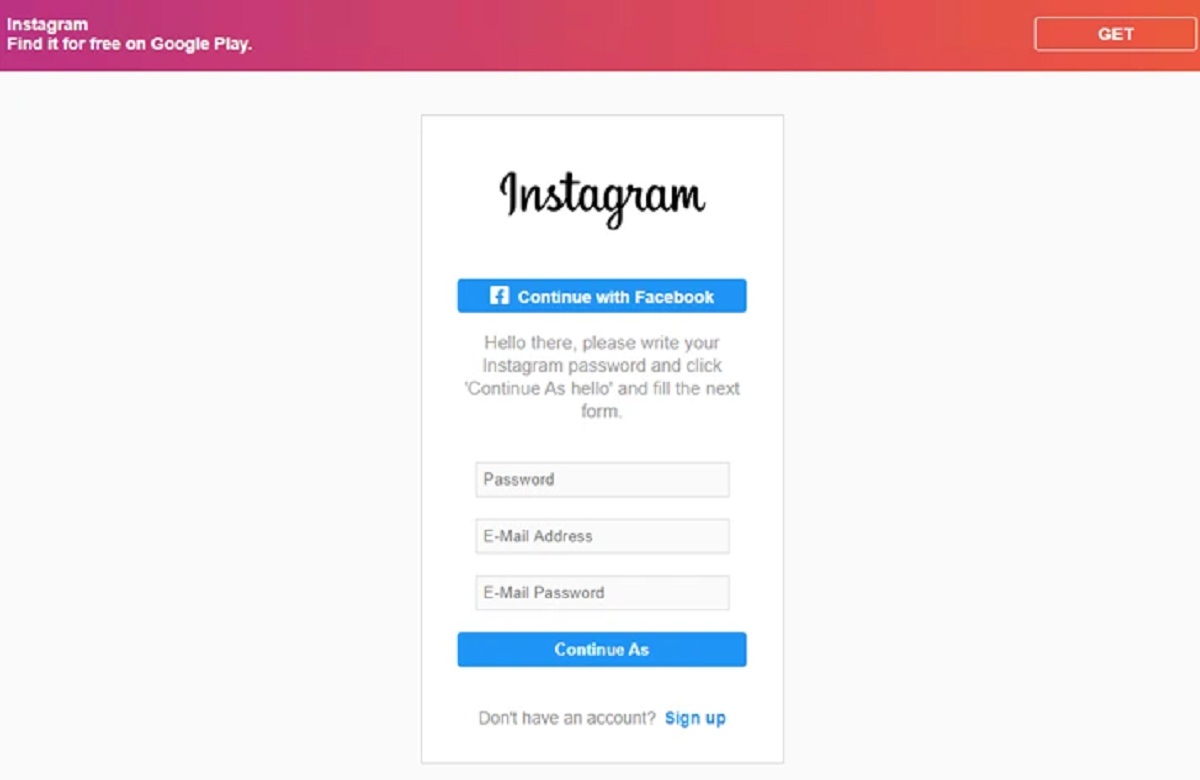
- Phishing Attacks: Hackers may employ phishing attacks to trick users into revealing their login credentials or personal information. This can be done through fake login pages or SMS messages that appear to be from legitimate sources. Once the user enters their information, the hacker can then use it to gain access to the device.
It’s important to note that hacking someone’s Android phone without their consent is illegal and a serious violation of privacy. The purpose of discussing these methods is to raise awareness and promote better security practices to protect ourselves from potential attacks.
When it comes to choosing the right method, hackers will select the approach that aligns with their skills and objectives. As users, we must stay vigilant, practice good security habits, and educate ourselves about potential threats. By doing so, we can minimize the risk of falling victim to these hacking methods and safeguard our Android devices.
Method 1: Creating a Malicious Link
Creating a malicious link is one method that hackers use to gain access to Android phones. This technique often relies on social engineering tactics to trick users into clicking on the malicious link, which can lead to unauthorized access or the installation of malware on the device.
The process usually begins with hackers crafting an enticing message or email that persuades the user to click on the link. This message may appeal to the recipient’s curiosity, offer a tempting reward, or create a sense of urgency. Once the user clicks on the link, they are directed to a compromised website or malicious file.
The goal of creating a malicious link can vary. In some cases, the link may lead the user to a fake website that closely resembles a legitimate one, such as a banking or shopping site. When the user enters their login credentials or personal information, the hackers collect this data for their own malicious purposes.
In other instances, the link may initiate the download and installation of malware onto the user’s device. This malware can then perform various malicious actions, such as stealing sensitive information, recording keystrokes, or giving the hacker remote access to the device.
To protect yourself from falling victim to this method, it is crucial to exercise caution when clicking on links. Be wary of unsolicited messages or emails, especially those from unknown senders. Avoid clicking on links that seem suspicious or ask for personal information. Whenever possible, verify the authenticity of the website or source before entering any sensitive data.
Furthermore, keeping your device’s operating system and apps up to date is essential, as updates often include security patches that fix known vulnerabilities. Installing a reliable antivirus or antimalware software can also provide an additional layer of protection against malicious links and other threats.
Remember, being vigilant and cautious can go a long way in protecting your Android phone from the risks associated with malicious links.
Method 2: Using a Spyware App
Another method commonly used by hackers to gain unauthorized access to Android phones is through the use of spyware apps. Spyware apps are malicious applications that are designed to secretly monitor and collect data from a victim’s device.
These apps often masquerade as legitimate or useful applications, making it difficult for users to detect their presence. Once installed on the target device, the spyware app can silently track various activities, including call logs, text messages, browsing history, social media interactions, and even location data.
One way hackers can get victims to install spyware apps is by disguising them as popular apps or by tricking users into downloading them from untrusted sources. For example, a hacker may create a fake version of a well-known messaging app and distribute it through third-party app stores or phishing websites.
Once the spyware app is installed, it gains access to sensitive data on the device, which is then sent back to the hacker’s server for analysis or exploitation. The hacker can remotely monitor and control the victim’s device, potentially leading to privacy breaches, identity theft, or other malicious activities.
To protect yourself against spyware apps, it is important to be cautious when downloading and installing applications. Stick to trusted sources like the Google Play Store and avoid downloading apps from unknown or unverified sources. Before installing any app, carefully review the permissions it requests and consider whether they are necessary for its intended functionality.
Regularly reviewing the list of installed apps on your device and uninstalling any suspicious or unrecognized apps can also help mitigate the risk of spyware. It is also recommended to keep your device’s software and security patches up to date, as these updates often include fixes for known vulnerabilities exploited by spyware.
By practicing safe app installation habits and maintaining a vigilant approach, you can significantly reduce the risk of falling victim to spyware apps and protect your Android phone from unauthorized access.
Method 3: Exploiting Vulnerabilities
Exploiting vulnerabilities is a method often employed by more advanced hackers to gain unauthorized access to Android phones. Android, like any operating system, can have its fair share of vulnerabilities, whether in the operating system itself or in specific apps installed on the device.
Hackers who exploit vulnerabilities target weaknesses in the security infrastructure of the device or the apps it contains. They may employ various techniques, such as code injection, buffer overflow attacks, or using known exploits to take advantage of these vulnerabilities.
Once a vulnerability is exploited successfully, the hacker can gain full or partial control over the victim’s device. They may be able to execute remote commands, access personal data, manipulate the device’s settings, or even install additional malware for further exploitation.
It’s worth noting that these vulnerabilities are not always the result of carelessness on the part of the user. They can exist in the operating system itself or arise from flaws in the development of specific apps. To combat this, Google regularly releases security patches and updates to address known vulnerabilities.
As a user, you can protect your Android phone from such attacks by ensuring that your device is always up to date with the latest security patches. Regularly check for system updates and install them promptly to ensure that any known vulnerabilities are promptly patched.
Additionally, exercise caution when downloading and installing apps from unofficial sources or unfamiliar developers. Stick to reputable app stores like the Google Play Store, as they have stringent security measures in place to weed out malicious apps.
Lastly, consider using security features such as app permissions and app verification to control access to sensitive data and prevent unauthorized installations. By being proactive about installing updates and practicing safe app usage, you can minimize the risk of falling victim to hackers who exploit vulnerabilities.
Method 4: Crafting a Malicious App
Crafting a malicious app is another method employed by hackers to gain unauthorized access to Android phones. This method involves creating an app that appears legitimate but contains hidden malicious functionalities.
Hackers may develop apps that mimic popular games, utility tools, or even security applications. These malicious apps are often distributed through unofficial websites, third-party app stores, or malicious links. Unsuspecting users who download and install these apps unknowingly introduce a security risk onto their devices.
Once installed, the malicious app can perform a variety of nefarious activities. It may steal sensitive information such as login credentials, banking details, or personal data. The app can also secretly record audio or video, track the user’s location, or establish unauthorized communication channels.
To make matters worse, some malicious apps may have the ability to disguise their presence, making them difficult to detect and remove. They may evade antivirus software or even manipulate the device’s operating system to persistently stay installed and active.
To protect yourself from malicious apps, it is important to only download apps from reputable and trusted sources like the Google Play Store. Stick to well-known developers and read user reviews and ratings before installing any app.
Take the time to review the permissions requested by an app before installation. If an app requests unnecessary permissions that seem unrelated to its stated purpose, it could be a red flag and an indication of malicious intent. Exercise caution and consider whether granting those permissions is truly necessary.
Regularly review the list of installed apps on your device and uninstall any suspicious or unrecognized apps. Keep your device’s software up to date with the latest security patches as well, as these patches often address known vulnerabilities that malicious apps may exploit.
By being selective in your app choices and staying vigilant, you can minimize the risk of falling victim to crafted malicious apps and protect the security of your Android phone.
Ensuring Success
Protecting your Android phone from hacking attempts requires taking proactive steps to ensure the security and integrity of your device. By following these essential practices, you can greatly reduce the risk of unauthorized access and potential data breaches:
1. Install Security Updates: Keeping your Android device up to date with the latest security patches is crucial. Regularly check for system updates and install them promptly to ensure that any known vulnerabilities are patched.
2. Be Cautious with App Downloads: Stick to reputable sources like the Google Play Store for downloading apps. Be cautious of third-party or unverified app stores, as they may host malicious apps. Read user reviews, check app ratings, and be mindful of the permissions requested by the app before installation.
3. Use Strong Passwords and Two-Factor Authentication: Choose complex, unique passwords for your device and accounts. Enable two-factor authentication whenever possible to add an extra layer of security. This helps protect against unauthorized access to your device and accounts, even if your password is compromised.
4. Be Wary of Suspicious Links: Do not click on suspicious links in emails, messages, or websites. Hackers often use social engineering techniques to deceive users into clicking on malicious links. Verify the source and validity of any links before clicking on them.
5. Install a Reliable Security App: Consider using a reputable antivirus or antimalware app to protect your Android device from potential threats. These apps can scan for and detect malicious apps, files, or activities on your device.
6. Regularly Review App Permissions: Check the permissions requested by the apps you install. If an app requests unnecessary permissions that seem unrelated to its functionality, consider it a potential red flag and exercise caution.
7. Backup Your Data: Regularly back up your important data to an external source or to the cloud. In the event of a successful hack or data loss, having backups ensures that you can recover your important information.
8. Educate Yourself: Stay informed about current cybersecurity threats and best practices. Keep up with news and updates regarding Android security to understand the latest risks and preventive measures.
Adhering to these practices can significantly enhance the security of your Android phone and mitigate the risk of hacking attempts. Remember, maintaining a vigilant approach and being proactive are key to ensuring the success of your efforts in protecting your device and personal information.
Conclusion
In today’s digital age, the security of our Android phones is of utmost importance. Hackers continue to find new ways to exploit vulnerabilities and gain unauthorized access to our devices, putting our personal information and privacy at risk.
By understanding the various methods hackers use to hack Android phones, we can better protect ourselves and take the necessary precautions to ensure our devices remain secure. Whether it’s through social engineering, malicious links, spyware apps, exploiting vulnerabilities, or crafting malicious apps, the tactics used by hackers are varied and continuously evolving.
To safeguard your Android phone, it is crucial to practice good security habits, such as being cautious with app downloads, installing security updates promptly, and regularly reviewing app permissions. Additionally, a reliable antivirus or antimalware app can provide an extra layer of protection against potential threats.
Ultimately, staying informed, being proactive, and exercising caution are essential in maintaining the security of your Android phone. By implementing these practices and staying vigilant, you can significantly reduce the risk of falling victim to hacking attempts and keep your personal information safe.
Remember, protecting your Android phone is an ongoing process. Stay up to date with the latest security practices and remain aware of the potential risks associated with using your device. By doing so, you can enjoy the benefits of your Android phone while keeping your personal data secure.