Introduction
Wireless routers have become an essential part of our daily lives, providing us with convenient Wi-Fi access to the internet. However, many users overlook the importance of securing their wireless router passwords, leaving them vulnerable to unauthorized access. With the ever-increasing dependence on wireless networks, it has become crucial to understand the methods used to crack wireless router passwords and take proactive measures to protect ourselves.
In this article, we will explore the various techniques employed by hackers to crack wireless router passwords. By gaining this knowledge, you will be better equipped to secure your wireless network and prevent unauthorized access. We will discuss common methods such as brute force attacks, dictionary attacks, exploiting router vulnerabilities, and utilizing WPS (Wi-Fi Protected Setup) attacks.
It’s important to note that the information provided in this article is solely intended for educational purposes and to raise awareness about the potential risks associated with weak wireless router passwords. Any attempt to crack someone else’s wireless router password without their consent is illegal and unethical.
Understanding the methods used by hackers to crack wireless passwords can help you realize the importance of creating strong and secure passwords for your wireless router. By implementing best practices for wireless router security, you can protect your sensitive data and ensure that only authorized individuals can access your network.
It is vital to stay informed and up-to-date with the latest security measures and updates provided by your router manufacturer. By following the recommended guidelines, you can significantly reduce the risk of falling victim to malicious attacks and protect your wireless network from unauthorized access.
Understanding Wireless Router Passwords
Before delving into the methods used to crack wireless router passwords, it’s essential to have a solid understanding of what these passwords are and how they work. A wireless router password, also known as a Wi-Fi password or network key, is a security measure designed to restrict access to your wireless network.
When you set up a wireless router, you are prompted to create a password. This password acts as a barrier, preventing unauthorized users from connecting to your network and potentially gaining access to your personal or sensitive information.
Wireless router passwords are typically composed of a combination of letters, numbers, and symbols. It’s crucial to choose a strong and unique password that is not easily guessable. Avoid using common passwords like “password” or “123456,” as these are the first passwords that hackers try when attempting to gain access to a network.
Additionally, it’s important to note that there are two types of passwords associated with a wireless router. The first is the administrative password, which grants access to the router’s settings and configuration options. The second is the Wi-Fi network password, which allows devices to connect to your wireless network.
By default, most wireless routers come with a pre-set username and password combination for administrative access. It is crucial to change these default credentials as they are widely known among hackers and can make your router vulnerable to unauthorized access.
Understanding the significance of wireless router passwords is vital in realizing the importance of keeping them secure. Failure to protect your wireless network with a robust password can open the door to various security threats, including unauthorized internet usage, data theft, and even the compromise of other devices connected to your network.
Now that we have a solid foundation of knowledge regarding wireless router passwords, let’s explore the different methods used by hackers to crack these passwords and gain unauthorized access to wireless networks. With this understanding, you will be better equipped to take proactive measures in securing your network.
Common Methods for Cracking Wireless Router Passwords
There are several methods that hackers commonly use to crack wireless router passwords. Understanding these methods can help you identify potential vulnerabilities in your network security and take proactive measures to protect yourself. Let’s take a closer look at these common methods:
- Brute Force Attacks: Brute force attacks are a straightforward yet time-consuming method used to crack passwords. Hackers use software to systematically try every possible combination of characters until they find the correct password. This method can be effective against weak passwords that are short in length or use common dictionary words.
- Dictionary Attacks: In dictionary attacks, hackers use specialized software to try a list of commonly used words or phrases as potential passwords. This method is effective against users who use easily guessable passwords, such as common words or phrases, names, or dates. Hackers leverage existing dictionaries and wordlists to automate the process and increase the chances of success.
- Exploiting Router Vulnerabilities: Wireless routers, like any other technology, can have vulnerabilities that hackers can exploit to gain unauthorized access. These vulnerabilities can occur due to outdated firmware, software bugs, or misconfigurations. Hackers exploit these weaknesses by deploying specialized tools or techniques to bypass the router’s security measures and gain access to the network.
- Using WPS (Wi-Fi Protected Setup) Attacks: Wi-Fi Protected Setup is a feature present in many routers that simplifies the process of connecting devices to a wireless network. However, it can also be an avenue for attackers to crack the router’s password. By exploiting vulnerabilities in the WPS implementation, hackers can gain unauthorized access to the network without needing to crack the actual Wi-Fi password.
It’s important to note that hackers employ a combination of these methods and adapt their techniques based on the specific circumstances. They may use a combination of brute force and dictionary attacks or exploit vulnerabilities in conjunction with other methods to maximize their chances of success.
Now that we have an understanding of the common methods used to crack wireless router passwords, let’s explore how hackers gather information to launch these attacks, as well as the preventive measures that can help protect your network from such breaches.
Gathering Information
Before attempting to crack a wireless router password, hackers often gather information about the target network and its devices. This information helps them in planning and executing their attacks more effectively. Here are some common methods used by hackers to gather information:
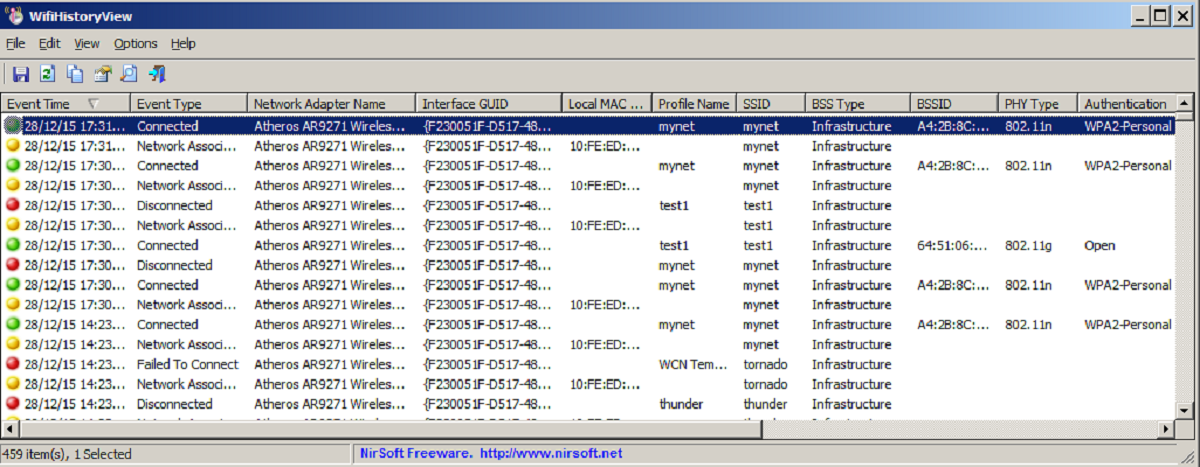
- Wi-Fi Network Scanning: Hackers perform Wi-Fi network scanning to identify nearby wireless networks. They can use specialized tools to detect and collect information such as network names (SSIDs), signal strength, encryption types, and the number of connected devices. This information gives them insights into potential targets.
- Network Packet Analysis: By capturing and analyzing network packets, hackers can gather information about the devices connected to a network. They can identify the operating systems, MAC addresses, and other details that help them in determining possible vulnerabilities.
- Social Engineering: Hackers may resort to social engineering tactics to gather information. This includes manipulating individuals into disclosing crucial network details, such as the Wi-Fi password, through tactics like phishing emails, phone calls, or impersonating technical support personnel.
- Publicly Available Information: Hackers can search for publicly available information about the target, such as social media profiles, websites, or forums. They may find clues about the potential passwords or security practices being followed.
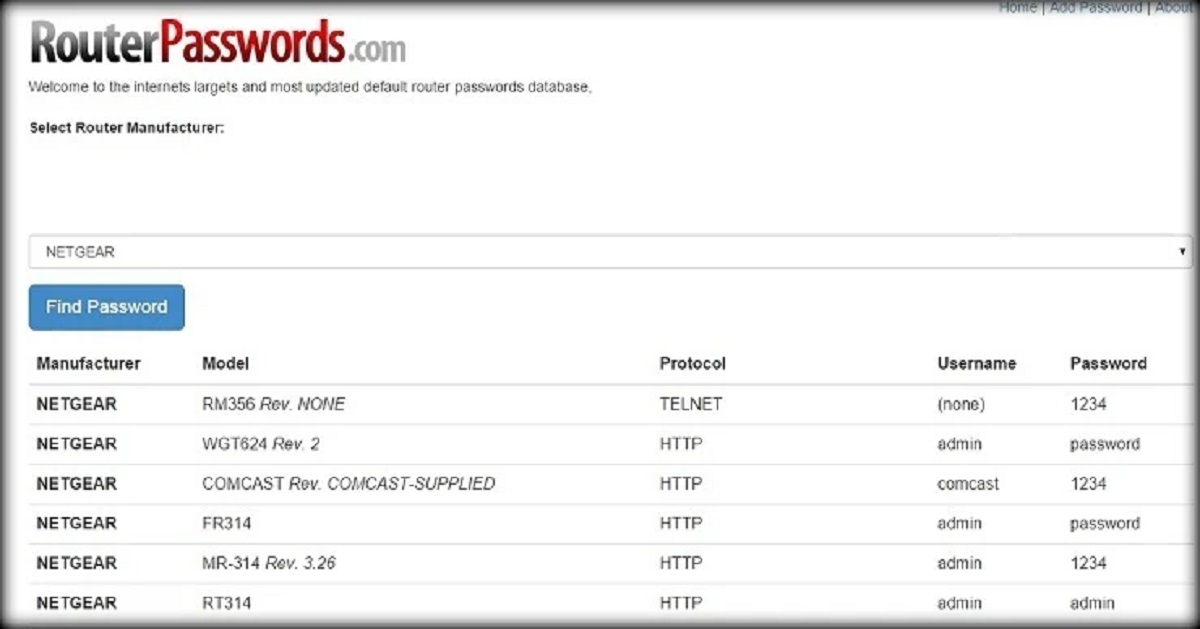
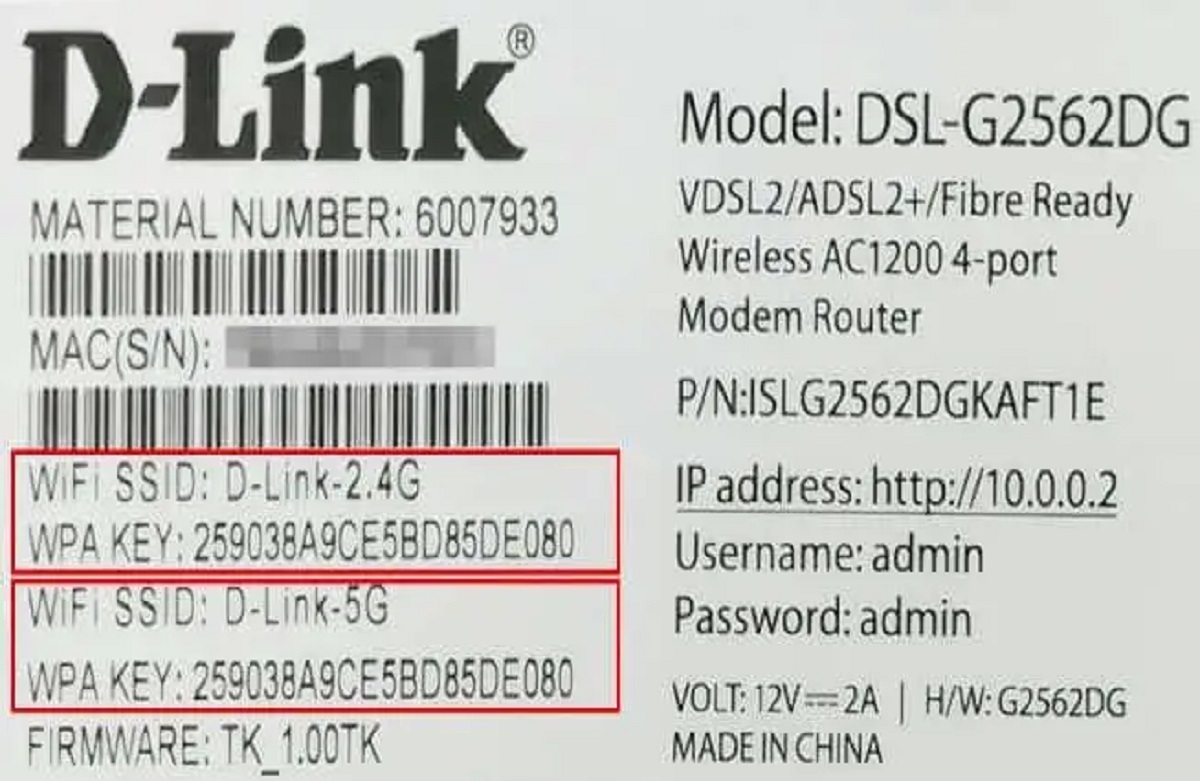
- Default Router Credentials: Some users fail to change the default credentials of their routers, making it easier for hackers. Attackers can find common default usernames and passwords associated with specific router models and attempt to use them to gain unauthorized access.
By gathering this information, hackers can gain insights into potential vulnerabilities and weaknesses within a network. This knowledge allows them to tailor their attacks and increase their chances of successfully cracking the wireless router password.
As a network owner, it is crucial to understand the methods used by hackers to gather information. By being aware of these tactics, you can take appropriate measures to protect your network, such as regularly updating your router’s firmware, using complex and unique passwords, and being cautious about sharing network details with unauthorized individuals.
Now that we have explored the methods used by hackers to gather information, let’s move on to the techniques they employ to crack wireless router passwords, including brute force attacks, dictionary attacks, and exploiting vulnerabilities.
Using Brute Force Attacks
Brute force attacks are a common method used by hackers to crack wireless router passwords. This method involves systematically trying every possible combination of characters until the correct password is found. Although time-consuming, brute force attacks can be successful against weak or easily guessable passwords. Here’s how hackers execute brute force attacks:
- Password Length and Complexity: Hackers start by determining the length of the password they need to crack. Typically, longer passwords are more secure, as they offer a larger pool of possible combinations. They also consider whether the password contains a combination of uppercase letters, lowercase letters, numbers, or special characters, as this affects the complexity of the attack.
- Automated Tools: Hackers use specialized software or scripts that automate the process of trying various password combinations. These tools leverage CPU or GPU processing power to generate and test a vast number of possible passwords in a short period.
- Iterations and Patterns: Brute force attacks follow a pattern that gradually exhausts every possible combination. Hackers start with common passwords, dictionary words, or easily guessable patterns. They then move on to trying every possible combination of characters, iterating through different lengths and combinations until the correct password is found.
- Time and Resources: The time required to crack a password using brute force attacks depends on several factors, including password complexity, length, available computing resources, and the processing power of the attacker’s hardware. Longer and more complex passwords can take an incredibly long time to crack, especially with strong encryption methods.
To protect your wireless network from brute force attacks, it is crucial to create strong and complex passwords. Use a combination of uppercase and lowercase letters, numbers, and special characters. Additionally, make sure your password is of sufficient length, as longer passwords are more challenging to crack.
Router manufacturers often implement security measures to mitigate brute force attacks. These measures include introducing delays, locking out users after a certain number of failed login attempts, or implementing two-factor authentication. Check your router settings to enable these security features and protect your network from unauthorized access.
It’s important to note that even with strong passwords and security measures in place, there is always a possibility that determined attackers can crack a password through brute force attacks. Therefore, it is best practice to regularly update your router’s firmware, monitor your network for any suspicious activity, and employ additional layers of security, such as network intrusion detection systems.
Now that we have explored brute force attacks, let’s move on to another common method used by hackers: dictionary attacks.
Using Dictionary Attacks
Dictionary attacks are another common method used by hackers to crack wireless router passwords. Unlike brute force attacks that systematically try every possible combination of characters, dictionary attacks rely on pre-existing lists of commonly used words, phrases, and passwords. Here’s how hackers execute dictionary attacks:
- Creating Wordlists: Hackers compile wordlists that consist of commonly used passwords, dictionary words, names, dates, and other easily guessable combinations. These wordlists can be obtained from various sources, including leaked password databases, previous data breaches, or publicly available password lists.
- Automated Tools: Hackers use specialized software or scripts that automate the process of trying each word from their wordlist as a potential password. This significantly speeds up the process and increases the chances of finding a match.
- Variations and Techniques: To improve their chances of success, hackers may employ various techniques during dictionary attacks. They can modify words by adding numbers or special characters, perform common substitutions (e.g., replacing “e” with “3” or “i” with “1”), or concatenate multiple words to create passwords.
- Language-Specific Wordlists: Hackers may also tailor their wordlists to target specific regions or languages. By considering the cultural and linguistic preferences of the target audience, attackers increase their chances of cracking passwords that align with common choices in that particular language or region.
To protect your wireless network from dictionary attacks, it is crucial to create complex passwords that are not easily guessable. Avoid using common dictionary words, known phrases, names, or easily predictable patterns. Additionally, regularly update your passwords to make them less susceptible to being cracked by dictionary attacks.
Router manufacturers often implement security measures to mitigate dictionary attacks. These measures include rate-limiting login attempts, blocking IP addresses after a certain number of failed login attempts, and implementing additional layers of authentication, such as CAPTCHA.
You can further enhance your network security by using long and complex passwords that don’t rely on easily guessable words. Consider using a random combination of uppercase and lowercase letters, numbers, and special characters. Additionally, enabling two-factor authentication adds an extra layer of security to your network.
While dictionary attacks can be successful against weak or common passwords, implementing strong and unique passwords significantly reduces the risk of falling victim to such attacks. Now that we have explored dictionary attacks, let’s move on to another method used by hackers: exploiting router vulnerabilities.
Exploiting Router Vulnerabilities
Exploiting vulnerabilities in wireless routers is a method commonly used by hackers to gain unauthorized access to networks. These vulnerabilities can exist due to outdated firmware, software bugs, misconfigurations, or known security weaknesses within the router’s operating system. Here’s how hackers exploit router vulnerabilities:
- Identifying Vulnerabilities: Hackers actively search for known vulnerabilities in popular router models and firmware versions. They leverage public sources, security advisories, or online forums to gather information about potential weaknesses that can be exploited.
- Exploit Tools and Scripts: Hackers often use pre-existing attack tools, scripts, or even write their own code to take advantage of the identified vulnerabilities. These tools automate the exploitation process, allowing hackers to gain unauthorized access to the router’s settings or bypass security measures.
- Default and Weak Credentials: Routers often come with default usernames and passwords that are widely known among hackers. Expanding on this, weak or easily guessable credentials can also be exploited to gain unauthorized access to a router.
- Remote Code Execution: In some cases, hackers can exploit vulnerabilities to execute malicious code on the router remotely. This gives them full control over the device, allowing them to manipulate settings, intercept traffic, or launch further attacks within the network.
- Firmware Exploitation: Outdated or unpatched firmware can be a significant vulnerability. Hackers can exploit these vulnerabilities to gain unauthorized access or install malicious firmware that grants them control over the router and the network.
To protect your router from exploitation of vulnerabilities, it is crucial to regularly update your router’s firmware. Router manufacturers often release firmware updates that address known vulnerabilities and strengthen the security of their devices. Additionally, it is recommended to change the default administrative credentials and use strong, unique passwords.
Staying informed about the latest security advisories and patches released by the router manufacturer is essential. Regularly check the manufacturer’s website or subscribe to security alerts to ensure you receive updates about any identified vulnerabilities or security patches.
By taking these preventive measures, you can significantly reduce the risk of falling victim to attacks that exploit router vulnerabilities. However, it is important to note that attackers continuously evolve their methods, and new vulnerabilities may emerge over time. Therefore, it is crucial to stay vigilant, keep your router updated, and follow best practices for securing your network.
Now that we have explored the method of exploiting router vulnerabilities, let’s move on to another common method used by hackers: using WPS (Wi-Fi Protected Setup) attacks.
Using WPS (Wi-Fi Protected Setup) Attacks
Wi-Fi Protected Setup (WPS) is a feature available on many wireless routers that simplifies the process of connecting devices to a wireless network. Unfortunately, this convenience can also be exploited by hackers to gain unauthorized access to a network without cracking the actual Wi-Fi password. Here’s how hackers employ WPS attacks:
- WPS PIN Enumeration: In a WPS PIN enumeration attack, hackers attempt to guess or brute force the eight-digit PIN used by WPS to authenticate new devices on the network. By exploiting vulnerabilities or weak implementations of WPS in routers, hackers can eventually guess the PIN and gain unauthorized access.
- PIN Bruteforce: Hackers automate the process of trying every possible combination of the eight-digit PIN to find the correct one. They leverage specialized tools or scripts that iterate through all possible combinations, taking advantage of any vulnerabilities or weaknesses in the WPS implementation.
- PIN Reaver Attacks: Reaver is a popular tool used by hackers for WPS attacks. It leverages online or offline brute force techniques to exploit known vulnerabilities in WPS implementations. Hackers utilize Reaver to guess the WPS PIN, bypass the security measures, and gain access to the network.
- Pixie Dust Attack: The Pixie Dust attack is another method used by hackers to exploit WPS vulnerabilities. It targets vulnerable WPS implementations and attempts to extract crucial information needed to recover the network’s original WPA/WPA2 passphrase, thus gaining unauthorized access to the network.
To protect your network from WPS attacks, you can disable the WPS feature on your router. This can typically be done through the router’s settings or administration interface. Disabling WPS removes the possibility of an attacker using the WPS PIN enumeration method to gain unauthorized access to your network.
It is also crucial to ensure your router’s firmware is up to date. Router manufacturers often release firmware updates to address known vulnerabilities in the WPS implementation or strengthen the security of the feature.
By disabling WPS and keeping your router’s firmware up to date, you can significantly reduce the risk of falling victim to WPS attacks. It’s important to stay informed about any new vulnerabilities or security advisories related to WPS and apply the necessary security measures.
Now that we have explored the method of using WPS attacks, let’s move on to discussing various tools used by hackers to crack wireless router passwords.
Router Password Cracking Tools
Hackers rely on a variety of specialized tools and software to crack wireless router passwords. These tools automate the process of executing different attacks, increasing the efficiency and success rate of their hacking attempts. Here are some commonly used router password cracking tools:
- Aircrack-ng: Aircrack-ng is a popular network security tool used by hackers for password cracking. It includes various components, such as packet sniffers, network detectors, and WPA/WPA2-PSK password cracking tools. Aircrack-ng focuses on capturing network packets and performing dictionary or brute force attacks on captured handshakes to crack passwords.
- Hashcat: Hashcat is a powerful password cracking tool capable of cracking a wide range of hash types, including those used by popular wireless routers. It supports various attack modes, including brute force, dictionary, and rule-based attacks. Hackers can leverage Hashcat to crack passwords by utilizing the processing power of modern CPUs and GPUs.
- Fern Wi-Fi Cracker: Fern Wi-Fi Cracker is a graphical user interface (GUI) tool used for wireless network security assessment. It combines several tools, including Aircrack-ng and Wifite, to automate the process of capturing packets, deauthenticating clients, and executing dictionary and brute force attacks against captured handshakes.
- RouterSploit: RouterSploit is an open-source framework that focuses on router-based vulnerabilities and exploits. It includes a wide range of modules that target specific router models or vulnerabilities, making it easier for hackers to execute targeted attacks and gain unauthorized access to routers.
- John the Ripper (JTR): John the Ripper is a versatile password cracking tool known for its speed and flexibility. It supports various attack modes, including dictionary, brute force, and hybrid attacks. While it is primarily used for cracking password hashes, JTR can be utilized to crack passwords captured from router configurations or handshakes.
It’s important to note that these tools, although primarily used for legitimate purposes like network auditing and penetration testing, can be misused by malicious individuals. As a responsible user, it is essential to use these tools for lawful and ethical purposes only.
To protect your network against such attacks, ensure that you are using strong, complex passwords and updating your router’s firmware regularly. Understanding the tools hackers use can help you remain vigilant and take proactive measures to secure your network.
Now that we have explored router password cracking tools, let’s move on to discussing preventive measures you can take to protect your wireless router password from being cracked.
Preventing Wireless Router Password Cracking
To protect your wireless router password from being cracked, it is crucial to implement preventive measures and establish strong security practices. Here are some key steps to help prevent wireless router password cracking:
- Create Strong Passwords: Choose a password that is complex, unique, and not easily guessable. Use a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using common dictionary words or easily predictable patterns.
- Regularly Update Router Firmware: Router manufacturers frequently release firmware updates that address known vulnerabilities and strengthen security. Regularly check for firmware updates and install them promptly to protect against potential exploits.
- Disable WPS: Wi-Fi Protected Setup (WPS) can be a vulnerability that hackers exploit to gain unauthorized access. Disable the WPS feature on your router to eliminate this attack avenue entirely.
- Change Default Credentials: Replace the default administrative username and password with a unique, strong password. Default credentials are widely known among hackers and can provide easy access to your router.
- Enable Network Encryption: Use strong encryption protocols like WPA2 or WPA3 to secure your Wi-Fi network. Avoid using weak encryption methods that can be easily compromised.
- Enable Firewall: Activate the built-in firewall on your router to add an extra layer of protection. Firewalls can help block unauthorized access attempts and prevent malicious activities.
- Use MAC Address Filtering: Implement MAC address filtering on your router to restrict access only to devices with known MAC addresses. This prevents unauthorized devices from connecting to your network.
- Monitor Network Activity: Regularly check the logs and activity on your router for any suspicious or unauthorized access attempts. Monitor connected devices to ensure they are legitimate and have authorized access.
- Be Cautious with Personal Information: Avoid sharing your wireless network details, such as SSID or password, with unauthorized individuals. Be cautious while providing personal information online and protect yourself from social engineering attacks.
- Educate Yourself and Users: Stay informed about the latest security practices and threats in the realm of wireless network security. Educate yourself and other users about the importance of strong passwords, firmware updates, and other security measures.
By implementing these preventive measures, you can significantly reduce the risk of your wireless router password being cracked. It is essential to remember that ensuring the security of your network is an ongoing process. Stay vigilant, keep your router updated, and adapt to changing security needs to maintain a secure and protected wireless network.
Now that we have explored preventive measures, let’s summarize the key points discussed in this article.