Introduction
The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting everyday objects to the internet and enabling seamless communication between devices. However, when it comes to IoT devices behind Network Address Translation (NAT), accessing them from external networks becomes a challenge.
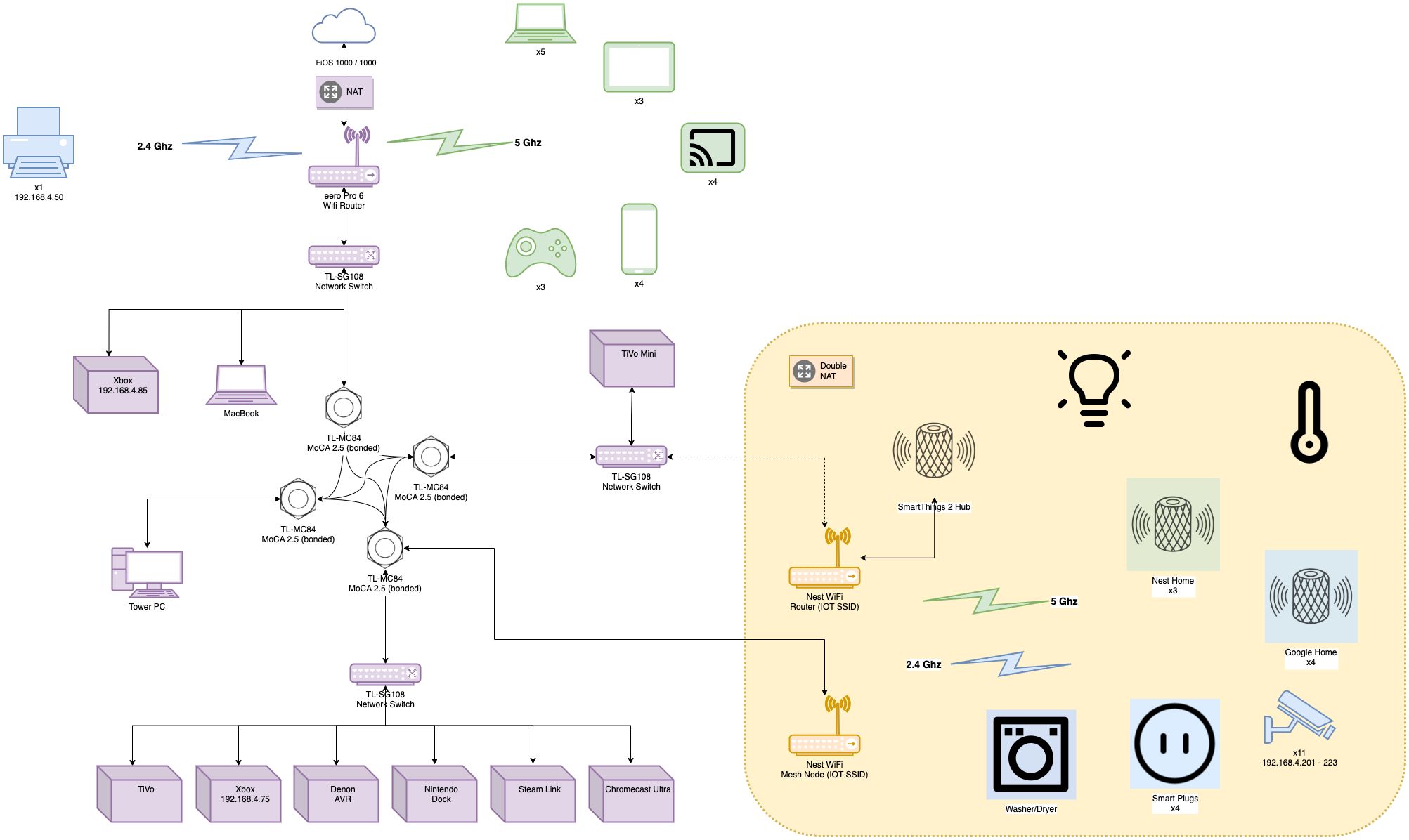
NAT is a common networking technique that allows multiple devices in a local network to share a single public IP address. This offers a layer of security by hiding the internal IP addresses from external networks. While NAT provides several benefits, it can also hinder direct access to IoT devices, posing challenges for remote management and control.
In this article, we will explore the various methods available for accessing an IoT device behind NAT. We will delve into the complexities of NAT and shed light on the potential solutions to overcome this hurdle. By understanding these methods, you can gain the necessary knowledge to effectively access and manage your IoT devices remotely.
So, if you’ve ever wondered how to get an IoT device behind NAT, continue reading to discover the different approaches and techniques that can help you establish a connection and unlock the full potential of your IoT setup.
Understanding NAT and its implications in IoT
Network Address Translation (NAT) is a technique widely used in networking to allow multiple devices in a local network to share a single public IP address. It acts as a mediator between the private local network and the public internet, translating the private IP addresses of devices into the public IP address of the NAT router. While NAT offers benefits such as improved security and conservation of IP addresses, it introduces complexities when it comes to accessing IoT devices.
In the context of IoT, NAT poses challenges for remote management and control of devices. Since each IoT device is assigned a private IP address within the local network, direct access from the internet becomes difficult. This means that controlling or monitoring an IoT device from a remote location becomes problematic.
Furthermore, the dynamic nature of IP address assignments in NAT can cause additional complications. As devices connect and disconnect from the network, their private IP addresses may change, making it challenging to establish a stable and reliable connection.
The implications of NAT on IoT include the inability to connect to devices from outside the local network, hindered data collection and monitoring, restricted remote configuration and updates, and limited access to real-time notifications and alerts. These limitations can hinder the full potential of IoT applications, which rely on seamless connectivity and remote management for optimal functionality.
To overcome these challenges, various methods have been developed, each with its own advantages and considerations. In the next sections, we will explore several techniques for accessing IoT devices behind NAT and discuss their strengths and limitations. By understanding these methods, you can make an informed decision based on your specific requirements and circumstances.
Challenges of accessing an IoT device behind NAT
Accessing an IoT device behind Network Address Translation (NAT) poses several challenges, primarily due to the limitations imposed by the NAT router. These challenges include the following:
1. Addressing and connectivity: NAT assigns private IP addresses to devices within the local network, making them inaccessible from outside the network. This hinders the ability to establish direct connections with IoT devices, limiting remote access and control.
2. Dynamic IP assignments: NAT routers often assign IP addresses dynamically, meaning that the private IP address of an IoT device may change over time. This dynamic nature of IP assignments complicates remote access, as the device’s address needs to be constantly updated.
3. Port blocking and restrictions: NAT routers typically implement security measures that block incoming traffic by default. This can result in blocked ports, making it difficult to establish direct connections to IoT devices.
4. Lack of public IP: NAT allows multiple devices to share a single public IP address, which means that the IoT device does not have a unique public IP. This lack of a public IP address further complicates remote access and restricts the device’s visibility on the internet.
5. Firewall configurations: Many NAT routers have built-in firewalls that can restrict incoming connections to IoT devices. Configuring the router’s firewall settings to allow traffic to specific ports can be a complex and technical task.
6. Security concerns: Opening ports and exposing IoT devices directly to the internet can introduce security risks. Attackers may attempt to exploit vulnerabilities in IoT devices or gain unauthorized access.
These challenges can significantly impact the functionality and usability of IoT devices. For businesses or individuals hoping to remotely manage and control their IoT devices, overcoming these obstacles is crucial.
In the following sections, we will explore different methods that can be employed to bypass the challenges of accessing an IoT device behind NAT. These methods offer various approaches to establish remote access, improve connectivity, and overcome the limitations imposed by NAT routers.
Different methods to get an IoT device behind NAT
When it comes to accessing an IoT device behind Network Address Translation (NAT), several methods can help establish a connection and overcome the challenges posed by NAT routers. Let’s explore some of these methods:
1. Port Forwarding: Port forwarding involves configuring the NAT router to forward specific incoming traffic from a public IP address to the internal IP address of the IoT device. This method allows external devices to access the IoT device through the specified port.
2. Universal Plug and Play (UPnP): UPnP is a protocol that enables IoT devices to automatically configure port forwarding on NAT routers. By implementing UPnP, IoT devices can request the router to open the necessary ports for external access.
3. Dynamic DNS: Dynamic DNS involves associating a domain name with the dynamic IP address assigned to the NAT router. This method allows users to access their IoT devices using a consistent domain name, regardless of the changing IP address.
4. Virtual Private Networks (VPNs): Creating a secure VPN connection allows users to establish a private network between their remote device and the local network where the IoT device resides. This method provides a secure route for accessing IoT devices behind NAT.
5. Reverse SSH Tunneling: Reverse SSH tunneling involves initiating a connection from the IoT device to a remote server outside the local network. This creates a secure tunnel through which external devices can access the IoT device by connecting to the remote server.
6. Cloud-based IoT platforms: Some IoT platforms offer cloud-based solutions that handle the connectivity challenges of accessing IoT devices behind NAT. These platforms act as intermediaries, facilitating secure and seamless communication between remote devices and IoT devices on the local network.
Each method has its own advantages and considerations, depending on factors such as security requirements, technical expertise, and the specific use case. By choosing the most suitable method, users can ensure efficient and reliable access to their IoT devices and maximize their benefits.
In the following sections, we will explore each of these methods in more detail, providing step-by-step instructions and discussing their strengths, limitations, and potential use cases.
Method 1: Port Forwarding
Port forwarding is a popular method for accessing an IoT device behind Network Address Translation (NAT). It involves configuring the NAT router to forward specific incoming traffic from a public IP address to the internal IP address of the IoT device, allowing external devices to access the IoT device through a specified port.
Here’s how port forwarding works:
1. Identify the internal IP address of the IoT device: To set up port forwarding, you need to know the internal IP address of the IoT device. This can usually be found in the device’s network settings or through the router’s connected devices list.
2. Access the NAT router’s configuration: Open a web browser and enter the router’s IP address in the address bar. Log in to the router’s configuration interface using the administrator credentials.
3. Locate the port forwarding settings: The location of port forwarding settings may vary depending on the router model and manufacturer. Look for options like “Port Forwarding,” “Virtual Servers,” or “Applications.”
4. Add a new port forwarding rule: Create a new port forwarding rule by specifying the internal IP address of the IoT device, the port number to be forwarded, and the protocol (TCP, UDP, or both). You may also need to provide a description for the rule.
5. Save the configuration: Once the port forwarding rule is set up, save the configuration changes in the router’s interface. The router will then start forwarding incoming traffic on the specified port to the internal IP address of the IoT device.
It’s important to note that port forwarding exposes the IoT device to the internet, potentially increasing the security risks. To mitigate these risks, it is recommended to:
– Use strong and unique passwords for both the router and the IoT device.
– Regularly update the firmware of both the router and the IoT device to patch any security vulnerabilities.
– Monitor and log incoming connections to detect any suspicious activity.
– Keep the IoT device’s software and applications up to date to ensure optimal security.
Port forwarding is a straightforward method for accessing IoT devices behind NAT, providing direct external access to the devices. However, it requires some technical knowledge and may not be suitable for users concerned about potential security risks or those who have limited control over the router’s configuration.
In the next section, we will explore another method, Universal Plug and Play (UPnP), which offers an automated approach to configure port forwarding on NAT routers.
Method 2: Universal Plug and Play (UPnP)
Universal Plug and Play (UPnP) is a protocol that enables IoT devices to automatically configure port forwarding on Network Address Translation (NAT) routers. It provides a simple and automated approach to establish external access to IoT devices without the need for manual configuration.
Here’s how UPnP works:
1. Check router and device compatibility: Ensure that both the NAT router and the IoT device support UPnP. Most modern routers and IoT devices have built-in UPnP capabilities. However, it’s important to verify compatibility before proceeding.
2. Enable UPnP on the router: Access the router’s configuration interface through a web browser and look for the UPnP settings. Enable UPnP if it’s not already enabled. This will allow the router to automatically configure the necessary port forwarding rules for UPnP-compatible devices.
3. Configure the IoT device: Enable UPnP on the IoT device. This option is typically found in the device’s network settings. Once enabled, the device will communicate with the router to automatically request the required port forwarding.
4. Verify port forwarding: After configuring UPnP on both the router and the IoT device, verify that the necessary port forwarding rules have been set up. Check the router’s configuration interface or use a UPnP discovery tool to confirm the successful establishment of external access.
UPnP simplifies the process of accessing IoT devices behind NAT by automating the configuration of port forwarding. It eliminates the need for manual configuration, making it a user-friendly option for those who may not have advanced technical knowledge.
However, it’s important to note that UPnP has its limitations. Some routers may have limited UPnP capabilities or may not support it at all. In such cases, it may be necessary to use alternative methods for accessing IoT devices behind NAT.
Moreover, UPnP introduces potential security risks, as it automatically opens ports on the router. It’s essential to keep the router’s firmware up to date and monitor for any suspicious activities to mitigate these risks.
In the next section, we will explore another method, Dynamic DNS, which provides a solution for devices with dynamic IP addresses by associating them with a consistent domain name.
Method 3: Dynamic DNS
Dynamic DNS (DDNS) is a method used to associate a domain name with the dynamic IP address assigned to Network Address Translation (NAT) routers. It provides a solution for accessing IoT devices behind NAT, even when their IP addresses change periodically.
Here’s how Dynamic DNS works:
1. Choose a Dynamic DNS provider: Select a Dynamic DNS provider that offers the service of linking a domain name to a dynamic IP address. Popular providers include DynDNS, No-IP, and DuckDNS. Create an account and follow their instructions to set up a hostname.
2. Configure the NAT router: Access the router’s configuration interface and locate the DNS settings. Enter the Dynamic DNS credentials provided by the selected provider, including the hostname and any additional authentication details. Save the configuration changes.
3. Install the Dynamic DNS client: Some routers have built-in Dynamic DNS client capabilities. If not, you can install a Dynamic DNS client on the IoT device itself. The client will periodically communicate with the Dynamic DNS provider to update the device’s IP address.
4. Access the IoT device using the domain name: With Dynamic DNS configured, you can now access the IoT device using the associated domain name rather than the changing IP address. The Dynamic DNS provider will automatically update the IP address mapping whenever it changes.
Dynamic DNS provides a convenient way to access IoT devices with dynamic IP addresses. It eliminates the need to manually track and update the evolving IP address, ensuring that remote access remains consistent.
It’s worth noting that Dynamic DNS relies on the availability of an internet connection for both the IoT device and the Dynamic DNS provider. If either of these connections goes down, accessing the device via the domain name may not be possible.
Additionally, ensuring the security of the Dynamic DNS setup is crucial. Choose a reputable Dynamic DNS provider and enable any available security features, such as two-factor authentication, to protect against unauthorized access.
In the next section, we will explore another method, Virtual Private Networks (VPNs), which provide secure and private access to IoT devices behind NAT.
Method 4: Virtual Private Networks (VPNs)
Virtual Private Networks (VPNs) offer a secure and private method for accessing IoT devices behind Network Address Translation (NAT). VPNs create an encrypted connection between the remote device and the local network where the IoT device resides, allowing for secure communication and remote access.
Here’s how VPNs work:
1. Choose a VPN provider: Select a reliable VPN provider that offers support for the desired device and network configuration. Consider factors such as security, speed, and compatibility when making your choice.
2. Install and configure the VPN client: Install the VPN client on both the remote device and the local network where the IoT device is located. Follow the provider’s instructions to configure the client with the necessary details, such as server addresses, authentication credentials, and encryption settings.
3. Establish a VPN connection: On the remote device, initiate a connection to the VPN server using the VPN client. This creates a secure tunnel through which all internet traffic is routed, including access to the IoT device on the local network.
4. Access the IoT device: With the VPN connection established, you can now access the IoT device as if it were on the same local network. Use the device’s internal IP address to connect to it, as the VPN effectively extends the local network to the remote device.
VPNs provide several advantages when accessing IoT devices behind NAT. Firstly, they ensure secure communication by encrypting all data transmitted between the remote device and the local network. Additionally, VPNs allow users to bypass any port forwarding or firewall restrictions that may be in place on the NAT router.
However, there are a few considerations when using VPNs for accessing IoT devices. Firstly, the speed and latency of the VPN connection can impact real-time applications and data streaming. Choose a VPN provider that offers fast and reliable connections. Secondly, VPNs may require additional configuration on the local network, such as enabling VPN passthrough on the NAT router.
It’s important to note that VPNs may introduce a single point of failure in the network. If the VPN server or the VPN client fails, remote access to the IoT device will be disrupted. Regularly monitor the VPN connection and ensure the VPN client and server are kept up to date to maintain a reliable connection.
In the next section, we will explore another method, Reverse SSH Tunneling, which provides a secure way to access IoT devices behind NAT without the need for configuring the router.
Method 5: Reverse SSH Tunneling
Reverse SSH tunneling is a method that allows you to securely access an IoT device behind Network Address Translation (NAT) without making any configuration changes to the router. It establishes a secure tunnel between the IoT device and a remote server outside the local network, enabling external access to the device.
Here’s how reverse SSH tunneling works:
1. Set up an SSH server: Install and configure an SSH server on a remote server located outside the NAT network. The SSH server acts as an intermediary for communication between the external device and the IoT device.
2. Configure the IoT device: On the IoT device, install an SSH client and configure it to initiate a reverse SSH tunnel to the remote server. This process involves specifying the remote server’s IP address, SSH port, and the local port on which the IoT device will listen for incoming connections.
3. Establish the reverse SSH tunnel: With the SSH client configured on the IoT device, initiate the reverse SSH tunnel by connecting to the remote server. This creates a secure and encrypted tunnel through which external devices can access the IoT device by connecting to the remote server.
4. Access the IoT device: To access the IoT device, connect to the remote server using SSH, specifying the local port that was configured for the reverse SSH tunnel. This connection is forwarded through the tunnel to the IoT device, providing remote access as if the device were directly accessible from the external network.
Reverse SSH tunneling provides a secure method for accessing IoT devices behind NAT without exposing them directly to the internet. It eliminates the need for configuring the router and bypasses any port forwarding or firewall restrictions that may be in place.
However, there are a few considerations when using reverse SSH tunneling. Firstly, the remote server must have a publicly accessible IP address or a port forwarding rule set up on its NAT router. Additionally, the stability and availability of the connection depend on the reliability of the remote server.
To enhance security, it’s recommended to use key-based authentication rather than password-based authentication when establishing the SSH connection. This adds an extra layer of protection against unauthorized access to the IoT device.
In the next section, we will explore another method, cloud-based IoT platforms, which offer a centralized and secure solution for accessing IoT devices behind NAT.
Method 6: Cloud-based IoT platforms
Cloud-based IoT platforms offer a centralized and secure solution for accessing IoT devices behind Network Address Translation (NAT). These platforms act as intermediaries, facilitating communication between the external network and IoT devices by leveraging cloud infrastructure.
Here’s how cloud-based IoT platforms work:
1. Select a cloud-based IoT platform: Choose a cloud-based IoT platform that provides remote access and management capabilities for IoT devices. Popular platforms include AWS IoT, Google Cloud IoT, and Microsoft Azure IoT. Sign up for an account and set up your IoT infrastructure on the platform.
2. Register and connect IoT devices: Register your IoT devices on the cloud-based platform and establish a connection between the devices and the platform. This typically involves installing the platform’s client software or using APIs for device integration.
3. Create an external-facing API: Configure the cloud-based platform to expose a secure external-facing application programming interface (API). This API acts as a bridge between the external network and the IoT devices behind NAT.
4. Access the IoT devices: To remotely access the IoT devices, users can connect to the cloud-based platform’s API using credentials provided by the platform. The API can provide functionalities such as data retrieval, device control, and firmware updates, allowing users to interact with the IoT devices from anywhere in the world.
Cloud-based IoT platforms offer several benefits, such as centralized management, scalability, and inherent security measures. They typically provide authentication, encryption, and access control mechanisms to ensure the secure communication between users and IoT devices.
Additionally, cloud-based platforms simplify the process of accessing IoT devices behind NAT by abstracting the complexities of NAT traversal and remote connectivity. They provide a standardized and streamlined approach, reducing the need for manual configuration and allowing users to focus on the core functionalities of their IoT applications.
However, it’s important to consider the cost and dependency on cloud infrastructure when using cloud-based IoT platforms. Some platforms may have usage-based pricing models, and reliance on a third-party service provider means that availability and performance can be affected by the provider’s infrastructure and service-level agreements.
In this article, we have explored different methods for accessing IoT devices behind NAT. Each method offers its own advantages, considerations, and levels of complexity. By understanding these methods, you can choose the most suitable approach based on your specific requirements and constraints.
Conclusion
Accessing IoT devices behind Network Address Translation (NAT) poses challenges for remote management and control. However, several methods can overcome these hurdles and establish external access to IoT devices.
Port forwarding allows you to manually configure the NAT router to forward specific incoming traffic to the IoT device. Universal Plug and Play (UPnP) automates the process by dynamically configuring port forwarding on compatible devices and routers. Dynamic DNS associates a domain name with the changing IP address of the IoT device, providing a consistent way to access it. Virtual Private Networks (VPNs) create secure connections between remote devices and the local network, enabling seamless access. Reverse SSH tunneling establishes secure tunnels between the IoT device and a remote server outside the network, while cloud-based IoT platforms offer a centralized and secure solution for accessing devices.
Each method has its own strengths and considerations, such as security risks, technical complexity, and dependency on external services. It’s important to evaluate the specific requirements and constraints of your IoT setup before choosing the most suitable method.
By understanding and implementing these methods, you can overcome the challenges of accessing IoT devices behind NAT and unlock the full potential of your IoT applications. Whether it’s remote monitoring, control, or data collection, these methods provide the means to seamlessly interact with your IoT devices from anywhere in the world.
As IoT technology continues to evolve, it’s crucial to stay informed about advancements in NAT traversal techniques and security practices. Regularly updating firmware, following best practices for securing network devices, and staying vigilant against potential security threats will help ensure the continued reliability and security of your IoT deployments.
While accessing IoT devices behind NAT can be a complex task, the rewards of seamless remote access and control make it worth the effort. Embrace the available methods, adapt them to your specific needs, and harness the true potential of your IoT devices in both personal and professional settings.