In a recent high-profile cyberattack, MGM Resorts fell victim to a devastating ransomware attack that caused significant disruptions to its operations. The attack affected several iconic casino hotels in Las Vegas, such as the Bellagio, Mandalay Bay, and the Cosmopolitan. As a result of the attack, guests experienced delays during check-in, electronic payments, slot machines, ATMs, and paid parking systems were all crippled. Moreover, the hackers were able to steal a massive amount of customers’ personal information from MGM’s servers.
Key Takeaway
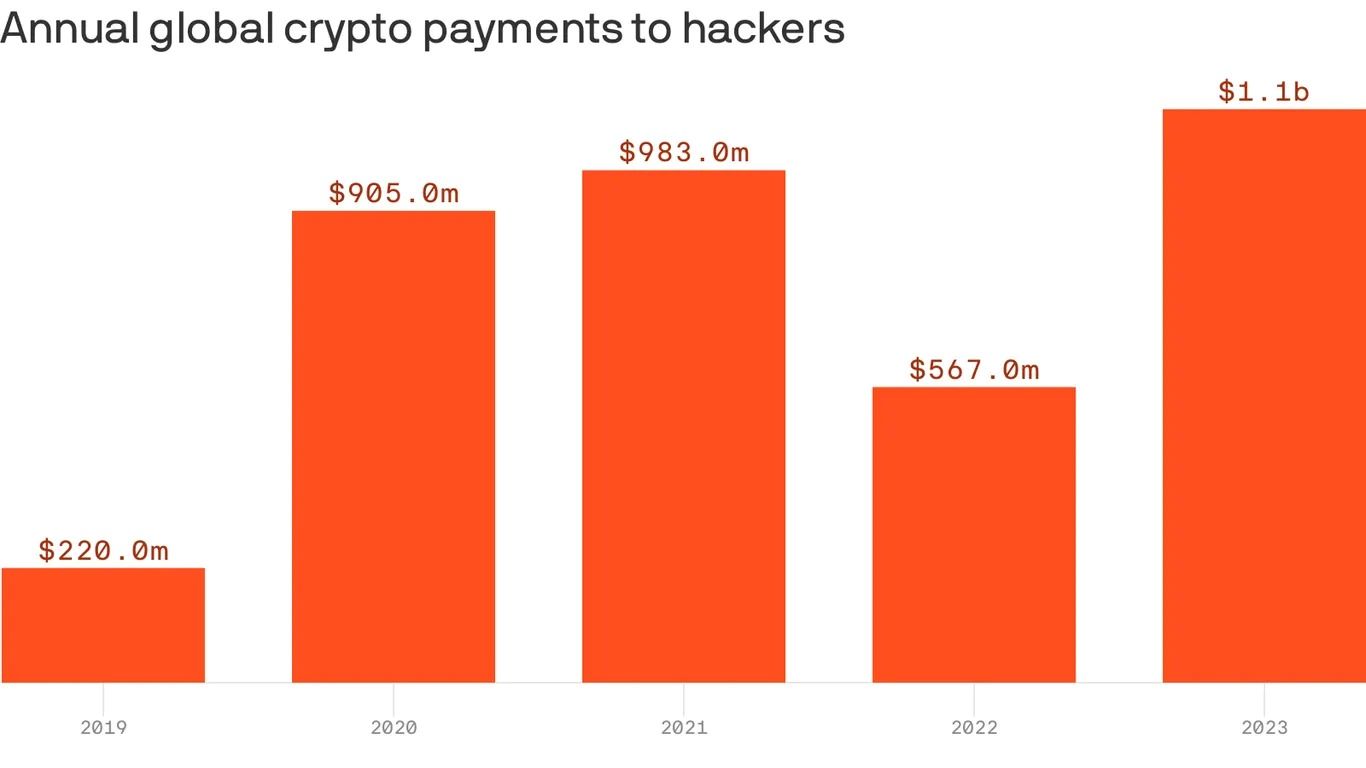
83% of organizations admit to paying hackers after a ransomware attack, with more than half paying at least
00,000. However, paying the ransom does not guarantee the safe return of stolen data or the complete removal of all copies. There is also an increased risk of subsequent attacks and higher ransom amounts demanded when organizations choose to pay.
MGM Resorts made a conscious decision not to pay the attackers’ ransom demand in order to regain control of their systems and retrieve their data. While the exact amount of the ransom is still unknown, it is likely to be less than the estimated $100 million that MGM Resorts expects to lose as a consequence of the cyberattack, according to regulatory filings. Despite this attack making headlines for weeks, an earlier attack on Caesars Entertainment received little attention in comparison. This is primarily due to the fact that Caesars decided to pay off the hackers to prevent the disclosure of the stolen data, hoping to minimize the incident’s impact.
For many organizations, paying the ransom may appear to be the easiest and most cost-effective solution to restore their networks and recover stolen data. However, there is no assurance that paying off the hackers will result in the safe return of the stolen data, or that all copies have been erased. Regardless of whether a ransom is paid or not, any data stolen by cybercriminals is already compromised. Trusting a criminal to delete the data is highly unreliable.
Caesars Entertainment’s breach did not receive much media attention, but the company still faced the same liability. Despite paying a ransom to the hackers who had stolen a copy of Caesars’ loyalty program database, which includes driver’s licenses and Social Security numbers of a significant number of members, the company admitted that it could not guarantee the removal of the stolen data by the hackers.
Moreover, paying a ransom can lead to additional technical difficulties. According to a study conducted by Cybereason, 80% of ransomware victims who paid the ransom were subsequently hit by a second ransomware attack. Out of the organizations compromised, 68% reported that the second attack occurred within a month and the hackers demanded a higher ransom. Paying the initial ransom may solve an immediate problem, but it also signals to the hackers that the organization is willing to pay large sums of money to resolve a crisis, making them more likely to target the organization again.
Paying a ransom demand is not illegal, but the FBI has long advised companies against it, as doing so encourages ransomware groups to continue targeting new victims. However, organizations can face legal and criminal consequences if they pay a ransom to groups sanctioned by the U.S. government. The U.S. Treasury warns that paying ransoms to these hacking and ransomware groups may violate U.S. sanctions laws and result in criminal prosecution.
Although paying the ransom may seem like a quick and inexpensive way out, it often ends up costing organizations more in the long run. It is crucial for organizations to invest in robust cybersecurity measures to prevent these attacks and mitigate the potential damage.