Why Is Crypto Security Important?
Cryptocurrency has gained immense popularity in recent years, with millions of individuals worldwide investing in digital assets. As the value and adoption of cryptocurrencies continue to increase, so do the security risks associated with holding and transacting these assets.
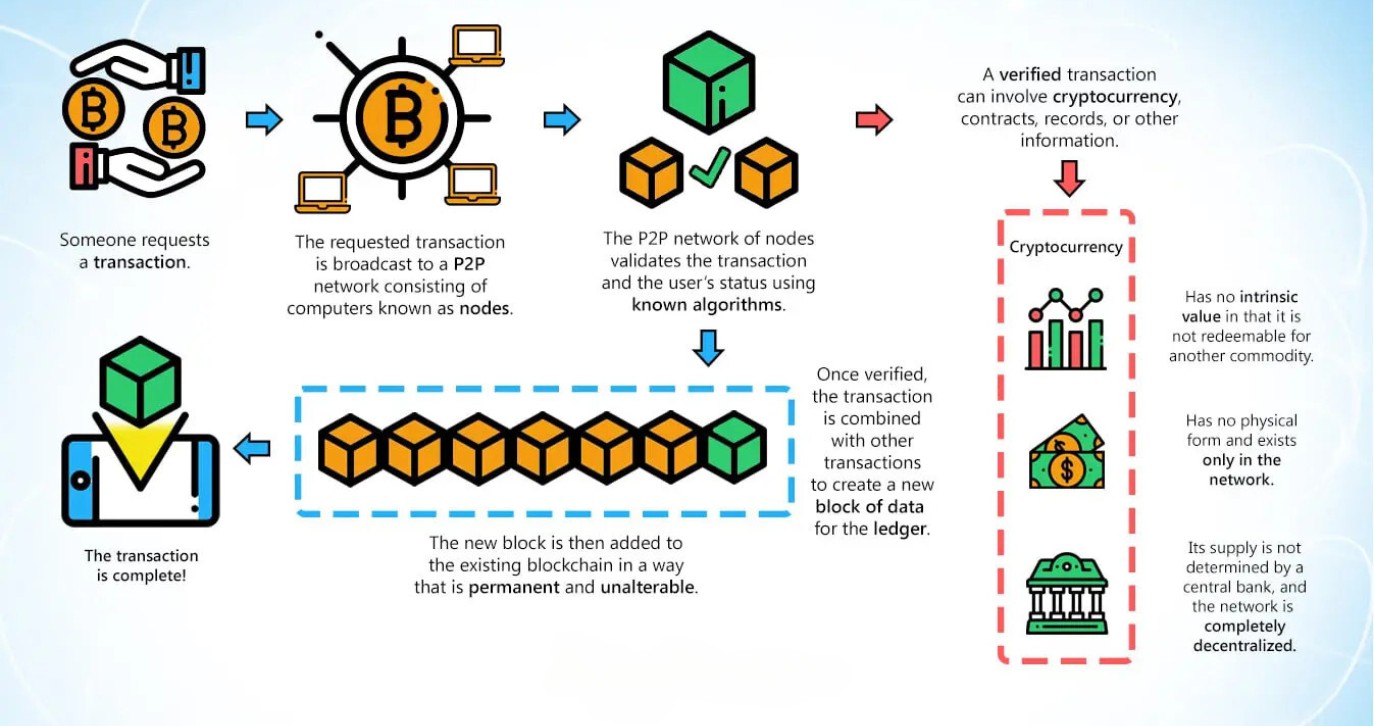
One of the main reasons why crypto security is crucial is the decentralized nature of digital currencies. Unlike traditional banking systems, cryptocurrencies rely on blockchain technology, which eliminates the need for intermediaries like banks and allows for peer-to-peer transactions. While this decentralization offers numerous benefits in terms of transparency and control, it also exposes users to various security risks.
One of the biggest threats in the crypto space is hacking and theft. Cybercriminals are constantly finding new ways to exploit vulnerabilities and gain unauthorized access to crypto wallets. Once they gain control of a wallet, they can easily transfer the funds to their own accounts, leaving the rightful owner with no recourse.
Additionally, the irreversible nature of cryptocurrency transactions means that there is little to no chance of recovering lost or stolen funds. Unlike traditional banking systems where fraudulent transactions can often be reversed, once a cryptocurrency transaction is confirmed, it cannot be reversed or disputed.
Another aspect of crypto security is the protection of personal information. When signing up for a crypto exchange or wallet, users are required to provide personal details such as their name, address, and identification documents. If this information falls into the wrong hands, it can be used for identity theft and other malicious activities.
Furthermore, maintaining crypto security is crucial for maintaining the overall integrity and trust in the cryptocurrency space. As more individuals and institutions adopt cryptocurrencies, it is essential to ensure that proper security measures are in place to prevent fraud and unauthorized access.
By prioritizing crypto security, users can safeguard their digital assets and gain peace of mind knowing that their funds are protected. Implementing the best practices and utilizing secure storage methods can significantly reduce the risk of falling victim to cyberattacks and losing valuable cryptocurrencies.
Understanding Cryptocurrency Wallets
When it comes to managing and securing your cryptocurrencies, having a wallet is essential. A cryptocurrency wallet is a digital application or hardware device that allows users to securely store, send, and receive their digital assets.
There are different types of cryptocurrency wallets available, each offering varying levels of security and convenience. The two main types of wallets are:
- Hot Wallets: These wallets are connected to the internet and are accessible through web-based platforms, mobile apps, or desktop applications. Hot wallets provide quick and convenient access to your cryptocurrencies, but they are more susceptible to hacking and cyber threats compared to cold wallets.
- Cold Wallets: These wallets are offline devices specifically designed to store cryptocurrencies in an offline, secure environment. Cold wallets provide an extra layer of security as they are not connected to the internet, making them less vulnerable to hacking attempts. The most common types of cold wallets are hardware wallets and paper wallets.
Hardware wallets are physical devices that typically resemble USB drives. They store your private keys offline and require you to physically connect them to a computer or mobile device when making transactions. By utilizing hardware wallets, you can keep your private keys secure and protected from potential online threats.
Paper wallets, on the other hand, are physical printouts of your private and public keys. These can be generated through certain websites or software applications. While paper wallets are considered a form of cold storage, they can be more prone to physical damage or loss if not stored properly.
When choosing a cryptocurrency wallet, it is important to consider factors such as the level of security, ease of use, and compatibility with the specific cryptocurrencies you own. It is also crucial to research and ensure that the wallet you choose has a strong track record of security and a dedicated development team that regularly updates the software.
It is worth noting that while wallets provide a secure way to store your cryptocurrencies, they do not actually hold the funds themselves. Instead, they store the private keys used to access and manage your digital assets on the blockchain.
Understanding and choosing the right cryptocurrency wallet is a vital step in securing your digital assets. By opting for a well-established wallet and following best practices in wallet management, you can enhance the security of your cryptocurrencies and give yourself peace of mind in this rapidly evolving digital landscape.
Different Types of Cryptocurrency Wallets
When it comes to storing and securing your cryptocurrency assets, there are several different types of wallets available to choose from. Each type offers its own unique features and level of security. Here are some of the common types of cryptocurrency wallets:
- Hot Wallets: Hot wallets are digital wallets that are connected to the internet. They can be accessed through web-based platforms, mobile apps, or desktop applications. Hot wallets offer convenience and ease of use, allowing users to easily send and receive cryptocurrencies. However, they are more susceptible to hacking and cyberattacks compared to cold wallets.
- Desktop Wallets: Desktop wallets are software applications that you install on your computer. They provide control over your private keys and allow you to manage your cryptocurrencies directly from your desktop. Desktop wallets are considered relatively secure, but they can be vulnerable to malware and viruses if proper precautions are not taken.
- Mobile Wallets: Mobile wallets are applications that you can install on your smartphone or tablet. They offer the convenience of accessing your cryptocurrencies on the go. Mobile wallets are typically user-friendly and can scan QR codes for easy transactions. However, it’s important to use trusted and secure mobile wallet applications from reputable sources to minimize the risk of malware or phishing attacks.
- Hardware Wallets: Hardware wallets are physical devices designed specifically for storing cryptocurrencies offline. They resemble USB drives and provide an extra layer of security. Hardware wallets store your private keys offline and require physical authentication, making them highly resistant to hacking attempts. They are considered one of the most secure options for storing cryptocurrencies.
- Paper Wallets: Paper wallets involve generating and printing out your private and public keys on a physical piece of paper. They offer a completely offline storage solution. Paper wallets can be generated using dedicated websites or software applications. It’s important to keep the printed paper wallet in a safe and secure location to prevent loss or damage.
When choosing a cryptocurrency wallet, it’s important to consider factors such as security, ease of use, compatibility with your chosen cryptocurrencies, and your specific needs. It’s also advisable to research and choose wallets developed by reputable companies with a solid track record of security.
It’s worth noting that some wallets also offer features like multi-signature functionality, where multiple users need to approve a transaction before it can be executed. This can provide an additional layer of security and prevent unauthorized access to funds.
Ultimately, the choice of wallet type depends on your individual preferences and the level of security you require for your cryptocurrency holdings. It’s recommended to diversify your holdings across different types of wallets to mitigate the risk of theft or loss. Regularly updating your wallet software and following security best practices will go a long way in ensuring the safety of your cryptocurrencies.
Setting Up a Hardware Wallet
Hardware wallets are widely regarded as one of the most secure options for storing cryptocurrencies. These physical devices offer an offline storage solution and provide an extra layer of security by keeping your private keys offline. Here are the steps to set up a hardware wallet:
- Choose the Right Hardware Wallet: Research and choose a reputable hardware wallet from a trusted manufacturer. Popular options include Ledger and Trezor. Consider factors such as supported cryptocurrencies, user interface, and security features.
- Unbox and Connect the Hardware Wallet: Once you have obtained your hardware wallet, unbox it and connect it to your computer or mobile device using the provided USB cable. Follow the manufacturer’s instructions to ensure proper connection.
- Install the Wallet Software: Visit the official website of the hardware wallet manufacturer and download the corresponding wallet software for your operating system. Install the software following the provided instructions.
- Initialize the Wallet: Open the wallet software and select the option to initialize or set up a new wallet. This process will involve creating a new wallet and initializing it on the hardware device.
- Set Up a PIN Code: During the initialization process, you will be prompted to set up a PIN code for accessing the wallet on the hardware device. Choose a strong PIN code and make sure to remember it securely.
- Generate and Backup the Recovery Seed: The next step is to generate a recovery seed, which is a series of words that act as a backup for your wallet. Write down the seed on a piece of paper or use the provided recovery sheet. This recovery seed is crucial for restoring your wallet in case of loss, theft, or damage to the hardware device.
- Verify the Recovery Seed: After generating the recovery seed, the wallet software will ask you to verify it. This ensures that you have correctly written down the seed. Carefully check each word to ensure accuracy.
- Finalize the Setup: Once the recovery seed is verified, the wallet setup process is complete. Safely store the recovery seed in a secure location separate from the hardware wallet to prevent unauthorized access.
Once your hardware wallet is set up, you can start using it to send and receive cryptocurrencies. You will need to connect the hardware wallet to your computer or mobile device whenever you want to access your wallet and sign transactions securely.
It’s essential to keep your hardware wallet firmware up to date by regularly checking for updates from the manufacturer. This ensures optimal security and compatibility with the latest security protocols.
By following these steps and taking the necessary precautions, you can set up a hardware wallet and enjoy the peace of mind that comes with having a secure offline storage solution for your valuable cryptocurrencies.
Creating a Strong Password
When it comes to protecting your cryptocurrency and other online accounts, creating a strong password is crucial. A strong password is your first line of defense against unauthorized access and potential theft. Here are some tips for creating a strong password:
- Use a Long Password: The longer the password, the harder it is for hackers to crack. Aim for a minimum of 12 characters or more.
- Include a Mix of Characters: A strong password should include a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using common words or predictable patterns.
- Avoid Personal Information: Do not use personal information such as your name, birthdate, or address in your password. This information is easily guessable and can make your accounts vulnerable to hacking.
- Don’t Rely on Common Passwords: Avoid using commonly used passwords, such as “123456” or “password.” These passwords are easy for hackers to guess and are frequently targeted in cyberattacks.
- Use Passphrases: Consider using a passphrase instead of a password. A passphrase is a series of words that are easy for you to remember but difficult for others to guess. Make sure the words are unrelated and include spaces or other characters.
- Unique Passwords for Each Account: Avoid using the same password for multiple accounts. If one account gets compromised, having unique passwords ensures that the damage is limited to that specific account.
- Consider Password Managers: If remembering multiple strong passwords is challenging, consider using a password manager. Password managers securely store your passwords and can generate strong, unique passwords for each account.
- Regularly Update Your Password: It’s good practice to update your passwords regularly, especially for critical accounts like your cryptocurrency wallet. Change your password every few months to ensure continued security.
While creating a strong password is important, it is equally essential to protect your password from being compromised. Here are some additional tips to keep in mind:
- Avoid Sharing Your Password: Never share your password with anyone, including friends, family, or colleagues. Keep your password confidential to maintain the security of your accounts.
- Beware of Phishing Attempts: Be cautious of phishing attempts where scammers try to trick you into revealing your password. Always double-check the sources of emails or websites before entering your login credentials.
- Enable Two-Factor Authentication: Two-factor authentication adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
Remember, the security of your cryptocurrencies relies on the strength of your password. By following these tips and best practices, you can significantly reduce the risk of unauthorized access and protect your valuable digital assets.
Utilizing Two-Factor Authentication (2FA)
When it comes to securing your cryptocurrency accounts, using two-factor authentication (2FA) is highly recommended. 2FA adds an additional layer of security by requiring two forms of verification when logging in or conducting transactions. This extra step significantly reduces the risk of unauthorized access and helps protect your valuable digital assets. Here’s how 2FA works and how you can make the most of it:
1. Choose the Right 2FA Method: There are several options for implementing 2FA, including:
- Text Message (SMS) Codes: One of the most common methods involves receiving a text message with a verification code to enter when logging in. While SMS codes can be convenient, they can also be susceptible to SIM card swapping or interception by attackers.
- Authentication Apps: Mobile apps like Google Authenticator, Authy, or LastPass Authenticator generate time-based one-time passwords (TOTPs) that you enter when logging in. These apps work offline and are more secure than SMS codes.
- Hardware Tokens: Some services provide physical hardware tokens that generate unique codes, offering an extra layer of security. These tokens are typically small devices that you carry with you.
2. Enable 2FA on Your Cryptocurrency Accounts: Go to the security settings of your cryptocurrency exchange or wallet and enable 2FA. Follow the instructions provided by the service to set up 2FA using your chosen method. Some services may require you to scan a QR code with your authentication app, while others may ask you to enter a unique code generated by the app.
3. Secure Your 2FA Backup Codes: When setting up 2FA, you will often receive a set of backup codes. These codes can be used to access your account if you lose access to your primary 2FA method. Keep these backup codes stored securely, preferably offline or printed and stored in a safe location.
4. Regularly Review and Update Your 2FA Settings: Periodically review your 2FA settings to ensure they are up to date. If you replace your mobile device or switch to a new authentication app, make sure to update your 2FA settings accordingly to avoid any issues with accessing your accounts.
5. Consider Setting Up Multiple 2FA Methods: Some services allow you to use multiple 2FA methods for added security. For example, you can enable both an authentication app and SMS codes. This provides redundancy and minimizes the risk of being locked out of your account if one method fails.
By utilizing two-factor authentication, you greatly enhance the security of your cryptocurrency accounts. Even if someone manages to obtain your password, they will still need the second factor (i.e., authentication code) to gain access. This significantly reduces the risk of unauthorized access and protects your digital assets from potential breaches.
Remember to securely store your backup codes and be cautious of phishing attempts or fake 2FA prompts that scammers may use to trick you into providing sensitive information. By practicing good security habits and utilizing 2FA, you can take important steps towards safeguarding your cryptocurrency accounts and maintaining peace of mind.
Using Cold Storage for Extra Security
When it comes to securing your cryptocurrencies, cold storage is considered one of the most secure methods available. Cold storage refers to storing your digital assets offline, away from potential online threats. By keeping your private keys offline, you greatly reduce the risk of hacking attempts and unauthorized access. Here are some common cold storage methods you can use to enhance the security of your cryptocurrencies:
1. Hardware Wallets: Hardware wallets are physical devices designed specifically for offline storage of cryptocurrencies. They provide an extra layer of security by keeping your private keys offline and requiring physical authentication for transactions. Hardware wallets, such as Ledger and Trezor, offer a user-friendly interface and are widely trusted within the crypto community.
2. Paper Wallets: Paper wallets involve printing out your private and public keys on a piece of paper. This offline method provides an air-gapped solution, as your keys are not stored on any electronic device. To create a paper wallet, you can use dedicated websites or software applications. Store the printed paper in a secure location away from prying eyes and ensure it is protected from damage or loss.
3. Offline Computer or USB Drive: Another cold storage option is creating an offline computer or using a secure USB drive to store your private keys. By keeping your private keys on an offline device, you eliminate the risk of online threats. Ensure that the offline computer or USB drive is secure and protected from physical access or theft.
4. Brain Wallets: Brain wallets are a unique form of cold storage where your private keys are derived from a passphrase or a series of words chosen by you. By memorizing the passphrase, you can access your cryptocurrencies without the need for any physical device. However, it’s important to choose a strong passphrase that cannot be easily guessed or cracked.
When using cold storage methods, it’s essential to consider the following best practices:
- Backup Your Wallet: Even with cold storage, it’s crucial to have backups of your private keys or recovery phrases. Backup your wallet and store copies in multiple secure and separate locations.
- Test Your Backup: Before relying solely on cold storage, test your backup process to ensure you can recover your wallet and access your funds if needed.
- Keep Software Updated: Periodically check for firmware and software updates from the manufacturer of your hardware wallet or the software you’re using for cold storage. These updates often include security fixes and improvements.
- Secure Storage: Choose secure physical locations to store your cold storage devices or paper wallets. Use fireproof safes, safety deposit boxes, or other secure storage options to protect them from theft, damage, or loss.
- Be Cautious of Physical Attacks: Be aware of physical attacks or tampering attempts on your cold storage devices. Regularly inspect the devices for any signs of tampering and only purchase hardware wallets or store paper wallets from trusted sources.
By utilizing cold storage methods, you can significantly enhance the security of your cryptocurrencies. Cold storage ensures that your private keys are stored offline, making it extremely difficult for attackers to gain access to your digital assets. However, it’s essential to maintain proper backup practices and adhere to security guidelines to mitigate the risk of losing access to your funds.
Protecting Your Private Keys
Private keys are critical components of cryptocurrency security, as they grant access to your digital assets. Protecting your private keys is essential to prevent unauthorized access and safeguard your valuable cryptocurrencies. Here are some important steps to help you protect your private keys:
1. Generate Private Keys Securely: When generating private keys, ensure you do it on a trusted, secure device. Use reputable wallet software or hardware wallets that are known for their strong security measures.
2. Keep Your Private Keys Offline: Storing your private keys offline, away from internet-connected devices, greatly reduces the risk of hacking or online attacks. Cold storage methods, such as hardware wallets or paper wallets, are the safest options for offline private key storage.
3. Do Not Share Your Private Keys: Treat your private keys as highly confidential information and never share them with anyone. Beware of phishing attempts or individuals trying to trick you into revealing your private keys.
4. Use Multisignature Wallets: Multisignature (multisig) wallets require multiple private key signatures to authorize transactions. By distributing the signing power across multiple devices or individuals, the risk of a single compromised private key impacting your funds is minimized.
5. Encrypt Digital Wallets with Strong Passwords: If you’re using a digital wallet, encrypt it with a strong, unique password. This adds an extra layer of protection, as even if someone gains access to your device, they would still need the password to access your wallet and private keys.
6. Regularly Backup Your Wallet: Make regular backups of your wallet, including your private keys or recovery phrases, and store them securely in multiple offline locations. This ensures that you can recover your wallet and access your funds if you ever encounter a device failure or loss.
7. Be Cautious of Keyloggers and Malware: Keyloggers and malware can capture keystrokes or take screenshots of your device, potentially compromising your private keys. Use trusted antivirus software, keep your operating system and applications updated, and avoid downloading files or clicking on suspicious links.
8. Consider Using Hardware Wallets: Hardware wallets, such as Ledger or Trezor, provide additional security for your private keys. They keep your private keys isolated on a secure device, protected from potential malware or keyloggers on your computer or mobile device.
9. Never Store Private Keys in Plain Text: Avoid storing your private keys in plain text on your computer, online storage platforms, or cloud services. If a hacker gains access to your devices or accounts, they could easily retrieve your private keys and gain control of your funds.
10. Practice Good Physical Security: If you print or write down your private keys, ensure you store them in a safe and secure location, such as a locked safe or safety deposit box. Minimize the risk of physical theft or damage to your private keys.
By implementing these practices, you can significantly enhance the security of your private keys and protect your cryptocurrencies from unauthorized access. Remember to exercise caution and remain vigilant, as the safety of your private keys is crucial for maintaining the integrity of your digital assets.
Securely Storing and Backing Up Your Wallet
Securely storing and backing up your wallet is essential for protecting your cryptocurrency investments. While cryptocurrencies are stored digitally, they can still be vulnerable to loss or theft. By implementing proper storage and backup practices, you can safeguard your funds and ensure access to your wallet in case of any unforeseen events. Here are some important steps to securely store and back up your wallet:
1. Choose a Secure Storage Method: Consider using a hardware wallet or a reputable software wallet with built-in security features. Hardware wallets, such as Ledger or Trezor, provide offline storage and an extra layer of protection for your private keys.
2. Keep Your Wallet Offline: Whenever possible, keep your wallet offline by utilizing hardware wallets or paper wallets. Cold storage options significantly reduce the risk of online hacking or unauthorized access to your funds.
3. Opt for Multiple Backups: Create multiple backups of your wallet to ensure you have redundancy. Store the backups in separate physical locations to safeguard against theft, natural disasters, or device failures.
4. Protect Your Wallet with Encryption: If you have a digital wallet, encrypt it with a strong password or passphrase. Encryption adds an extra layer of security, ensuring that even if your wallet file is accessed, it remains secure.
5. Use Encrypted External Drives or USBs: When creating backups, store them in encrypted external drives or USBs. Encryption provides an additional safeguard against unauthorized access to your wallet backup files.
6. Consider Distributed Storage or Cloud Backup: If you choose to store your wallet backups in the cloud or online, ensure that the service provider offers robust security measures and encryption. Distributing your backups across multiple cloud storage platforms can also minimize the risk of data loss.
7. Regularly Test Your Wallet Backup: Periodically verify the integrity of your wallet backups by restoring them on a separate device or computer. This practice ensures that your backups are functional and can be successfully recovered.
8. Keep Backup Details Confidential: Treat the details of your wallet backups as highly confidential information. Share backup instructions and access details only with trusted individuals. Beware of phishing attempts or scams where individuals may pose as support staff and request your backup files.
9. Update and Maintain Your Backups: Keep your backups up to date by creating new ones whenever you make significant changes to your wallet. Regularly revisit your backup strategy to ensure it aligns with any updates or changes in your cryptocurrency holdings.
10. Test Restoration Process: Familiarize yourself with the process of restoring your wallet from a backup. This knowledge will be valuable in case of an emergency or if you ever need to recover your wallet.
By securely storing and backing up your wallet, you can mitigate the risk of losing access to your funds and prevent potential disasters. Remember to regularly review your storage and backup solutions to adapt to any changes in your circumstances or the evolving security landscape.
Being Mindful of Phishing Attacks
Phishing attacks are a significant threat in the world of cryptocurrencies. These attacks involve malicious actors attempting to trick you into revealing sensitive information, such as your wallet credentials or private keys. It is crucial to be mindful of phishing attacks and take steps to protect yourself. Here are some important measures to keep in mind:
1. Verify the Source: Be cautious of any unsolicited emails, messages, or websites that request your wallet credentials or personal information. Always verify the source before providing any sensitive information. Check the email address, domain name, or URL to ensure they are legitimate.
2. Use Two-Factor Authentication (2FA): Enable 2FA on your cryptocurrency accounts whenever possible. This provides an additional layer of security by requiring a second form of verification before accessing your account.
3. Never Click on Suspicious Links: Avoid clicking on links in unsolicited emails or messages, or on social media platforms. These links may redirect you to fake websites that resemble authentic platforms but are designed to steal your login credentials.
4. Be Wary of Fake Wallet Apps: Stick to official app stores when downloading wallet apps. Fake or malicious apps can be designed to mimic legitimate wallets and steal your private keys.
5. Double-Check Website URLs: Always double-check the website URLs of cryptocurrency exchanges, wallets, or other platforms before entering any login information. Phishing sites may have URLs that resemble the real platform but have slight variations or typos.
6. Keep Your Software Updated: Regularly update your operating system, web browsers, and antivirus software. These updates often include important security patches that help protect against known vulnerabilities exploited by phishing attempts.
7. Never Share Your Private Keys: Be extremely cautious of anyone asking for your private keys. Your private keys should be kept confidential and shared with trusted individuals only. No legitimate service or support team will require your private keys.
8. Educate Yourself and Stay Informed: Keep up to date with the latest phishing techniques and learn how to spot red flags. Stay informed about new phishing tactics and trends in the cryptocurrency community, as attackers are constantly evolving their methods.
9. Report Phishing Attempts: If you encounter a phishing attempt or suspect fraudulent activity, report it to the relevant authorities, such as the platform or website that was targeted, as well as any anti-phishing organizations.
10. Trust Your Instincts: If something feels suspicious or too good to be true, trust your instincts and proceed with caution. Take the time to verify the legitimacy of any requests or offers before taking any action.
Being mindful of phishing attacks is crucial for protecting your cryptocurrencies and personal information. By implementing these measures and staying vigilant, you can significantly reduce the risk of falling victim to phishing attempts and ensure a safer crypto journey.
Keeping Your Operating System and Software Updated
Maintaining up-to-date software and operating systems is a critical aspect of cybersecurity, especially when it comes to protecting your cryptocurrency investments. Regular software updates and operating system patches play a vital role in ensuring your digital assets remain secure. Here’s why you should prioritize updating your software and operating system:
1. Patching Security Vulnerabilities: Software updates often include security patches that address vulnerabilities discovered by developers or those that have been exploited by cybercriminals. By updating your software, you can mitigate the risk of falling victim to known vulnerabilities.
2. Protection Against Malware: Malware developers are continually refining their techniques to bypass security measures. Software updates typically include improvements to security features that help ward off new malware threats.
3. Bug Fixes and Performance Enhancements: Software updates not only address security vulnerabilities but also fix bugs and optimize performance. These fixes can enhance the stability and efficiency of your applications, ensuring a smooth experience while interacting with your cryptocurrency wallets and exchanges.
4. Compatibility with Latest Security Standards: As the cryptocurrency landscape evolves, security standards and protocols also change accordingly. Keeping your software and operating system updated helps ensure compatibility with the latest security measures and protocols, reducing the risk of compromise.
5. Protection Against Exploits: Cybercriminals often target known vulnerabilities and exploits in outdated software and operating systems. By promptly applying updates, you close the door on potential exploits that could leave your digital assets vulnerable to theft.
6. Preventing Remote Attacks: System updates often address weaknesses that allow remote access to your device. Failing to install updates leaves your system at risk of unauthorized access, potentially compromising not only your cryptocurrency but also other personal data.
7. Regular Cryptocurrency Wallet Support: Cryptocurrency wallets and exchanges frequently release updated versions to accommodate improvements and new features. By keeping your software up to date, you ensure compatibility and access to the latest wallet features and security enhancements.
8. Automate Updates Where Possible: Many operating systems and applications allow you to automate software updates. Enabling this feature ensures that you stay protected without needing to manually initiate updates.
To maintain the security of your cryptocurrencies, follow these best practices:
- Enable Automatic Updates: Enable automatic updates for your operating system, software, and security applications. This helps ensure that you are always protected with the latest security patches.
- Regularly Check for Updates: If automatic updates are not available or enabled, regularly check for updates manually. Visit the official websites of your operating system, applications, and cryptocurrency wallets to download and install the latest versions.
- Be Cautious with Third-Party Software: Be mindful of installing third-party software or plugins, as they may introduce security vulnerabilities. Stick with trusted sources and regularly update any third-party software you rely on.
- Keep Hardware Firmware Updated: For hardware wallets or other similar devices, check for firmware updates and install them as they become available. Hardware updates often include security enhancements.
By keeping your software and operating system updated, you enhance your overall cybersecurity posture, effectively safeguarding your cryptocurrency investments and reducing the risk of security breaches.
Practicing Safe Online Behavior
Practicing safe online behavior is essential for protecting your cryptocurrencies and personal information from cyber threats. By following best practices and adopting a proactive approach to security, you can minimize the risk of falling victim to scams, fraud, and other online attacks. Here are some key principles to keep in mind:
1. Be Skeptical and Vigilant: Exercise caution when interacting online, especially in the cryptocurrency space. Be skeptical of unsolicited messages, offers, or investment opportunities. Stay vigilant for signs of scams, phishing attempts, or fraudulent schemes.
2. Verify Websites and Secure Connections: Before entering any sensitive information on a website, make sure it is secure by checking for the padlock symbol in the browser’s address bar. Double-check the URL to ensure it matches the legitimate website you intend to visit.
3. Use Strong, Unique Passwords: Create strong, unique passwords for your cryptocurrency wallets, exchanges, and other online accounts. Avoid reusing passwords and consider using a password manager to securely store and generate strong passwords.
4. Enable Two-Factor Authentication (2FA): Enable 2FA whenever possible on your cryptocurrency accounts. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your mobile device.
5. Beware of Public Wi-Fi: Avoid accessing your cryptocurrency accounts or conducting financial transactions when connected to public Wi-Fi networks. Public networks may be insecure, making you vulnerable to attacks. Use a virtual private network (VPN) if necessary.
6. Regularly Update Security Software: Install and keep your security software, antivirus software, and firewalls up to date. These tools help protect against malware, viruses, and other online threats.
7. Be Careful Sharing Personal Information: Be cautious when sharing personal information online. Avoid sharing unnecessary details or sensitive identifying information that could be used for identity theft or targeted attacks.
8. Educate Yourself: Stay informed about the latest security practices and cryptocurrency scams. Educate yourself on common phishing techniques, social engineering tactics, and the latest trends in cybercrime. This knowledge will help you recognize and avoid potential threats.
9. Back Up Your Data Regularly: Regularly back up your cryptocurrency wallets, important files, and documents. Store backups in secure and separate locations to ensure you can recover your valuable data in case of device loss, theft, or hardware failure.
10. Keep Your Software Up to Date: Maintain regular updates for your operating system, web browsers, and other software applications. Updates often include critical security patches that address vulnerabilities and protect against emerging threats.
11. Be Mindful of Social Engineering Tactics: Cybercriminals may attempt to manipulate or deceive you through social engineering tactics. Be cautious of unexpected requests for personal information, urgent money transfers, or attempts to gain your trust through false pretenses.
By practicing safe online behavior, you can significantly reduce the risk of falling victim to online threats and protect your cryptocurrencies. Stay informed, resilient, and proactive in maintaining your online security.
Is It Safe to Store Cryptocurrency on Exchanges?
Storing cryptocurrency on exchanges is a common practice for many investors, as it offers convenience and easy access to trading. However, it is important to understand the potential risks involved and make an informed decision about the safety of storing your cryptocurrency on an exchange.
1. Security Breaches: Cryptocurrency exchanges can be vulnerable to security breaches. Hackers may target exchanges to gain unauthorized access to user funds. Several high-profile exchange hacks have occurred in the past, resulting in the loss of significant amounts of cryptocurrency.
2. Custodial Ownership: When you store your cryptocurrency on an exchange, you essentially transfer custodial ownership of your funds to the exchange. This means that you rely on the exchange’s security practices and trust that they will protect your assets.
3. Target for Hackers: Exchanges are prime targets for hackers due to the large amounts of cryptocurrency they hold. Even exchanges with robust security measures are not immune to potential attacks. The risk of hacking and theft is a constant concern when storing funds on exchanges.
4. Regulatory and Compliance Risks: Exchanges are subject to regulatory requirements and compliance measures, which can vary from jurisdiction to jurisdiction. Regulatory changes or non-compliance issues could impact the safety and accessibility of your funds.
5. Limited Control: Storing your cryptocurrency on exchanges means relinquishing some control over your private keys. With your funds held by a third party, you are dependent on the exchange’s security practices and processes in the event of any issues.
6. Operational Risks: Exchanges can face operational risks, such as technical glitches, outages, or even insolvency. These risks could potentially affect your ability to access and withdraw your funds in a timely manner.
Given these risks, it is generally recommended to consider alternative storage options for long-term holdings or substantial amounts of cryptocurrency. Some additional options to consider include:
- Hardware Wallets: Hardware wallets offer offline storage of private keys, providing an extra layer of security. They are considered one of the safest options for storing cryptocurrency, as they are not connected to the internet.
- Software Wallets: Software wallets installed on your computer or mobile device can provide more control over your private keys. However, it is crucial to choose reputable wallet software and take appropriate security precautions.
- Paper Wallets: Paper wallets involve printing out your private and public keys on paper and storing them securely offline. They provide an air-gapped storage option but require careful handling to prevent loss or damage.
Ultimately, the decision to store cryptocurrency on an exchange depends on your risk tolerance, the amount of cryptocurrency you hold, and your own assessment of the exchange’s security measures. It is important to research and choose reputable exchanges that employ stringent security protocols and have a track record of protecting user funds. Additionally, consider diversifying your storage strategy by utilizing a combination of secure wallets and exchanges.
Remember to regularly review and strengthen your security practices, keep your software up to date, and remain vigilant against potential threats in the ever-evolving landscape of cryptocurrency security.
What to Do If You Suspect a Security Breach
If you suspect a security breach or unauthorized access to your cryptocurrency accounts, it is crucial to act quickly and take appropriate steps to mitigate the potential damage. Here are some important actions to consider if you suspect a security breach:
1. Isolate and Secure Your Devices: Disconnect your affected devices from the internet immediately to prevent further unauthorized access. This includes unplugging network cables or disabling Wi-Fi connections. Take steps to secure your devices, such as changing passwords and running security scans to detect any malware or keyloggers.
2. Change Your Passwords: Change the passwords for all your cryptocurrency accounts, email accounts, and any other accounts that may be linked to your cryptocurrencies. Use strong, unique passwords that are not easily guessable. Enable two-factor authentication (2FA) if it is not already enabled, and update your recovery or backup codes.
3. Monitor Your Accounts: Regularly monitor your cryptocurrency accounts for any unusual activity. Check the transaction history and addresses associated with your wallet to ensure no unauthorized transactions have occurred. Take note of any unfamiliar addresses or suspicious transactions and report them to the appropriate authorities or your wallet provider.
4. Contact Support or Customer Service: Reach out to the customer support or security teams of the relevant cryptocurrency exchanges or wallet providers to report the suspected breach and seek assistance. They may be able to investigate the issue, provide guidance, or help secure your accounts.
5. Notify Your Bank or Financial Institution: If your cryptocurrency accounts are linked to your bank accounts, credit cards, or other financial services, notify your bank or financial institution about the suspected security breach. They can take additional precautions to protect your traditional funds and monitor for any unauthorized transactions.
6. Report the Incident: Report the suspected security breach to the appropriate authorities, such as local law enforcement or cybersecurity agencies. Provide them with all necessary details, including any evidence or suspicious activity you have observed.
7. Enhance Your Security Measures: After a security breach, it is important to strengthen your security measures. Consider implementing additional security measures, such as using hardware wallets, adopting more secure password management practices, and regularly updating your software and operating systems to the latest versions.
8. Inform Other Users: If you suspect a security breach on a platform or exchange that involves other users, consider notifying them of the potential risk. This can help prevent further victims and allow others to take appropriate actions to secure their accounts.
Remember, it is crucial to remain calm and take immediate action when you suspect a security breach. By following these steps and promptly reporting the incident to the appropriate authorities and service providers, you can minimize the potential impact of the breach and protect your cryptocurrency investments.
Conclusion
Securing your cryptocurrency assets is of utmost importance in today’s digital landscape. By implementing proper security measures and best practices, you can mitigate the risk of theft, hacking, and unauthorized access. Understanding the importance of crypto security and taking proactive steps to protect your digital assets is crucial for maintaining peace of mind and safeguarding your investments.
In this article, we explored various aspects of cryptocurrency security. We discussed the significance of understanding different types of cryptocurrency wallets and the benefits of using hardware wallets for extra security. Creating strong passwords and utilizing two-factor authentication (2FA) were highlighted as critical steps in bolstering account security.
Cold storage methods, such as hardware wallets and paper wallets, were explored as powerful ways to keep your cryptocurrencies offline and safe from online threats. We also emphasized the importance of securing and backing up your wallet to prevent any loss or irreversible damage. Being mindful of phishing attacks, practicing safe online behavior, and keeping your operating system and software up to date were emphasized as essential preventative measures.
The question of whether it is safe to store cryptocurrency on exchanges was analyzed, with risks and potential alternatives being discussed. Additionally, we covered the recommended steps to take if you suspect a security breach, including isolating devices, changing passwords, monitoring accounts, and contacting support or relevant authorities.
Remember, the evolving nature of cryptocurrency security requires ongoing education and adaptation to new threats. Stay informed about emerging security practices, remain vigilant, and employ a multi-layered approach to safeguarding your digital assets. By prioritizing security, you can protect your cryptocurrencies and enjoy the benefits of this exciting and transformative technology.