Introduction
Welcome to the world of cybersecurity, a field that plays a critical role in protecting our digital lives. In today’s interconnected world, where information is readily accessible and communication happens instantaneously, the need for robust cybersecurity measures is more important than ever before.
As technology continues to evolve, so do the threats that lurk in the digital landscape. Cybercriminals are constantly developing new tactics to exploit vulnerabilities and gain unauthorized access to sensitive information. From financial fraud to data breaches and identity theft, the consequences of inadequate cybersecurity can be devastating.
Understanding what cybersecurity entails is the first step towards safeguarding yourself, your business, and your personal information in the digital age. From implementing strong passwords to recognizing phishing attempts and keeping software updated, there are several essential practices you can adopt to stay one step ahead of cyber threats.
In this article, we will explore the importance of cybersecurity, common cyber threats, and provide you with practical tips to ensure your online safety. By following these guidelines, you can enhance your digital resilience and minimize the risk of falling victim to cybercrime.
Understanding Cybersecurity
Cybersecurity refers to the practices and measures taken to protect computer systems, networks, and data from unauthorized access, theft, and damage. It encompasses a wide range of strategies, technologies, and protocols designed to prevent, detect, and respond to cyber threats.
At its core, cybersecurity is all about safeguarding the confidentiality, integrity, and availability of information. Confidentiality ensures that data is only accessible to authorized individuals, integrity ensures that data remains unaltered and accurate, and availability ensures that critical systems and data are accessible when needed.
Cybersecurity is not limited to protecting individual computers or devices; it extends to securing entire networks, cloud-based systems, websites, and mobile apps. It involves identifying vulnerabilities, implementing protective measures, and responding effectively to incidents to minimize potential damage.
One of the fundamental principles of cybersecurity is the concept of defense in depth. This approach involves deploying multiple layers of security controls to create a robust and resilient defense system. These layers can include firewalls, intrusion detection systems, antivirus software, encryption protocols, access controls, and employee awareness.
Another crucial aspect of cybersecurity is risk management. It is essential to assess and understand the potential risks and vulnerabilities faced by an organization or individual and develop strategies to mitigate those risks. This involves conducting regular security assessments, implementing security controls, and monitoring systems for suspicious activities.
Furthermore, cybersecurity is a rapidly evolving field. Threats and vulnerabilities are constantly emerging, and new technologies are introduced regularly. To stay ahead of cyber threats, cybersecurity professionals must remain vigilant, continuously update their knowledge and skills, and adapt their strategies to combat emerging risks.
By understanding the principles and foundations of cybersecurity, individuals and organizations can make informed decisions and implement effective security measures to protect their digital assets. Whether you are a small business owner, an individual internet user, or a large multinational corporation, cybersecurity should be a top priority to safeguard your information and maintain the trust of your customers and clients.
Importance of Cybersecurity
In today’s digital landscape, cybersecurity is of paramount importance. The increasing reliance on technology and the growing interconnectedness of our lives have made us more vulnerable to cyber threats. Here are some key reasons why cybersecurity is crucial:
Protection of Personal Information: We live in an era where our personal and sensitive information is stored and shared online. From financial transactions to social media profiles, our information is at risk of being exposed or exploited by cybercriminals. Implementing robust cybersecurity measures helps safeguard our personal data and protects us from identity theft, fraud, and other cybercrimes.
Financial Security: Cybercrime can have severe financial implications. Businesses face the risk of financial loss, damage to the brand’s reputation, and legal consequences in the event of a data breach or cyber attack. Implementing effective cybersecurity measures minimizes these risks and ensures the financial stability of individuals and organizations.
Preserving Business Continuity: Any disruption to a company’s IT infrastructure can have significant consequences. Cyberattacks, such as ransomware or Distributed Denial of Service (DDoS), can lead to temporary or even permanent shutdown of systems, resulting in loss of productivity, customer trust, and revenue. By investing in cybersecurity, businesses can ensure the uninterrupted operation of critical systems, thereby preserving business continuity.
Protection of Intellectual Property: Intellectual property is a valuable asset for organizations. Cyber-espionage and theft of intellectual property can cripple businesses, disrupt innovation, and diminish their competitive edge. Cybersecurity measures, such as data encryption and access controls, can protect intellectual property from theft and unauthorized access.
Maintaining Customer Trust: In the digital era, customers entrust their personal information to businesses in exchange for products and services. A single data breach or privacy mishap can erode this trust and damage the reputation of a company. Demonstrating a commitment to cybersecurity reassures customers that their personal information is safe and can help maintain their trust and loyalty.
Protecting Critical Infrastructure: Cybersecurity is crucial for safeguarding key sectors such as energy, transportation, healthcare, and government. A cyberattack on critical infrastructure can have devastating consequences, affecting public safety, economic stability, and national security. Implementing robust cybersecurity measures protects these vital sectors from potential harm.
By recognizing the importance of cybersecurity and implementing proactive measures, individuals and organizations can mitigate risks, protect sensitive information, and ensure the smooth functioning of digital operations. Taking cybersecurity seriously is an investment in the stability, reliability, and security of our increasingly interconnected world.
Common Cyber Threats
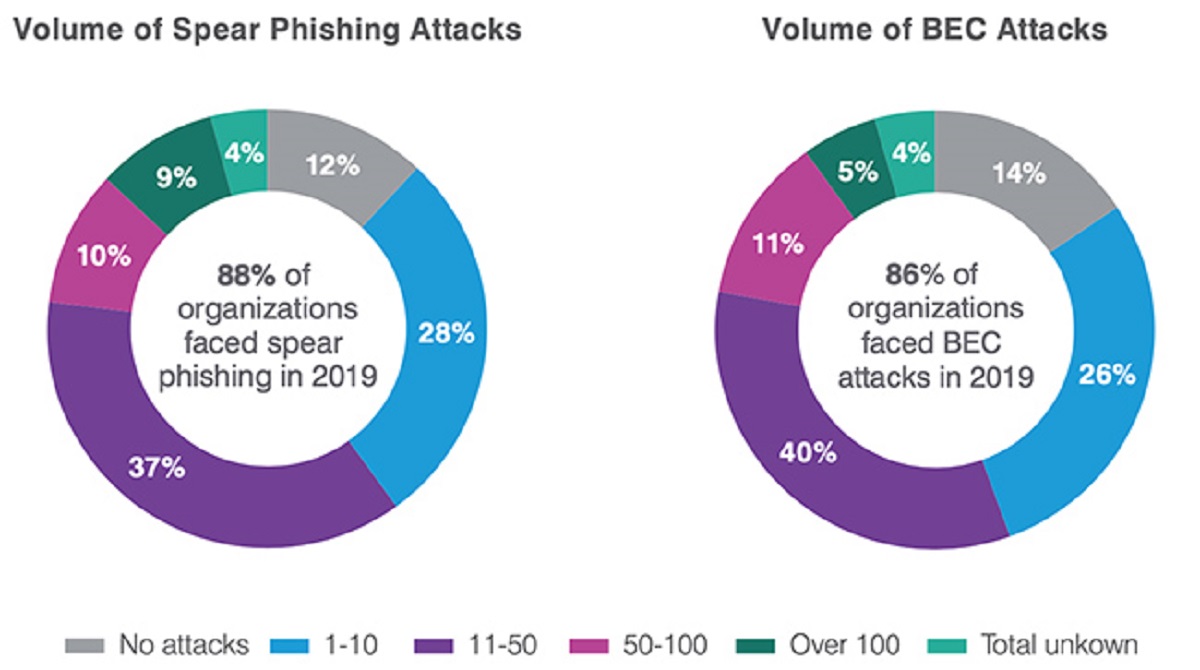
In the ever-evolving world of cybersecurity, cyber threats continue to grow in sophistication, posing significant risks to individuals and organizations alike. Understanding these threats is essential to implementing effective cybersecurity measures. Here are some of the most common cyber threats:
Malware: Malware, short for malicious software, is a broad term that encompasses various types of harmful software designed to disrupt or gain unauthorized access to computer systems. Common types of malware include viruses, worms, ransomware, and spyware. Malware can spread through infected email attachments, malicious websites, or removable media.
Phishing: Phishing is a technique used by cybercriminals to deceive individuals into revealing sensitive information, such as login credentials or financial details. Phishing attacks usually involve fraudulent emails or websites that mimic legitimate organizations, enticing victims to click on malicious links or provide confidential information.
Social Engineering: Social engineering involves manipulating individuals through psychological tactics to gain unauthorized access to systems or sensitive information. It often relies on human interactions, such as impersonating a trusted person or exploiting human weaknesses, rather than solely relying on technical vulnerabilities.
Denial-of-Service (DoS) Attacks: DoS attacks aim to overwhelm a target system or network, causing a disruption in its normal functioning. Attackers flood the target with a massive volume of traffic, rendering it unavailable to legitimate users. Distributed Denial-of-Service (DDoS) attacks employ multiple compromised devices to launch the attack, making it even more challenging to mitigate.
Insider Threats: Insider threats refer to attacks or breaches carried out by individuals within an organization who have authorized access to sensitive systems or data. Insiders can misuse their privileges intentionally or unintentionally, leading to data breaches, intellectual property theft, or sabotage.
Brute Force Attacks: Brute force attacks involve systematically trying every possible combination of passwords until the correct one is found. These attacks are often used to gain unauthorized access to user accounts or encrypted files. Implementing strong passwords and using account lockout mechanisms can help mitigate the risk.
Man-in-the-Middle (MitM) Attacks: MitM attacks occur when an attacker intercepts and potentially alters communications between two parties who believe they are directly communicating with each other. This allows the attacker to eavesdrop on sensitive information or manipulate data without the knowledge of the communicating parties.
SQL Injection: SQL injection involves exploiting vulnerabilities in a website or web application’s database layer to gain unauthorized access or manipulate data. By inserting malicious SQL code into user input fields, attackers can execute unauthorized database queries, leading to data breaches or unauthorized actions.
These are just a few examples of the many cyber threats that exist today. It is important to stay informed about emerging threats, keep systems and software up-to-date, and educate oneself and others about best practices to defend against these malicious activities.
Tips for Ensuring Cybersecurity
Protecting yourself and your digital assets from cyber threats requires a proactive approach. By following these essential tips, you can strengthen your cybersecurity defenses and reduce the risk of falling victim to cyber attacks:
Implementing Strong Passwords: Use unique, complex passwords for each of your online accounts. Include a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using easily guessable information, such as your name or birthdate, and consider using a reliable password manager to securely store and generate passwords.
Enable Two-Factor Authentication: Two-Factor Authentication (2FA) adds an extra layer of security by requiring an additional verification step, such as entering a unique code sent to your mobile device, in addition to your password. Enable 2FA wherever available, especially for your email, banking, and social media accounts.
Keep Software Updated: Regularly update the operating system, web browsers, applications, and antivirus software on your devices. Software updates often include important security patches that fix vulnerabilities and protect against the latest cyber threats.
Recognizing Phishing Attempts: Be cautious of emails, messages, or phone calls asking for personal information or urging you to click on suspicious links. Look for red flags, such as misspellings, unexpected requests, or unusual email addresses. When in doubt, verify the legitimacy of the communication through a trusted source.
Avoid Public Wi-Fi Networks: Public Wi-Fi networks can be insecure, making it easier for hackers to intercept your internet traffic and gain access to your sensitive information. Whenever possible, use a secure and private network, such as a virtual private network (VPN), or use your mobile data connection.
Use VPNs for Online Privacy: A VPN encrypts your internet traffic and routes it through a secure server, protecting your privacy and making it more difficult for attackers to track your online activities. Consider using a reputable VPN service, especially when accessing sensitive information or using public Wi-Fi networks.
Encrypting Sensitive Data: Encrypting sensitive data adds an additional layer of protection. Use encryption tools or features provided by your operating system or software applications to encrypt files and folders containing personal or confidential information.
Backing Up Important Files: Regularly back up your important files and data to an external hard drive, cloud storage, or a reliable backup service. In the event of a data breach, ransomware attack, or hardware failure, having backups ensures you can recover your valuable information.
Educating Employees on Cybersecurity: If you run a business, ensure that your employees receive regular training on cybersecurity best practices. Teach them how to identify potential threats, recognize phishing emails, and report any suspicious activities. Encouraging a culture of cybersecurity awareness is essential for protecting your organization’s digital assets and data.
Monitoring and Assessing Security Measures: Regularly monitor your systems for any signs of unusual activity or breaches. Utilize intrusion detection systems, log analysis, and network monitoring tools to identify potential threats. Conduct regular security assessments, such as penetration testing, to evaluate the effectiveness of your security measures.
By implementing these tips, you can significantly enhance your cybersecurity posture. Remember that cybersecurity is an ongoing effort and requires constant vigilance and adaptation to stay ahead of evolving threats. Stay informed, keep your defenses up-to-date, and prioritize security in both your personal and professional digital activities.
Implementing Strong Passwords
One of the most crucial steps in ensuring cybersecurity is implementing strong passwords. A strong password acts as a barrier to unauthorized access, protecting your online accounts from cybercriminals. Here are some essential tips to create and manage strong passwords:
Use Unique and Complex Passwords: Avoid using the same password for multiple accounts. Each online account should have its own distinct password. Create passwords that are complex and difficult to guess. Use a combination of uppercase and lowercase letters, numbers, and special characters.
Length Matters: The longer the password, the stronger it is. Aim for passwords that are at least 12 characters in length. Long and complex passwords are more challenging for attackers to crack using brute force or dictionary attacks.
Avoid Personal Information: Avoid using easily guessable information in your passwords, such as your name, birthdate, or address. Cybercriminals can easily gather personal information from social media or public records to guess your passwords.
Phrases and Acronyms: Consider using memorable phrases or acronyms as the basis for your passwords. For example, “ILove2Travel!” can be transformed into “IL2T!rvl”. Adding numbers, special characters, and altering the case can make it even stronger.
Password Managers: Consider using a reputable password manager to generate, store, and manage your passwords. Password managers create and remember strong passwords for you, eliminating the need to remember multiple complex passwords.
Frequent Password Changes: Periodically change your passwords to reduce the risk of compromise. Set a reminder to update your passwords every three to six months. If you suspect a potential breach or compromise, change your passwords immediately.
Multi-Factor Authentication (MFA): Enable Multi-Factor Authentication (MFA) whenever available. MFA adds an extra layer of security by requiring an additional verification step, such as a unique code sent to your mobile device, in addition to your password.
Avoid Sharing and Storing Passwords: Do not share your passwords with anyone, including friends or colleagues. Additionally, avoid storing passwords in plain text or on unsecured digital or physical locations. With password managers, you can store your passwords securely.
Stay Vigilant: Regularly monitor your accounts for any signs of unauthorized activity or suspicious behavior. If you notice any unusual activity, change your passwords immediately and report the incident to the respective service provider.
Education and Awareness: Educate yourself and others about the importance of strong passwords. Promote password security practices within your organization, and encourage colleagues, friends, and family members to implement strong passwords to protect their accounts.
Remember, strong passwords are your first line of defense against unauthorized access and account compromise. By creating unique and complex passwords, changing them periodically, and utilizing password managers, you can significantly enhance the security of your online accounts and protect your sensitive information from cyber threats.
Two-Factor Authentication
Two-Factor Authentication (2FA), also known as multi-factor authentication, is an additional layer of security that enhances the protection of your online accounts. With 2FA enabled, accessing an account requires not only a password but also a second form of verification. This adds an extra barrier for cybercriminals, even if they manage to obtain your password. Here’s how 2FA works and why it is essential for ensuring cybersecurity:
How does Two-Factor Authentication work?
When you enable 2FA on an account, a second factor of authentication is required in addition to your password. This second factor could be something you have, such as a security key or a verification code sent via text message or email, or something you are, such as a biometric scan like a fingerprint or facial recognition.
When you log in to your account, you will need to provide the second factor of authentication along with your password. This ensures that even if someone manages to steal or guess your password, they won’t be able to access your account without the second required factor.
Why is Two-Factor Authentication important?
Enhanced Security: 2FA significantly bolsters the security of your online accounts. Even if an attacker obtains your password, they would still need the second factor of authentication to gain access. This makes it much more challenging for unauthorized individuals to breach your accounts.
Protection of Personal Information: Many online accounts hold sensitive personal information, such as financial data, private conversations, or personal records. Enabling 2FA adds an extra layer of protection to safeguard this information from unauthorized access and potential misuse.
Defending Against Phishing Attacks: Phishing attacks rely on tricking users into entering their passwords on fraudulent websites or disclosing them through fake emails. By having 2FA enabled, even if you fall victim to a phishing attack and unknowingly provide your password, the attacker would still need the second factor of authentication to gain access to your account.
Securing Business Accounts: For businesses, 2FA is especially crucial. It helps prevent unauthorized access to company resources and protects sensitive data, including customer information and business communications. Implementing 2FA for employee accounts adds an extra layer of authentication, reducing the risk of security breaches and unauthorized data access.
Peace of Mind: Enabling 2FA provides peace of mind, knowing that your online accounts are better protected. It adds an extra level of assurance that even if your password is compromised, your accounts remain secure.
How to Enable Two-Factor Authentication:
Many online platforms and services offer options to enable 2FA. Check the account settings or security settings of the respective platform or service to find instructions on enabling 2FA. Generally, you will need to provide a phone number or an email address to receive the second factor of authentication.
Once you have enabled 2FA, remember to have your second factor of authentication readily available when logging in to your account. This could be your smartphone, a dedicated security key, or a biometric authentication method.
By enabling and using Two-Factor Authentication, you add an extra layer of protection to your online accounts, mitigating the risk of unauthorized access and enhancing your overall cybersecurity. Take advantage of this powerful security feature to safeguard your personal information and maintain control over your digital identity.
Keeping Software Updated
Keeping software updated is a vital aspect of maintaining a strong cybersecurity posture. Software updates, also known as patches or software upgrades, provide essential fixes, security patches, and new features that help protect your devices and data from vulnerabilities and exploit attempts. Here’s why keeping your software updated is crucial for your cybersecurity:
Patch Vulnerabilities: Software updates often include patches that fix known vulnerabilities in the software. By keeping your software up to date, you ensure that these vulnerabilities are addressed, reducing the risk of exploitation by cybercriminals. Vulnerabilities can be exploited to gain unauthorized access or control over your devices or to steal sensitive data.
Shield against Cyber Threats: Cyber threats are continually evolving, with new threats and attack methods emerging regularly. Keeping your software updated helps protect against the latest threats by ensuring that your devices and applications have the latest security features and configurations.
Protect Personal and Financial Information: Many software updates focus on fixing security vulnerabilities that could be exploited to steal your personal or financial information. Hackers often target outdated software with known vulnerabilities to gain access to sensitive data. By regularly updating your software, you reduce the risk of data breaches and identity theft.
Ensure Compatibility: Software updates often improve compatibility between different software components or devices. By keeping all your software up to date, you avoid compatibility issues that could lead to system crashes, data corruption, or other technical problems.
Enhance Performance and Stability: Software updates not only address security concerns but also often include performance enhancements and bug fixes. These improvements can result in faster and smoother operation of the software, providing a better user experience.
Automate Updates: Many software applications and operating systems offer automated update mechanisms, making it easy to keep your software up to date. Enable automatic updates whenever possible to ensure that you receive the latest security patches and bug fixes without requiring manual intervention.
Monitor Third-Party Software: It’s not just the operating system and major applications that need regular updates. Keep an eye on third-party software, such as browser plugins, extensions, or small utility programs, and ensure they are up to date. Cybercriminals often target outdated third-party software as a gateway to exploit vulnerabilities and gain unauthorized access to your system.
Stay Informed: Stay informed about the software you use and the potential vulnerabilities or security issues associated with it. Subscribe to software vendor newsletters, security blogs, or mailing lists to receive notifications about new software updates and security advisories.
Ensure a Proactive Approach: Don’t neglect the importance of software updates in your cybersecurity strategy. Adopt a proactive approach by regularly checking for updates, enabling automatic updates, and promptly installing new versions or patches. This will ensure that you are prepared to defend against the latest threats.
By prioritizing software updates, you significantly reduce the risk of security breaches, data loss, and other cybersecurity incidents. Make it a habit to regularly check for updates and install them promptly to keep your devices and data safe.
Recognizing Phishing Attempts
Phishing is a common cyber attack technique used by cybercriminals to deceive individuals into revealing sensitive information, such as usernames, passwords, or credit card details. Recognizing phishing attempts is essential for protecting yourself and your personal information from falling into the wrong hands. Here are some key tips to help you identify and avoid falling victim to phishing scams:
Be Wary of Suspicious Emails: Pay attention to emails that seem suspicious or unexpected. Be cautious when opening emails from unfamiliar senders or those that contain generic greetings instead of personalized ones. Look for red flags, such as misspellings, grammatical errors, or unusual email addresses.
Verify the Sender: Phishers often impersonate legitimate organizations or individuals to gain your trust. Check the sender’s email address, as subtle variations or misspellings can indicate fraudulent activity. If you receive an email from a familiar organization, verify its authenticity by contacting them directly using official contact information.
Be Mindful of Urgency or Threats: Phishers often create a sense of urgency or use threats to manipulate victims into taking immediate action. They may claim that your account will be closed, or you will face legal consequences if you do not provide your personal information promptly. Beware of such pressure tactics and verify the legitimacy of the request independently.
Don’t Click on Suspicious Links: Avoid clicking on links in emails, especially if they appear suspicious or unexpected. Hover your mouse over the link (without clicking) to see the actual URL it leads to. Be cautious of links that redirect you to unfamiliar or suspicious websites. When in doubt, manually type the known and trusted URL directly into your browser.
Beware of Requests for Personal Information: Legitimate organizations typically do not ask for personal information, such as passwords, Social Security numbers, or credit card details, via email. Be suspicious of any email that requests such sensitive information. Remember that reputable companies already have your information and would not need to ask you for it again.
Double-Check Website Security: Before entering any sensitive information on a website, ensure that the connection is secure. Look for “https://” at the beginning of the URL, indicating a secure, encrypted connection. A closed padlock icon in the browser’s address bar also signifies a secure connection.
Keep Security Software Updated: Maintain up-to-date antivirus and anti-malware software on your devices. This helps detect and prevent malicious links or attachments from infecting your system with malware that can steal your personal information.
Report and Delete Suspicious Emails: If you receive a suspicious email, do not engage with the sender. Report the email as spam or phishing to your email provider. Additionally, delete the email to prevent accidental clicks on any links or attachments.
Stay Educated and Informed: Stay updated on the latest phishing techniques and common scams. Educate yourself about how phishers operate and learn to identify the signs of a phishing attempt. Stay informed about new phishing trends and share this knowledge with friends, family, and colleagues.
By developing a cautious mindset and being vigilant, you can greatly reduce the risk of falling victim to phishing attempts. Remember that your personal information is valuable, and it’s essential to protect it by recognizing and avoiding phishing scams.
Avoiding Public Wi-Fi Networks
Public Wi-Fi networks have become ubiquitous, offering convenient internet access in cafes, airports, hotels, and other public spaces. While these networks provide convenience, they also pose several security risks. To safeguard your sensitive information and protect yourself from potential cyber threats, it is essential to be cautious when connecting to public Wi-Fi networks. Here are some important tips to help you avoid the risks associated with public Wi-Fi:
Use Your Mobile Data: Whenever possible, utilize your mobile data network instead of connecting to public Wi-Fi networks. Mobile data connections are generally more secure than public Wi-Fi networks, as they are encrypted and offer a dedicated connection.
Verify Network Authenticity: Before connecting to a public Wi-Fi network, verify the network’s authenticity. Cybercriminals often create fake Wi-Fi networks with names that resemble legitimate networks to trick users into connecting. Confirm the network name with the establishment or use their verified Wi-Fi network if available.
Connect to Trusted Networks: Whenever possible, connect to trusted and secured Wi-Fi networks, such as those provided by reputable hotels, businesses, or established public Wi-Fi networks. These networks are more likely to have proper security measures in place to protect users.
Utilize Hotspot Shielding: Consider using a Virtual Private Network (VPN) when connecting to public Wi-Fi networks. A VPN creates an encrypted connection, protecting your data from being intercepted or accessed by malicious actors on the same network. VPNs provide an additional layer of security and privacy for your online activities.
Avoid Accessing Sensitive Information: Avoid accessing or transmitting sensitive information, such as financial data, passwords, or personal details, when connected to a public Wi-Fi network. Assume that anything you do on the network can potentially be intercepted or monitored by cybercriminals.
Disable Automatic Wi-Fi Connections: Disable your device’s automatic connection feature to prevent it from connecting to any available public Wi-Fi networks without your knowledge. It helps you have greater control over your network connections and reduces the risk of connecting to malicious networks unknowingly.
Enable Firewall and Antivirus Protection: Ensure your device’s firewall and antivirus software are enabled and up to date. Firewalls add an extra layer of protection by monitoring and filtering incoming and outgoing network traffic, while antivirus software helps detect and prevent malware infections.
Keep Apps and Devices Updated: Regularly update your apps and operating system to ensure that you have the latest security patches and bug fixes. Software updates often address vulnerabilities that can be exploited by cybercriminals when connected to unsecured networks.
Consider Using a Wi-Fi Hotspot: If you must access sensitive information or perform secure transactions, consider using your mobile device as a Wi-Fi hotspot. This way, you can connect your other devices to your mobile device’s secure internet connection, providing a more secure browsing experience.
Stay Vigilant: Be vigilant when using public Wi-Fi networks and pay attention to any potential warning signs. Keep an eye out for any suspicious or unusual network behavior, such as frequent disconnections or slow network speeds, which could be indicators of a compromised network.
By following these best practices, you can minimize the risks associated with using public Wi-Fi networks and protect your sensitive information from falling into the wrong hands. It is essential to prioritize your online security and be proactive in safeguarding your digital privacy, even when using Wi-Fi networks outside the safety of your home or workplace.
Using VPNs for Online Privacy
In an increasingly connected world, maintaining online privacy and security has become crucial. A Virtual Private Network (VPN) can help you protect your personal information, maintain anonymity, and enhance your online privacy. Here’s why using a VPN is important and how it can benefit you:
Secure and Encrypted Connection: A VPN creates a secure and encrypted tunnel between your device and the internet. This encryption protects your data from eavesdropping and interception by unauthorized individuals, ensuring that your online activities remain private.
Anonymity and Privacy: When you connect to the internet through a VPN, your IP address and location are masked with the IP address of the VPN server. This provides a layer of anonymity, making it difficult for websites, ISPs, or malicious actors to track your online activities or identify your real-world location.
Bypassing Geo-Restrictions: VPNs allow you to bypass geographic restrictions imposed by certain websites or services. By connecting to a server in another country, you can access content that may otherwise be blocked or unavailable in your location.
Protection on Public Wi-Fi: When connected to public Wi-Fi networks, such as those in cafes or airports, your data is vulnerable to interception by hackers. By using a VPN, your data is encrypted, making it much more difficult for malicious actors to snoop on your online activities or steal your sensitive information.
Preventing ISP Tracking: Internet Service Providers (ISPs) have the ability to track your online activities and collect data about your browsing habits. By encrypting your internet connection with a VPN, you prevent your ISP from monitoring or logging your online activities, thereby preserving your privacy.
Secure Remote Access: VPNs enable secure remote access to private networks. This is particularly useful for individuals and businesses that need to connect to their home or office networks while traveling or working remotely. VPNs ensure that data transmitted between your device and the network is encrypted and protected from unauthorized access.
Protection from Cyber Attacks: VPNs provide an added layer of protection against cyber attacks, such as man-in-the-middle attacks or packet sniffing. By encrypting your connection, VPNs make it difficult for attackers to intercept data or manipulate it for malicious purposes.
Choosing a Reliable VPN: When selecting a VPN service, opt for reputable providers that prioritize privacy and have strong security protocols in place. Look for providers that do not keep logs of user activity and offer features such as kill switches and DNS leak protection to enhance your privacy.
Usage Considerations: While VPNs offer important privacy benefits, it is essential to remember that they are not a foolproof solution and should be used in conjunction with other security measures. Additionally, VPNs may slightly impact your internet speed due to encryption overhead, especially when connected to servers located far away.
Using a VPN is a proactive step towards protecting your online privacy and security. By encrypting your internet connection, maintaining your anonymity, and bypassing restrictions, VPNs provide a secure and private online experience. Consider using a VPN, especially when accessing the internet through public networks or conducting sensitive activities, to take control of your online privacy and maintain your digital freedom.
Encrypting Sensitive Data
As we increasingly rely on digital storage and transmission of sensitive information, the importance of encrypting data cannot be overstated. Encryption is a method of converting readable data into unreadable code, ensuring that only authorized parties with the decryption key can access and understand the information. Encrypting sensitive data provides an extra layer of protection against unauthorized access and data breaches. Here are some key reasons why encrypting sensitive data is crucial:
Data Protection: Encrypting sensitive data ensures that even if it falls into the wrong hands, it remains unreadable and unintelligible. Encryption algorithms use complex mathematical operations to scramble data, making it extremely difficult for unauthorized individuals to decipher the information without the corresponding decryption key.
Confidentiality: Encryption helps maintain the confidentiality of sensitive data, such as personal information, financial transactions, or confidential business records. It ensures that only authorized individuals, who possess the decryption key, can access and comprehend the data.
Compliance with Regulations: Various laws and regulations, such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA), require organizations to protect sensitive data through encryption. Compliance with these regulations is essential to avoid legal consequences and maintain the trust of customers and clients.
Protection against Data Breaches: Data breaches pose a significant threat, with cybercriminals continually seeking to exploit vulnerabilities and gain access to sensitive information. Encrypting data significantly reduces the likelihood of data breaches resulting in unauthorized access to personal or confidential data, even if the breached data is compromised.
Email and File Security: Encrypting sensitive emails and files adds an extra layer of security when transmitting or storing this data. By encrypting attachments or using secure email protocols, you minimize the risk of interception or unauthorized access to sensitive information through email or file transfer.
Mobile Device Security: With the ubiquity of smartphones and tablets, securing sensitive data on these devices is crucial. Encrypting data on mobile devices protects against physical theft or loss, ensuring that even if the device is accessed without authorization, the data remains encrypted and inaccessible.
Cloud Storage and Backup: When utilizing cloud storage or backup services, encrypting data before uploading it adds an additional layer of protection. Encrypting data ensures that even if there is a security breach or unauthorized access to the cloud storage, the encrypted data is of no use to the intruders.
End-to-End Encryption: End-to-end encryption is a method that ensures data remains encrypted throughout its entire journey, from the point of origin to the point of reception. This type of encryption is commonly used in messaging apps and video conferencing platforms, protecting the privacy of conversations and content exchanged between users.
Encryption Best Practices: To ensure effective data encryption, it is essential to utilize strong encryption algorithms, implement secure key management practices, regularly update encryption systems and software, and store encryption keys separately from the encrypted data.
By encrypting sensitive data, you protect it from unauthorized access, maintain confidentiality, comply with regulations, and reduce the risk of data breaches. Encryption is a fundamental component of a robust cybersecurity strategy, and everyone, from individuals to businesses, should prioritize the encryption of sensitive data to enhance privacy and security.
Backing Up Important Files
Backing up important files is an essential practice that protects your data from loss or damage. The loss of critical files, such as personal documents, business records, or cherished memories, can be devastating. Implementing a reliable backup strategy ensures that you have duplicate copies of your important files, enabling you to restore them in the event of data loss. Here’s why backing up important files is crucial:
Data Recovery: Accidental deletion, hardware failure, theft, natural disasters, or malware attacks can result in data loss. By regularly backing up your files, you can easily recover and restore them, minimizing the impact of data loss on your personal or professional life.
Protection against Ransomware: Ransomware attacks encrypt your files, holding them hostage until you pay a ransom. Having up-to-date backups allows you to restore your files without yielding to the attackers’ demands, avoiding financial loss and preserving your valuable data.
Version Control: Backup systems often include versioning capabilities, allowing you to store multiple versions of a file over time. This feature is particularly helpful in cases where you need to revert to an earlier version of a document or recover corrupted files.
Redundancy and Fault Tolerance: A backup system adds redundancy to your data storage, providing an additional layer of protection against data loss. By having duplicate copies of your files stored in separate locations or on different storage media, you reduce the risk of complete data loss due to hardware failure or disasters.
Peace of Mind: Knowing that your important files are securely backed up provides peace of mind. You can carry on with your daily activities, knowing that even if an unforeseen incident occurs and your primary data becomes inaccessible, you have a reliable backup to rely on.
Multiple Storage Options: Backup solutions offer various storage options, such as local external hard drives, network-attached storage (NAS), cloud storage, or offsite backups. Choose the option that best suits your needs and budget. Cloud storage provides the added advantage of remote access to your files from anywhere with an internet connection.
Scheduling and Automation: Implement a regular backup schedule and automate the process whenever possible. Set up automated backups to ensure that your files are regularly backed up without requiring manual intervention. This eliminates the risk of forgetting to back up important files.
Test Backup Integrity: Regularly check the integrity of your backups to ensure they are error-free and complete. Verify that files can be successfully restored from the backups and periodically test the restoration process to confirm that your backup system is working correctly.
Offsite Backups: Storing backups in an offsite location, separate from your primary data storage, protects against physical damage or loss due to unforeseen events like fires, floods, or theft. Consider using cloud storage or keeping physical backups in a secure location outside of your immediate premises.
Remember that having a single backup copy is not sufficient. Implementing the 3-2-1 backup rule is a recommended practice: maintain three copies of your important files, store them on two different storage media, and keep one copy offsite. This provides a comprehensive and reliable backup strategy.
By regularly backing up your important files, you ensure their availability and protect against data loss. Choose a reliable backup solution, define a backup schedule, and make it a habit to regularly back up your files. This simple practice provides invaluable peace of mind and safeguards your valuable data from unexpected events.
Educating Employees on Cybersecurity
Effective cybersecurity requires a collective effort, and employees play a crucial role in maintaining the security of an organization’s digital assets. Educating employees on cybersecurity best practices is essential to empower them with the knowledge and skills necessary to protect sensitive information and prevent cyber threats. Here are some key reasons why educating employees on cybersecurity is vital:
Human Element: Employees are often the first line of defense against cyber threats. Hackers frequently target individuals within an organization through tactics like phishing or social engineering. By educating employees on cybersecurity, they become more equipped to recognize and respond appropriately to these types of attacks.
Improved Awareness: Cybersecurity education helps employees develop a heightened sense of awareness regarding the potential risks and threats they may encounter. By understanding the common tactics used by cybercriminals, employees can be more alert and cautious in their online activities, reducing the likelihood of falling victim to attacks.
Protecting Sensitive Data: Educating employees about the significance of safeguarding sensitive data, such as customer information or trade secrets, helps foster a culture of data protection. Through training, employees gain an understanding of the importance of handling and storing data securely, reducing the risk of data breaches or unauthorized access.
Preventing Insider Threats: Insider threats pose a significant risk to organizations. Employees who are unaware of proper cybersecurity practices may unknowingly compromise security or intentionally engage in malicious activities. By educating employees on cybersecurity, organizations can reduce the likelihood of insider threats and minimize potential damages.
Secure Remote Work: With the rise of remote work, it is essential to educate employees on secure remote practices. This includes using secure networks, enabling two-factor authentication, encrypting devices, and ensuring the secure transmission of data. By providing necessary guidance, organizations can maintain a secure remote work environment.
Role-Specific Training: Different roles within an organization may have different cybersecurity needs. Tailoring cybersecurity education to specific job functions, such as IT administrators, finance personnel, or customer service representatives, ensures that employees receive specialized training to address the unique risks and challenges they may encounter.
Regular Updates: Cybersecurity threats and best practices evolve rapidly. Ongoing education and regular training sessions help employees stay up to date with the latest security trends, emerging threats, and mitigation strategies. This ensures that their knowledge and skills are continually refreshed and aligned with current industry practices.
Promoting a Cybersecurity Culture: Educating employees on cybersecurity fosters a culture of proactive security-consciousness within an organization. By creating an environment where cybersecurity is prioritized, employees are more likely to adopt secure practices, report potential threats, and actively contribute to the overall security posture of the organization.
Leading by Example: Leadership involvement in cybersecurity education is critical. When executives and managers actively participate and demonstrate a commitment to cybersecurity, it reinforces the importance of cybersecurity awareness throughout the organization. Executives should not only support training initiatives but also adhere to cybersecurity policies themselves.
Educating employees on cybersecurity is a crucial investment in protecting an organization’s digital assets. By raising awareness, fostering a culture of cybersecurity, and providing role-specific training, organizations empower their employees to become effective guardians against cyber threats. Continuous education ensures that employees remain well-informed and prepared to face the ever-evolving challenges of the digital landscape.
Monitoring and Assessing Security Measures
Monitoring and assessing security measures are essential components of a robust cybersecurity strategy. Simply implementing security measures is not enough; organizations must ensure that these measures are functioning effectively and provide adequate protection against evolving cyber threats. Here’s why monitoring and assessing security measures are crucial:
Early Detection of Security Incidents: Continuous monitoring allows organizations to detect and respond to security incidents in their early stages. By monitoring security systems, networks, and endpoints, suspicious activities, anomalies, or indicators of compromise can be identified, enabling swift action to mitigate potential damage and prevent further compromise.
Real-Time Threat Intelligence: Monitoring security measures provides access to real-time threat intelligence. This includes information about emerging threats, new exploit methods, and vulnerabilities being actively exploited by cybercriminals. Utilizing this intelligence allows organizations to update security systems, implement patches, and strengthen their defenses in response to the latest threats.
Assessing Effectiveness of Controls: Regular assessments of security measures help organizations evaluate the effectiveness of their existing controls and identify any weaknesses or gaps in their security posture. This enables proactive remediation of vulnerabilities and the implementation of additional security measures as necessary.
Compliance with Standards and Regulations: Monitoring and assessing security measures ensure compliance with industry standards and regulations that govern data protection and privacy. Regular assessments help organizations validate their adherence to these standards, such as the Payment Card Industry Data Security Standard (PCI DSS) or the General Data Protection Regulation (GDPR).
Identifying Security Trends and Patterns: Continuous monitoring allows organizations to identify emerging security trends and patterns. Monitoring activities such as network traffic, user behaviors, and access logs can help detect patterns that may indicate ongoing or potential security threats. Recognizing these patterns enables proactive measures to mitigate risks before they manifest into significant security incidents.
Testing Incident Response Readiness: Regularly monitoring and assessing security measures provides an opportunity to test the incident response capabilities of an organization. By performing simulated security incidents, organizations can evaluate the effectiveness of their response plans, identify areas of improvement, and refine their incident response processes.
Enhancing Security Awareness and Training: Monitoring security measures creates data and insights that can be used for security awareness and training purposes. Analytics derived from monitoring activities can help identify common user errors, security policy violations, or areas requiring additional training. This data-driven approach enables organizations to focus training efforts on the specific areas that need improvement.
Staying Ahead of Evolving Threat Landscape: Cyber threats are dynamic and constantly evolving. The practice of monitoring and assessing security measures ensures that organizations remain proactive in adapting their security controls to counter new threats. By monitoring the effectiveness of existing measures and implementing necessary enhancements, organizations can stay ahead of cybercriminals.
Collaboration and Communication: Monitoring security measures encourages collaboration and communication among various stakeholders within an organization. Regular security assessments and reporting facilitate knowledge sharing, promote a culture of security awareness, and ensure that relevant parties are informed about the overall security status and any necessary actions.
Monitoring and assessing security measures are essential for an effective cybersecurity program. By leveraging real-time threat intelligence, identifying vulnerabilities, and proactively addressing security gaps, organizations can enhance their security posture and reduce the risk of successful cyberattacks.
Conclusion
In today’s interconnected world, ensuring cybersecurity is more critical than ever before. Cyber threats continue to evolve, putting individuals and organizations at risk of cyberattacks, data breaches, and financial loss. By implementing essential practices and educating ourselves and others, we can strengthen our cybersecurity defenses and protect our digital lives.
We have explored various aspects of cybersecurity, from understanding the importance of cybersecurity to recognizing common cyber threats. We have seen the significance of strong passwords, two-factor authentication, and keeping software updated. Recognizing phishing attempts, avoiding public Wi-Fi networks, and using VPNs for online privacy are crucial steps in safeguarding our digital privacy. Moreover, encrypting sensitive data, backing up important files, and monitoring and assessing security measures all play vital roles in protecting against cyber threats.
Educating employees on cybersecurity is essential for creating a strong security culture within organizations. By providing comprehensive training, tailored to specific roles and responsibilities, organizations equip their employees with the knowledge and skills needed to identify and address potential threats.
Continual monitoring and assessment of security measures are vital to maintain an effective cybersecurity strategy. By staying proactive, organizations can detect security incidents early, identify vulnerabilities, and constantly adapt to emerging threats in the ever-evolving cyber landscape.
Remember, cybersecurity is a collective responsibility. By following best practices, implementing robust security measures, and staying informed about emerging threats, we can all contribute to a safer digital environment. Whether you are an individual internet user or an organization handling sensitive data, prioritizing cybersecurity is crucial to protect our personal information, finances, and digital assets.
By adopting a proactive and informed approach to cybersecurity, we can mitigate the risks, safeguard our digital lives, and navigate the digital landscape with confidence.