Introduction
Welcome to the world of cybersecurity services, where protecting digital assets and combating online threats are of utmost importance. As technology continues to advance, so do the risks associated with it. This has created a high demand for cybersecurity solutions to safeguard sensitive data, systems, and networks from unauthorized access and malicious attacks.
In this era of rapid digital transformation, businesses of all sizes and industries are increasingly recognizing the need to invest in cybersecurity to mitigate risks and protect their valuable assets. This presents a lucrative opportunity for cybersecurity service providers to offer their expertise and help organizations navigate the complex landscape of online security.
Whether you are an established IT company looking to diversify your offerings or a cybersecurity enthusiast considering entering the industry, selling cybersecurity services requires a strategic approach. This comprehensive guide will walk you through the key steps and considerations to effectively sell cybersecurity services.
From assessing your cybersecurity expertise to understanding market demand, building a compelling value proposition, and developing a marketing and sales strategy, we will explore every aspect of the journey. We will also delve into practical tips for engaging potential customers, overcoming objections, and delivering high-quality cybersecurity services.
Successful selling of cybersecurity services goes beyond simply promoting software or hardware products. It involves in-depth knowledge of different cybersecurity domains, staying updated on the latest threats, and continually adapting to the evolving landscape. By mastering the art of selling cybersecurity services, you can not only protect organizations from cyber threats but also establish a financially rewarding business.
So, let’s dive into the world of cybersecurity services and equip ourselves with the knowledge and strategies needed to thrive in this ever-growing field.
Understanding the Market Demand for Cybersecurity Services
In today’s interconnected digital world, the demand for cybersecurity services is higher than ever before. Organizations are increasingly recognizing the importance of protecting their sensitive data, intellectual property, and customer information from evolving cyber threats. Understanding the market demand for cybersecurity services is essential for positioning your offerings and capturing a share of this growing market.
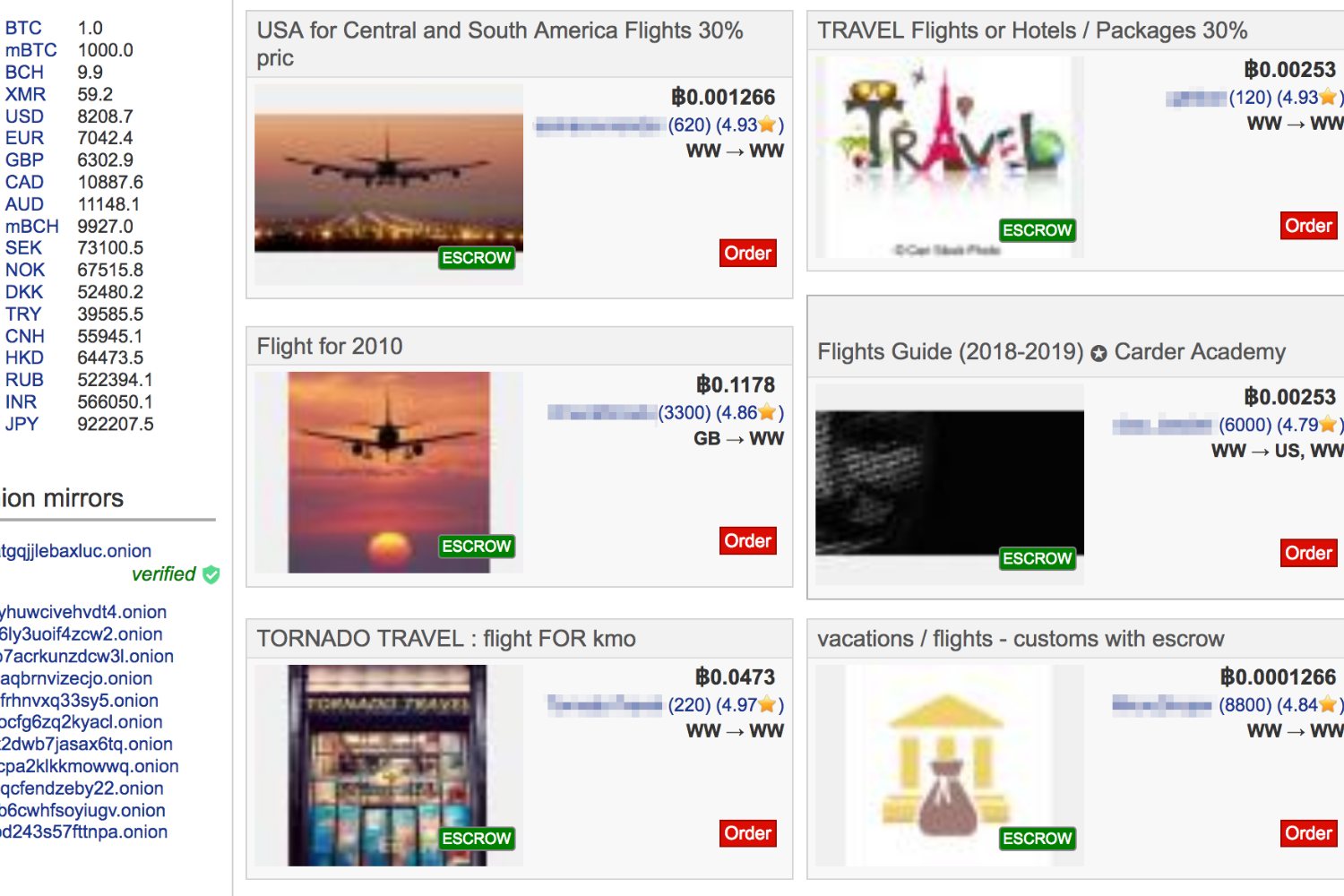
One of the key drivers of market demand for cybersecurity services is the rise in cybercrime. Hackers and cybercriminals are constantly devising new and sophisticated ways to infiltrate systems and exploit vulnerabilities. High-profile incidents of data breaches and ransomware attacks have resulted in significant financial losses and reputational damage for many companies. As a result, businesses are now proactively seeking cybersecurity services to prevent and mitigate these risks.
Another factor contributing to the market demand for cybersecurity services is the increasing adoption of cloud computing and digital technologies. As organizations digitize their operations and move their data and applications to the cloud, they need robust security measures to protect their assets from unauthorized access and data leaks. Managed security services, intrusion detection systems, and vulnerability assessments are in high demand to ensure the integrity and confidentiality of cloud-based infrastructure.
Furthermore, compliance requirements and regulations have become stricter across various industries. Organizations are legally obligated to maintain the privacy and security of customer data, such as personal information and financial records. Failure to comply with these regulations can result in severe penalties and damage to a company’s reputation. This has led to a surge in demand for cybersecurity services that can help businesses meet regulatory standards and protect sensitive data.
The market demand for cybersecurity services is not limited to large enterprises. Small and medium-sized businesses (SMBs) are increasingly becoming targets of cyberattacks due to their often more vulnerable security infrastructure. SMBs are realizing the need to invest in cybersecurity solutions to safeguard their operations and maintain customer trust. This represents a significant growth opportunity for cybersecurity service providers who can offer tailored solutions to meet the unique needs and budget constraints of SMBs.
Overall, the market demand for cybersecurity services is driven by the escalating threat landscape, the adoption of digital technologies, and regulatory requirements. By understanding these factors and staying abreast of industry trends, you can position your cybersecurity services as a valuable and necessary investment for organizations of all sizes and industries.
Assessing Your Cybersecurity Expertise and Capabilities
Before diving into selling cybersecurity services, it is crucial to assess your expertise and capabilities in the field. This will help you determine your strengths, identify any knowledge gaps, and determine the types of cybersecurity services you can effectively offer to clients.
Start by evaluating your team’s qualifications and experience. Assess each team member’s expertise in areas such as network security, data protection, incident response, vulnerability assessment, and compliance. You may need to invest in additional training or certifications to enhance your team’s skills and ensure you have a well-rounded cybersecurity workforce.
Next, evaluate your infrastructure and technology resources. Determine if you have the necessary tools and software to deliver cybersecurity services effectively. This may include firewalls, antivirus software, intrusion detection systems, vulnerability scanning tools, and monitoring solutions. If you lack certain resources, consider investing in them or partnering with a third-party provider to augment your capabilities.
Assessing your cybersecurity expertise also involves staying up to date with the latest industry trends and best practices. Cybersecurity is a rapidly evolving field, with new threats, attack vectors, and mitigation techniques emerging regularly. Ensure that you and your team are continually learning and engaging in professional development activities to stay ahead of the curve.
Additionally, consider the specific industries or sectors you have experience in. Some industries may have unique compliance requirements or industry-specific cybersecurity challenges. By focusing on a particular niche or industry, you can position yourself as a specialized expert and attract clients within that sector.
Lastly, evaluate your track record and past client projects. Assess the success and impact of the cybersecurity solutions you have provided in the past. Collect case studies and testimonials that highlight your expertise and accomplishments. This will not only help you showcase your capabilities to potential clients but also give you insights into areas where you can further improve your services.
By conducting a thorough assessment of your cybersecurity expertise and capabilities, you can identify your strengths, address any gaps, and position yourself as a trusted and knowledgeable cybersecurity service provider. This self-evaluation will guide you in determining the types of services you can confidently deliver and help you build a strong foundation for your cybersecurity business.
Building a Comprehensive Cybersecurity Service Offering
Building a comprehensive cybersecurity service offering is essential to meet the diverse needs of clients and stand out in the competitive marketplace. By combining various services, you can provide a holistic approach to cybersecurity that addresses the different layers of protection required by organizations. Here are some key steps to consider when building your cybersecurity service offering:
1. Conduct a Needs Assessment: Start by understanding the specific cybersecurity challenges and requirements of your target clients. Conduct assessments and consultations to identify their vulnerabilities, compliance needs, and risk tolerance. This will help you tailor your service offering to their unique needs.
2. Define Service Categories: Categorize your services based on different cybersecurity domains. This could include network security, endpoint protection, cloud security, data security, incident response, and compliance. By defining these categories, you can offer a range of specialized services and highlight your expertise in each area.
3. Determine Service Levels: Based on the severity of cyber threats and the level of protection needed, develop service level options for clients. This could range from basic cyber hygiene services to advanced threat detection and response solutions. Clearly articulate the scope, deliverables, and pricing for each service level to ensure transparency.
4. Partner with Technology Providers: Build partnerships with reputable technology providers to enhance your service offering. This could include partnerships with firewall vendors, antivirus software companies, and network monitoring tools. By leveraging these partnerships, you can provide clients with best-in-class security solutions.
5. Offer Managed Security Services: Consider offering managed security services where you proactively monitor and manage clients’ security infrastructure. This can include 24/7 monitoring, incident response, patch management, and vulnerability assessments. Managed services provide ongoing value to clients and establish long-term relationships.
6. Develop Security Policies and Frameworks: Create comprehensive security policies and frameworks that clients can implement to improve their overall security posture. Offer consulting services to help clients develop and implement these policies, ensuring they align with industry standards and compliance requirements.
7. Provide Employee Training and Awareness: Offer security awareness training programs to educate client employees on best practices, phishing awareness, password management, and social engineering tactics. By investing in employee training, you can help clients build a security-minded culture within their organizations.
8. Stay Updated with Emerging Threats: Continuously monitor the cybersecurity landscape to identify new threats and vulnerabilities. Update your service offering to address emerging risks promptly. This demonstrates your commitment to staying ahead of the curve and providing the most effective cybersecurity solutions.
By building a comprehensive cybersecurity service offering, you can attract a wide range of clients and position yourself as a trusted expert in the industry. Continuously refine and expand your service offering based on market demand and emerging trends to ensure you remain a top choice for organizations seeking robust cybersecurity solutions.
Identifying Potential Target Customers
Identifying potential target customers is a critical step in selling cybersecurity services. By understanding your target audience, their unique needs, and pain points, you can effectively tailor your marketing and sales strategies to attract the right clients. Here are some key factors to consider when identifying potential target customers:
1. Industry and Verticals: Start by identifying industries or verticals that are most likely to require cybersecurity services. Industries such as finance, healthcare, e-commerce, and government tend to have stringent security requirements and may be more willing to invest in comprehensive cybersecurity solutions.
2. Company Size: Consider the size of companies you want to target. Large enterprises typically have more complex IT infrastructure and higher security needs, making them potential clients for advanced cybersecurity services. Small and medium-sized businesses (SMBs), on the other hand, may require more affordable and scalable cybersecurity solutions that fit their budget and resource constraints.
3. Geographical Location: Assess the geographical areas in which you want to operate. Certain regions or countries may have higher cybersecurity needs or face specific regulatory challenges. Understanding the local market dynamics will help you target customers effectively.
4. Compliance Requirements: Identify industries or jurisdictions with strict compliance requirements, such as healthcare (HIPAA), finance (PCI DSS), or data privacy regulations (GDPR). These organizations are more likely to invest in cybersecurity services to ensure they meet regulatory standards and protect sensitive information.
5. Existing Connections and Networks: Leverage your existing connections and networks to identify potential customers. Reach out to your professional contacts, attend industry conferences and events, and join relevant online communities to establish relationships with individuals and organizations that may require cybersecurity services.
6. Competitor Analysis: Analyze your competitors’ target customers to identify gaps and opportunities. Determine the types of clients they serve, their marketing strategies, and the unique selling propositions they offer. This will help you differentiate your services and tailor your offerings to meet the specific needs of overlooked segments.
7. Pain Points and Challenges: Understand the pain points and challenges that potential customers face in relation to cybersecurity. This could include concerns about data breaches, compliance issues, or lack of in-house expertise. Tailor your messaging and solutions to address these pain points effectively.
8. Budget Considerations: Determine the budget range of potential customers to ensure your service offerings align with their financial capabilities. Offering flexible pricing options, such as scalable packages or subscription-based models, can attract a wider range of clients.
By identifying and targeting potential customers based on industry, company size, compliance requirements, geographical location, and pain points, you can focus your marketing efforts and resources on the most relevant prospects. This strategic approach will optimize your chances of attracting customers who have a genuine need for your cybersecurity services.
Creating a Compelling Value Proposition for Your Cybersecurity Services
Creating a compelling value proposition is crucial in differentiating your cybersecurity services from competitors and attracting potential customers. A strong value proposition communicates the unique benefits and value that clients will receive by choosing your services. Here are key steps to create a compelling value proposition:
1. Identify the Core Benefits: Start by identifying the core benefits that your cybersecurity services offer. Consider how your services address the specific pain points and challenges that clients face, such as protecting sensitive data, mitigating cyber threats, and ensuring regulatory compliance. Highlight the positive outcomes that clients can expect from using your services.
2. Understand Your Target Customers: Gain a deep understanding of your target customers’ needs, goals, and priorities. Identify their motivations for seeking cybersecurity services and the specific outcomes they are looking to achieve. This will help you tailor your value proposition to resonate with their unique requirements.
3. Highlight Your Expertise and Experience: Showcase your expertise and experience in the cybersecurity field. Highlight key certifications, years of experience, and success stories of past clients. This will establish your credibility and position you as a trusted authority in the industry.
4. Differentiate from Competitors: Identify what sets your cybersecurity services apart from competitors. This could include proprietary technology, unique methodologies, or specialized areas of expertise. Differentiation can be based on factors such as speed of response, customized solutions, or proactive threat intelligence. Clearly articulate these differentiators in your value proposition to showcase your competitive advantage.
5. Quantify the Value: Whenever possible, quantify the value your cybersecurity services bring to clients. This can be in terms of cost savings, risk reduction, improved productivity, or increased regulatory compliance. Demonstrating tangible benefits helps clients understand the return on investment they can expect by engaging your services.
6. Emphasize Trust and Security: In the cybersecurity industry, trust is paramount. Highlight the measures you take to ensure the confidentiality, integrity, and availability of client data and systems. Emphasize the security controls, data protection protocols, and compliance standards you adhere to. Instilling confidence in clients will reinforce your value proposition.
7. Focus on Customer Success: Position your value proposition around the success of your customers. Showcase testimonials, case studies, and success stories that highlight how your services have helped organizations overcome cybersecurity challenges and achieve their goals. This social proof will strengthen the credibility of your value proposition.
8. Customize for Each Customer Segment: Tailor your value proposition to different customer segments based on their specific needs and pain points. Avoid a one-size-fits-all approach and craft messaging that speaks directly to the concerns and priorities of each segment. This personalized approach will resonate more strongly with potential customers.
By creating a compelling value proposition for your cybersecurity services, you can effectively communicate the unique benefits and value you bring to clients. Your value proposition should clearly articulate how your services address their needs, differentiate from competitors, quantify the value delivered, and establish trust and credibility. Continuously refine and evolve your value proposition based on feedback and market trends to ensure it remains relevant and impactful.
Pricing Your Cybersecurity Services Effectively
Pricing your cybersecurity services effectively is crucial in ensuring that your offerings are competitive, profitable, and align with the value you provide to clients. Here are key considerations to help you establish a pricing strategy for your cybersecurity services:
1. Understand Your Costs: Begin by thoroughly understanding your costs associated with delivering cybersecurity services. This includes factors such as employee salaries, technology investments, software licenses, and ongoing maintenance and updates. Accurately accounting for your costs will help you determine a baseline for pricing.
2. Value-Based Pricing: Consider adopting a value-based pricing approach, where the price aligns with the perceived value and benefits that clients receive from your services. Assess the potential cost savings, risk reduction, and improved security posture that your services offer, and price accordingly. This approach enables you to capture a fair share of the value you deliver.
3. Research Competitor Pricing: Conduct market research to understand the pricing strategies of your competitors. Analyze how your offering compares to theirs in terms of features, quality, and expertise. Position your pricing in a way that reflects the value and differentiation you offer relative to competitors.
4. Tiered Pricing: Consider offering tiered pricing options to cater to different customer segments and their specific needs. This allows clients to choose the level of service that aligns with their budget and requirements. Each tier can offer increasing levels of features, support, and security measures.
5. Additional Service Options: Offer additional service options and add-ons that clients can choose from, allowing them to customize their cybersecurity package. This can include services such as penetration testing, incident response retainer, employee training, or compliance audits. By providing these flexible options, you can cater to specific client needs and generate additional revenue.
6. Long-Term Contracts: Consider offering discounts or incentives for clients who commit to long-term contracts. This provides you with a predictable revenue stream and encourages client loyalty. However, ensure that the terms and conditions of long-term contracts are carefully drafted to protect your interests.
7. Pricing Transparency: Be transparent about your pricing structure and ensure clients have a clear understanding of what is included in each package. Clearly communicate the scope of services, any limitations, and potential additional fees or charges. Pricing transparency builds trust and avoids any surprises down the line.
8. Flexibility for SMBs: Recognize the budget constraints of small and medium-sized businesses (SMBs) and consider offering flexible pricing options that cater to their needs. This can include scaled-down packages or subscription models that are affordable and scalable. By catering to this market segment, you can tap into a significant customer base.
Regularly review and analyze your pricing strategy to ensure it remains competitive and aligned with market trends. Pay attention to client feedback and adapt your pricing as necessary. Ultimately, effective pricing involves finding the right balance between capturing the value you offer and meeting the budgetary constraints and expectations of your target customers.
Developing a Marketing and Sales Strategy for Your Cybersecurity Services
Developing a robust marketing and sales strategy is essential for effectively promoting and selling your cybersecurity services. A well-defined strategy will help you reach your target audience, generate leads, and convert them into paying clients. Here are key steps to develop a marketing and sales strategy for your cybersecurity services:
1. Define Your Target Audience: Start by identifying your ideal target audience. Consider factors such as industry, company size, geographical location, compliance requirements, and pain points. Understanding your target audience will help tailor your marketing messages and tactics to resonate with their specific needs.
2. Craft Your Unique Value Proposition: Develop a compelling value proposition that differentiates your cybersecurity services from competitors. Clearly communicate the unique benefits and value clients will receive by choosing your services. Highlight your expertise, experience, and the specific problems your services address.
3. Build Your Online Presence: Establish a strong online presence to increase your visibility and credibility. Create a professional website that showcases your services, case studies, testimonials, and industry certifications. Optimize your website for search engines to improve organic traffic. Leverage social media platforms, relevant forums, and industry blogs to engage with your target audience and share valuable content.
4. Content Marketing: Develop informative and educational content that highlights your expertise and addresses the pain points of your target audience. This can include blog posts, whitepapers, ebooks, videos, and infographics. Distribute your content through various channels to attract and engage potential clients. Focus on providing value and establishing yourself as a trusted authority in the cybersecurity field.
5. Thought Leadership and Speaking Engagements: Position yourself and your team as thought leaders in the cybersecurity industry. Publish articles in industry publications, contribute to relevant cybersecurity forums, and offer to speak at industry conferences and events. Thought leadership establishes credibility and raises awareness of your services among key decision-makers.
6. Strategic Partnerships: Build strategic partnerships with complementary service providers or technology vendors. This can include IT companies, managed service providers, or cloud service providers. Collaborate on joint marketing efforts, referrals, and co-hosting events to expand your reach and tap into their networks.
7. Lead Generation and Nurturing: Implement lead generation strategies to capture potential clients’ information and nurture them through the sales funnel. This can include offering valuable gated content, hosting webinars, and running targeted advertising campaigns. Use email marketing, personalized follow-ups, and marketing automation to nurture leads and build relationships with prospects.
8. Network and Industry Involvement: Attend industry conferences, join relevant industry associations, and participate in networking events to connect with potential clients and industry influencers. Establishing relationships and staying active in the cybersecurity community can open doors for partnerships and generate referrals.
9. Sales Enablement: Equip your sales team with the necessary tools, resources, and training to effectively sell your cybersecurity services. Develop sales collateral, such as presentations, case studies, and FAQs, to support the sales process. Continuously monitor sales performance, provide feedback, and refine your strategies based on market feedback and client interactions.
By developing a comprehensive marketing and sales strategy, you can effectively reach your target audience, generate leads, and convert them into loyal clients. Continuously monitor and adjust your strategies based on market trends and client feedback to ensure you stay competitive in the ever-evolving cybersecurity landscape.
Approaching and Engaging Potential Customers
Approaching and engaging potential customers is a critical step in converting leads into paying clients for your cybersecurity services. By implementing effective strategies and tactics, you can build relationships, establish trust, and ultimately persuade potential customers to choose your services. Here are key steps to approach and engage potential customers:
1. Personalized Outreach: Tailor your outreach efforts to each potential customer to demonstrate that you understand their specific cybersecurity needs. Craft personalized emails, LinkedIn messages, or direct mail pieces that address their pain points and highlight how your services can provide solutions. Avoid generic, one-size-fits-all messages that can create the perception of spam.
2. Targeted Advertising: Utilize targeted online advertising campaigns to reach potential customers who fit your ideal client profile. Use platforms such as Google Ads, social media advertising, or industry-specific websites to display your ads to relevant audiences. Focus on delivering compelling messaging and captivating visuals to grab the prospects’ attention and generate interest.
3. Thought Leadership Content: Share valuable content that positions you as a thought leader and expert in the cybersecurity field. Develop blog posts, articles, or videos that provide insights, tips, and industry updates. Distribute your content through channels such as your website, social media, email newsletters, and industry publications to capture the attention of potential customers.
4. Networking and Referrals: Build relationships and expand your network within the cybersecurity industry. Attend industry events, join professional associations, and actively engage in online forums and communities. Establishing credibility and relationship-building can lead to referrals from industry peers or satisfied clients who can vouch for your services.
5. Free Consultations or Assessments: Offer complimentary cybersecurity consultations or assessments to potential customers. This allows you to identify their specific pain points and propose tailored solutions. Demonstrating your expertise during these sessions can build trust and credibility, increasing the chances of them engaging your services.
6. Webinars and Workshops: Host webinars or workshops on cybersecurity-related topics that are of interest to your target audience. Offer valuable insights, practical tips, and action steps they can take to enhance their cybersecurity posture. This positions you as a knowledgeable resource and builds trust with potential customers who attend these events.
7. Case Studies and Testimonials: Showcase real-life examples of how your cybersecurity services have helped clients overcome challenges and achieve desired outcomes. Develop compelling case studies and collect testimonials from satisfied clients. Publish these on your website, social media, and other marketing materials to demonstrate your track record and success stories to potential customers.
8. Follow-Up and Relationship Building: Consistently follow up with potential customers to nurture the relationship and keep your services top of mind. Personalize your follow-ups based on previous interactions and their specific needs. Provide additional information, answer questions, and offer ongoing support to demonstrate your commitment to their cybersecurity success.
Approaching and engaging potential customers requires a strategic and personalized approach. By understanding their needs, providing valuable insights, and nurturing relationships, you can effectively convert leads into loyal clients for your cybersecurity services.
Demonstrating the Value of Your Cybersecurity Services
Demonstrating the value of your cybersecurity services is crucial in convincing potential customers that investing in your offerings is beneficial to their organization. By effectively showcasing the benefits, outcomes, and return on investment (ROI) of your services, you can build trust and credibility. Here are key strategies to demonstrate the value of your cybersecurity services:
1. Communicate the Impact: Clearly articulate the tangible impact your cybersecurity services will have on the potential customer’s business. Highlight how your services will protect their sensitive data, prevent security breaches, maintain regulatory compliance, and safeguard their reputation. Use real-world examples, statistics, or case studies to support your claims.
2. ROI Calculation: Help potential customers understand the financial value and return on investment they can expect by engaging your services. Calculate the potential cost savings or risk reduction that your services provide. Showcase the ROI by comparing the investment in your services to the potential financial losses they could incur from a security breach.
3. Highlight Expertise and Experience: Emphasize your team’s expertise, certifications, and extensive experience in the cybersecurity industry. Showcase case studies and testimonials from satisfied clients who have benefited from your services. This demonstrates that you have a track record of delivering value and instills confidence in potential customers.
4. Demonstrate Industry Compliance: If your potential customers operate in industries with specific compliance requirements, demonstrate how your services can help them meet those standards. Highlight your expertise in industry-specific regulations and frameworks. Assure potential customers that by engaging your services, they will be better positioned to pass compliance audits and avoid penalties.
5. Showcase Technology Partnerships: If you partner with leading technology providers, emphasize how these partnerships enhance your service offering. Highlight the cutting-edge tools, technologies, and security measures you employ to deliver optimal protection to clients’ sensitive data. The credibility of reputable technology partnerships reinforces the value of your services.
6. Client Testimonials and Case Studies: Collect testimonials and case studies from satisfied clients who have experienced the value of your cybersecurity services firsthand. These success stories provide social proof and demonstrate the positive impact you have had on previous clients’ security posture. Share these testimonials on your website, marketing materials, and sales presentations.
7. Demonstrations and Trials: Offer potential customers the opportunity to experience your services firsthand through product demonstrations or trial periods. This allows them to see the value and benefits in action, gaining confidence in both your services and the impact they can have on their organization. Ensure that these demonstrations or trials are accompanied by clear explanations of how the services address their specific needs.
8. Continuous Support and Monitoring: Emphasize the ongoing support, monitoring, and improvement that your services provide even after the initial implementation. Highlight your commitment to staying proactive against emerging threats and technologies. Demonstrating that your services adapt and evolve with the evolving cybersecurity landscape reinforces their long-term value.
By effectively demonstrating the value of your cybersecurity services through impact communication, ROI calculations, industry compliance, technology partnerships, client testimonials, demonstrations, and ongoing support, you can build trust and credibility with potential customers. This demonstrates the positive impact your services can have on their organization’s security and provides compelling reasons for them to choose your cybersecurity offerings.
Overcoming Objections and Closing the Sale
During the sales process, potential customers may raise objections or concerns about your cybersecurity services. Overcoming these objections and effectively closing the sale requires a strategic approach. Here are key strategies to address objections and successfully close the sale:
1. Active Listening: Listen attentively to the objections raised by potential customers. Allow them to fully express their concerns and clarify any ambiguities. Demonstrate empathy and understanding to build rapport and trust. Engage in active listening to show that you value their input and are genuinely interested in addressing their concerns.
2. Provide Clear and Detailed Explanations: Respond to objections with clear and detailed explanations of how your cybersecurity services address their specific concerns. Highlight the features and capabilities that directly mitigate the risks they have raised. Use plain language and avoid technical jargon to ensure easy understanding.
3. Showcase Proof and Evidence: Provide evidence to support your claims and alleviate potential customers’ doubts. This can include case studies, client testimonials, industry awards, certifications, or third-party assessments. Offering tangible proof of your service’s effectiveness reinforces potential customers’ confidence in your solutions.
4. Tailor the Solution: Customize your offering to address potential customers’ specific objections. It may involve modifying service deliverables, adjusting pricing, or adding extra support. Tailor your proposal to demonstrate that you have listened to their concerns and are committed to providing a solution that meets their unique needs.
5. Highlight Differentiators: Reinforce the unique value and advantages your cybersecurity services offer compared to competitors. Emphasize the unique features, expertise, or technology partnerships that set you apart. Articulate how these differentiators address potential customers’ objections and provide added value.
6. Offer Risk Mitigation: Address concerns related to potential risks or uncertainties by highlighting risk mitigation measures. This can include providing guarantees, service level agreements, or warranties. Demonstrating your commitment to addressing risks and ensuring a smooth implementation can build trust and alleviate objections.
7. Provide Implementation Support: Assure potential customers that you will provide comprehensive implementation support. Highlight the training, onboarding, and ongoing support that you will offer to facilitate a seamless transition. Addressing their objections related to implementation challenges can underscore your commitment to their success.
8. Create a Sense of Urgency: Encourage potential customers to take action by creating a sense of urgency. Communicate the importance of addressing their cybersecurity needs promptly, emphasizing the potential consequences of delaying or choosing a suboptimal solution. Offer limited-time promotions, discounts, or bonuses to incentivize them to make a decision and close the sale.
9. Ask for the Sale: After addressing objections and building a strong case for your cybersecurity services, it’s important to ask for the sale. Clearly articulate the next steps, provide a proposal or contract, and request their commitment. Confidence, assertiveness, and a clear call to action can help guide potential customers towards closing the sale.
The process of overcoming objections and closing the sale requires active listening, clear explanations, evidence, customization, risk mitigation, implementation support, creating a sense of urgency, and confidently asking for the sale. By effectively addressing concerns and demonstrating the value of your services, you can successfully close the sale and secure new clients for your cybersecurity offerings.
Implementing and Delivering Cybersecurity Services to Clients
Implementing and delivering cybersecurity services to clients involves a structured approach to ensure the effective deployment of your solutions and the successful protection of their digital assets. Here are key steps to consider when implementing and delivering cybersecurity services to clients:
1. Project Kick-off: Begin by conducting a project kick-off meeting with the client to establish clear communication channels, define project goals, and outline expectations. Align on project timelines, deliverables, and key milestones to ensure a smooth implementation process.
2. Customization and Configuration: Tailor your cybersecurity services to the specific needs of the client’s organization. Assess their IT infrastructure, data protection requirements, compliance needs, and security objectives. Configure your solutions accordingly, ensuring they seamlessly integrate with existing systems and align with the client’s unique environment.
3. Installation and Deployment: Once the solutions are configured, proceed with the installation and deployment process. Work closely with the client’s IT team to ensure a smooth transition and minimize disruptions to their operations. Provide clear instructions, documentation, and training to facilitate the implementation process.
4. Testing and Validation: Perform thorough testing and validation of the implemented cybersecurity solutions to ensure they operate effectively and meet the desired outcomes. Conduct penetration tests, vulnerability scans, or simulated attack scenarios to identify any vulnerabilities or weaknesses that need to be addressed.
5. Training and Education: Offer comprehensive training sessions to the client’s employees to ensure they understand the importance of cybersecurity and how to use the implemented solutions effectively. Educate them on best practices, security protocols, and how to identify and respond to potential threats. By empowering employees, you enhance the overall security posture of the client’s organization.
6. Ongoing Monitoring and Maintenance: Implement monitoring systems and establish proactive measures to continually monitor the client’s IT infrastructure and detect potential security breaches. Regularly update and patch the cybersecurity solutions to incorporate the latest threat intelligence and ensure optimal protection. Provide ongoing support and maintenance to promptly address any issues or concerns that may arise.
7. Incident Response and Remediation: Develop a robust incident response plan in collaboration with the client. Define roles, responsibilities, and procedures to follow in the event of a cybersecurity incident. Conduct regular drills and simulations to test the effectiveness of the incident response plan. In the event of an incident, respond promptly, mitigate the impact, and implement corrective measures to prevent future occurrences.
8. Client Engagement and Communication: Maintain regular communication and engagement with the client throughout the implementation process and beyond. Provide progress updates, share insights, and address any questions or concerns they may have. Foster a strong client relationship by being responsive, transparent, and proactive in your communication.
9. Performance Monitoring and Reporting: Track the performance of your cybersecurity solutions and regularly provide performance reports to the client. Highlight key metrics, demonstrate the effectiveness of the implemented solutions, and quantify the value delivered. Adapting reports to the client’s specific needs ensures they understand the impact of your services.
By following a systematic approach to implementing and delivering cybersecurity services, you can ensure that the client’s digital assets are effectively protected. By customizing the solutions, providing training and ongoing support, and maintaining clear communication, you establish a strong client relationship and position yourself as a trusted cybersecurity service provider.
Maintaining and Expanding Customer Relationships
Maintaining and expanding customer relationships is vital for the long-term success of your cybersecurity services. By nurturing existing client relationships and focusing on customer satisfaction, you can build trust, retain clients, and uncover opportunities for growth. Here are key strategies to maintain and expand customer relationships:
1. Regular Communication: Stay in regular contact with your clients to foster open lines of communication. Provide updates on industry trends, emerging threats, and new cybersecurity solutions. Share educational content, articles, or case studies that demonstrate your expertise and reinforce the value you bring.
2. Proactive Support: Be proactive in providing support and addressing any issues that arise. Establish clear channels for clients to reach out with questions or concerns and respond promptly. Anticipate their needs by offering proactive recommendations or updates based on the evolving cybersecurity landscape.
3. Ongoing Training and Education: Offer continued training and educational resources to keep your clients informed and up to date with the latest cybersecurity best practices. Conduct workshops, webinars, or knowledge-sharing sessions to help them strengthen their own security awareness and enhance their cybersecurity posture.
4. Performance Reviews and Reporting: Conduct periodic performance reviews to evaluate the effectiveness of your cybersecurity services. Provide comprehensive reports that highlight key metrics, demonstrate the value delivered, and identify areas for improvement. Collaborate with clients to develop action plans based on these insights for continuous enhancement.
5. Relationship Building Activities: Organize networking events, roundtable discussions, or industry conferences where your clients can connect with peers, share experiences, and gain further insights into the cybersecurity landscape. Building a community of clients fosters a sense of belonging and provides opportunities for cross-collaboration.
6. Upselling and Cross-Selling: Continually assess the evolving needs of your clients and identify potential upsell or cross-sell opportunities. As their trusted cybersecurity advisor, offer additional services or products that align with their evolving requirements. Educate them on the benefits of these expansions and the value they bring to their organization.
7. Client Feedback and Surveys: Regularly seek feedback from your clients to gauge satisfaction levels and identify areas for improvement. Conduct client satisfaction surveys to gather insights into their experiences and gather suggestions for enhancing your services. Actively listen to their feedback and use it to continuously refine and enhance your offerings.
8. Customer Appreciation and Loyalty Programs: Implement customer appreciation initiatives to recognize and reward the loyalty of your clients. This can include VIP access to new features or services, exclusive events, or loyalty discounts. By showing appreciation for their business, you foster a sense of loyalty and inspire them to continue partnering with you.
9. Proactive Account Management: Assign dedicated account managers to build relationships and provide personalized support to clients. These account managers serve as a single point of contact, ensuring that clients receive prompt attention and have a clear channel for escalating any concerns or requests.
By maintaining regular communication, providing proactive support, offering ongoing training, conducting performance reviews, and engaging in relationship-building activities, you can strengthen customer relationships. Through proactive account management, upselling, and cross-selling, you can uncover opportunities for growth and expand the scope of your cybersecurity services with existing clients.
Monitoring and Adapting to Changing Cybersecurity Threats and Trends
Monitoring and adapting to changing cybersecurity threats and trends is a critical aspect of providing effective cybersecurity services. The threat landscape is continually evolving, with new vulnerabilities, attack vectors, and tactics emerging regularly. Remaining vigilant and proactive in monitoring these developments allows you to stay one step ahead and offer optimal protection to your clients. Here are key strategies to monitor and adapt to changing cybersecurity threats and trends:
1. Continuous Threat Monitoring: Implement robust threat monitoring systems that continually track and analyze potential threats. Leverage threat intelligence feeds, security information and event management (SIEM) tools, and security analytics to detect evolving threats and vulnerabilities. Stay up to date with the latest trends in hacking techniques, malware, and social engineering tactics.
2. Security Information Sharing: Engage in information sharing initiatives with trusted peers, industry consortiums, and government agencies. Participate in threat intelligence communities and forums where cybersecurity professionals exchange insights and discuss emerging threats. Sharing knowledge and collaborating with the wider security community can provide valuable early warnings and mitigation strategies.
3. Continuous Education and Training: Invest in ongoing education and training for yourself and your team. Encourage professional development by attending cybersecurity conferences, industry webinars, and specialized training programs. Stay updated with the latest certifications and industry best practices to enhance your capabilities in detecting, preventing, and responding to evolving threats.
4. Advanced Analytics and Machine Learning: Leverage advanced analytics and machine learning capabilities to analyze large volumes of security data. Use these technologies to identify patterns, detect anomalies, and automate threat detection processes. By harnessing these powerful tools, you can improve the efficiency and effectiveness of your threat monitoring and response mechanisms.
5. Regular Security Assessments: Conduct regular security assessments and audits for your clients to identify vulnerabilities and gaps in their security posture. This includes penetration testing, vulnerability assessments, and compliance audits. Regular assessments help you identify evolving risks and recommend appropriate countermeasures to mitigate them.
6. Incident Response and Forensics: Develop a robust incident response plan that outlines the steps to follow in the event of a security incident. Establish procedures for investigation, containment, recovery, and communication. Regularly review and update your incident response plan to account for new threats and ensure alignment with evolving best practices.
7. Security Automation and Orchestration: Adopt security automation and orchestration tools to streamline your security operations. Automate routine tasks, such as security event correlation or patch management, to free up valuable time for proactive threat monitoring and mitigation. By automating repetitive processes, you can respond more rapidly to emerging threats and allocate resources effectively.
8. Collaboration with Technology Partners: Foster strong relationships with technology partners, such as software vendors or threat intelligence providers. Stay informed about the latest product updates, security patches, and emerging threat indicators. Collaborate with your partners to enhance your cybersecurity services and leverage their expertise and insights.
9. Regular Client Communication: Maintain regular communication with your clients to keep them informed about evolving cybersecurity threats and trends. Provide regular updates and recommendations on improving their security posture based on the latest industry insights. Being proactive with client communication builds trust and demonstrates your commitment to their ongoing protection.
Monitoring and adapting to changing cybersecurity threats and trends requires a proactive and continuous effort. By leveraging advanced technologies, engaging in information sharing, conducting regular security assessments, and maintaining open communication with clients, you can enhance your cybersecurity services and better protect your clients from emerging threats.
Conclusion
Selling cybersecurity services requires a strategic approach that encompasses understanding market demand, assessing your expertise, building a comprehensive service offering, identifying potential customers, creating a compelling value proposition, pricing effectively, developing a marketing and sales strategy, approaching and engaging potential customers, demonstrating the value of your services, overcoming objections, and closing the sale. Once the sale is closed, implementing and delivering the cybersecurity services to clients is crucial in ensuring their digital assets are protected.
Maintaining and expanding customer relationships is essential for long-term success, and this involves continuous communication, proactive support, ongoing training, performance monitoring, and relationship-building activities. Furthermore, staying agile in the ever-evolving cybersecurity landscape is paramount. This means monitoring changing threats and trends, leveraging advanced analytics and automation, collaborating with technology partners, and regularly communicating with clients about emerging risks.
By following these key steps and strategies, you can position yourself as a trusted and reliable cybersecurity service provider. Remember to continuously adapt and refine your approaches based on market feedback, emerging technologies, and evolving client needs. With a strong foundation, dedication to ongoing improvement, and a commitment to delivering exceptional cybersecurity services, you can thrive in this dynamic industry and protect businesses from the constantly evolving threats of the digital world.