Introduction
Welcome to this comprehensive guide on how to make your own proxy server for Spire. If you’re a Spire user looking to enhance your browsing experience or access blocked websites, a proxy server can be a valuable tool. In this article, we will delve into the world of proxy servers, why you need one for Spire, and provide a step-by-step guide on setting up your own proxy server.
A proxy server acts as an intermediary between your device and the internet. When you send a request to access a website or online service, the request first goes through the proxy server. The server then forwards the request to the destination server and retrieves the response. This process helps protect your privacy, increase security, and bypass certain restrictions.
If you use Spire, a proxy server can be extremely useful when it comes to accessing geo-restricted content, maintaining anonymity, or speeding up your browsing experience. By setting up your own proxy server, you have full control over its configuration and can ensure the reliability and security of your connection.
Now, without further ado, let’s dive into the step-by-step guide to setting up your own proxy server for Spire. But before we begin, let’s gather all the necessary materials and tools to make the process smoother.
What is a proxy server?
A proxy server is a server that acts as an intermediary between your device and the internet. It allows you to make requests to websites or online services through the server, rather than directly from your device. When you send a request, it is first intercepted by the proxy server, which then forwards it to the destination server on your behalf. The response from the destination server is then sent back to the proxy server, which in turn sends it back to your device.
The primary function of a proxy server is to serve as a gateway between your device and the internet. It can provide several benefits, such as enhancing security, protecting your privacy, and allowing access to restricted websites or content. By using a proxy server, your IP address is masked, making it difficult for websites or services to track your online activities. This can be particularly useful if you want to browse anonymously or bypass regional restrictions.
Proxy servers also offer caching capabilities, which can significantly improve your browsing experience. When you request a webpage or any online content through a proxy server, it caches the response. The next time you request the same content, instead of fetching it from the original server, the proxy server retrieves it from its cache, resulting in faster load times.
Additionally, proxy servers can provide content filtering and traffic management. Administrators can use proxy servers to restrict access to certain websites or types of content, ensuring that users comply with company policies or age restrictions. They can also prioritize or limit bandwidth for specific users or applications, optimizing network traffic and improving overall performance.
In summary, a proxy server acts as an intermediary between your device and the internet, providing benefits such as enhanced security, privacy protection, faster browsing, and content filtering. In the next section, we will explore why you need a proxy server specifically for Spire.
Why do you need a proxy server for Spire?
If you’re a Spire user, you may already be aware of its powerful browsing capabilities. However, there are specific scenarios where a proxy server can greatly enhance your experience with Spire.
One of the key reasons you may need a proxy server for Spire is to bypass geographical restrictions. Many online services, streaming platforms, and websites limit access to certain regions due to licensing or copyright agreements. With a proxy server, you can route your connection through a server in a different location, making it appear as if you’re accessing the internet from that location. This allows you to access geo-restricted content and enjoy streaming services, websites, or online gaming that may not be available in your country.
Another important benefit of using a proxy server with Spire is increased privacy and anonymity. By routing your internet traffic through a proxy server, your original IP address is masked. This prevents websites, advertisers, or other entities from tracking your online activities. It provides an added layer of privacy and can protect your personal information from being exploited.
Furthermore, a proxy server can help improve the performance of Spire. By caching frequently accessed content, it reduces the load on the Spire servers and can significantly speed up your browsing experience. The proxy server can store and serve static elements of a webpage, resulting in faster load times and smoother navigation.
Additionally, if you are using Spire in a corporate or educational environment, a proxy server can be crucial in enforcing content filtering and security measures. Administrators can configure the proxy server to block access to certain websites or types of content, ensuring compliance with company policies or protecting users from potentially harmful or inappropriate content.
In summary, a proxy server for Spire can help you bypass geo-restrictions, enhance your privacy and anonymity, improve browsing performance, and enforce content filtering and security measures. Now that you understand the benefits, let’s move on to the step-by-step guide on how to set up your own proxy server for Spire.
Step-by-step guide to setting up your own proxy server for Spire
Now that you understand the benefits of having a proxy server for Spire, let’s explore the step-by-step process of setting up your own proxy server. Follow these instructions carefully to ensure a successful setup:
- Choose your server: Start by selecting a server to host your proxy service. You can choose a cloud-based server or set up a physical server depending on your requirements and technical expertise.
- Install Squid proxy server: Squid is a widely used and powerful open-source proxy server. Install Squid on your chosen server by following the appropriate installation guide for your operating system.
- Configure Squid proxy server: After installing Squid, you’ll need to configure its settings. This includes defining the allowed IP addresses, port numbers, and access control rules. Consult the Squid documentation for detailed instructions on configuring the server.
- Secure your proxy server: It’s important to secure your proxy server to protect it from unauthorized access and potential abuse. Implement measures such as setting up strong authentication methods, enabling SSL/TLS encryption, and monitoring access logs for any suspicious activity.
- Test your proxy server: Once you have configured and secured your proxy server, it’s time to test its functionality. Ensure that you can connect to the internet through the proxy server and verify that your IP address is masked when accessing websites or services.
- Troubleshoot common issues: In case you encounter any issues during the setup or configuration process, consult the documentation of your proxy server software or seek assistance from online forums or support communities.
By following these steps, you can successfully set up your own proxy server for Spire. Remember to regularly update and maintain your server to ensure optimal performance and security. Now that you have the necessary information, gather the required materials and tools and begin the process of creating your own proxy server.
Required materials and tools
Before embarking on setting up your own proxy server for Spire, make sure you have the following materials and tools ready:
- A server: You’ll need a server to host your proxy server. This can be a cloud-based server or a physical machine running a compatible operating system.
- Operating system: Ensure that your chosen server has a supported operating system, such as Linux, Windows, or macOS.
- Squid proxy server software: Download and install the Squid proxy server software, as it is a reliable and widely-used open-source option for setting up a proxy server.
- Root access or administrative privileges: Depending on the server configuration, you may require root access or administrative privileges to install and configure the necessary software.
- Network connectivity: Ensure that your server has a stable internet connection with appropriate bandwidth to handle the proxy server’s traffic.
- Port forwarding (if needed): If you intend to access the proxy server from outside your local network, you may need to set up port forwarding on your router to redirect incoming connections to the server.
- Firewall settings: Configure your server’s firewall to allow necessary inbound and outbound connections for the proxy server to function properly.
- TLS/SSL certificate (optional): If you want to secure your proxy server connections with SSL/TLS encryption, you will need to obtain and configure a valid SSL/TLS certificate.
- Documentation and online resources: Keep handy the relevant documentation and online resources for the server operating system, Squid proxy server, and any additional tools you may need during the setup process.
Having these materials and tools ready before starting the setup process will ensure a smoother experience and help you quickly progress through each step. Once you have everything in place, you’re ready to move on to the installation and configuration of the Squid proxy server.
Installing Squid Proxy Server
Now that you have gathered the necessary materials and tools, it’s time to install the Squid proxy server on your chosen server. Follow the steps below:
- Linux: If you are using a Linux server, open a terminal or SSH into your server.
- Package Manager: Use the appropriate package manager for your Linux distribution to install Squid. For example, on Ubuntu, you can use the command
sudo apt-get install squid. - Windows: If you are using a Windows server, download the Squid installer from the official Squid website.
- Installation Wizard: Run the Squid installer on your Windows server and follow the on-screen instructions to complete the installation.
- Configuration Files: Regardless of the operating system, Squid’s configuration files are typically located in the
/etc/squid/directory on Linux. On Windows, you can find them in the Squid installation directory. - Edit Configuration: Open the Squid configuration file,
squid.conf, using your preferred text editor. - Customize Configuration: Customize the configuration according to your needs. You can specify the proxy listening port, access control rules, cache settings, and other parameters. Refer to the Squid documentation for more information on configuring the proxy server.
- Save Changes: Save the changes you made to the configuration file and exit the text editor.
- Start Squid: Finally, start the Squid service using the appropriate command for your operating system. For example, on Linux, run
sudo systemctl start squidto start the Squid service. - Verify Installation: Verify that Squid is running by checking its status. On Linux, you can use the command
sudo systemctl status squid.
By following these steps, you should have successfully installed Squid proxy server on your server. The next step involves configuring Squid to ensure it meets your specific requirements. Continue reading to learn how to configure Squid for your proxy server setup.
Configuring Squid Proxy Server
Now that you have successfully installed the Squid proxy server, it’s time to configure it to meet your specific needs. Follow the steps below to customize your Squid proxy server settings:
- Edit configuration file: Open the Squid configuration file, typically located at
/etc/squid/squid.confon Linux or in the Squid installation directory on Windows. Use your preferred text editor to make changes. - Define listening port: Specify the port on which Squid will listen for incoming connections. Look for the
http_portdirective in the configuration file and update it accordingly. For example, you can set the port to3128. - Configure ACLs: Access Control Lists (ACLs) allow you to define rules for controlling access to your proxy server. Use the Squid configuration file to create ACLs for specific IP addresses, networks, or domains. You can set permissions to allow or deny access based on these ACLs.
- Enable caching: Squid has powerful caching capabilities that can improve browsing speed. Adjust the cache configuration settings in the Squid configuration file to determine the cache size, storage location, and expiration rules for cached content.
- Enable authentication (optional): If you want to secure your proxy server, you can enable authentication. Squid supports various authentication methods such as Basic, Digest, and NTLM. Choose the method that suits your requirements and configure the authentication settings in the Squid configuration file.
- Configure SSL/TLS (optional): If you want to secure the connections to your proxy server with SSL/TLS encryption, you will need to obtain an SSL/TLS certificate and configure Squid to use it. Refer to the Squid documentation for detailed instructions on configuring SSL/TLS.
- Save changes: After making the necessary configuration changes, save the Squid configuration file and exit the text editor.
Once you have configured Squid proxy server according to your requirements, you can start the server and begin using your own proxy server for Spire. Bear in mind that Squid offers a vast array of configuration options, so explore the documentation to fully understand the available settings and further customize your proxy server if desired.
Securing Your Proxy Server
Securing your proxy server is crucial to protect it from unauthorized access and potential misuse. Follow these steps to enhance the security of your proxy server:
- Enable access control: Utilize access control lists (ACLs) to restrict access to your proxy server. Define rules that allow only trusted IP addresses or networks to connect to the server, preventing unauthorized access.
- Implement authentication: Enable authentication to ensure only authenticated users can use the proxy server. Configure usernames and passwords for authorized users, and choose an authentication method supported by Squid, such as Basic, Digest, or NTLM.
- Set up SSL/TLS encryption: If you plan to use your proxy server over the internet or for sensitive data transmission, secure the connections with SSL/TLS encryption. Acquire an SSL/TLS certificate, configure Squid to use it, and enforce secure connections.
- Monitor and analyze logs: Enable logging and regularly review the access logs to identify potential security threats or unauthorized activities. Configure Squid to log any suspicious activity or excessive usage that may indicate abuse.
- Regularly update Squid: Stay up to date with the latest version of Squid and update it promptly when new security patches or updates are released. Regularly check for updates to address any potential vulnerabilities.
- Configure firewall rules: Utilize firewall rules to limit incoming connections to only those required for the proper functioning of your proxy server. Block unnecessary ports or protocols to reduce the attack surface.
- Apply strong password policy: Enforce a strong password policy for user authentication. Require users to choose strong and unique passwords, and regularly remind them to change their passwords to maintain account security.
- Limit resource usage: Configure Squid to limit the amount of resources allocated to each client connection. This prevents excessive usage or abuse that could impact server performance and stability.
- Regularly perform security audits: Conduct periodic security audits to identify any vulnerabilities or weaknesses in your proxy server setup. Perform penetration testing or involve a security professional to assess the overall security of your proxy server.
By implementing these security measures, you can significantly enhance the security of your proxy server, protecting it from unauthorized access and potential security threats. Remember to regularly monitor and update the security settings to ensure ongoing protection.
Testing Your Proxy Server
After setting up and securing your proxy server, it’s important to perform testing to ensure its functionality and verify that it meets your requirements. Follow these steps to test your proxy server:
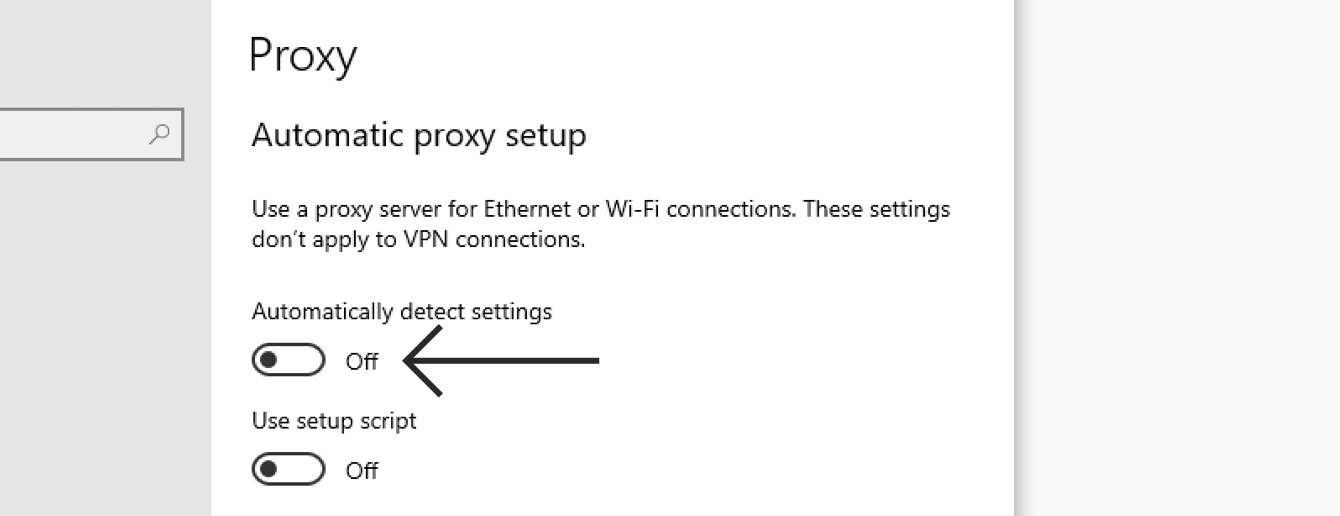
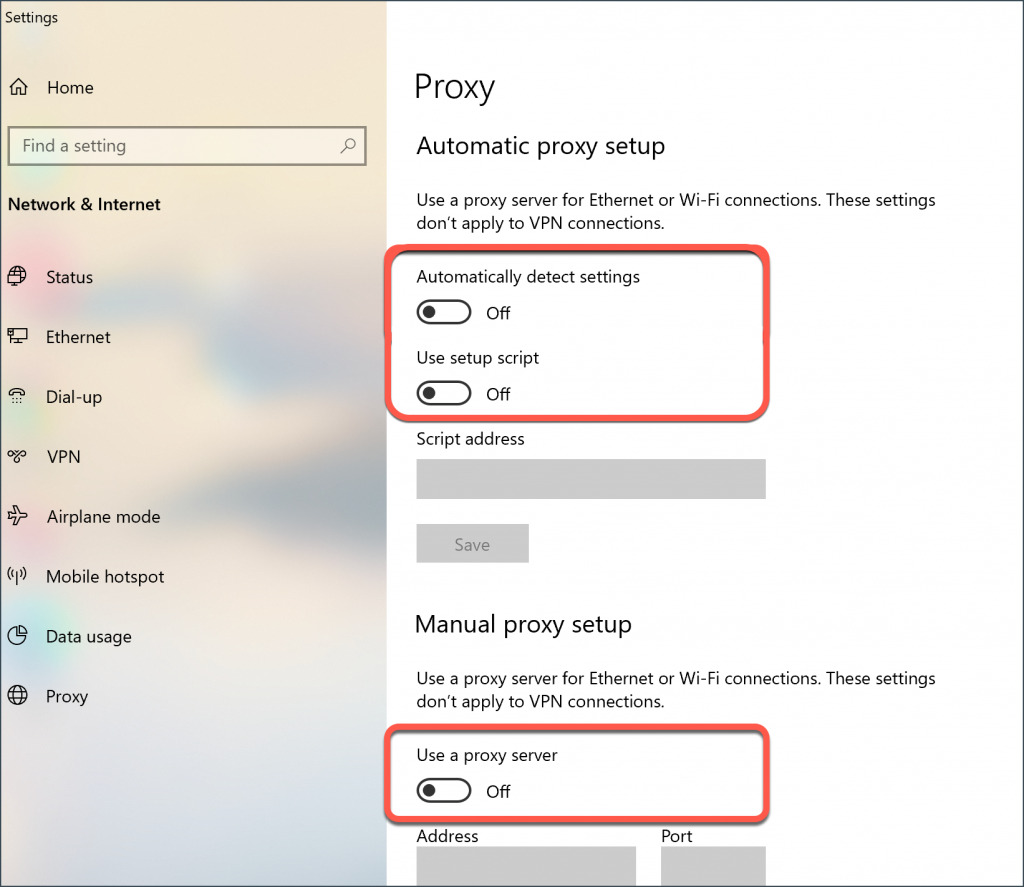
- Connect to the proxy server: Configure your device or browser to connect to the proxy server. Enter the IP address or hostname of the server and the port number you specified during the setup process.
- Verify anonymity: Visit a website that displays your IP address and check if it shows the IP address of the proxy server instead of your original IP address. This confirms that the proxy server is successfully hiding your identity.
- Test geo-restriction bypass: Access a website or service that is geographically restricted. If you are able to access the content without any issues, it indicates that your proxy server is successfully bypassing geo-restrictions.
- Check caching: Visit multiple websites and observe the page load times. If subsequent visits to the same website show faster load times, it confirms that the proxy server is caching content and improving browsing performance.
- Test access control: Attempt to access a website or service that is blocked by the access control rules set up in your proxy server. If you are unable to access the blocked content, it means that the access control measures are working as intended.
- Verify SSL/TLS encryption: If you have configured SSL/TLS encryption, visit a website that uses HTTPS. Verify that your browser shows a secure connection and the padlock icon in the address bar, indicating that the communication is encrypted.
- Monitor logs: Review the logs generated by the proxy server to identify any suspicious activity or errors. Look for any unusual access patterns or excessive usage that may indicate a security concern or misconfiguration.
- Test on multiple devices: Test the proxy server on multiple devices and operating systems to ensure compatibility and consistent performance across different platforms.
- Perform load testing: Simulate heavy traffic by accessing the proxy server with multiple simultaneous connections. Observe if the server can handle the load without significant degradation in performance.
- Verify DNS resolution: Test if the proxy server correctly resolves domain names to IP addresses. Visit websites using their domain names and ensure they load properly.
By conducting thorough testing, you can identify and resolve any issues or configuration errors, ensuring that your proxy server functions as intended. Regular testing and monitoring will help you maintain optimal performance and security throughout the lifetime of your proxy server.
Troubleshooting Common Issues
While setting up and maintaining a proxy server for Spire, you may encounter some common issues. Understanding these issues and how to troubleshoot them can help ensure smooth operation of your proxy server. Here are some common problems and their possible solutions:
- Connection Issues: If you are unable to connect to your proxy server, ensure that the server is running and that the correct port number is specified in your device or browser settings. Check your firewall settings to ensure that the necessary ports are open for communication.
- Authentication Problems: If you have enabled authentication on your proxy server and are experiencing issues logging in, double-check that you are entering the correct username and password combination. Ensure that the authentication method is supported and configured correctly in the Squid configuration file.
- Proxy Server Load: If your proxy server is experiencing high traffic or performance issues, consider optimizing the server by increasing its resources such as CPU, RAM, or bandwidth. You may also need to fine-tune Squid’s caching and resource allocation settings to ensure efficient utilization.
- SSL/TLS Certificate Issues: If you encounter SSL/TLS certificate errors, confirm that you have correctly configured the SSL/TLS certificate in the Squid configuration file. Ensure that the certificate is valid and trusted by the connecting devices. Resolve any issues with certificate installation or chain validation.
- Access Control Problems: If your access control rules are not functioning as expected, review the configuration in the Squid configuration file. Double-check the order of the access control rules and verify that they are correctly defined to allow or deny specific IP addresses or networks.
- Cache Refresh Problems: If you notice that the cached content is not being updated, check the cache settings in the Squid configuration file. Ensure that the expiration rules are appropriately set to refresh the cache at regular intervals or when the content changes.
- Logging and Monitoring: If you have difficulties monitoring or analyzing the logs generated by the proxy server, ensure that the logging directives are properly configured in the Squid configuration file. Verify the log file path and permissions, and consider using log analysis tools to aid in troubleshooting.
- Performance Optimization: If you experience slow performance or latency issues, evaluate your proxy server’s hardware resources and network connectivity. Consider upgrading or optimizing your server’s resources, such as increasing RAM, optimizing disk I/O, or improving network bandwidth.
- Compatibility Problems: If you encounter compatibility issues with certain websites or services, check if the proxy server is configured to handle the specific protocols or technologies required by those websites or services. Consider adjusting the proxy server configuration to cater to these requirements.
- Updates and Upgrades: If you encounter issues after updating or upgrading Squid or any associated software, check the release notes and documentation for any changes or deprecations that may impact your proxy server’s configuration. Adjust your configuration accordingly to ensure compatibility.
By troubleshooting and resolving these common issues, you can maintain the smooth functioning of your proxy server and ensure a seamless experience while using Spire.
Conclusion
Congratulations! You have now learned how to set up your own proxy server for Spire. Having your own proxy server can provide numerous benefits, including bypassing geo-restrictions, enhancing privacy and anonymity, improving browsing performance, and enforcing access control measures. By following the step-by-step guide in this article, you should now have a functional and secure proxy server that can enhance your Spire experience.
Remember to regularly monitor, maintain, and update your proxy server to ensure optimal performance and security. Stay informed about the latest security best practices and apply them to your proxy server setup. Keep an eye on any updates or patches for the Squid proxy server software and promptly implement them to address potential vulnerabilities.
Now that you have a solid understanding of proxy servers, their functionality, and the process of setting up your own server, you can explore and experiment with different configurations to further customize and optimize your proxy server according to your specific needs.
Enjoy the benefits of your self-hosted proxy server for Spire and take full advantage of its capabilities to access geo-restricted content, maintain privacy, and optimize your browsing experience. Happy proxying!