The current crop of cyber attackers is unrelenting, focusing on both the quality and quantity of their attacks. The threats posed, as a result, have been considerable, with a report establishing that 86% of companies have already experienced phishing attacks, 50% have experienced ransomware attacks, and 48% experienced information-stealing malware in 2022. These statistics point to the need for organizations to secure their local networks and servers using a selection of proven technologies, including proxy servers and firewalls.
What Is a Proxy Server?
A proxy server is any hardware-based or software-based solution that serves as an intermediary between a user’s computer or local (private) network and the internet (web servers). It intercepts all internet traffic – both outgoing HTTP/HTTPS requests and incoming server responses. In addition, the proxy anonymizes the requests by hiding their real IP address(es) and assigning new IP addresses. In this way, proxy servers generally promote user privacy. Certainly, an advantage for individuals and companies since a report made it clear that threats can affect anyone.
Security-Enhancing Proxy Servers
There are several proxy types, some of which not only enhance privacy but also boost security. For instance, transparent proxies block access to specific websites as well as direct access to particular web pages based on specific preset rules. In addition, transparent proxies can prevent phishing attacks by allowing connections to only a preauthorized list of websites.
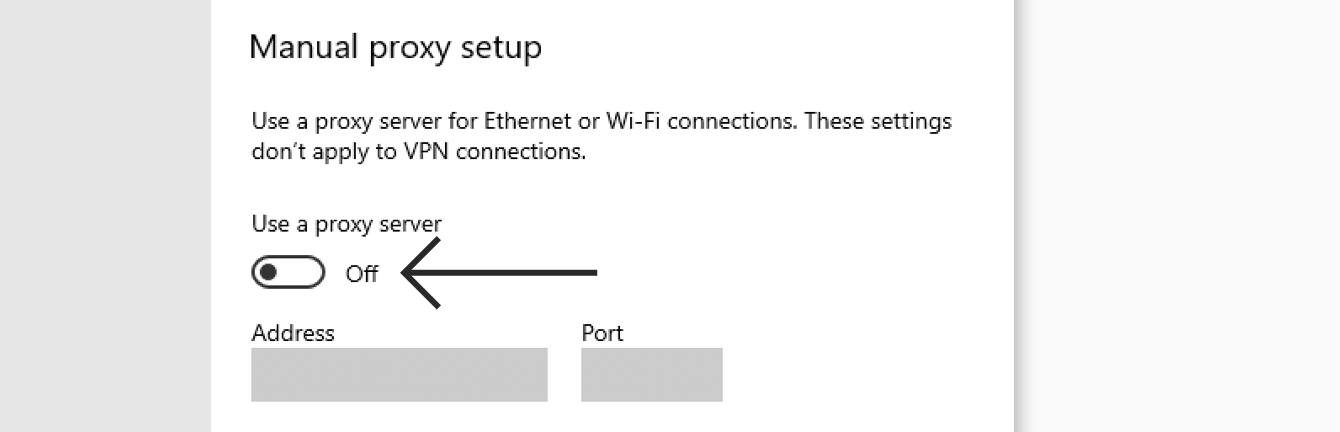
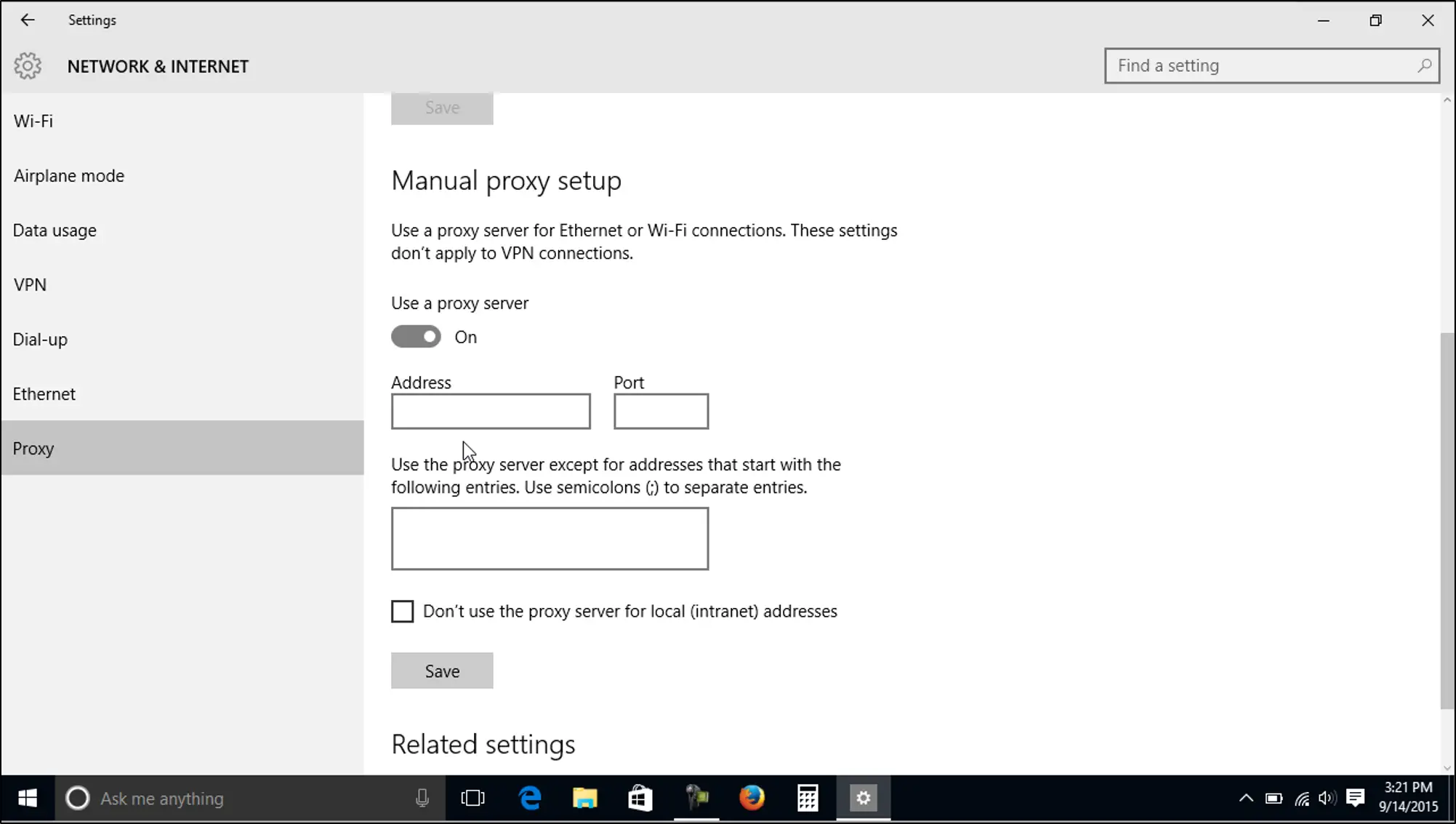
When it comes to enhancing security, no other proxy type comes close to what the HTTP proxy can achieve. What is an HTTP proxy? You may ask. This proxy can be created on your computer or web server by simply changing a few settings. Once configured, the HTTP proxy acts as a high-performance content filter that protects the server or computer. One of the industry-leading companies wrote a blog post about HTTP proxies, make sure to check it out.
A client-side HTTP (also known as HTTP-client) proxy filters the incoming responses, detecting and blocking/deleting phishing links sent via email, for example. Similarly, server-side HTTP (also known as HTTP-server) proxies filter incoming HTTP requests and block malicious ones. Additionally, they cache frequently accessed files. HTTP-server proxies are also useful for load balancing purposes, safeguarding your web server from malicious attacks such as Distributed Denial of Service (DDoS) attempts.
What Is a Firewall?
A firewall is a network security element that forms the network boundary between the intranet and the internet. It monitors all outgoing and incoming traffic, blocking or allowing access based on predefined security-oriented rules. A firewall can be software, hardware, software-as-a-service (SaaS), or cloud-based.
Like proxies, there are several types of firewalls, including:
- Proxy firewalls: they are essentially proxy servers)
- Stateful inspection firewalls or traditional firewalls: they block or allow traffic based on state, port, or protocol and monitor traffic throughout a connection
- Unified threat management (UTM) firewalls: they combine the functionality of stateful inspection firewalls with antivirus and intrusion prevention tools
- Next-generation firewalls (NGFW): Filter packets and URLs based on reputation and geolocation, undertake stateful inspection, and block advanced malware, application-layer attacks, and risky applications
- Threat-focused next-generation firewalls: they include all the capabilities of NGFWs and offer advanced threat and risk detection and remediation (the process of reversing or stopping damage)
- Virtual firewalls: they are deployed in the cloud to secure traffic between virtual and physical networks
- Cloud-native firewalls: they are designed for scale to secure networks and workload infrastructure at scale
Proxy Servers vs. Firewalls: Similarities and Differences
Indeed, proxy servers and firewalls can boost the security of a private network. But how similar or different are they?
Similarities Between Proxy Servers And Firewalls
- They can be either hardware or software-based
- Proxies and firewalls enhance security
- Some proxies, such as data center proxies, exist virtually – in the cloud – in the same way, virtual firewalls exist in the cloud
- Monitors and filters incoming as well as outgoing internet traffic to and from a network
- For proxy servers, this function is performed by transparent and HTTP proxies only
- Proxy servers and firewalls can exist at various layers of the OSI model – proxies work on the transport layer (layer 4) or higher, while firewalls can work on layers 7, 5, 4, 3, and 2
Differences Between Proxy Servers and Firewalls
| Proxy Servers | Firewalls |
| They can be used as firewalls, e.g., proxy firewalls | They cannot be used as proxies |
| Proxy servers –need configuration to work | Modern computers come with built-in firewalls meaning no configuration is required for them to work |
| They hide the real IP address | They do not hide the real IP address |
| Proxies are installable on either a private or public network | Firewalls are interfaces between private and public networks |
| Some proxies, such as SOCKS proxies, help are used to bypass firewalls and therefore forego restrictions | All firewalls are designed to protect an internal network from malicious attacks – they institute restrictions |
Final Thoughts
Proxies and firewalls differ in several ways. For instance, proxies need configuration to work, while firewalls do not. Especially those that come with modern computers. Additionally, proxies mask IP addresses, whereas firewalls do not. Nonetheless, proxy servers and firewalls are similar in multiple ways, including that they both help enhance security.