Introduction
Welcome to the world of P2P! P2P, which stands for Peer-to-Peer, is a revolutionary technology that has transformed the way we share and distribute files online. It has become an integral part of our digital lives, playing a pivotal role in various industries and applications.
P2P technology allows users to share resources directly with each other, without the need for a central server. This decentralized approach enables faster and more efficient file sharing, as well as greater scalability and resilience. P2P has revolutionized the way we access and distribute media, such as music, videos, and software.
So, what exactly does P2P stand for? P2P, as mentioned earlier, refers to Peer-to-Peer. In a P2P network, every device (or peer) connected to the network can act as both a client and a server, meaning it can both request and provide resources to other devices. This self-sufficiency and collaborative nature of P2P networks make them highly efficient and flexible.
With the rise of P2P technology, the way we consume and distribute media has transformed. Gone are the days of relying solely on centralized servers for file sharing. P2P networks have taken the internet by storm, allowing users to directly and seamlessly interact with each other’s devices, fostering a greater sense of community and connectivity.
In this article, we will delve into the world of P2P networks, exploring their workings, history, types, advantages, disadvantages, common applications, and security risks. By the end of this article, you will have a comprehensive understanding of P2P technology and its impact on our digital landscape.
Definition of P2P
P2P, or Peer-to-Peer, is a networking model that allows devices to communicate and share resources directly with each other without the need for a centralized server. In a P2P network, each device functions as both a client and a server, enabling it to both request and provide resources to other devices connected to the network.
The concept of P2P is based on the principle of decentralization, where the traditional client-server model is replaced with a distributed network of interconnected peers. Unlike in a client-server model, which relies on a central server to facilitate communication and resource sharing, P2P networks rely on the collective power and capabilities of all devices within the network.
One of the key features of P2P networks is their ability to handle high traffic loads and distribute resources efficiently. Since each device in the network can contribute to sharing files and resources, the workload is distributed across multiple devices, resulting in improved performance and scalability.
P2P networks are commonly associated with file sharing protocols, where users can exchange files directly with one another, without relying on a central server. This has revolutionized the distribution of media, such as music, videos, and software, as it allows users to obtain files from multiple sources simultaneously, boosting download speeds and availability.
Moreover, P2P technology has expanded beyond file sharing and is now seen in various other applications, such as peer-to-peer lending, decentralized cryptocurrency networks, and collaborative computing.
Overall, the fundamental principle behind P2P is the direct communication and resource sharing between devices without the need for intermediaries. This decentralized approach has transformed the way we interact and collaborate in the digital world, enabling us to harness the power of collective resources and connectivity.
How P2P Works
Understanding how P2P works is essential to grasp the underlying mechanisms that facilitate direct communication and resource sharing in a decentralized network. Here’s a breakdown of the key components and steps involved in the operation of a P2P network:
- Discovery: In order for devices to connect and communicate with each other in a P2P network, they need to discover and identify one another. There are several methods used for peer discovery, including centralized trackers, distributed hash tables (DHTs), and multicast protocols. These methods allow devices to locate and establish connections with other peers in the network.
- Connection Establishment: Once devices have discovered each other, they need to establish a direct connection to facilitate communication. This is usually done through the use of socket-based protocols, where devices create a connection over the internet using IP addresses and port numbers. The devices then negotiate protocols and establish the necessary communication channels.
- Resource Indexing: In a P2P network, each device maintains an index of the resources it possesses and is willing to share. This index can include files, services, or any other form of resource that the device wants to make available to other peers. The index can be stored locally or distributed across multiple peers using DHTs or other indexing mechanisms.
- Data Transfer: Once a connection is established and resources are indexed, devices in a P2P network can begin transferring data. This data transfer can occur in various ways, depending on the specific protocol being used. Some P2P protocols implement a tit-for-tat strategy, where devices exchange data in a reciprocal manner, while others utilize distributed algorithms to distribute data efficiently among the peers.
- Dynamic Network: One of the defining characteristics of a P2P network is its dynamic nature. Peers can join or leave the network at any time, without compromising the overall functionality. When a new peer joins the network, it can discover and connect to existing peers, allowing for seamless integration. Similarly, when a peer leaves the network, other peers can adjust their connections and resource distribution accordingly.
By leveraging these components and steps, P2P networks enable devices to communicate directly with each other, exchange resources, and collaborate without relying on a central server. This decentralized approach empowers users with greater control, improved performance, and enhanced connectivity in the digital realm.
History of P2P
The history of P2P dates back to the early days of computer networking, with the concept originating from the desire to create a decentralized network where resources can be shared directly between peers. Here is a glimpse into the evolution of P2P technology:
1. The Birth of P2P: The concept of P2P can be traced back to the 1970s when researchers began exploring the idea of distributed systems. However, it wasn’t until the late 1990s and early 2000s that P2P gained widespread attention and popularity.
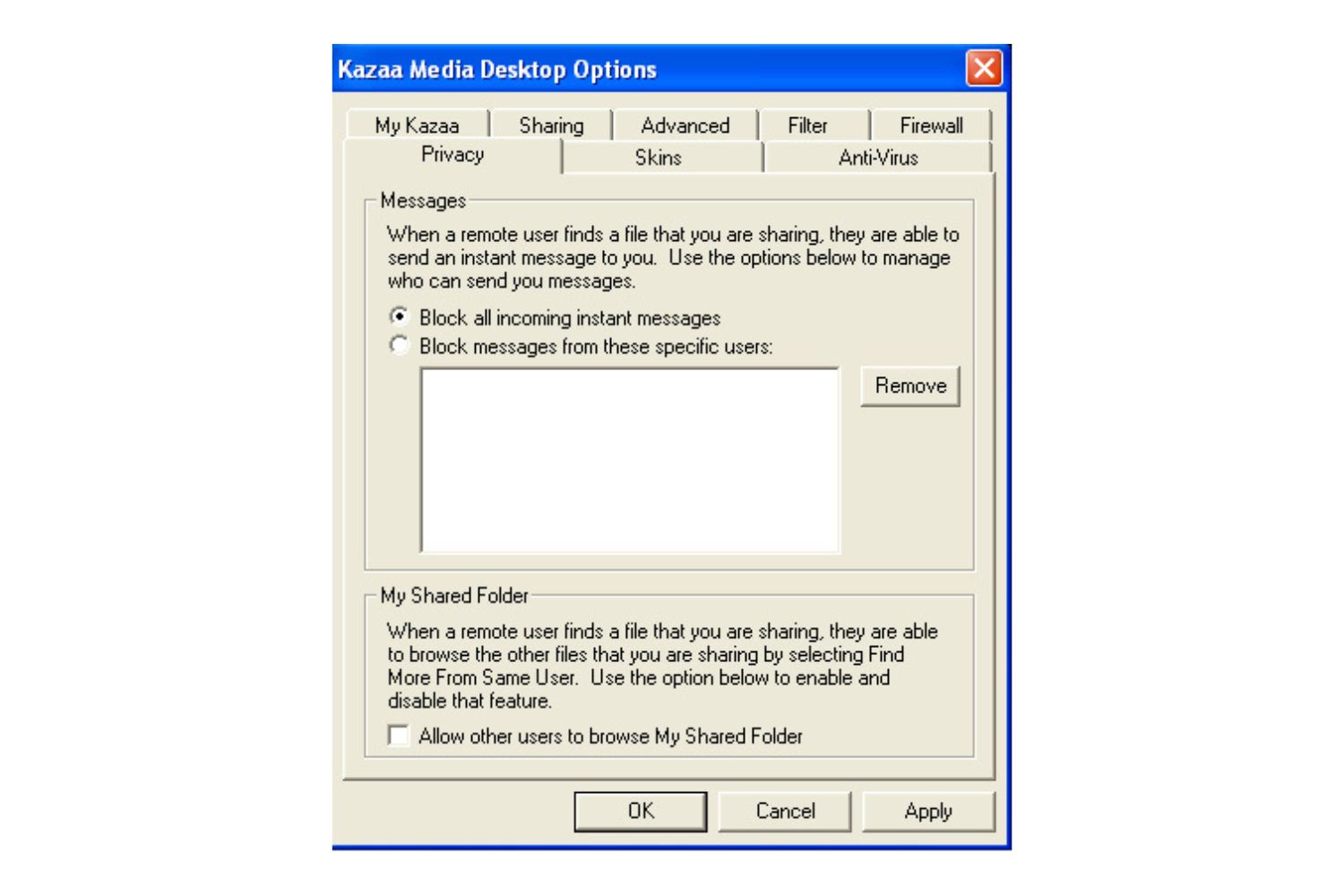
2. Napster: One of the pioneers of P2P technology was Napster, launched in 1999 by Shawn Fanning. Napster introduced the concept of file sharing through centralized servers, where users could search for and download music files from other users. The centralized architecture drew significant attention, but it also faced legal challenges due to copyright infringement concerns.
3. Decentralization with Gnutella: Following the downfall of Napster, decentralized P2P networks began to emerge. In 2000, Gnutella, a decentralized file-sharing protocol, was released. Gnutella allowed users to connect directly with each other, bypassing the need for a central server. This marked a shift towards true P2P networks and sparked the development of other decentralized protocols.
4. BitTorrent: The release of BitTorrent in 2001 by Bram Cohen revolutionized P2P file sharing. BitTorrent introduced a new protocol that utilized a “swarm” approach, where users transferred files in small pieces from multiple sources simultaneously. This significantly improved download speeds and reduced the strain on individual peers, making BitTorrent one of the most popular P2P protocols to date.
5. Blockchain and Cryptocurrencies: P2P technology also played a crucial role in the development of blockchain and cryptocurrencies. Bitcoin, the first decentralized digital currency, utilizes P2P networks to enable secure and transparent transactions without the need for intermediaries.
Since then, P2P technology has continued to evolve and expand into various domains, including peer-to-peer lending, video streaming, messaging applications, and more. The decentralized nature of P2P networks has empowered individuals to share and collaborate on a global scale, challenging traditional centralized systems and fostering a more open and interconnected digital ecosystem.
Types of P2P Networks
P2P networks come in various forms, each with its own characteristics and applications. Here are some of the commonly recognized types of P2P networks:
- Centralized P2P: In centralized P2P networks, a central server or a set of servers act as intermediaries to facilitate connections between peers. The server keeps track of the available peers and coordinates the resource sharing process. Examples of centralized P2P networks include early versions of Napster.
- Decentralized P2P: Decentralized P2P networks, such as Gnutella and eDonkey2000, allow direct communication between peers without relying on a central server. Peers discover and connect to each other through various mechanisms, such as distributed hash tables (DHTs) or peer exchange protocols. These networks offer greater resilience and independence from a single point of failure.
- Hybrid P2P: Hybrid P2P networks combine elements of both centralized and decentralized architectures. They use a central server for initial peer discovery and communication establishment, but once the connection is established, the file transfers occur directly between peers. This hybrid approach provides a balance between efficiency and decentralization. Limewire is an example of a hybrid P2P network.
- Overlay P2P: Overlay P2P networks build a layer on top of the existing internet infrastructure to facilitate direct communication between peers. Peers form connections with other peers in the overlay network, creating a virtual network topology that spans across physical networks. Overlay networks are often used in large-scale P2P systems for improved scalability and fault tolerance.
- Unstructured P2P: Unstructured P2P networks do not enforce specific rules or guidelines for organizing peers or resources. Peers rely on random or ad-hoc connections to discover other peers within the network. Unstructured P2P networks are simple to implement but may suffer from scalability and inefficiency issues. The early versions of Gnutella operated as unstructured P2P networks.
- Structured P2P: Structured P2P networks utilize specific algorithms and data structures to organize peers and resources in a structured manner. Examples of structured P2P networks include the Chord and CAN (Content Addressable Network) protocols. Structured P2P networks provide efficient resource lookup and routing at the cost of increased complexity.
Each type of P2P network has its own advantages and disadvantages, and the choice of network type depends on the specific requirements and constraints of the application. By understanding the different types of P2P networks, developers and users can make informed decisions and leverage the most suitable network architecture for their needs.
Advantages of P2P
P2P technology offers a range of advantages that have contributed to its widespread adoption and popularity. Here are some key benefits of using P2P networks:
- Decentralization: One of the significant advantages of P2P networks is their decentralized nature. By removing the reliance on a central server, P2P networks are more resilient and less vulnerable to single points of failure. This ensures that the network remains operational even if some peers become unavailable.
- Scalability: P2P networks are highly scalable as the workload is distributed among all participating peers. As more peers join the network, the overall capacity and resources of the network increase, allowing for better performance and improved scalability without the need to invest in expensive infrastructure.
- Efficiency in File Sharing: P2P networks excel in file sharing scenarios. Each peer in the network acts as a potential source for the requested file, leading to faster and more efficient downloads. By leveraging the power of multiple peers simultaneously, P2P networks reduce the strain on individual sources and enable quicker file transfers.
- Reduced Bandwidth Costs: P2P networks can help reduce bandwidth costs for content providers. In traditional client-server models, servers bear the bandwidth costs for distributing files to multiple clients. However, in P2P networks, the bandwidth is shared among the peers, alleviating the burden on individual servers and reducing bandwidth costs.
- Increased Availability: P2P networks enhance file availability by allowing users to obtain files from multiple sources simultaneously. If a particular source is unavailable or experiences slow download speeds, the P2P network leverages other available sources to complete the file transfer. This redundancy ensures that files are readily accessible to users, even in scenarios where one or more peers may be offline.
- Collaborative Computing: P2P networks support collaborative computing, enabling users to leverage the collective resources and computing power of the network. Distributed computing projects, such as SETI@home and Folding@home, utilize P2P networks to harness the processing capabilities of individual devices, contributing to scientific research and advancements.
These advantages highlight the versatility and efficiency of P2P networks, making them an excellent choice for various applications, including content distribution, collaboration, and distributed computing.
Disadvantages of P2P
Although P2P networks offer numerous benefits, they also come with certain drawbacks that need to be considered. Here are some of the key disadvantages associated with P2P:
- Security Risks: P2P networks are vulnerable to security risks, including malware, viruses, and unauthorized access. Since peers can connect directly with each other, there is a higher risk of malicious files or attackers disguising themselves as legitimate sources. Users must exercise caution and employ proper security measures when participating in P2P networks.
- Quality and Reliability: The quality and reliability of downloaded files in P2P networks can vary. Not all sources may have the same file version or quality, leading to inconsistencies in the downloaded content. Additionally, since P2P networks rely on the participation of peers, if there is a lack of active sources for a particular file, the download speed and availability may be compromised.
- Copyright Infringement: P2P networks have often been associated with copyright infringement due to the ease of file sharing. Users can freely distribute copyrighted content without proper authorization, leading to legal consequences. While P2P technology itself is not inherently illegal, it has been subject to legal scrutiny and regulation in many jurisdictions.
- Network Overhead: P2P networks generate additional network overhead due to the constant exchange of data between peers. This can result in increased bandwidth usage and congestion, especially in networks with limited resources or slow internet connections. The network overhead can potentially impact the performance and responsiveness of other network activities.
- Lack of Centralized Control: In P2P networks, there is no centralized control or authority governing the system. While decentralization is a key advantage, it can also lead to challenges in terms of managing and enforcing policies, resolving disputes, and ensuring compliance. This lack of central control can make it difficult to address issues that arise within the network.
- Unequal Contribution: P2P networks rely on the willingness of peers to contribute resources to the network. However, not all participants contribute equally. Some users may consume more resources than they provide, creating an imbalance in the network. This unequal contribution can pose challenges for sustaining the network and distributing resources fairly.
It is important to be aware of these potential drawbacks and address them accordingly to ensure a secure and efficient P2P experience. Proper user education, security measures, and legal compliance can help mitigate some of these disadvantages and foster a more reliable and responsible use of P2P networks.
Common P2P Applications
P2P technology has revolutionized various aspects of our digital lives, enabling innovative applications that leverage the power of decentralized networks. Here are some common P2P applications that have gained popularity:
- File Sharing: P2P networks are renowned for their role in file sharing. Platforms like BitTorrent and eMule allow users to share files directly with one another, enabling efficient and widespread distribution of media, such as music, movies, and software. P2P file sharing has transformed the way we access and consume digital content.
- Messaging and Communication: P2P networks have also been utilized in messaging and communication applications. Peer-to-peer instant messaging platforms, like Skype and Telegram, enable users to exchange messages, voice calls, and video calls directly with each other, bypassing centralized servers. This enhances privacy, security, and efficiency in communication.
- Content Delivery Networks (CDNs): Some Content Delivery Networks utilize P2P technology to improve content delivery efficiency. By allowing users who have downloaded specific content to serve as sources for other users, CDNs can reduce server load and improve download speeds. This approach is particularly beneficial for popular content with high user demand.
- Peer-to-Peer Lending: P2P lending platforms connect borrowers with lenders directly. These platforms eliminate the need for traditional financial intermediaries, enabling individuals to lend and borrow money from each other. P2P lending has opened up new avenues for borrowing and investing, providing accessibility and potentially lowering costs compared to conventional lending institutions.
- Distributed Computing: P2P networks play a crucial role in distributed computing projects. Projects like SETI@home and Folding@home leverage the computational power of individual participants’ devices to solve complex scientific problems collectively. By distributing computing tasks across a network of devices, P2P networks enable large-scale scientific research and data analysis.
- Decentralized Cryptocurrencies: P2P networks are the foundation of decentralized cryptocurrencies like Bitcoin and Ethereum. These cryptocurrencies rely on P2P networks to facilitate secure and transparent transaction verification and recording. P2P technology eliminates the need for intermediaries and central authorities in financial transactions, providing greater autonomy and security.
These examples demonstrate the versatility and impact of P2P technology across various sectors. P2P applications continue to evolve, powering innovative solutions that promote collaboration, efficiency, and user empowerment in the digital realm.
Security Risks and Concerns
While P2P networks offer numerous benefits, they also present certain security risks and concerns that users need to be aware of. Here are some common security risks associated with P2P technology:
- Malware and Viruses: P2P networks are highly susceptible to malware and viruses due to the direct exchange of files between users. Malicious users can upload infected files, leading to the unintentional spread of malware across the network. It is crucial for users to exercise caution and use reliable antivirus software to protect themselves from potential threats.
- Privacy Risks: P2P networks operate on the principle of direct communication between peers, which can expose user privacy. Monitoring and tracking user activities are relatively easier in P2P networks compared to traditional client-server architectures. Users should be cautious about the personal information they share and consider using encryption and anonymity tools to safeguard their privacy.
- Copyright Infringement: P2P networks have been associated with copyright infringement due to the widespread sharing of copyrighted content without authorization. Engaging in illegal file sharing through P2P networks can lead to legal consequences, including lawsuits and fines. Users should be aware of copyright laws and respect intellectual property rights when using P2P networks.
- Identity Spoofing and Social Engineering: Due to the decentralized nature of P2P networks, it is challenging to verify the true identity of peers. Malicious users can impersonate others or engage in social engineering tactics to gain unauthorized access to sensitive information or exploit vulnerabilities. Users must exercise caution when interacting with unknown peers and avoid sharing sensitive information with untrusted sources.
- Unreliable Sources and Data Integrity: P2P networks rely on the contributions of individual peers to share files and data. However, not all sources can be trusted, and the integrity of downloaded files may be compromised. Users may encounter incomplete or tampered files, leading to data corruption or privacy breaches. It is important to verify the credibility of sources and use file verification mechanisms to ensure data integrity.
- Network Overload and Performance Issues: P2P networks can experience network overload due to the increased traffic generated by the constant exchange of data among peers. This can result in network congestion and performance issues, affecting the responsiveness and download speeds. Users should be mindful of their network resources and consider using quality of service (QoS) measures to manage network traffic.
These security risks and concerns highlight the importance of adopting proper security measures and responsible practices when utilizing P2P networks. Users should prioritize their privacy, employ reliable security tools, and exercise caution to mitigate potential risks and ensure a safe and secure P2P experience.
Conclusion
P2P technology has transformed the way we share, distribute, and collaborate in the digital world. By enabling direct communication and resource sharing between peers, P2P networks have revolutionized file sharing, messaging, content delivery, lending, distributed computing, and decentralized cryptocurrencies.
We explored the definition of P2P and its decentralized nature, allowing devices to act as both clients and servers. P2P networks have provided several advantages, including improved scalability, efficient file sharing, reduced bandwidth costs, enhanced availability, and collaborative computing.
However, it is important to acknowledge the potential disadvantages of P2P networks. Security risks, such as malware and privacy concerns, can pose significant threats. Copyright infringement and network congestion are also challenges that need to be addressed responsibly.
Despite these drawbacks, P2P networks continue to evolve and find application in numerous domains. They have revolutionized the way we access and share media, empowered users to collaborate and lend money directly, supported distributed computing research, and enabled the creation of decentralized cryptocurrencies.
As technology advances, it is essential for users to understand the benefits and risks associated with P2P networks. By following best practices, including using reliable security measures, respecting intellectual property rights, and verifying sources, users can navigate the world of P2P technology responsibly and enjoy its benefits while mitigating potential risks.
In conclusion, P2P networks have reshaped the digital landscape, providing decentralized and efficient ways to connect, collaborate, and distribute resources. With proper understanding and responsible usage, P2P technology can continue to offer innovative solutions, foster user empowerment, and drive the evolution of digital ecosystems.