Introduction
Welcome to our guide on the hashing algorithm used in Ethereum. Hashing algorithms are an essential component of blockchain technology, ensuring the integrity and security of the data stored on the Ethereum network. In this article, we will explore the concept of hashing algorithms, dive into the commonly used ones, and specifically examine the hashing algorithm employed by Ethereum.
Hashing algorithms play a pivotal role in data encryption and verification processes. They are mathematical functions that take an input (known as the “message”) and produce an output of fixed length (known as the “hash value”). The primary objective of a hashing algorithm is to convert data of any size into a unique hash value, which can then be used to verify the integrity and authenticity of the data.
Many different hashing algorithms exist, each with its own unique characteristics and uses. Some of the commonly used ones include MD5, SHA-1, SHA-256, and Keccak-256. These algorithms have varying levels of complexity and security, making them suitable for different applications.
Now, let’s shine a spotlight on the hashing algorithm used in Ethereum. Ethereum utilizes the Keccak-256 hashing algorithm, which is a member of the SHA-3 family of algorithms. Keccak-256 offers exceptional security and efficiency, making it well-suited for the demanding decentralized ecosystem of Ethereum.
In the following sections, we will delve deeper into the Keccak-256 hashing algorithm and explore how it is utilized within the Ethereum network. We will also outline the benefits that this algorithm brings to the blockchain, such as data integrity, tamper resistance, and efficient verification processes.
So, without further ado, let’s dive into the world of hashing algorithms and uncover the inner workings of Ethereum’s hashing algorithm.
What is a hashing algorithm?
A hashing algorithm is a mathematical function that takes an input (or “message”) and generates a fixed-length output known as a hash value or digest. The primary purpose of a hashing algorithm is to ensure data integrity and security by producing a unique representation of the original data. This unique hash value acts as a digital fingerprint for the input data, allowing for efficient verification and comparison.
Hashing algorithms are designed to have certain key properties:
- Deterministic: Given the same input, a hashing algorithm will always produce the same output. This property allows for easy verification of data integrity.
- Fixed output length: Hashing algorithms generate hash values of a fixed length, regardless of the size of the input. This makes them ideal for storing and comparing large amounts of data efficiently.
- One-way function: It should be computationally infeasible to reverse-engineer the original input from the hash value. This property provides security, as it prevents unauthorized access to the original data.
- Collision resistance: Hashing algorithms aim to minimize the likelihood of two different inputs producing the same hash value, known as a collision. While it is theoretically possible for collisions to occur, strong hashing algorithms have a very low probability of collision.
Hashing algorithms find applications in various fields, including data verification, password storage, encryption, and digital signatures. In the context of blockchain technology, hashing algorithms are used to secure the integrity of the data stored on the decentralized ledger.
When data is added to a blockchain, it is hashed using a specific hashing algorithm. This hash value is then stored within the blockchain, ensuring that any modifications or tampering with the data will result in a different hash value. This feature makes blockchains resistant to data tampering and provides a reliable way to verify the consistency of the stored information.
In the next section, we will take a closer look at some of the commonly used hashing algorithms, including SHA-1, SHA-256, and MD5, to gain a better understanding of their characteristics and applications.
Commonly used hashing algorithms
There are several widely used hashing algorithms that serve various purposes in different applications. Let’s explore some of the commonly used ones:
- MD5 (Message Digest Algorithm 5): MD5 is a widely recognized hashing algorithm that produces a 128-bit hash value. It is known for its speed and simplicity; however, it is considered relatively weak in terms of security due to vulnerabilities and collision attacks.
- SHA-1 (Secure Hash Algorithm 1): SHA-1 generates a 160-bit hash value and was widely used in the past. However, it is now considered deprecated and insecure due to vulnerabilities found in the algorithm. It is no longer recommended for critical security applications.
- SHA-256 (Secure Hash Algorithm 256-bit): SHA-256 is a member of the SHA-2 family of hashing algorithms, published by the National Institute of Standards and Technology (NIST). It produces a 256-bit hash value and is widely used in blockchain applications, including Bitcoin. SHA-256 is known for its strong security and resistance to collision attacks.
- SHA-3: SHA-3 is the latest addition to the Secure Hash Algorithm family, also published by NIST. It includes several hashing algorithms, with Keccak-256 being the one used in Ethereum. SHA-3 algorithms provide enhanced security and resistance against certain types of attacks compared to the SHA-2 family.
Each of these hashing algorithms has its own strengths and weaknesses, making them suitable for specific use cases. When it comes to blockchain technology, the choice of the hashing algorithm depends on factors such as security requirements, computational efficiency, and scalability.
It is important to note that the security of hashing algorithms has evolved over time, and what may have been considered secure in the past may no longer meet the standards of today. Therefore, it is crucial to stay updated with the latest cryptographic advances and use algorithms that are widely recognized as secure.
Now that we have explored some commonly used hashing algorithms, let’s delve into the specific hashing algorithm employed in the Ethereum network – Keccak-256.
Hashing algorithm used in Ethereum
Ethereum, one of the most popular blockchain platforms, utilizes the Keccak-256 hashing algorithm as its core cryptographic function. Keccak-256 is a member of the SHA-3 family of hashing algorithms, which were selected through a public competition organized by NIST to find a new, secure hashing algorithm. Keccak-256 was chosen as the winner and became the basis for the SHA-3 standard.
Keccak-256 operates on 64-byte blocks and produces a 256-bit hash value. It is designed to be highly secure and resistant to various cryptographic attacks, including pre-image attacks and collision attacks. The algorithm ensures that even a tiny change in the input data will result in a completely different hash value.
One of the notable features of Keccak-256 is its flexibility in supporting various output sizes. While Ethereum uses a 256-bit output, Keccak can generate hash values of different lengths, making it adaptable for different use cases. This flexibility allows Ethereum developers to utilize different hash lengths, depending on their specific needs and requirements.
The selection of Keccak-256 as Ethereum’s hashing algorithm was driven by the need for enhanced security, efficient computation, and the desire to align with the latest cryptographic standards. By leveraging Keccak-256, Ethereum ensures the integrity and security of the transactions and data stored on its blockchain network.
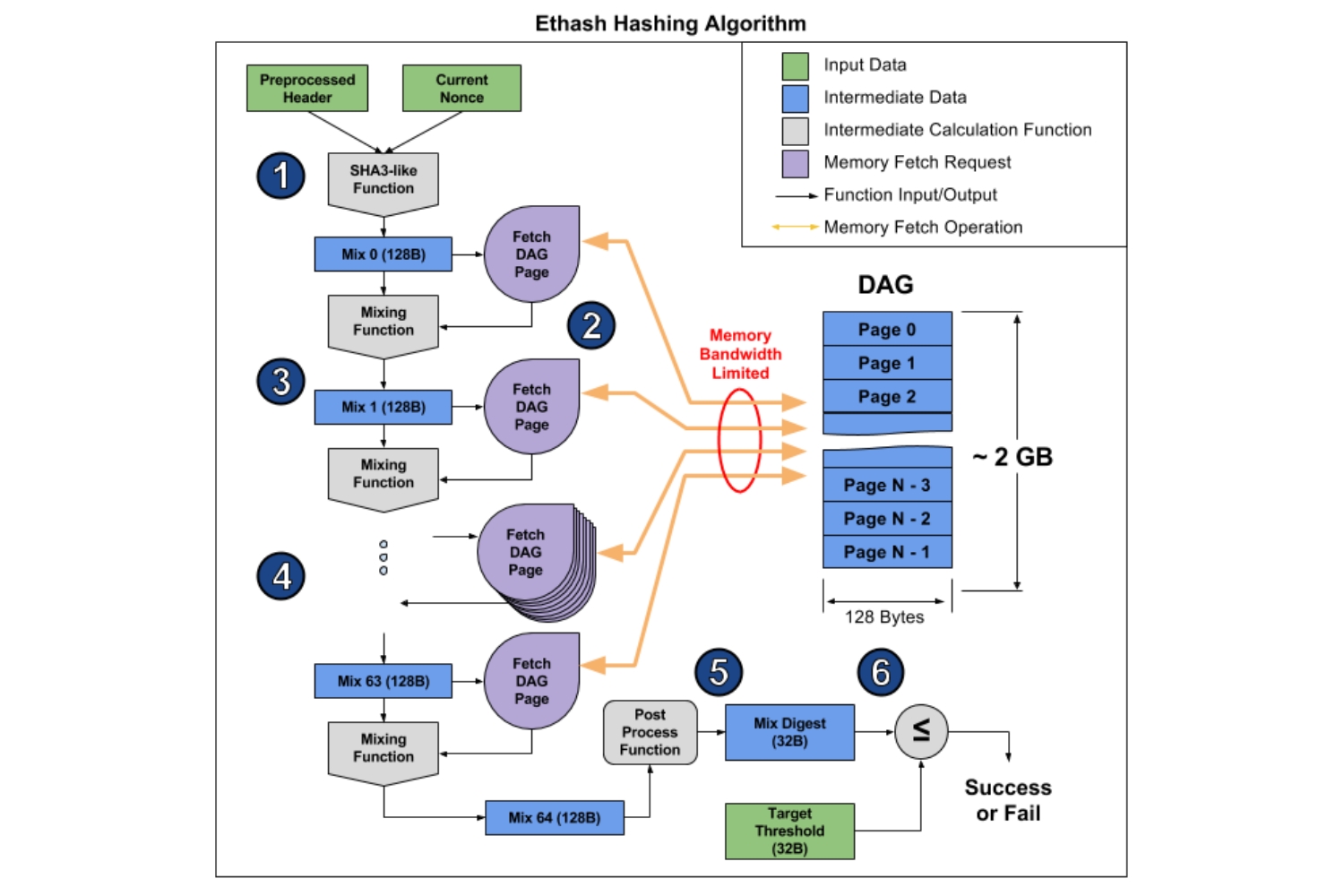
The implementation of Keccak-256 in Ethereum involves subjecting the input data to the algorithm’s repeated rounds of transformation, including permutation, mixing, and bit manipulation. These operations ensure that the resulting hash value is unique, tamper-resistant, and reflects the content of the original data.
As the Ethereum network continues to evolve, it is essential for the hashing algorithm to be able to withstand increasing computational power and potential cryptographic breakthroughs. Keccak-256’s reputation as a secure and efficient hashing algorithm positions Ethereum well for the future growth and security of the platform.
Now that we have explored the hashing algorithm used in Ethereum, let’s dive deeper into how hashing is used within the Ethereum network and the benefits it brings to the blockchain ecosystem.
Keccak-256
Keccak-256 is the specific implementation of the Keccak hashing algorithm that is used in Ethereum. It belongs to the SHA-3 family of cryptographic hash functions and is widely recognized for its security, efficiency, and resistance to cryptographic attacks. The “256” in its name refers to the length of the hash value it produces, which is 256 bits.
One of the key advantages of Keccak-256 is its ability to handle different output lengths, making it a flexible and versatile hashing algorithm. In the case of Ethereum, the 256-bit output length is used, providing a sufficient level of security for the blockchain network’s operations.
Keccak-256 operates by processing message data in a series of rounds, involving bitwise operations, permutation, and mixing operations. Throughout these rounds, the algorithm ensures that even a small change in the input data will result in a significantly different hash value, ensuring the data’s integrity and tamper resistance.
The Keccak-256 algorithm has been extensively analyzed and scrutinized by cryptographic experts, which has contributed to its wide adoption and acceptance. It has undergone thorough scrutiny in order to identify any potential vulnerabilities and ensure its robustness in withstanding attacks.
Moreover, the Keccak-256 algorithm is designed to be resistant to cryptanalytic attacks, including collision attacks, where two different inputs produce the same hash value. While it is theoretically possible for collisions to occur, Keccak-256’s cryptographic properties make such occurrences highly improbable and computationally infeasible to exploit. This collision resistance is crucial for maintaining the security and integrity of the data stored on the Ethereum blockchain.
The choice of Keccak-256 as the hashing algorithm for Ethereum showcases the platform’s commitment to implementing state-of-the-art cryptographic standards and ensuring the highest level of security for its users. By utilizing Keccak-256, Ethereum enhances the protection of data integrity, reducing the risk of unauthorized modifications and tampering.
The security and efficiency of Keccak-256 make it a suitable choice for a decentralized system like Ethereum, which relies on cryptographic functions for tasks such as transaction verification, smart contract execution, and data storage. The algorithm’s robustness and computational efficiency contribute to the overall scalability and reliability of the Ethereum network.
Now that we have explored Keccak-256 and its significance in Ethereum, let’s delve into how hashing is utilized within the Ethereum network and the benefits it brings to the blockchain ecosystem.
How hashing is used in Ethereum
Hashing plays a critical role in various aspects of the Ethereum network, ensuring the integrity, security, and efficiency of its operations. Let’s explore how hashing is specifically utilized in Ethereum:
Data Integrity: When a transaction is created in Ethereum, the transaction data, including the sender, recipient, and amount, is hashed using the Keccak-256 algorithm. This hash value acts as a unique identifier for the transaction and provides a secure way to verify its authenticity and integrity. Any changes to the transaction data would result in a different hash value, thereby alerting the network to potential tampering attempts.
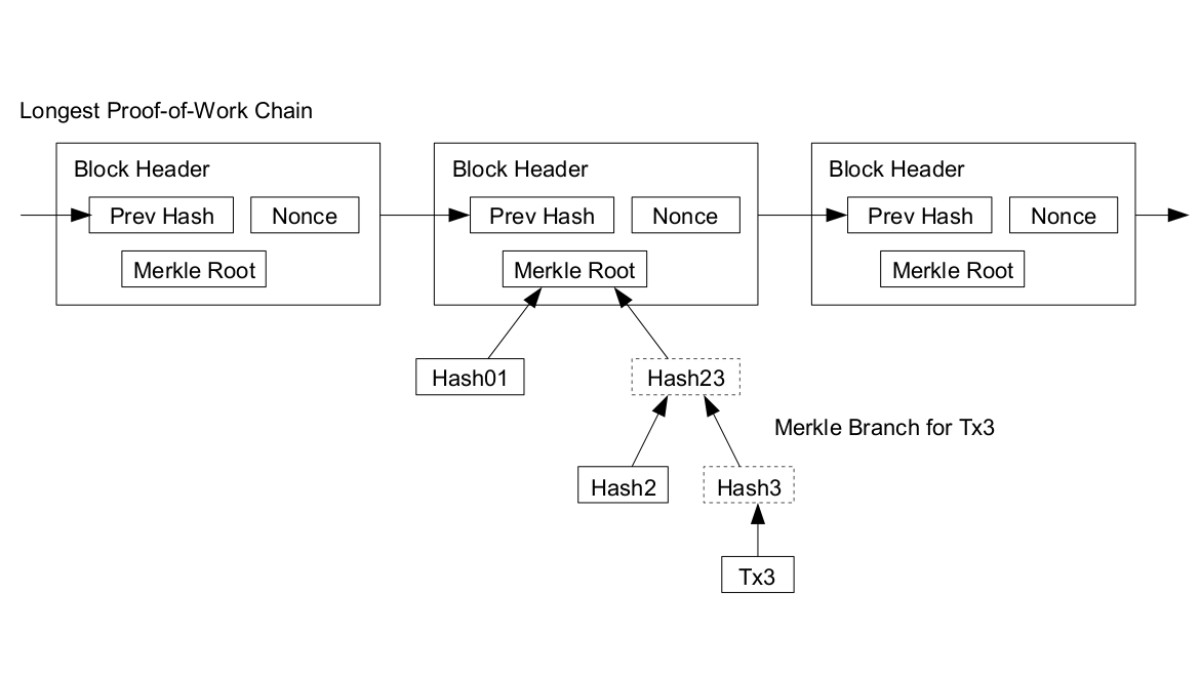
Merkle Trees: Ethereum employs Merkle trees, a data structure that utilizes hashing, to efficiently store and verify the integrity of large sets of data. Merkle trees help reduce the computational burden by organizing data into smaller, manageable chunks and hashing them. The resulting hash values are then further hashed until a single root hash is obtained, known as the Merkle root. This Merkle root serves as a compact representation of the entire set of data, enabling efficient verification and retrieval of information within the Ethereum blockchain.
Block Validation: In Ethereum, each block includes a header, which contains various pieces of information, including the previous block’s hash. This hash acts as a link that connects each block to the previous one, forming an unbroken chain. To ensure the validity and integrity of a newly added block, miners verify that the previous block’s hash matches the actual hash stored on the blockchain. This process, known as block validation, relies on hashing to guarantee the correctness of the blockchain’s structure.
Smart Contract Execution: Ethereum’s smart contracts, self-executing contracts with the terms of the agreement directly written into code, also rely on hashing for security and verification purposes. Each smart contract is assigned a unique address derived from the hash of its contract code. This address serves as an identifier and allows participants to interact with the contract on the Ethereum network using the address, ensuring secure and reliable execution of the contract’s functions.
By utilizing hashing algorithms like Keccak-256, Ethereum ensures that the data stored within its blockchain is resistant to tampering, secure from unauthorized modifications, and efficiently verifiable by network participants. Hashing provides a foundation of trust and security in the Ethereum network, enabling participants to confidently interact with the blockchain’s data and smart contracts.
Next, let’s explore the benefits that the Keccak-256 hashing algorithm brings to Ethereum and how it enhances the overall blockchain ecosystem.
Benefits of using Keccak-256 in Ethereum
The utilization of the Keccak-256 hashing algorithm in Ethereum brings several notable benefits to the blockchain ecosystem. Let’s explore these advantages:
Security: Keccak-256 is designed to be highly secure, with a low probability of collisions and resistance to various cryptographic attacks. Its strong cryptographic properties ensure that the data stored on the Ethereum blockchain remains tamper-resistant and that any modifications to the data will result in different hash values. This enhances the overall security of the network, making it more robust against unauthorized access and manipulation.
Efficiency: Keccak-256 offers efficient computation, which is crucial for a decentralized system like Ethereum. The algorithm is optimized to perform hashing operations quickly, ensuring that transactions, smart contract executions, and other blockchain operations can be processed efficiently. This efficiency contributes to the scalability and performance of the Ethereum network, allowing for a larger volume of transactions to be processed within a given timeframe.
Alignment with Standards: By adopting the Keccak-256 hashing algorithm, Ethereum aligns itself with the latest cryptographic standards. Keccak-256 is part of the SHA-3 family of algorithms, which have undergone thorough analysis and scrutiny to ensure their security and resistance to attacks. This alignment with recognized standards enhances trust in the Ethereum ecosystem and provides reassurance to developers and users that their data is protected using state-of-the-art cryptography.
Flexibility: Keccak-256 offers the flexibility of generating hash values of different lengths. Ethereum specifically uses the 256-bit hash output, which provides a suitable balance between security and efficiency for the platform. The ability to choose different output lengths allows developers to adapt the hashing algorithm to their specific needs and requirements, accommodating various use cases within the Ethereum ecosystem.
Overall, the use of Keccak-256 in Ethereum reinforces the platform’s commitment to security, efficiency, and adherence to cryptographic standards. The algorithm’s strong security properties, computational efficiency, and flexibility contribute to building a robust and reliable blockchain ecosystem. With Keccak-256, Ethereum users can have confidence in the security and integrity of their transactions, smart contracts, and data stored on the blockchain.
Now that we have explored the benefits of using Keccak-256 in Ethereum, let’s wrap up our discussion on the hashing algorithm and its significance in the Ethereum network.
Conclusion
In this guide, we have delved into the hashing algorithm used in Ethereum and its significance in ensuring data integrity and security on the blockchain. Ethereum adopts the Keccak-256 hashing algorithm, a member of the SHA-3 family, known for its strong cryptographic properties and resistance to attacks.
We explored the concept of hashing algorithms and their role in generating unique hash values for data. We also discussed some commonly used hashing algorithms, such as MD5, SHA-1, SHA-256, and how they compare to Keccak-256 in terms of security and efficiency.
Keccak-256 provides several benefits to the Ethereum network. It enhances the overall security by ensuring data integrity and tamper resistance. The algorithm’s efficiency contributes to the scalability and performance of the Ethereum blockchain, enabling a larger volume of transactions to be processed. Keccak-256 also aligns with recognized cryptographic standards, establishing trust and confidence in the Ethereum ecosystem.
We explored how hashing is utilized in Ethereum for data integrity, Merkle trees, block validation, and smart contract execution. Hashing plays a crucial role in these aspects, enabling participants to verify the authenticity and integrity of transactions, efficiently store and retrieve data, and facilitate secure smart contract execution.
Overall, the choice of the Keccak-256 hashing algorithm in Ethereum reflects the platform’s commitment to security, efficiency, and alignment with cryptographic standards. By leveraging Keccak-256, Ethereum provides a robust, secure, and scalable decentralized ecosystem for transactions, smart contracts, and other blockchain operations.
As Ethereum continues to evolve and grow, the strength and reliability of the hashing algorithm will remain paramount in ensuring the security and trustworthiness of the network. The implementation of Keccak-256 reinforces Ethereum’s dedication to maintaining the highest standards of data integrity and security.
In conclusion, the Keccak-256 hashing algorithm is a fundamental component of the Ethereum blockchain, offering robust security, computational efficiency, and flexibility. Its use in Ethereum establishes a strong foundation for the network’s operations and instills confidence in its users. As advancements in cryptography continue, Ethereum will adapt and evolve its hash functions to remain at the forefront of secure and reliable blockchain technology.