Introduction
The rise of blockchain technology has revolutionized various industries, from finance to supply chain management. One of the intriguing aspects of blockchain-enabled systems is their ability to operate in a trustless environment. Despite the term “trustless” appearing counterintuitive, it is a defining characteristic of blockchain technology.
Blockchain technology was originally introduced as the underlying technology behind the cryptocurrency Bitcoin. However, its applications have since extended beyond digital currencies, proving to be a powerful tool for creating secure and decentralized systems.
So, what exactly is a trustless system? In simple terms, a trustless system is one that operates without the need for participants to place trust in a central authority or each other. It achieves this through a combination of cryptographic algorithms and consensus mechanisms.
Traditionally, in centralized systems, trust is placed in a single governing entity, such as a bank or a government, to facilitate transactions and ensure security. In contrast, trustless systems distribute authority across a network of participants, where no single entity holds complete control.
In this article, we will explore the concept of trustlessness in blockchain technology, how it works, and the implications it has on various industries.
What is Blockchain?
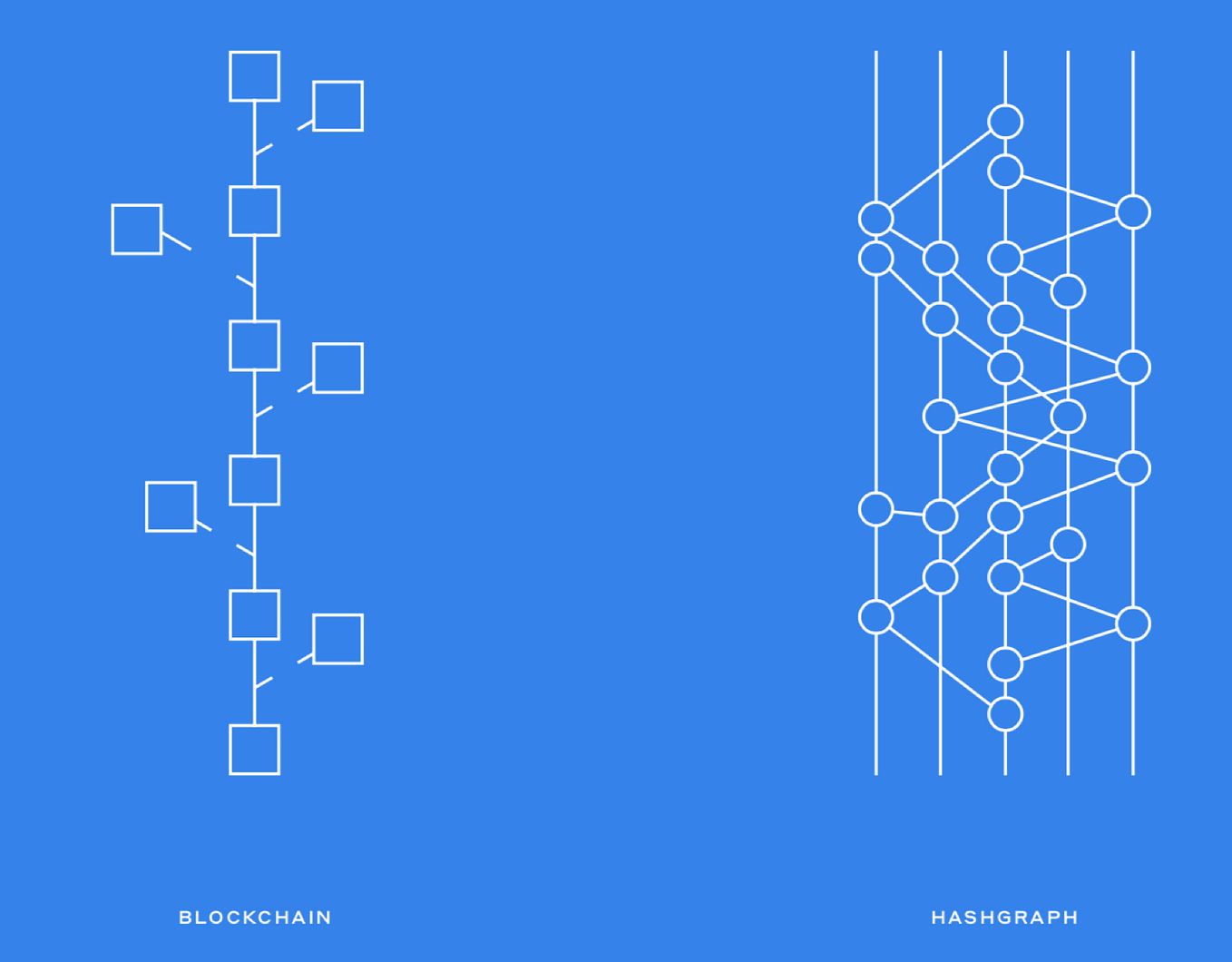
Before diving into the concept of trustless systems, it is essential to understand what blockchain technology is. At its core, a blockchain is a decentralized and distributed ledger that records transactions across multiple computers or nodes in a network.
Each transaction that occurs on a blockchain is bundled into a block and added to a chain of previously verified blocks, hence the name “blockchain.” This chain of blocks forms a permanent and transparent record of all transactions, creating a tamper-proof and auditable history.
Blockchain technology operates on the principles of decentralization, transparency, and immutability. Unlike traditional databases or ledgers, which are stored and controlled by a central authority, the data on a blockchain is stored across multiple nodes in a network. This decentralization ensures that no single entity or individual has complete control over the system.
Additionally, the transparency of blockchain technology allows all participants in the network to view and verify transactions. Each transaction is timestamped and linked to previous transactions, creating a transparent and traceable audit trail.
Immutability is a fundamental characteristic of blockchain technology. Once a block is added to the blockchain, it becomes extremely challenging to alter or delete the information contained within it. This ensures the integrity and security of the data, making blockchain an ideal solution for applications that require tamper-proof records.
The most well-known use case of blockchain is in the realm of digital currencies, with Bitcoin being the first decentralized cryptocurrency built on blockchain technology. However, the potential applications of blockchain extend far beyond cryptocurrencies.
Blockchain technology can be utilized in various industries to streamline processes, enhance security, and facilitate trustless transactions. From supply chain management to healthcare, from voting systems to intellectual property protection, blockchain has the potential to revolutionize how we conduct business and interact with one another.
Trustless Systems
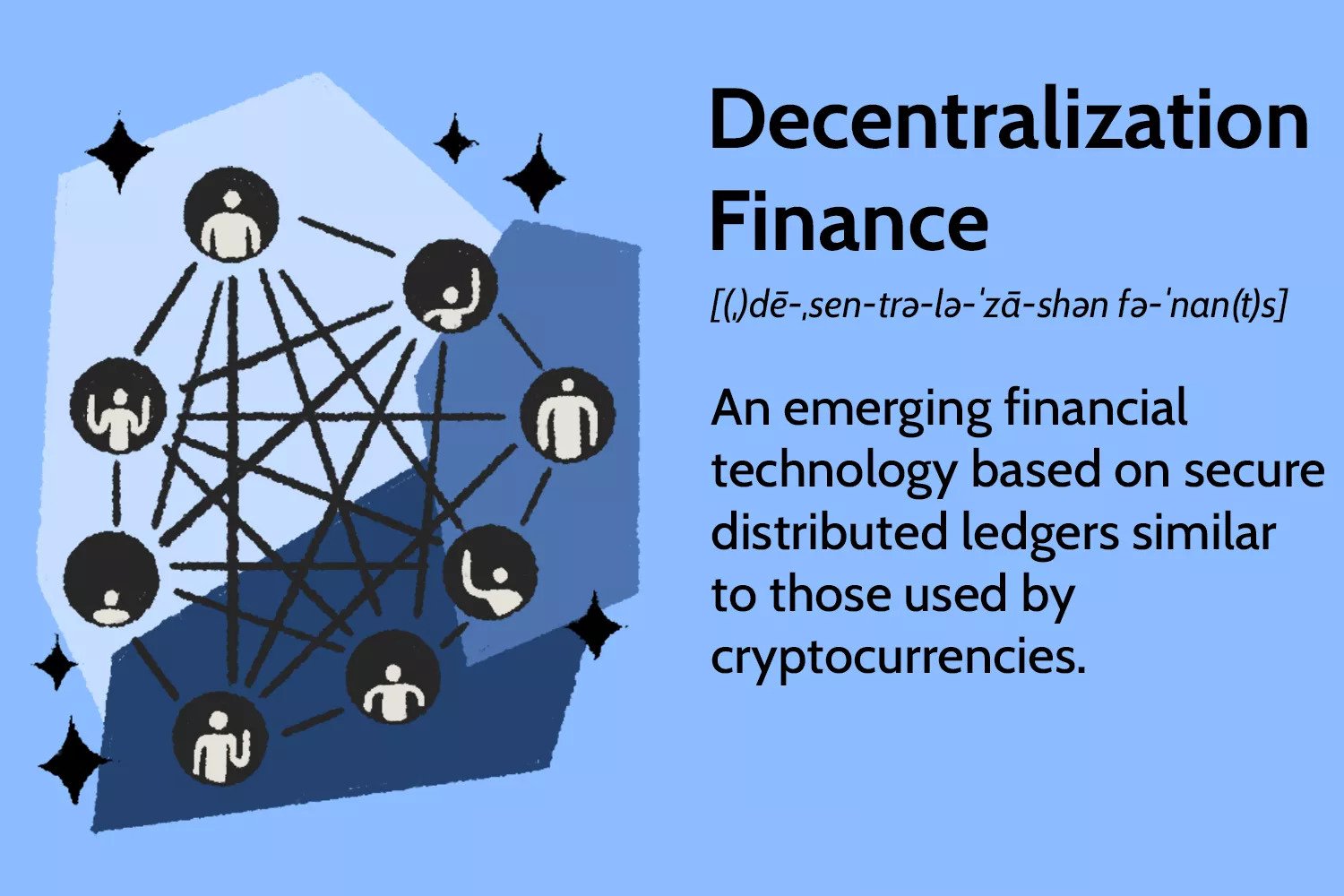
In the context of blockchain technology, trustless systems refer to the ability to conduct transactions and verify information without the need for trust in a central authority or other participants. It is a fundamental principle that sets blockchain apart from traditional centralized systems.
In traditional systems, trust is placed in a central entity to validate transactions and maintain the integrity of the system. For example, when making a financial transaction through a bank, individuals trust that the bank will accurately record and execute the transaction.
In a trustless system, transactions are verified and validated through a consensus mechanism, typically implemented through a consensus algorithm such as Proof of Work (PoW) or Proof of Stake (PoS). These mechanisms ensure that multiple participants in the network reach a consensus on the validity of transactions without relying on centralized authority.
Trust is replaced with cryptographic algorithms, mathematical proofs, and consensus protocols. Through these mechanisms, the entire network collectively validates transactions, eliminating the need for reliance on a single trusted entity.
By eliminating the need for trust, trustless systems offer several advantages. Firstly, they enhance security. As transactions are verified and recorded on multiple nodes in the network, it becomes extremely difficult for malicious actors to tamper with or manipulate the data. This makes trustless systems highly resistant to fraud, hacking, and unauthorized modifications.
Trustless systems also promote transparency and accountability. As every transaction is recorded on the blockchain, participants can view and verify the history of transactions. This transparency builds trust among participants, and any discrepancy or fraudulent activity can be easily identified and traced back to its source.
Moreover, trustless systems enable peer-to-peer interactions without the need for intermediaries. This reduces costs associated with middlemen and streamlines transactions. It also provides access to financial services for unbanked populations who may not have access to traditional banking infrastructure.
Overall, trustless systems empower individuals and businesses by providing a secure, transparent, and efficient mechanism for conducting transactions. By removing the need for trust in centralized entities, blockchain-enabled trustless systems have the potential to transform various sectors, revolutionizing industries such as finance, supply chain management, healthcare, and more.
How Does Trustless Work in Blockchain?
To understand how trustlessness is achieved in the context of blockchain technology, it is important to delve into the mechanisms that underpin its operation. There are a few key components that contribute to the trustless nature of blockchain systems.
Decentralization: Blockchain relies on a decentralized network of computers or nodes, where each node maintains a copy of the entire blockchain and participates in the validation and verification process. This decentralized structure ensures that no single entity has complete control or authority over the system.
Cryptographic Algorithms: Cryptography plays a crucial role in establishing trustlessness. Blockchain uses cryptographic algorithms to secure the data and provide authenticity and integrity. Hash functions, digital signatures, and encryption techniques are employed to verify the identity of users, ensure data integrity, and protect sensitive information.
Consensus Mechanisms: Consensus mechanisms are employed to reach agreement on the validity of transactions and determine the order in which they are added to the blockchain. Proof of Work (PoW) and Proof of Stake (PoS) are two commonly used consensus algorithms. In PoW, participants compete to solve complex mathematical puzzles, and the winner (node) gets the right to add the next block to the chain. In PoS, participants are selected to validate transactions based on the number of coins they hold and are willing to “stake” as collateral.
These mechanisms ensure that the majority of participants in the network agree on the state of the blockchain, making it difficult for any individual or group to manipulate or alter the data without consensus.
When a transaction is initiated on a blockchain, it is broadcasted to the network and distributed to multiple nodes. The distributed network then collectively validates the transaction, ensuring that it meets the predefined rules and criteria. Once the transaction is validated and confirmed by a consensus mechanism, it is added to a block and permanently recorded on the blockchain.
Every participant in the network has access to the complete history of transactions and can independently verify the validity of the blockchain. This transparent and decentralized nature ensures that the system is trustless, as participants do not have to rely on a single trusted authority to validate and maintain the integrity of the transactions.
Through decentralization, cryptographic algorithms, and consensus mechanisms, blockchain achieves a trustless environment, where individuals can securely transact and interact without relying on intermediaries or centralized entities.
Transparency and Accountability in Trustless Systems
One of the key benefits of trustless systems built on blockchain technology is the enhanced transparency and accountability they offer. Unlike traditional centralized systems where trust is placed in a single authority to maintain transparency, blockchain enables participants to independently verify and validate transactions, ensuring a higher level of transparency and accountability.
Transparency is inherent in blockchain technology because every transaction is recorded on a distributed ledger that is accessible to all participants in the network. This transparency builds trust among participants, as they can view and verify the history of transactions without relying on a central authority or intermediaries.
With blockchain, the entire transaction history from the very first block is permanently stored, providing an immutable and tamper-resistant audit trail. This transparency not only fosters trust but also enables effective auditing, as auditors can easily verify the accuracy and integrity of the data recorded on the blockchain.
Moreover, the use of cryptographic algorithms in blockchain technology ensures the integrity and authenticity of transactions. Each transaction is digitally signed, providing a unique identifier for participants and ensuring that the data has not been altered. Any attempt to modify a transaction would result in a change in the cryptographic hash, alerting participants to the tampering attempt.
Accountability is another vital aspect of trustless systems. In traditional centralized systems, accountability is often placed on a single entity or authority. However, in trustless systems, accountability is distributed across the network. Each participant is responsible for maintaining the integrity of the blockchain and verifying the transactions.
Consensus mechanisms, such as Proof of Work (PoW) or Proof of Stake (PoS), further strengthen accountability in blockchain networks. Participants are incentivized to act in the best interest of the network, as any malicious behavior can result in penalties or loss of stake. This ensures that participants collectively play a role in maintaining the integrity and security of the system.
Trustless systems built on blockchain technology provide a higher degree of transparency and accountability compared to centralized systems. Participants can independently verify transactions, ensuring that the data is accurate, tamper-proof, and auditable. This transparency not only improves trust among participants but also reduces the risk of fraud or misconduct, as any discrepancies can be readily identified and addressed.
Furthermore, the transparency and accountability of trustless systems can have wider societal implications. It allows individuals, organizations, and governments to foster a culture of openness, fairness, and accountability, setting a new standard for conducting business and exchange of value.
Benefits of Trustless Systems
Trustless systems, powered by blockchain technology, bring numerous benefits to various industries and sectors. These benefits stem from the unique characteristics of trustlessness, which include enhanced security, reduced costs, increased efficiency, and improved accessibility.
1. Enhanced Security: Trustless systems provide a higher level of security compared to traditional centralized systems. The use of cryptographic algorithms and consensus mechanisms ensures that transactions are validated and recorded on a tamper-proof and immutable ledger. This makes it extremely difficult for malicious actors to alter or manipulate the data, protecting against fraud, hacking, and unauthorized access.
2. Reduced Costs: Trustless systems eliminate the need for intermediaries, such as banks or third-party service providers, reducing transaction costs. By removing the reliance on trusted authorities, participants can directly interact with each other, streamlining processes and reducing fees associated with middlemen. This cost reduction is particularly beneficial in cross-border transactions, where traditional systems often incur high fees and extended settlement times.
3. Increased Efficiency: Trustless systems offer faster and more efficient transactions. Traditional systems often involve lengthy processes and multiple intermediaries, leading to delays and inefficiencies. With trustless systems, transactions can occur directly between participants, cutting out unnecessary steps and reducing the time and resources required for verification and settlement. This increased efficiency has the potential to revolutionize industries such as supply chain management and financial services.
4. Improved Accessibility: Trustless systems provide access to financial services and other decentralized applications to individuals who are unbanked or underbanked. Traditional banking systems often require individuals to meet stringent criteria and rely on physical infrastructure. Trustless systems, on the other hand, enable anyone with internet access to participate, opening up opportunities for financial inclusion and economic empowerment.
5. Transparent and Auditable: Trustless systems offer a high level of transparency and auditability. As every transaction is recorded on a distributed ledger, participants can independently verify and audit the history of transactions. This transparency fosters trust among participants, reduces the risk of fraud, and allows for effective auditing and compliance monitoring.
6. Decentralization: Trustless systems are built on a decentralized network, distributing authority and control among multiple participants. This decentralization ensures that no single entity or group can monopolize or manipulate the system. It promotes a more equitable and democratic environment, where decisions are made collectively, and power is distributed among the network participants.
Overall, trustless systems offer a range of benefits, including enhanced security, reduced costs, increased efficiency, improved accessibility, transparency, and decentralization. These benefits have the potential to transform various industries, shape new business models, and empower individuals and communities by facilitating secure, efficient, and inclusive transactions.
Potential Applications of Trustless Systems
The advent of trustless systems based on blockchain technology has opened up a wide range of potential applications across various industries. These applications leverage the transparency, security, and efficiency offered by trustless systems to transform traditional processes and create new opportunities.
1. Financial Services: Trustless systems have the potential to revolutionize the financial industry by enabling secure and efficient transactions without the need for traditional intermediaries. Blockchain-based cryptocurrencies, such as Bitcoin and Ethereum, showcase the possibility of decentralized digital currencies that allow for peer-to-peer transactions worldwide. Additionally, trustless systems can facilitate decentralized lending and borrowing, cross-border payments, and remittances, providing financial services to unbanked populations.
2. Supply Chain Management: Trustless systems can enhance transparency and traceability in supply chains, reducing the risk of counterfeit products, ensuring ethical sourcing, and streamlining logistics. With blockchain, every step of the supply chain can be recorded and verified, allowing participants to track the origin, movement, and quality of products in real-time. This transparency fosters trust among stakeholders and minimizes the need for costly audits and manual record-keeping.
3. Healthcare: Trustless systems can improve the security and privacy of health records, enable secure sharing of medical data between healthcare providers, and streamline insurance processes. By utilizing blockchain technology, patient information can be securely stored, ensuring that only authorized parties have access. This can lead to more accurate and coordinated care, reduced administrative burdens, and enhanced data security and integrity.
4. Voting Systems: Trustless systems have the potential to revolutionize voting processes by enhancing transparency, security, and participation. By utilizing blockchain technology, votes can be securely recorded, tamper-proof, and auditable. This mitigates the risk of voter fraud and enables remote and transparent voting, ensuring a more inclusive and trustworthy democracy.
5. Intellectual Property Protection: Trustless systems can be utilized to establish a transparent and immutable record of intellectual property rights, ensuring that creators receive adequate credit and protection for their work. Smart contracts, powered by blockchain technology, can automate the registration, licensing, and payment processes, reducing the complexity and costs associated with intellectual property management.
6. Internet of Things (IoT): Trustless systems can facilitate trust and secure interactions within the rapidly evolving IoT ecosystem. With blockchain, IoT devices can securely authenticate and interact with each other, ensuring data integrity and privacy. This trustless environment allows for the seamless exchange of data and value between IoT devices, enabling innovative and secure applications across various sectors.
These are just a few examples of the potential applications of trustless systems. As the technology continues to evolve, new use cases and opportunities will emerge. Trustless systems have the potential to reshape entire industries, providing secure, transparent, and efficient solutions that empower individuals and enable new business models.
Challenges and Limitations of Trustless Systems
While trustless systems based on blockchain technology offer numerous benefits, there are some challenges and limitations that need to be addressed for widespread adoption and implementation.
1. Scalability: One of the primary challenges of trustless systems is scalability. As the number of participants and transactions in a blockchain network increases, the system’s performance can suffer. The decentralized nature of trustless systems requires every node to process and validate every transaction, which can lead to slower transaction times and increased costs. Scaling solutions such as off-chain processing and sharding are being explored, but further advancements are needed to handle the scale of global applications.
2. Energy Consumption: Trustless systems, particularly those that utilize Proof of Work (PoW) consensus, consume significant amounts of computational power and energy. The process of mining, which validates transactions and adds them to the blockchain, requires intensive computational calculations. This high energy consumption has raised concerns regarding the environmental impact of blockchain technology. Research and development of more energy-efficient consensus mechanisms are necessary to mitigate this challenge.
3. Regulatory Compliance: Trustless systems can often pose challenges in terms of regulatory compliance. While blockchain technology promotes transparency and security, it can also make it challenging to meet certain regulatory requirements, such as data privacy and know-your-customer (KYC) regulations. Striking a balance between the benefits of decentralization and the need to comply with legal and regulatory frameworks remains a challenge that needs to be addressed to enable broader adoption.
4. User Experience: The user experience of trustless systems can be complex and unfamiliar to average users. The need to manage private cryptographic keys, wallets, and interact with decentralized applications (dApps) can present usability challenges. Simplifying the user experience and making trustless systems more user-friendly are crucial to promote wider adoption among the general population.
5. Governance and Consensus: Trustless systems often require consensus mechanisms to validate transactions and maintain the integrity of the network. However, determining the appropriate governance and consensus model can be a challenge. Achieving consensus among a large and diverse network of participants, while ensuring the interests of all stakeholders are taken into account, is a complex task that requires ongoing research and development.
6. Security Risks: Despite the inherent security of trustless systems, there are still vulnerabilities that need to be mitigated. Smart contract vulnerabilities, hacking attempts on exchanges, and the potential for 51% attacks (where an entity gains majority control of the network) are issues that need to be addressed to ensure the overall security of trustless systems.
Addressing these challenges and limitations is crucial for the widespread adoption and successful implementation of trustless systems. Further research, technological advancements, and collaboration between industry, regulators, and academia are necessary to overcome these hurdles and unlock the full potential of trustless systems.
Conclusion
Trustless systems built on blockchain technology have the potential to transform various industries by providing secure, transparent, and efficient solutions. Through decentralization, cryptographic algorithms, and consensus mechanisms, trustless systems eliminate the need for participants to place trust in a central authority or each other.
Blockchain technology has emerged as a powerful tool, enabling trustless systems that enhance security, reduce costs, increase efficiency, and improve accessibility. The transparency and accountability offered by trustless systems foster trust among participants and promote a culture of openness and fairness in various sectors.
Despite the numerous benefits of trustless systems, they also face challenges and limitations such as scalability, energy consumption, regulatory compliance, user experience, governance, and security risks. Addressing these challenges requires ongoing research, technological advancements, and collaboration among stakeholders.
As the technology continues to evolve, new use cases for trustless systems will continue to emerge. Industries such as finance, supply chain management, healthcare, and voting systems stand to benefit from the transparency, security, and efficiency that trustless systems offer.
Trustless systems have the potential to reshape traditional processes, create new opportunities, and empower individuals and communities. By enabling secure and efficient transactions without the need for intermediaries or centralized authorities, trustless systems unlock a world of possibilities, fostering innovation and transforming the way we conduct business and interact with one another.