Introduction
Welcome to the world of cybersecurity, where protecting sensitive data and systems from various threats has become crucial in today’s digital landscape. While most people are familiar with the concept of cybersecurity in relation to computers, networks, and software, there is another important aspect that often goes unnoticed – OT Cybersecurity.
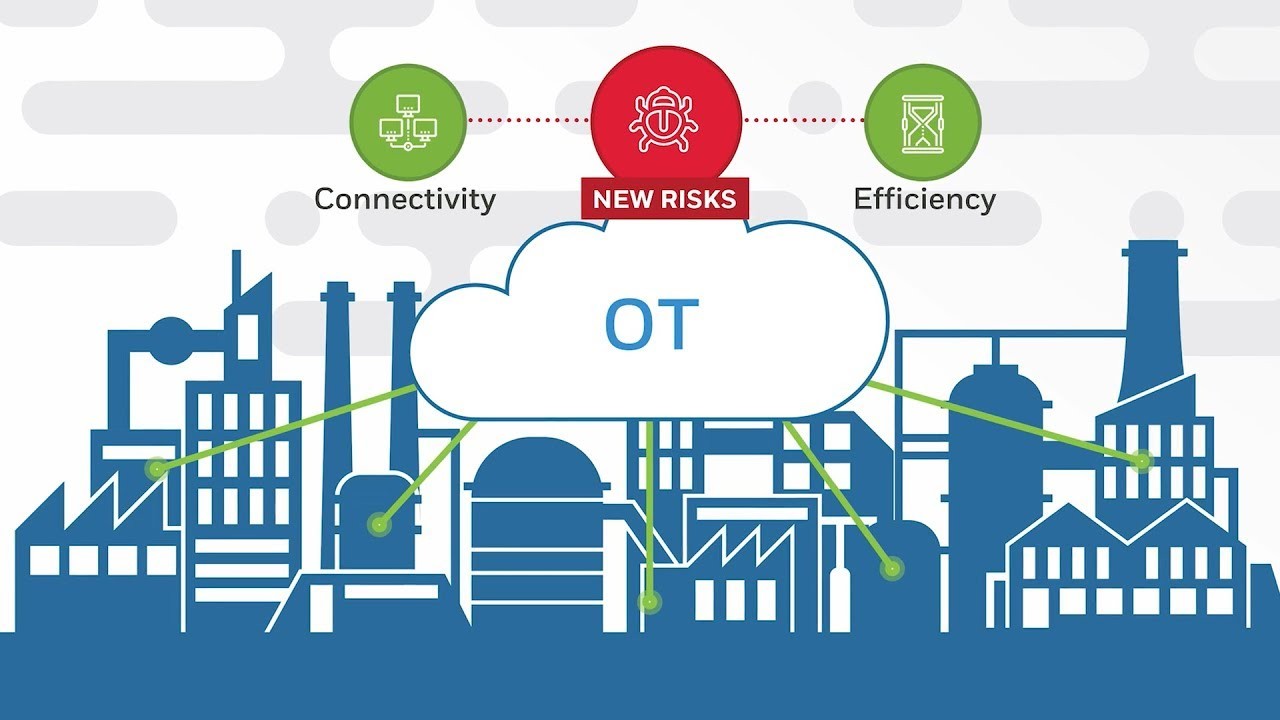
OT, which stands for Operational Technology, refers to the hardware, software, and systems used to control and manage physical processes and infrastructure in industries such as manufacturing, energy, transportation, and utilities. These systems are critical to the smooth operation of these industries and are often interconnected with information technology (IT) systems. OT cybersecurity, therefore, focuses on the protection of these operational technologies from cyber threats.
The convergence of IT and OT has opened up new avenues for hackers and cybercriminals to exploit vulnerabilities and gain unauthorized access to critical infrastructure. From power grids to industrial control systems, the potential consequences of a successful cyber attack on OT systems can be devastating, not only causing financial losses but also endangering public safety.
As organizations increasingly rely on interconnected OT systems to enhance efficiency and productivity, the need for robust cybersecurity measures becomes paramount. In this article, we will explore the importance of OT cybersecurity, the key differences between IT and OT cybersecurity, the common threats faced in the OT environment, and the challenges associated with securing OT systems.
Additionally, we will delve into best practices and tools used to protect OT systems from cyber threats. Whether you are an industrial professional, a cybersecurity enthusiast, or just curious about the world of OT cybersecurity, this article aims to provide you with a comprehensive understanding of this critical field.
What is OT Cybersecurity?
OT cybersecurity refers to the set of practices, measures, and technologies implemented to protect operational technology (OT) systems from cyber threats. These systems, which include industrial control systems (ICS), supervisory control and data acquisition (SCADA) systems, and other hardware and software used in critical industries, play a vital role in controlling and managing physical processes.
OT systems are designed to ensure the safe and efficient operation of industries such as manufacturing, energy, transportation, and utilities. They control processes such as power generation, water treatment, production lines, and transportation networks. However, as these systems become more interconnected with IT networks and the Internet, they become vulnerable to cyber attacks.
OT cybersecurity focuses on securing these critical infrastructure systems and protecting them from various threats, including unauthorized access, data breaches, and malicious activities. The goal is to safeguard the integrity, availability, and confidentiality of the OT systems, ensuring their continuous operation and preventing any disruption that could have severe consequences.
Effective OT cybersecurity involves a multi-layered approach that combines hardware, software, and procedural controls to mitigate risks and defend against cyber threats. It includes elements such as network security, access control, threat detection, incident response, and security awareness training.
One of the key aspects of OT cybersecurity is the identification and assessment of the potential vulnerabilities in the OT systems. This involves analyzing the OT infrastructure, identifying weak points, and understanding how these vulnerabilities can be exploited by attackers.
OT cybersecurity also encompasses the development and implementation of policies, procedures, and guidelines that govern the secure operation of OT systems. This includes defining access controls, establishing incident response protocols, and conducting regular security audits and assessments.
Moreover, OT cybersecurity involves continuous monitoring of the OT systems to detect any abnormal activities or potential threats. This can be done through the use of security tools and technologies that provide real-time visibility into the network, enabling security professionals to identify and respond to any potential security incidents.
Overall, OT cybersecurity plays a critical role in safeguarding the operation and integrity of industrial control systems and other OT infrastructure. By implementing robust security measures and staying vigilant against emerging threats, organizations can protect their critical assets and ensure the smooth operation of their industrial processes.
The Importance of OT Cybersecurity
In today’s interconnected world, the security of operational technology (OT) systems has become paramount. The consequences of a cyber attack on critical infrastructure can be severe, ranging from financial losses to disruption of essential services and potentially even loss of life. Here are some key reasons why OT cybersecurity is of utmost importance:
- Safeguarding public safety: Industries such as energy, transportation, and utilities play a crucial role in providing essential services to the public. A successful cyber attack on these OT systems can lead to disruptions, compromising the safety and well-being of individuals, communities, and even nations.
- Protecting critical infrastructure: OT systems control and manage critical infrastructure, including power grids, water treatment plants, and transportation networks. Securing these systems is not only necessary to ensure their continuous operation but also to prevent potential damage to the environment and economic stability.
- Preventing financial losses: The impact of a cyber attack extends beyond immediate disruptions. It can result in significant financial losses due to system downtime, production interruptions, recovery costs, regulatory fines, and damage to the organization’s reputation.
- Maintaining business continuity: For industries that rely heavily on OT systems, any disruption can have far-reaching consequences. By implementing robust OT cybersecurity measures, organizations can minimize the risk of downtime, ensuring the continuous operation of their critical processes and maintaining business continuity.
- Protecting sensitive data: OT systems often handle sensitive data such as customer information, intellectual property, and proprietary processes. A successful cyber attack can lead to data breaches, resulting in the loss of valuable information and potential legal and regulatory compliance issues.
- Countering evolving cyber threats: As cyber threats continue to evolve in sophistication and complexity, organizations need to stay one step ahead. Proactively implementing OT cybersecurity measures helps organizations identify and mitigate vulnerabilities and defend against emerging threats.
It is important to recognize that OT cybersecurity is not just an IT problem. It requires collaboration between IT and OT teams, as well as input from industry experts, security professionals, and regulatory bodies. Organizations must develop a holistic approach to cybersecurity that encompasses people, processes, and technology to effectively address the unique challenges faced in the OT environment.
By prioritizing OT cybersecurity, organizations can protect their critical assets, ensure the safety and well-being of the public, and maintain the stability and resilience of essential services that form the backbone of our modern society.
Key Differences between IT and OT Cybersecurity
While both IT (Information Technology) and OT (Operational Technology) encompass cybersecurity, there are significant differences between the two in terms of objectives, environments, and challenges. Understanding these distinctions is crucial for implementing effective cybersecurity measures. Here are some key differences:
- Objectives: The primary objective of IT cybersecurity is to protect data, information systems, and networks from unauthorized access, data breaches, and other cyber threats. On the other hand, the main goal of OT cybersecurity is to safeguard physical processes and critical infrastructure from potential disruptions that can have catastrophic consequences.
- Environments: IT systems exist in traditional office environments, while OT systems are found in operational environments such as power plants, manufacturing facilities, and transportation networks. OT systems are often older, with longer life cycles, and may lack regular updates and patches, making them more susceptible to cyber threats.
- Timing and consequences: In IT systems, security incidents can have immediate consequences, such as data breaches and financial losses. In contrast, OT systems control physical processes that can have real-time impacts on safety, reliability, and public welfare. A cyber attack on an OT system can lead to human injuries, environmental damage, and disruption of critical services.
- Cultural differences: IT and OT departments have different priorities and cultural norms. IT teams are typically more focused on innovation, efficiency, and agility, whereas OT teams prioritize safety, reliability, and maintaining stability. Bridging this cultural gap is critical for effective collaboration and alignment in implementing cybersecurity measures.
- Security controls: IT systems primarily rely on software-based security controls such as firewalls, antivirus software, and encryption. In contrast, OT systems include hardware components such as programmable logic controllers (PLCs) and industrial control systems (ICS), which require a different set of security controls and considerations.
- Legacy systems: OT environments often have legacy systems that have been in operation for many years. These systems may lack built-in security measures and may not be compatible with modern cybersecurity technologies. Securing these legacy systems requires specialized knowledge and expertise.
Addressing the unique challenges of OT cybersecurity requires a specialized approach that considers the criticality and complexity of the systems involved. It necessitates collaboration between IT and OT teams, ensuring that security measures are implemented across the converged IT-OT infrastructure.
By understanding the key differences between IT and OT cybersecurity and tailoring cybersecurity strategies to these specific environments, organizations can better protect their critical assets and ensure the safety and continuity of their operations.
Common OT Cybersecurity Threats
Operational Technology (OT) systems face a wide range of cybersecurity threats that can have severe consequences on critical infrastructure and industrial processes. Understanding these threats is key to implementing effective countermeasures. Here are some of the most common OT cybersecurity threats:
- Malware: Malicious software poses a significant risk to OT systems. Malware can enter the system through various vectors, including infected USB drives, malicious email attachments, or compromised websites. Once inside, malware can disrupt or disable critical processes, steal sensitive information, or enable unauthorized remote access.
- Phishing and social engineering: Phishing attacks target unsuspecting employees to gain access to OT systems. Attackers may impersonate trusted entities or use social engineering techniques to trick employees into revealing sensitive information or providing unauthorized access credentials.
- Insider threats: Insider threats can come from current or former employees, contractors, or vendors with authorized access to OT systems. These individuals may knowingly or unwittingly compromise security by intentionally causing disruptions, stealing data, or inadvertently introducing vulnerabilities.
- Denial of Service (DoS) attacks: DoS attacks aim to overwhelm OT systems with a flood of network traffic, rendering them unable to perform their intended functions. This can lead to system downtime, disruption of critical services, and potential safety hazards.
- Ransomware: Ransomware attacks have become increasingly prevalent in recent years. Once inside an OT system, ransomware encrypts critical files and demands a ransom for their release. The impact of a successful ransomware attack can be significant, leading to operational disruptions and financial losses.
- Zero-day vulnerabilities: A zero-day vulnerability refers to a weakness in a system that is unknown to the vendor or cybersecurity community. Attackers exploit these vulnerabilities to gain unauthorized access to OT systems, often with devastating consequences. Detecting and patching zero-day vulnerabilities is challenging and requires proactive security measures.
- Physical attacks: Physical attacks on OT systems are another significant threat. This can involve unauthorized access to facility premises, tampering with hardware components, or even sabotaging critical infrastructure. Insufficient physical security measures can make OT systems vulnerable to such attacks.
These are just a few examples of the threats that OT systems face; the threat landscape is constantly evolving, and new threats are emerging regularly. Additionally, the convergence of IT and OT systems introduces new attack vectors and complexities that need to be addressed.
To mitigate these threats, organizations must implement a multi-layered approach that includes network segmentation, access controls, regular patch management, employee training and awareness programs, incident response plans, and continuous monitoring for anomalous activities. It is also essential to stay updated on the latest threat intelligence and collaborate with industry peers and cybersecurity experts to share knowledge and best practices.
By understanding and proactively addressing these threats, organizations can enhance the resilience and security of their OT systems, protecting critical infrastructure and minimizing the potential impact of cyber attacks.
Challenges in OT Cybersecurity
Protecting operational technology (OT) systems from cyber threats presents unique challenges that differentiate it from traditional IT cybersecurity. The convergence of IT and OT, the complexity of industrial environments, and the criticality of OT systems create several hurdles in implementing effective OT cybersecurity. Here are some of the key challenges:
- Legacy Systems: Many OT systems run on aging and proprietary technology that predates modern cybersecurity standards. These legacy systems may lack built-in security features or be incompatible with newer security solutions, making it difficult to implement robust cybersecurity measures effectively.
- Availability versus Security: OT systems are designed for high availability and reliability to ensure uninterrupted industrial processes. Adding security controls can sometimes introduce complexities, as security measures may conflict with the need for continuous operation. Finding the right balance between availability and security is a challenge in OT environments.
- Interconnectedness: The interconnection between OT systems and IT networks, combined with the increasing adoption of IoT devices, expands the attack surface and creates potential entry points for cyber attackers. Securing these interconnected systems, particularly when they span multiple locations and include third-party vendors, is a significant challenge.
- Skills Gap: OT cybersecurity requires specialized knowledge and expertise that may not be readily available. Cybersecurity professionals with an understanding of OT systems, protocols, and industry-specific requirements are in high demand. Bridging the skills gap and ensuring sufficient resources and expertise is a challenge for organizations.
- Limited Visibility: OT systems often lack the extensive logging and monitoring capabilities found in IT systems. This limited visibility into network traffic, system events, and user activities makes it challenging to detect and respond to security incidents in a timely manner.
- Regulatory Compliance: Many industries with OT systems are subject to specific regulations and compliance requirements. Ensuring cybersecurity measures align with these regulations, such as NERC CIP for the energy sector, presents additional challenges in OT cybersecurity, as non-compliance can result in severe penalties.
- Culture and Collaboration: The collaboration between OT and IT teams poses cultural and communication challenges. OT and IT departments traditionally have different priorities, mindsets, and approaches. Bridging the cultural gap and establishing effective collaboration channels is crucial for implementing holistic OT cybersecurity strategies.
To overcome these challenges, organizations need to take a comprehensive approach to OT cybersecurity. This includes investing in training and skill development for OT and IT teams, staying updated on industry-specific standards and regulations, conducting regular risk assessments and vulnerability scans, and implementing a defense-in-depth strategy that combines multiple layers of security controls.
Addressing the challenges in OT cybersecurity requires a collaborative effort involving stakeholders from various departments, industry experts, and cybersecurity professionals. By proactively identifying and resolving these challenges, organizations can enhance the resilience and security of their OT systems in the face of evolving cyber threats.
Best Practices for OT Cybersecurity
Implementing effective cybersecurity measures is crucial to protect operational technology (OT) systems from cyber threats. Here are some best practices to enhance OT cybersecurity:
- Network Segmentation: Segregate OT networks from other networks to limit the impact of a potential compromise. Use firewalls and access controls to control communication between different segments.
- Asset Inventory and Risk Assessment: Maintain an inventory of all OT devices and systems to understand vulnerabilities and prioritize security measures. Regularly assess risks to identify and mitigate potential threats.
- Strong Access Controls: Implement strict access controls for OT systems, including strong authentication methods, role-based access controls, and privileged access management. Regularly review and update access privileges as needed.
- Patch Management: Stay up to date with vendor-supplied patches and security updates for OT systems. Implement a robust patch management process to ensure timely and controlled patch deployment.
- Employee Training and Awareness: Provide regular cybersecurity training to all personnel, emphasizing the importance of adhering to security practices and being vigilant against phishing and social engineering attacks.
- Security Monitoring and Incident Response: Deploy intrusion detection systems, security information and event management (SIEM) solutions, and real-time monitoring tools to detect and respond to security incidents promptly. Develop an incident response plan to minimize the impact of cyber attacks.
- Vendor and Supply Chain Management: Assess the cybersecurity practices of third-party vendors and suppliers, ensuring they meet your organization’s security requirements. Include contractual obligations for cybersecurity in vendor agreements.
- Continuous Monitoring and Vulnerability Management: Implement continuous monitoring of OT systems using intrusion detection systems, anomaly detection, and vulnerability scanners. Regularly perform vulnerability assessments and penetration testing to identify and address potential weaknesses.
- Data Backup and Recovery: Regularly back up critical data and establish a robust data recovery plan in the event of a cybersecurity incident. Test backup and recovery systems periodically to ensure their effectiveness.
- Regular Security Audits and Assessments: Conduct periodic security audits and assessments of OT systems to identify areas for improvement and ensure compliance with industry regulations and best practices.
It is important to note that cybersecurity is an ongoing process and should be treated as such. Regularly review and update security practices and technologies to adapt to emerging threats. Establish a culture of cybersecurity awareness throughout the organization and promote a proactive approach to OT cybersecurity.
By implementing these best practices and continually enhancing OT cybersecurity measures, organizations can protect their critical assets, maintain the integrity of their industrial processes, and minimize the risk of devastating cyber attacks on their OT systems.
OT Cybersecurity Tools and Technologies
As the field of OT (Operational Technology) cybersecurity continues to evolve, a variety of tools and technologies have been developed to address the unique challenges faced in securing OT systems. These tools and technologies play a crucial role in monitoring, detecting, and responding to cyber threats. Here are some of the key tools and technologies used in OT cybersecurity:
- Intrusion Detection Systems (IDS): IDS are designed to detect unauthorized access, malicious activities, and anomalous network behavior in real-time. They analyze network traffic, identify potential threats, and trigger alerts to alert security professionals to potential security incidents.
- Security Information and Event Management (SIEM) Systems: SIEM systems collect, analyze, and correlate security event logs from various sources, such as firewalls, intrusion detection systems, and servers. They provide a centralized view of security events, enabling security teams to identify patterns and respond to incidents effectively.
- Vulnerability Scanners: Vulnerability scanners automate the process of identifying vulnerabilities in OT systems. They scan the network, devices, and software for known vulnerabilities and provide reports that highlight areas of weakness, allowing organizations to remediate them before they can be exploited.
- Endpoint Protection: Endpoint protection solutions help secure OT devices and endpoints by providing antivirus, anti-malware, and host-based intrusion prevention capabilities. They protect against known and zero-day threats, ensuring the integrity and availability of critical OT systems and devices.
- Anomaly Detection: Anomaly detection solutions monitor system behavior and network traffic, looking for deviations from normal patterns. Unusual or suspicious activities can indicate an ongoing cyber attack or a potential security breach, enabling organizations to respond promptly to mitigate the impact.
- Network Segmentation Tools: Network segmentation tools help create separate network segments within OT environments. By isolating critical assets and implementing access controls, these tools limit the lateral movement of threats and mitigate the potential impact of a compromised system.
- Encryption Technologies: Encryption technologies play a vital role in protecting the confidentiality and integrity of data transmitted between OT systems. They encrypt data at rest and in transit, ensuring that sensitive information remains secure from unauthorized access.
- Security Orchestration, Automation, and Response (SOAR) Platforms: SOAR platforms streamline incident response by automating security processes, orchestrating workflows, and integrating with various security tools. They help security teams investigate and respond to security incidents efficiently, reducing response times and improving overall incident management.
- Continuous Monitoring Solutions: Continuous monitoring solutions provide real-time visibility into OT systems, networks, and devices. They monitor and analyze network traffic, system logs, and activity data to identify potential security incidents, ensuring timely response and mitigation.
- Security Awareness and Training Platforms: Security awareness and training platforms help organizations educate employees about best practices, policies, and procedures related to OT cybersecurity. They provide interactive training modules, phishing simulations, and other resources to improve the cybersecurity awareness of personnel.
It is important to note that while these tools and technologies can significantly enhance OT cybersecurity, they should be implemented as part of a holistic approach that includes well-defined policies, processes, and skilled cybersecurity personnel. Regular evaluation, updates, and training are essential to ensure the effectiveness of these tools and technologies in safeguarding OT systems.
By leveraging these tools and technologies, organizations can strengthen their defenses, detect threats in real-time, and respond effectively to cybersecurity incidents in their OT environments.
Closing Thoughts
As industries become increasingly reliant on interconnected operational technology (OT) systems, the importance of robust OT cybersecurity cannot be overstated. Securing critical infrastructure and protecting industrial processes from cyber threats is crucial for public safety, business continuity, and the overall stability of our society.
OT cybersecurity presents unique challenges, from legacy systems and cultural differences to the convergence of IT and OT environments. However, by implementing best practices, leveraging advanced tools, and fostering collaboration between IT and OT teams, organizations can effectively mitigate these challenges and enhance their cybersecurity posture.
Continuous monitoring, vulnerability management, and regular risk assessments are essential to identify and remediate vulnerabilities in OT systems. Network segmentation, strict access controls, and employee training play key roles in limiting the impact of potential cyber threats. Implementing advanced technologies such as intrusion detection systems, SIEM, and anomaly detection solutions provides real-time visibility and enables swift incident response.
Additionally, staying informed about emerging cyber threats and compliance regulations in specific industries is crucial. By adapting security practices to the evolving threat landscape and complying with industry-specific standards, organizations can ensure they are adequately protected.
In closing, OT cybersecurity requires a proactive and multifaceted approach that combines technology, processes, and human expertise. It necessitates a strong commitment to ongoing monitoring, assessment, and improvement. By prioritizing OT cybersecurity and implementing best practices, organizations can safeguard critical infrastructure, protect public safety, and maintain the operational integrity of their industrial processes. Let us continue to strive for a safer and more secure digital future.