Introduction
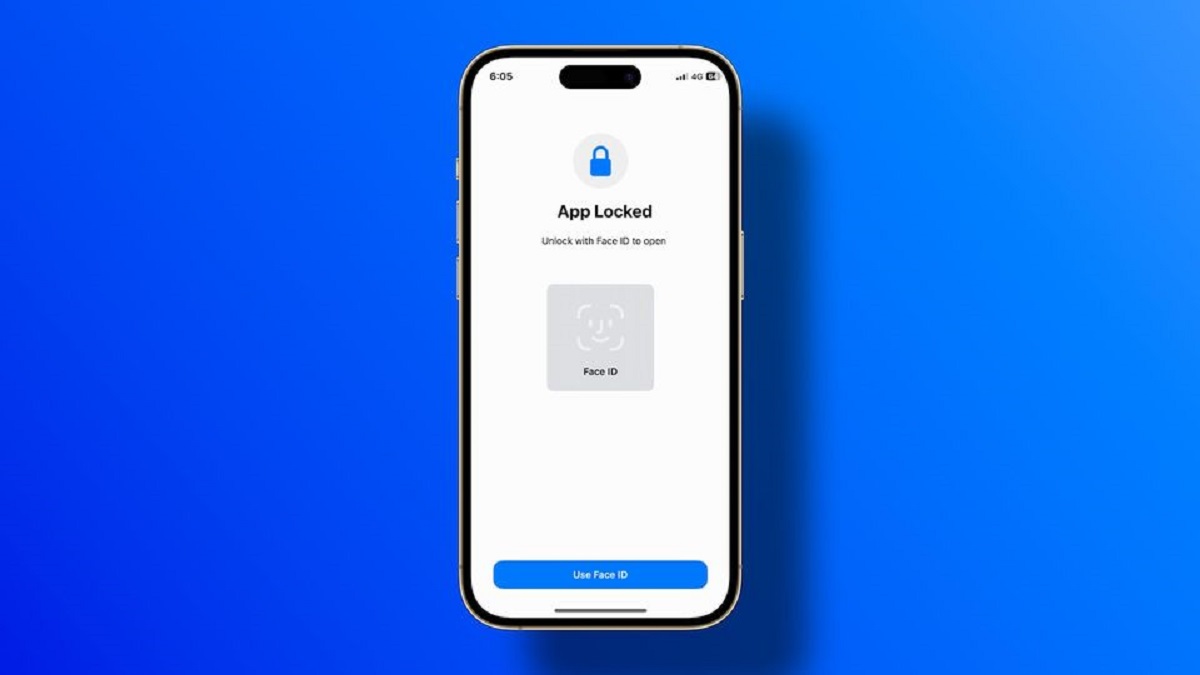
With the increasing prevalence of smartphones and the need for secure access to personal information, biometric authentication methods have become more common. One such method is Face ID, a facial recognition technology developed by Apple for their iPhones and iPads. Unlike traditional passwords or PIN codes, Face ID uses a person’s unique facial features to grant access to their device and sensitive data.
While Face ID provides a convenient and efficient way to unlock devices and authenticate payments, there may be instances where it becomes necessary to find or recover Face ID passwords. This could be due to forgetting the password or needing to gain access to someone’s device for legitimate purposes, such as for troubleshooting or data retrieval.
In this article, we will explore various methods that can be employed to find Face ID passwords. It’s important to note that these methods should only be used in ethical and legal situations, and any information obtained should be handled responsibly and in accordance with applicable laws.
By familiarizing yourself with these techniques, you can potentially regain access to a Face ID-protected device and assist others with their password recovery needs. However, it is crucial to always seek proper authorization and use these methods responsibly.
Why is it important to find Face ID passwords?
Understanding the importance of finding Face ID passwords can help us grasp the significance of the methods discussed in this article. Here are a few reasons why it may be necessary to find Face ID passwords:
1. Device Access: In situations where someone has forgotten their Face ID password, finding it becomes crucial for gaining entry into their device. This is especially important when valuable data, such as personal photos, documents, or important contacts, are stored on the device.
2. Device Recovery: In cases of lost or stolen devices, knowing the Face ID password is key to recovering the device. By finding the password, you can assist the rightful owner in reclaiming their valuable device and minimizing the risk of unauthorized access to their personal information.
3. Troubleshooting: Many users encounter technical issues with their Face ID settings or experience difficulties in unlocking their devices. By finding the Face ID password, you can help troubleshoot and resolve these issues, ensuring that the device functions properly and providing a seamless user experience.
4. Data Transfer: When switching to a new device or performing software updates, transferring data from an existing device is often necessary. By finding the Face ID password, you can ensure a smooth and secure data transfer process, preserving the integrity of the user’s information.
5. Digital Forensics: In certain legal or investigative scenarios, finding Face ID passwords can play a vital role in facilitating digital forensic examinations. This can assist law enforcement agencies or cybersecurity professionals in gathering evidence, investigating cases, and ensuring the safety and security of individuals.
By understanding the importance of finding Face ID passwords, we recognize the need for ethical and responsible approaches to access protected devices. It is crucial to exercise caution and obtain proper authorization before employing any of the methods discussed in this article.
Method 1: Using password hints
One of the simplest and often effective methods to find a Face ID password is by using password hints. Many users provide hints or clues to help them remember their passwords, and these can be valuable in recovering the Face ID password. Here’s how you can use password hints to your advantage:
1. Check device settings: Start by checking the settings of the Face ID-enabled device. Look for any password hints or reminders that the user might have set up. This could include personal information like dates, names, or favorite things that hold significance to the user.
2. Analyze patterns: If you have access to the user’s other devices, analyze their previous passwords to identify any recurring patterns or themes. People often use familiar patterns or variations of their passwords, so pay attention to keywords, numbers, or symbols that might be used in their Face ID password as well.
3. Personal information: Consider the user’s personal information, such as names of family members, pets, or significant dates like birthdays or anniversaries. These details might be used directly or slightly modified to form their Face ID password. Use your knowledge of their preferences and personal history to make educated guesses.
4. Common passwords: Familiarize yourself with common passwords that people often use, such as “password123,” “123456,” or “qwerty.” While these might seem obvious, many users still choose weak passwords. Try these common passwords with slight variations or combinations to see if they match the Face ID password.
5. Social media: Gather as much information as possible from the user’s social media profiles. Likes, comments, and personal interactions might contain clues about their interests and preferences that could be utilized in guessing their Face ID password. Be cautious not to infringe on their privacy or engage in any unauthorized activities.
Remember, the use of password hints should always be ethical and done with the user’s consent or in situations where legal access to the device is granted. It is crucial to respect privacy and follow the appropriate legal and ethical guidelines when attempting to find Face ID passwords using password hints.
Method 2: Utilizing social engineering techniques
Social engineering is the art of manipulating individuals to disclose sensitive information or grant unauthorized access. When it comes to finding Face ID passwords, social engineering can be a powerful tool. Here are some techniques you can use:
1. Establish trust: Gain the target’s trust by impersonating a trusted party, such as a support technician or a friend. Engage in friendly conversation and create a comfortable environment that encourages them to share their Face ID password.
2. Pretexting: Create a plausible pretext or scenario that requires the person to reveal their Face ID password. For example, posing as an app developer in need of testing, you can ask the individual to temporarily share their password for debugging purposes.
3. Phishing: Phishing involves sending fraudulent emails or messages that appear legitimate in order to trick individuals into revealing their sensitive information like passwords. Craft a convincing email or message that prompts the target to provide their Face ID password unknowingly.
4. Impersonation: Impersonate someone the target knows and trusts, such as a family member or coworker, and request their Face ID password for a seemingly legitimate reason. Ensure that you are familiar with the impersonated person’s personal details and mannerisms to enhance credibility.
5. Observation and manipulation: Observe the target’s behaviors and habits, such as the way they enter their password or the time they usually unlock their device. Use this information to subtly influence them into revealing their Face ID password without arousing suspicion.
It’s important to note that social engineering techniques should always be used ethically and with proper authorization. This means obtaining consent from the individual or verifying that you have the legal authority to access their device. Unlawful and unauthorized use of social engineering techniques can have serious legal consequences.
Due to the potential for abuse and harm, it is vital to approach social engineering techniques responsibly and with integrity. Always prioritize ethical considerations and ensure that you are operating within the boundaries of the law when attempting to find Face ID passwords through social engineering.
Method 3: Accessing stored passwords on connected devices
Another method to find Face ID passwords is by accessing stored passwords on connected devices. Many users choose to save their passwords on their devices, allowing for automatic logins and ease of use. Here’s how you can utilize this method:
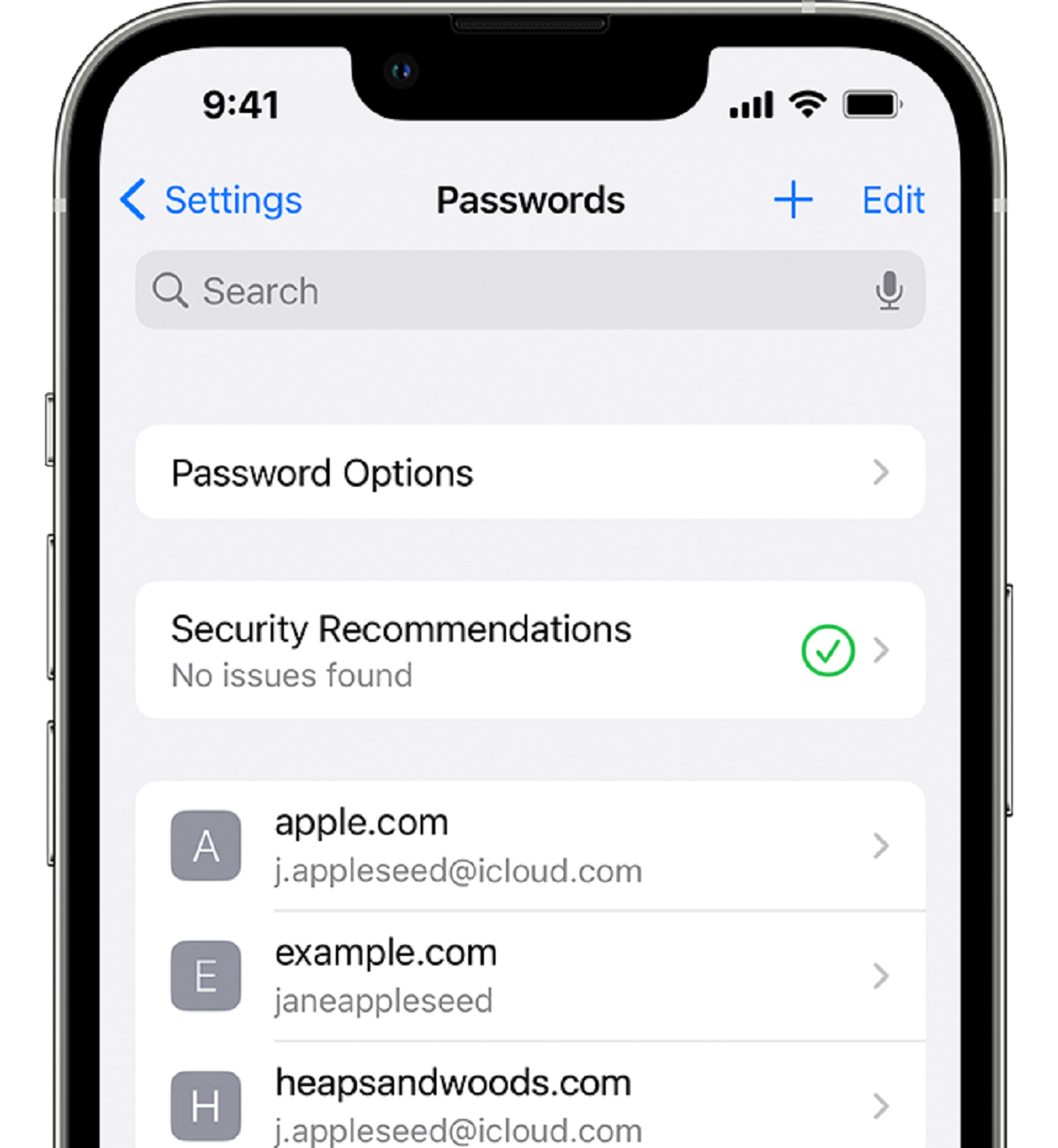
1. Synced devices: If the user has multiple devices connected to the same iCloud or Google account, check if their Face ID password is synced across these devices. This can include iPhones, iPads, Macs, or other compatible devices. Accessing the password on one connected device may provide the necessary information to unlock the Face ID-protected device.
2. Keychain access: On Mac devices, the Keychain Access utility stores passwords and other sensitive information. If the user has allowed iCloud Keychain, you can utilize this utility to access the Face ID password or any other passwords associated with their accounts.
3. Third-party password managers: Many users rely on third-party password management applications like LastPass, Dashlane, or 1Password to store their passwords securely. If the person has installed such an application and granted access, you may be able to find the Face ID password stored within the password manager.
4. Browser password managers: Web browsers often have built-in password managers that save login credentials for various websites. Check the browser settings to see if any stored passwords can be accessed. These passwords might include the Face ID password if it has been saved for automatic login on certain websites or apps.
5. Shared networks: If the device is connected to a shared network, such as a Wi-Fi network or a work network, there might be network administrators who have the ability to access stored passwords on connected devices. In these instances, seeking permission from the network administrator is essential before attempting to find Face ID passwords using this method.
It’s crucial to approach this method ethically and responsibly. Always ensure that you have proper authorization or consent from the owner before accessing their stored passwords on connected devices. Respecting privacy and following legal guidelines is paramount to maintain trust and integrity.
Method 4: Exploiting password recovery options
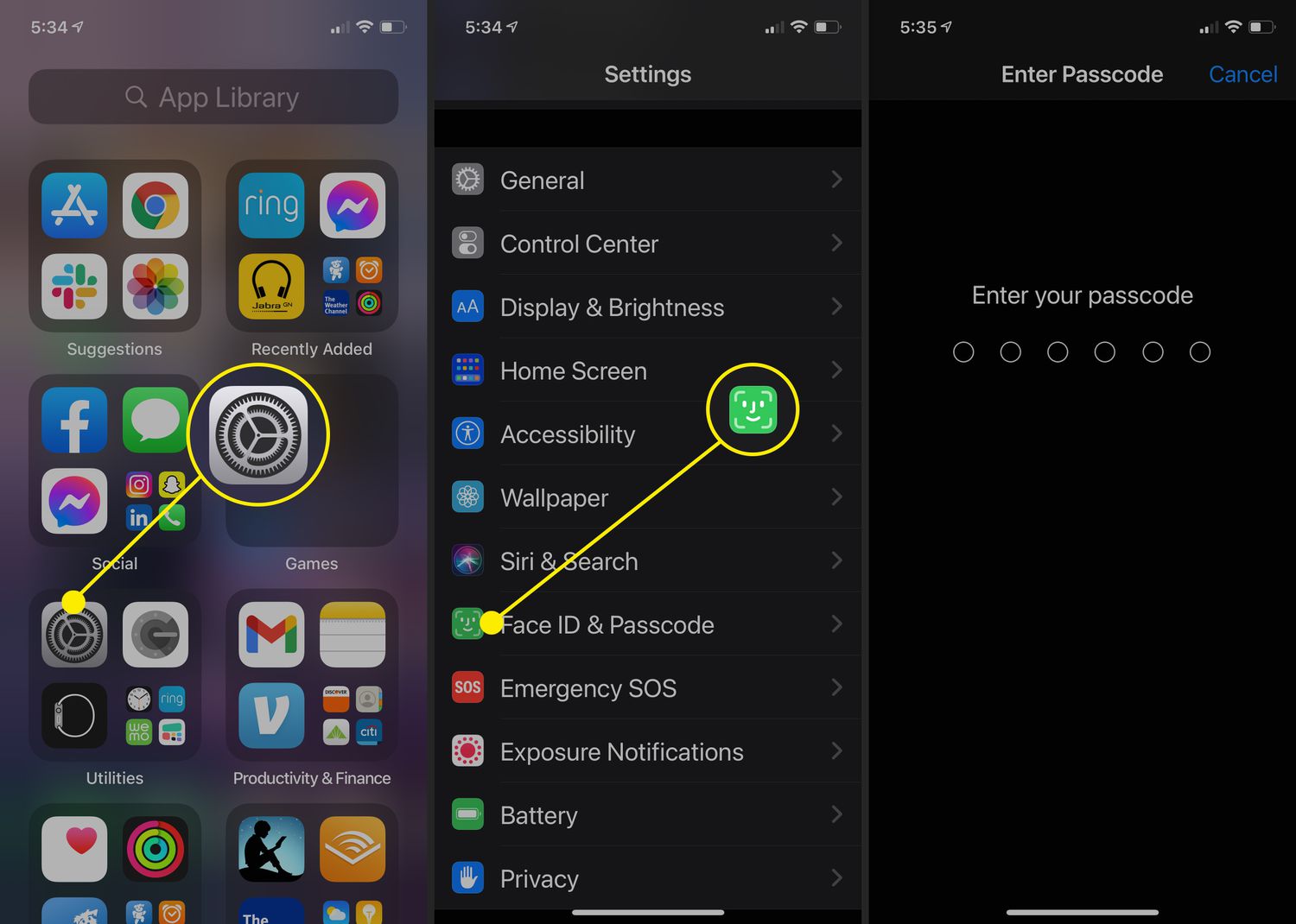
Exploiting password recovery options is another method that can be used to find Face ID passwords. When users forget their passwords, they often rely on various recovery options provided by device manufacturers or service providers. Here’s how you can leverage these options:
1. Security questions: Most password recovery processes involve security questions set up by the user. If you have access to the user’s personal information, such as their email address, phone number, or social media profiles, you may be able to guess or find answers to their security questions. This can provide a pathway to recovering their Face ID password.
2. Email and SMS recovery: Many password recovery mechanisms involve sending a reset link or verification code to the user’s email or phone. If you have access to their email account or can intercept their SMS messages, you may be able to initiate the password recovery process and ultimately find their Face ID password.
3. Account recovery with service providers: Some service providers, such as Apple or Google, offer account recovery options that involve verifying personal information, previous purchases, or device details. By gathering information about the user’s account and device, you may be able to successfully recover their Face ID password through these channels.
4. Two-factor authentication: If the user has enabled two-factor authentication on their account, there may be alternative methods for password recovery. This can include using backup codes, secondary devices, or contacting the service provider for assistance. By understanding their two-factor authentication setup, you may be able to recover their Face ID password.
5. Device manufacturer support: Contacting the device manufacturer’s support service can sometimes provide insights or assistance in recovering a Face ID password. Provide them with relevant details and proof of ownership to determine if they can help you through their official support channels.
It is essential to note that exploiting password recovery options should only be done with proper authorization or with the user’s consent. Attempting to bypass security measures without permission is illegal and unethical. Always respect the user’s privacy and follow appropriate legal and ethical guidelines when using this method to find Face ID passwords.
Method 5: Employing password cracking software
When other methods fail, employing password cracking software can be a last resort to find Face ID passwords. Password cracking software utilizes various techniques, including brute-force attacks and dictionary attacks, to systematically guess passwords. Here’s how this method can be used:
1. Brute-force attacks: Brute-force attacks involve trying every possible combination of characters until the correct password is found. Password cracking software can systematically generate and test millions or even billions of password combinations within a short period. This method can be time-consuming and resource-intensive, especially if the password is complex or lengthy.
2. Dictionary attacks: Dictionary attacks rely on pre-existing wordlists or dictionaries to guess passwords. The software systematically tests each word in the dictionary against the Face ID password. This method is more efficient than brute-force attacks, as it eliminates the need to try all possible combinations. However, it is less effective against complex or unique passwords.
3. Hybrid attacks: Hybrid attacks combine elements of both brute-force and dictionary attacks. Password cracking software can employ techniques such as adding numbers or symbols to words from a dictionary to create additional password variations. This strategy aims to increase the chances of finding the correct Face ID password while maximizing efficiency.
4. GPU acceleration: Password cracking software often utilizes the processing power of Graphics Processing Units (GPUs) to accelerate the cracking process. GPUs can perform multiple calculations simultaneously, significantly speeding up the password cracking process. This is particularly useful when dealing with complex passwords or large wordlists.
5. Rainbow table attacks: Rainbow tables are precomputed tables used to hash common passwords, reducing the time needed to crack them. Password cracking software can utilize rainbow tables to quickly retrieve the original Face ID password from its hashed form. However, this method is less effective against unique or less common passwords.
It is important to note that employing password cracking software can have legal and ethical implications. Unauthorized use of such software or attempting to crack someone’s Face ID password without their consent is illegal. Always ensure that you have proper authorization or consent to use password cracking software, and abide by the applicable laws and ethical guidelines.
Furthermore, it’s worth mentioning that modern security measures, such as strong encryption and frequent password hashing, can significantly increase the difficulty of cracking Face ID passwords. As a result, utilizing password cracking software may not always guarantee success.
Ensuring security and ethical considerations
When attempting to find Face ID passwords, it is crucial to prioritize security and adhere to ethical considerations. Here are some key points to keep in mind:
1. Seek proper authorization: Always obtain proper authorization from the device owner before attempting to find their Face ID password. This ensures that you are acting within legal boundaries and respecting the individual’s privacy and consent.
2. Respect privacy: Respect the privacy of the device owner throughout the process. Avoid accessing or sharing any personal or sensitive information obtained during your efforts to find the Face ID password. Ensure that you handle any data securely and delete it once you have completed your task.
3. Follow legal guidelines: Adhere to applicable laws and regulations when attempting to find Face ID passwords. Understand the legal boundaries related to password recovery, personal data protection, and unauthorized access to electronic devices. Violating these laws can lead to serious legal consequences.
4. Use ethical practices: Employ ethical practices throughout the process. Do not engage in malicious activities, exploit vulnerabilities for personal gain, or engage in unauthorized actions. Always act in a manner that upholds integrity and respects the rights and well-being of others.
5. Consent and disclosure: Transparently communicate your intentions and obtain consent from the device owner when possible. Clearly explain why you need to find their Face ID password, what steps you will be taking, and what information may be accessed. Transparency and open communication build trust and ensure that everyone involved understands the process.
6. Data protection: Safeguard any data or information obtained during the process. Handle it responsibly and securely, ensuring that it is protected from unauthorized access or disclosure. Dispose of any unnecessary data promptly and ensure compliance with relevant data protection regulations.
7. Share responsibly: If you discover any vulnerabilities or weaknesses in the Face ID system or other security mechanisms, handle this information responsibly. Report it to the appropriate authorities or device manufacturers in a responsible and timely manner, allowing them to address the issue and improve security for everyone.
By considering these security and ethical considerations, you can improve the overall integrity of the process of finding Face ID passwords. Always prioritize the security and privacy of device owners and conduct your activities in a responsible and lawful manner.
Conclusion
Finding Face ID passwords can be a challenging and complex task, requiring a careful balance of technical knowledge, ethical considerations, and legal boundaries. While the methods discussed in this article can be effective in certain situations, it’s important to approach them with caution, integrity, and respect for privacy.
Whether it’s utilizing password hints, employing social engineering techniques, accessing stored passwords on connected devices, exploiting password recovery options, or using password cracking software, it’s vital to always seek proper authorization and adhere to applicable laws. These methods should only be used in ethical and legal circumstances, and any information obtained during the process should be handled responsibly and securely.
Ensuring security and ethical considerations is paramount. Seek consent from the device owner, respect their privacy, and protect any data or information obtained. Follow legal guidelines and handle vulnerabilities responsibly by reporting them to the appropriate authorities. By doing so, we contribute to maintaining trust, integrity, and the overall security of the digital ecosystem.
Remember, the ultimate goal is not just to find Face ID passwords, but also to contribute to a safer and more responsible digital world. Prioritize ethical practices, respect privacy, and use the knowledge gained from these methods responsibly and for legitimate purposes.
By understanding the importance of finding Face ID passwords, being aware of the various methods available, and considering security and ethical implications, we can navigate this process with integrity and safeguard the privacy and security of individuals and their devices.