Introduction
In today’s digital age, data security has become a paramount concern. With the increasing reliance on solid-state drives (SSDs) for storage, protecting sensitive information has become more crucial than ever. SSD encryption provides a robust solution to safeguard your data from unauthorized access or theft.
SSD encryption refers to the process of encoding data stored on an SSD, making it unreadable to anyone without the decryption key. By implementing encryption, you can ensure that even if your SSD falls into the wrong hands, the data will remain secure. Encryption adds an additional layer of protection on top of traditional password-based access controls.
The benefits of encrypting your SSD go beyond just securing your data. It also helps organizations comply with data privacy regulations such as the General Data Protection Regulation (GDPR) and ensures that personal and confidential information remains confidential.
Determining whether your SSD is already encrypted is an important consideration. Some SSDs come with built-in hardware encryption, while others require software-based encryption. Knowing the encryption status of your SSD will guide you in choosing the appropriate method for securing your data.
Before embarking on the SSD encryption process, there are a few precautions to keep in mind. Backing up your data is vital in case any issues arise during the encryption process. Additionally, understanding the different methods of encryption and the available software and hardware options will enable you to make an informed decision.
This article will guide you through the steps involved in encrypting your SSD and provide insights into the various software and hardware solutions available. It will also outline best practices for managing encrypted SSDs to ensure data security and integrity.
By the end of this article, you will have a clear understanding of SSD encryption, its benefits, and the necessary steps to protect your data effectively.
What is SSD encryption?
SSD encryption is a method of protecting data stored on solid-state drives (SSDs) by encoding it in such a way that only authorized users with the decryption key can access and decipher the information. It provides a layer of security that prevents unauthorized individuals or entities from reading or tampering with sensitive data.
Unlike traditional hard disk drives (HDDs), SSDs use flash memory to store data. This makes them faster and more efficient but also presents certain security concerns. If an SSD is stolen or falls into the wrong hands, the sensitive data stored on it could be easily accessed, potentially leading to identity theft, financial loss, or other serious consequences.
SSD encryption can be implemented through two main methods: hardware-based encryption and software-based encryption.
Hardware-based encryption: Some SSDs have built-in encryption capabilities, making use of a dedicated encryption chip present on the drive’s circuit board. This hardware encryption ensures that all data written to the SSD is automatically encrypted in real-time and decrypted when accessed by authorized users. This method offers a high level of security, as the encryption process is performed directly on the SSD, independent of the host system.
Software-based encryption: If your SSD does not have built-in hardware encryption, you can utilize software-based encryption solutions. These involve using encryption software to encrypt the data before it is written to the SSD. The encryption software utilizes various encryption algorithms, such as Advanced Encryption Standard (AES), to convert the data into an unreadable format. When the data needs to be accessed, the software decrypts it using the encryption key.
It is important to note that SSD encryption operates on a block-level, meaning that individual blocks of data are encrypted and decrypted as needed, rather than the entire drive being encrypted at once. This allows for faster access to specific data blocks and reduces the performance impact typically associated with full-drive encryption.
Whether you are an individual user or a business organization, implementing SSD encryption is essential for protecting sensitive and confidential information. By encrypting your SSD, you add an extra layer of security that ensures your data remains secure, even if the physical drive is compromised.
In the next sections, we will explore the benefits of SSD encryption and guide you through the process of determining if your SSD is already encrypted.
Benefits of encrypting SSD
Encrypting your SSD provides several important benefits that enhance data security and protect sensitive information. Let’s explore some of the key advantages:
1. Data Protection: The primary benefit of SSD encryption is the protection it offers to your data. By encrypting the information stored on the drive, you create a barrier that prevents unauthorized individuals from accessing or understanding the data even if the drive is stolen or lost. This is particularly crucial for sensitive personal data, financial information, and confidential business data.
2. Compliance with Data Privacy Regulations: Many industries and jurisdictions have specific regulations regarding data privacy and security. Encrypting your SSD helps ensure compliance with these regulations, such as the General Data Protection Regulation (GDPR) in Europe or the Health Insurance Portability and Accountability Act (HIPAA) in the United States. Compliance with these regulations not only avoids hefty fines and legal consequences but also instills trust in your customers and stakeholders.
3. Prevention of Data Breaches and Identity Theft: By encrypting your SSD, you significantly reduce the risk of data breaches and identity theft. If your SSD is lost, stolen, or hacked, the encrypted data remains inaccessible, providing an extra layer of protection against unauthorized access. This is especially crucial for mobile devices like laptops, tablets, and smartphones that contain sensitive personal and business information.
4. Peace of Mind: Encrypting your SSD provides peace of mind. Knowing that your data is secured and protected, even in worst-case scenarios, relieves the anxiety associated with data breaches and potential misuse of personal or sensitive information. This peace of mind extends to both personal users and business entities, knowing that their data and the data of their clients is safeguarded.
5. Seamless Integration into Existing Security Infrastructure: SSD encryption solutions are designed to seamlessly integrate into existing IT security systems and infrastructure. With hardware-based encryption, the encryption process is transparent to the operating system, applications, and users. Software-based encryption solutions often come with user-friendly interfaces that allow for easy integration and management within your existing environment.
6. Performance Impact Mitigation: Unlike traditional full-drive encryption methods, SSD encryption typically operates on a block-level, minimizing the performance impact on the drive’s read and write operations. This ensures that the encryption process does not sacrifice the speed and performance advantages that SSDs offer.
By encrypting your SSD, you enhance data security, protect sensitive information, and ensure compliance with data privacy regulations. The benefits of SSD encryption extend to individuals and businesses alike, providing peace of mind and effective protection against data breaches and identity theft. In the next section, we will discuss how to determine if your SSD is already encrypted.
How to determine if your SSD is already encrypted
Before proceeding with the SSD encryption process, it is crucial to determine whether your SSD is already encrypted. Understanding the encryption status of your SSD will guide you in choosing the appropriate method to secure your data. Here are a few methods to help you determine if your SSD is already encrypted:
1. Check manufacturer specifications: Start by researching the specifications and documentation provided by the manufacturer of your SSD. Look for information regarding encryption features or hardware encryption support. Some manufacturers explicitly mention whether their SSD models come with built-in encryption capabilities.
2. Review the BIOS or UEFI settings: Access the BIOS or UEFI settings on your computer and navigate to the SSD-related options. Look for any settings related to encryption or security features. Depending on the SSD and motherboard manufacturer, these options may be labeled differently. Look for terms such as “encryption,” “security,” or “encryption support.”
3. Consult your operating system: Some operating systems, such as Windows and macOS, provide tools that can help you determine if your SSD is encrypted. In Windows, open the BitLocker Drive Encryption settings and check if your SSD is listed and if encryption is active. In macOS, navigate to the System Preferences, select Security & Privacy, and check the FileVault section for SSD encryption status.
4. Utilize third-party software: Several third-party software tools can detect and analyze the encryption status of your SSD. These tools often provide comprehensive information about your SSD, including encryption support and status. Some popular options include CrystalDiskInfo, SSD Life, and SSD Utility.
5. Consult your device manufacturer or IT department: If you are using a company-provided device, reach out to your device manufacturer or IT department for information on SSD encryption. They will be able to provide specific details about the encryption features and status of your SSD.
Remember that it is possible for different SSD models or versions from the same manufacturer to have different encryption capabilities. Therefore, it is essential to verify the encryption status of your specific SSD model.
By determining the encryption status of your SSD, you can make informed decisions regarding the next steps in securing your data. If your SSD is not already encrypted, you can proceed with implementing encryption using either software-based or hardware-based encryption methods. In the following sections, we will discuss precautions to consider before encrypting your SSD and provide step-by-step instructions for encrypting your SSD.
Precautions before encrypting your SSD
Before embarking on the process of encrypting your SSD, it is important to take certain precautions to ensure a smooth and successful encryption process. These precautions help minimize any potential risks and ensure that your data remains safe throughout the encryption process. Here are some essential precautions to consider:
1. Backup your data: Before initiating the encryption process, it is crucial to backup all important data stored on your SSD. Although encryption aims to protect your data, there is always a slight possibility of issues arising during the encryption process. Having a backup ensures that you can recover any lost or inaccessible data in case of any unforeseen circumstances.
2. Update your SSD firmware: It is recommended to update your SSD firmware to the latest version provided by the manufacturer. Firmware updates often include performance improvements, bug fixes, and security enhancements, ensuring that your SSD is operating optimally and securely. Check the manufacturer’s website for firmware updates specific to your SSD model.
3. Check for compatibility: If you plan to use software-based encryption, verify that your operating system and encryption software are compatible with your SSD. Not all SSD models or encryption software may be supported on every operating system. Checking compatibility beforehand helps avoid any potential issues or compatibility conflicts during the encryption process.
4. Allocate sufficient time for encryption: SSD encryption can take a significant amount of time, depending on the size of your SSD and the encryption method used. It is important to allocate enough time for the encryption process to complete. Interruptions or halting the encryption process midway may result in data corruption or loss.
5. Store your encryption key securely: When encrypting your SSD, you will usually be prompted to create an encryption key or passphrase. It is crucial to store this key securely, preferably in multiple locations. Losing the encryption key may result in permanent data loss, as it is nearly impossible to decrypt the data without it. Consider using a password manager or a hardware-encrypted USB drive to store your encryption key securely.
6. Test your backups: Before initiating the encryption process, test the integrity of your backups to ensure that you can successfully restore your data if needed. This helps verify that the backup is complete and that the data is accessible and intact.
By taking these precautions, you can minimize the risks associated with the SSD encryption process and ensure that your data remains protected throughout. Once you have implemented these precautions, you can proceed confidently with encrypting your SSD, safeguarding your sensitive information from unauthorized access. In the next section, we will provide step-by-step instructions for encrypting your SSD.
Steps to encrypt SSD
Encrypting your SSD is a straightforward process that can be accomplished through software-based or hardware-based encryption methods. The specific steps may vary slightly depending on your operating system and encryption software. Here is a general guide to encrypting your SSD:
Step 1: Prepare your SSD: Ensure that your SSD is connected and recognized by your computer. Make sure that you have completed the necessary precautions, such as backing up your data and updating your SSD firmware, as discussed in the previous sections.
Step 2: Choose an encryption method: Decide whether you will be using software-based or hardware-based encryption. If your SSD supports hardware-based encryption, you may opt for that method for enhanced security and performance. Otherwise, you can choose a software-based encryption solution.
Step 3: Install encryption software: If you are opting for software-based encryption, download and install the encryption software of your choice that is compatible with your operating system. Popular software options include VeraCrypt, BitLocker (Windows), and FileVault (macOS).
Step 4: Launch the encryption software: Open the encryption software and navigate to the SSD encryption section. Depending on the software, you may find this under drive encryption, encryption options, or security settings.
Step 5: Select your SSD for encryption: Choose your SSD from the list of available drives within the encryption software. Ensure that you have selected the correct SSD to avoid encrypting the wrong drive.
Step 6: Set encryption parameters: Configure the encryption parameters according to your preferences. This may include selecting the encryption algorithm (e.g., AES-256), setting an encryption key or passphrase, and defining any additional security options. Follow the prompts provided by the encryption software to input the required information.
Step 7: Start the encryption process: Once you have set the encryption parameters, initiate the encryption process. This may involve clicking on an “Encrypt” or “Start” button within the encryption software. The encryption process may take some time, depending on the size of your SSD and the encryption method used.
Step 8: Monitor the encryption progress: It is advisable to keep an eye on the encryption progress to ensure that it completes successfully. Some encryption software provides a progress indicator or a percentage completion status. Do not interrupt or shut down your computer during the encryption process.
Step 9: Completion and verification: Once the encryption process is complete, the software will notify you. At this point, your SSD is successfully encrypted and protected. Verify that you can access your data and that the encryption is functioning as intended.
It is important to note that the specific steps and options may vary depending on the software and operating system you are using. Consult the documentation and user guides provided with your encryption software for detailed instructions and any additional considerations specific to your setup.
By following these steps, you can encrypt your SSD and protect your data from unauthorized access. The encryption process adds an extra layer of security, ensuring the confidentiality and integrity of your sensitive information. In the next sections, we will explore software and hardware options for SSD encryption and provide best practices for managing encrypted SSDs.
Software options for SSD encryption
When it comes to encrypting your SSD, there are several software options available that offer reliable encryption solutions. These software tools provide a user-friendly interface and a range of features to encrypt and protect your data. Let’s explore some popular software options for SSD encryption:
1. VeraCrypt: VeraCrypt is a free open-source encryption software that is highly regarded for its strong security features. It provides on-the-fly encryption, meaning that data is automatically encrypted as it is written to the SSD and decrypted when accessed by authorized users. VeraCrypt supports various encryption algorithms, including AES, Serpent, and Twofish, and allows you to create encrypted volumes, encrypt entire partitions, or even encrypt entire operating systems.
2. BitLocker (Windows): BitLocker is a built-in encryption feature in Windows operating systems that provides native encryption for SSDs. It offers both software-based encryption and hardware-based encryption (if your SSD supports it). BitLocker integrates seamlessly with Windows and provides easy-to-use encryption options, such as encryption of individual files and folders or entire drives. It supports the widely-used AES encryption algorithm and allows for the use of Trusted Platform Modules (TPMs) for enhanced security.
3. FileVault (macOS): FileVault is the built-in encryption tool provided by Apple for macOS. It allows you to encrypt the entire contents of your SSD, providing robust protection for your data. FileVault uses the secure XTS-AES-128 encryption with a 256-bit key, ensuring high-level security. Setting up FileVault is straightforward, and it integrates seamlessly with your macOS user account and system settings. It also supports the use of personal recovery keys, making it easier to regain access to your encrypted SSD if needed.
4. Bitdefender GravityZone Full Disk Encryption: Bitdefender GravityZone Full Disk Encryption is a comprehensive encryption solution suitable for both individual users and businesses. It offers a range of encryption features, including full-disk encryption for SSDs, file and folder encryption, and removable media encryption. Bitdefender GravityZone uses the AES-256 encryption algorithm and provides centralized management capabilities for easy deployment and administration across multiple devices and endpoints.
5. Symantec Endpoint Encryption: Symantec Endpoint Encryption is a robust encryption solution designed for enterprise environments. It offers full-disk encryption, removable media encryption, and file and folder encryption, ensuring comprehensive data protection. Symantec Endpoint Encryption supports SSDs and utilizes strong encryption algorithms, such as AES-256 and RSA. It provides centralized management features, allowing IT administrators to efficiently manage and enforce encryption policies across the organization.
These are just a few examples of software options available for encrypting your SSD. It is important to evaluate the features, compatibility, and ease of use when choosing the right software for your specific needs. Consult the documentation and user guides provided with the software to ensure proper installation, configuration, and usage.
Remember that each software option may have specific system requirements and compatibility considerations. It is crucial to verify the compatibility of the software with your operating system, SSD, and any other components of your system before proceeding with the encryption process.
In the next section, we will explore hardware options for SSD encryption, offering an alternative to software-based encryption.
Hardware options for SSD encryption
In addition to software-based encryption solutions, there are hardware options available for encrypting your SSD. Hardware-based encryption provides an additional layer of security and can offer faster encryption and decryption speeds. Let’s explore some popular hardware options for SSD encryption:
1. Self-Encrypting Drives (SEDs): Self-Encrypting Drives (SEDs) are SSDs that have built-in hardware encryption capabilities. These drives feature an encryption chip on the drive’s circuit board that performs real-time encryption and decryption of data without impacting performance. SEDs utilize encryption keys stored on the drive itself, ensuring that the data remains encrypted even if the drive is removed from the system. SEDs often support trusted computing features, such as Trusted Platform Modules (TPMs) and Opal specifications, to further enhance security.
2. Solid-State Drive with Hardware Encryption: Some SSD models come with hardware encryption support integrated into the drive, but they may require additional software or drivers to enable and manage the encryption features. These drives typically offer high-performance encryption and decryption capabilities, making them an excellent option for users who require both speed and security. It is important to ensure compatibility with your operating system and confirm that the drive’s encryption features meet your specific requirements.
3. External Hardware Encryption Devices: External hardware encryption devices are standalone devices that connect between your computer and your SSD. These devices act as intermediaries, encrypting and decrypting data going to and from the SSD. They often offer additional features such as password authentication, key management, and secure data wiping. External hardware encryption devices provide an extra layer of security and are a suitable option for users who want to encrypt their SSD without relying on built-in encryption features.
4. Hardware Security Modules (HSMs): Hardware Security Modules (HSMs) are dedicated hardware devices used for cryptographic operations, including encryption and decryption. While not specifically designed for SSD encryption, HSMs can be utilized to enhance the security of your encryption keys and provide a secure environment for performing encryption operations. HSMs are commonly used in enterprise environments where robust security and compliance requirements are mandated.
5. Trusted Platform Module (TPM): Trusted Platform Modules (TPMs) are hardware chips integrated into certain computer systems that provide secure storage and management of encryption keys, among other security functions. While TPMs do not directly encrypt the SSD, they can be used in conjunction with software-based or hardware-based encryption solutions to enhance security by securely storing and managing encryption keys.
When considering hardware options for SSD encryption, it is important to research and select products that are compatible with your specific SSD model and meet your security requirements. Consult the manufacturer’s documentation and user guides to ensure proper installation and configuration of the hardware encryption solution.
Hardware-based encryption offers a level of security that is independent of the host system and can provide faster encryption and decryption speeds. However, it is essential to evaluate the compatibility, cost, and features of the hardware solution before making a decision.
In the next section, we will discuss best practices for managing encrypted SSDs, ensuring the continued security and integrity of your data.
Best practices for managing encrypted SSDs
Managing encrypted SSDs involves implementing certain best practices to ensure the continued security and integrity of your data. Following these practices will help you effectively manage and maintain your encrypted SSDs. Here are some key best practices to consider:
1. Regularly update encryption software and firmware: Keep your encryption software and SSD firmware up to date. Software and firmware updates often include security patches and improvements, ensuring that your encrypted SSD remains protected against emerging threats. Check for updates regularly and apply them as soon as they become available.
2. Safely store and backup encryption keys: Store your encryption keys securely and back them up in multiple locations. If you lose the encryption keys, you may permanently lose access to your encrypted data. Consider using a dedicated password manager or hardware-encrypted USB drives to securely store and manage your encryption keys.
3. Implement strong passwords and authentication methods: Use strong and unique passwords for your SSD encryption software and operating system. Additionally, consider enabling multi-factor authentication (MFA) methods, such as biometrics or hardware tokens, to further enhance the security of your encrypted SSD. Strong passwords and MFA protect against unauthorized access to your encrypted data.
4. Regularly back up your encrypted data: Backing up your encrypted data ensures that you have a copy of your data in case of any unforeseen circumstances, such as hardware failure or data corruption. Regularly schedule backups to a separate and secure location, ensuring the integrity and availability of your encrypted data at all times.
5. Maintain an inventory of encrypted SSDs: Create and maintain an inventory of your encrypted SSDs. Keep track of the specific SSD models, encryption methods used, encryption keys, and any relevant information associated with each encrypted SSD. This inventory helps in managing and tracking your encrypted SSDs, especially in a business or organizational setting.
6. Educate users on best practices: Provide training and educate users on best practices for managing and using encrypted SSDs. This includes password security, recognizing phishing attempts, and ensuring proper protocols are followed when accessing and using encrypted data. User awareness plays a vital role in maintaining the security of your encrypted SSDs.
7. Perform regular system and security audits: Conduct regular audits of your systems and security practices to identify any vulnerabilities or weaknesses. This includes reviewing access controls, encryption configurations, and encryption key management practices. Regular audits help ensure that your encrypted SSDs are properly secured and aligned with industry best practices.
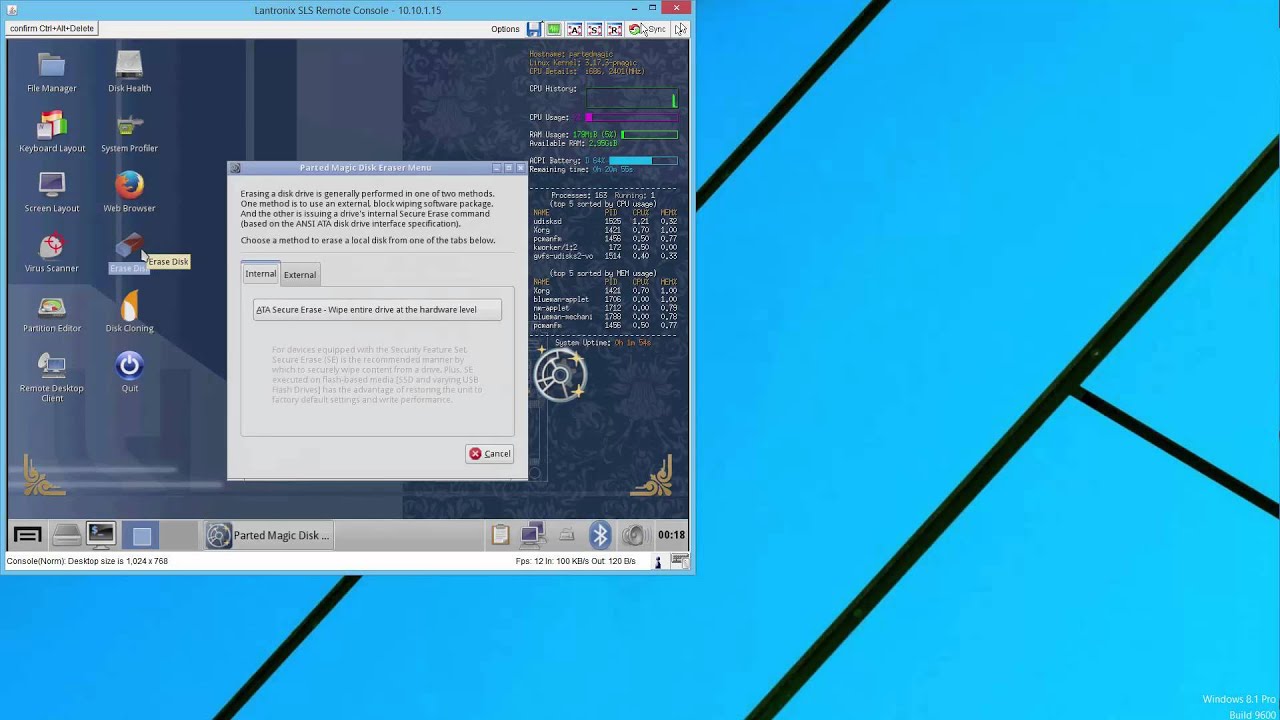
8. Implement data disposal and secure erasure protocols: When it comes time to retire or dispose of an encrypted SSD, employ secure data disposal protocols. This may involve permanently erasing the data using secure erasure methods or physically destroying the drive to ensure data cannot be recovered. Proper disposal ensures that sensitive information remains protected even after the SSD is no longer in use.
By adhering to these best practices, you can effectively manage and secure your encrypted SSDs, minimizing the risk of data breaches and ensuring the ongoing protection of your sensitive information. Remember, data security is a continual process, and regular maintenance and adherence to best practices are essential.
In the concluding section, we will summarize the key points discussed and emphasize the importance of implementing SSD encryption to ensure data security in today’s digital landscape.
Conclusion
Encrypting your solid-state drive (SSD) is a crucial step in securing your data and protecting sensitive information. Whether you opt for software-based encryption or leverage the hardware-based capabilities of your SSD, encryption provides an additional layer of security that prevents unauthorized access and safeguards your data from theft or misuse.
Throughout this article, we explored the concept of SSD encryption, its benefits, and the steps involved in encrypting your SSD. We learned about the different encryption methods, such as hardware-based encryption and software-based encryption, and discussed popular software and hardware options available for implementing SSD encryption.
By encrypting your SSD, you not only protect your data from unauthorized access but also demonstrate compliance with data privacy regulations. The benefits of SSD encryption go beyond just data protection; it offers peace of mind, helps prevent data breaches and identity theft, and seamlessly integrates into your existing security infrastructure.
Before encrypting your SSD, it is important to take precautions such as backing up your data, updating SSD firmware, and verifying compatibility with your operating system. Following these precautions ensures a smooth and successful encryption process.
We explored software options such as VeraCrypt, BitLocker, FileVault, as well as hardware options like Self-Encrypting Drives (SEDs) and external hardware encryption devices. These solutions offer different features and levels of security, allowing you to choose the one that best suits your needs.
Managing encrypted SSDs requires the implementation of best practices, including regular updates, secure storage of encryption keys, strong passwords, regular backups, and user education. These practices help maintain the security and integrity of your encrypted data and ensure continued protection.
In today’s digital landscape, where data breaches and identity theft are a constant threat, encrypting your SSD is a vital step in safeguarding your sensitive information. Whether you are an individual or a business, protecting your data should be a top priority, and SSD encryption provides an effective solution to achieve that.
Remember to always stay informed about the latest advancements in SSD encryption technology and security best practices. Regularly review and update your encryption systems to adapt to the evolving threat landscape and maintain the highest level of data security.
Encrypting your SSD may require some initial effort, but the peace of mind and protection it provides is invaluable. Take the necessary steps to implement SSD encryption today and keep your data secure in the face of rapidly advancing digital threats.