Introduction
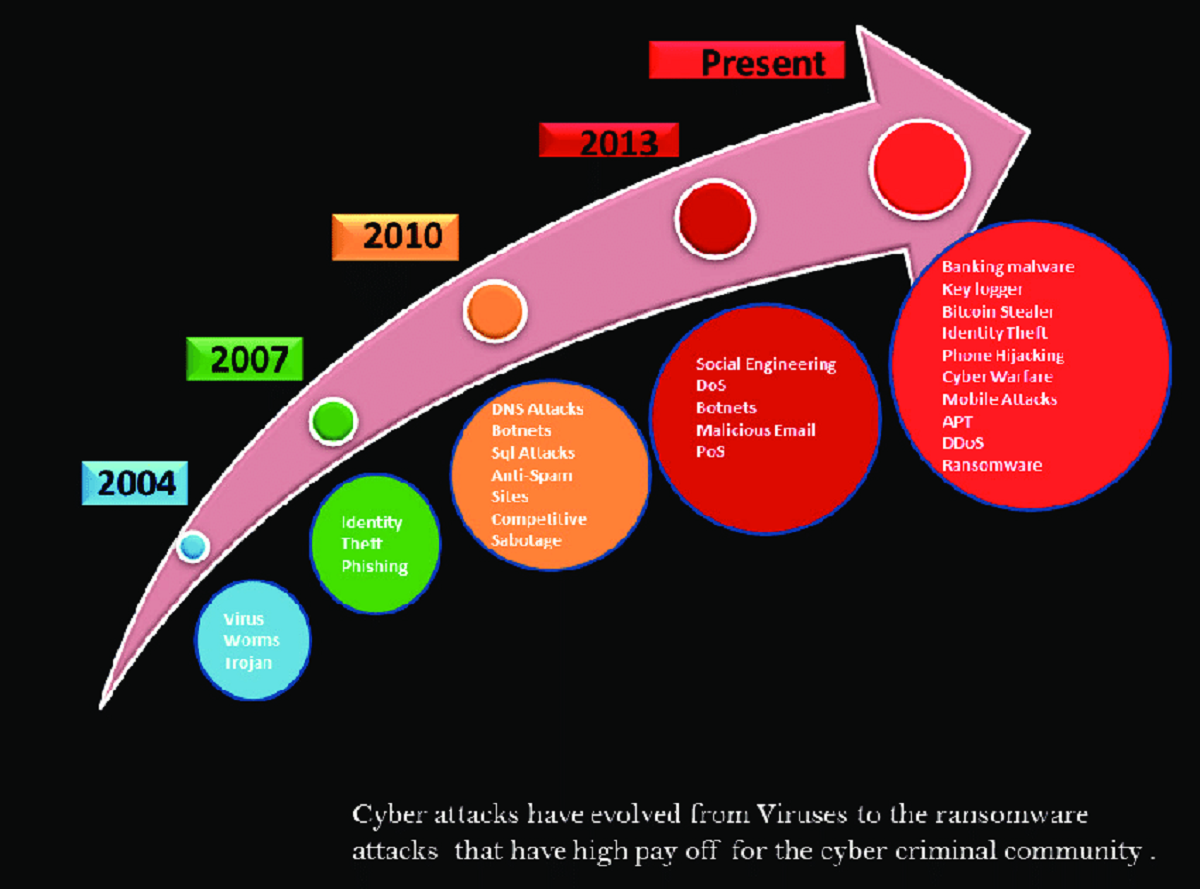
Welcome to the world of cyber threats, where data breaches and hacking attempts lurk around every corner. As technology advances, so do the sophistication and prevalence of cyberattacks. In this digital age, protecting sensitive information and securing digital assets has become a paramount concern for individuals and organizations alike. One emerging technology that holds great promise in revolutionizing the field of cybersecurity is quantum computing.
Quantum computing harnesses the principles of quantum mechanics, the branch of physics that deals with the behavior of matter and energy at a quantum level. Unlike classical computers, which use binary bits to store and process data, quantum computers use quantum bits, or qubits, which can represent multiple states simultaneously. This inherent ability to exist in multiple states simultaneously, known as superposition, gives quantum computers immense computational power and the potential to solve complex problems at an exponentially faster rate.
While classical computing has made significant strides in securing digital systems, it has its limitations. Classical encryption algorithms, such as RSA and AES, rely on the difficulty of factoring large numbers or solving difficult mathematical problems. However, the advent of quantum computing threatens to render these encryption methods obsolete, as quantum computers can efficiently solve these problems using algorithms like Shor’s algorithm.
Quantum computing has the potential to revolutionize cybersecurity by providing enhanced encryption and threat detection capabilities. In this article, we will explore the potential of quantum computing in the field of cybersecurity and how it can help overcome the limitations of classical computing. We will discuss the concept of quantum cryptography, which offers the promise of unbreakable security, and explore quantum key distribution for secure communication channels. We will also delve into the concept of post-quantum cryptography, which aims to develop encryption methods resistant to quantum attacks. Furthermore, we will explore how quantum machine learning can enhance threat detection and discuss measures that can be taken to protect against quantum attacks.
Join us on this journey as we navigate through the exciting possibilities that quantum computing offers in the realm of cybersecurity. Brace yourself for a future where unbreakable encryption, secure communication channels, and advanced threat detection become the pillars of digital defense.
Understanding Quantum Computing
Before delving into the potential impact of quantum computing on cybersecurity, it is essential to have a fundamental understanding of how quantum computers work. Unlike classical computers that operate on bits, which represent information as either a 0 or a 1, quantum computers use qubits to store and process data. Qubits, being quantum entities, can exist in a superposition of states, meaning they can represent both 0 and 1 simultaneously.
This ability of qubits to be in multiple states at once is what gives quantum computers their immense computational power. While classical computers process data sequentially, considering one possibility at a time, quantum computers can process multiple possibilities simultaneously. This parallel processing capability enables quantum computers to solve complex problems exponentially faster than classical computers.
Another important concept in quantum computing is quantum entanglement. Entanglement occurs when two or more qubits become linked in such a way that the state of one qubit is dependent on the state of another, even if they are physically separated. This phenomenon allows for the creation of entangled pairs of qubits, in which the measurement of one qubit instantaneously determines the state of the other, regardless of the distance between them.
However, quantum computing is not without its challenges. One of the main obstacles in building practical quantum computers is maintaining the delicate quantum states of qubits. Quantum systems are susceptible to environmental interference, which can cause quantum information to degrade or lose coherence, leading to errors in calculations.
As a result, researchers and engineers are continually working on developing error-correction techniques to address this issue and improve the stability of quantum computers. Additionally, quantum computers require specialized infrastructure and technologies, such as ultra-low temperatures and precise control mechanisms, to create and manipulate qubits.
Despite these challenges, advancements in the field of quantum computing have been substantial. Quantum computers have already demonstrated their potential in tackling problems that are beyond the reach of classical computers. From simulating complex quantum systems to optimizing logistical operations and cryptography, quantum computing holds the key to unlocking a new era of possibilities.
Now that we have a basic understanding of quantum computing, let us explore how this groundbreaking technology can revolutionize the field of cybersecurity and address the limitations of classical computing.
The Limitations of Classical Computing
Classical computing has been the backbone of our digital infrastructure for decades, revolutionizing various aspects of our lives. However, as cyber threats become increasingly sophisticated, classical computing faces inherent limitations that hinder its ability to provide foolproof cybersecurity.
One of the primary limitations of classical computing lies in its computational power. Classical computers process information sequentially, performing calculations one after another. This linear approach poses challenges when solving complex problems, such as factoring large numbers or solving intricate mathematical equations.
Classical encryption algorithms, such as RSA and AES, rely on the difficulty of these computational problems to secure data and communications. However, the advent of quantum computers threatens to undermine this security. Quantum computers can efficiently solve these problems using algorithms like Shor’s algorithm, rendering classical encryption methods susceptible to attack.
Another limitation of classical computing is its vulnerability to brute force attacks. Brute force attacks involve systematically trying every possible combination to crack passwords or encryption keys. While classical computers can perform these calculations relatively quickly, the exponential growth in computational power of quantum computers could drastically reduce the time required for a successful brute force attack.
Furthermore, classical computing faces challenges in managing big data. As the volume, velocity, and variety of data continue to grow exponentially, classical computers struggle to process and analyze this vast amount of information effectively. Real-time analysis and decision-making become increasingly challenging, leaving potential vulnerabilities and threats undetected.
Additionally, classical computing lacks the ability to ensure the integrity and authenticity of data. While encryption algorithms can protect data during transit or storage, they do not provide a foolproof method of verifying the credibility of the data itself. This poses a significant challenge in an era where data manipulation and forgery are prevalent, as trust in the integrity of data becomes crucial.
Overall, classical computing’s limitations necessitate the exploration of alternative technologies to strengthen cybersecurity measures. Quantum computing presents an intriguing solution, with its exponential computational power and unique properties that can overcome the shortcomings of classical computing.
Now that we understand the limitations of classical computing, let us explore the potential of quantum computing in revolutionizing the field of cybersecurity.
The Potential of Quantum Computing
Quantum computing holds immense potential in transforming the field of cybersecurity, offering unprecedented computational power and innovative techniques to safeguard sensitive information. By leveraging the inherent properties of quantum mechanics, quantum computing can surmount the limitations of classical computing and revolutionize various aspects of cybersecurity.
One of the most promising applications of quantum computing in cybersecurity is quantum cryptography. Unlike classical cryptographic methods that rely on computational complexity, quantum cryptography utilizes the principles of quantum mechanics to provide unbreakable security. Quantum key distribution (QKD), a subfield of quantum cryptography, enables the secure exchange of cryptographic keys between two parties with the guarantee of detecting any interception or tampering.
Using the properties of quantum entanglement, QKD ensures that any attempt to eavesdrop on the communication is immediately detected, making it virtually impossible for an attacker to intercept or decipher the exchanged keys. This unbreakable security can protect sensitive data and communications from even the most advanced forms of attacks.
While quantum cryptography offers unparalleled security, post-quantum cryptography addresses the challenge of preparing for the future threat of quantum computers breaking existing encryption algorithms. Post-quantum cryptography aims to develop encryption methods that are resistant to quantum attacks, ensuring that data protected today remains secure in the era of quantum computing.
Besides cryptography, quantum computing holds the potential to enhance threat detection and mitigation. Quantum machine learning algorithms have shown promise in analyzing large datasets and identifying patterns or anomalies that may indicate potential cyber threats. The parallel processing capability of quantum computers can significantly speed up the analysis of massive amounts of data, enabling real-time threat detection and response.
Furthermore, quantum computing can aid in optimizing complex security algorithms, such as those used in intrusion detection systems and network monitoring. By solving intricate mathematical problems more efficiently, quantum computers can improve the performance of these algorithms, thereby strengthening overall cybersecurity defenses.
It is important to note that alongside these potential benefits, quantum computing also brings new risks. Quantum computers themselves could be used maliciously to break traditional encryption methods, undermining current security measures. As such, the development and implementation of quantum-resistant encryption algorithms become critical in preparing for the future.
As we explore the potential of quantum computing in cybersecurity, it is crucial to acknowledge that the technology is still in its nascent stages. Practical quantum computers with significant computational power are not yet widely available. Nevertheless, ongoing advancements and research in the field are paving the way for a future where quantum computing plays a vital role in securing our digital world.
In the next sections, we will delve deeper into the specific applications of quantum computing in cybersecurity, such as quantum cryptography and machine learning, to understand how these advancements can enhance our defenses against cyber threats.
Quantum Cryptography: Unbreakable Security
Quantum cryptography is a revolutionary approach to securing information that provides unbreakable security using the principles of quantum mechanics. Unlike classical cryptographic methods, which rely on computational complexity, quantum cryptography harnesses the inherent properties of quantum physics to offer unprecedented levels of security.
At the heart of quantum cryptography is the concept of quantum key distribution (QKD). QKD enables the secure exchange of cryptographic keys between two parties, ensuring that any attempt to intercept or tamper with the communication is immediately detected. This guarantees the confidentiality and integrity of the exchanged keys and, subsequently, the security of the encrypted data or communication.
The security provided by QKD is rooted in the quantum properties of entanglement and the Heisenberg uncertainty principle. Through the use of entangled quantum particles, typically photons, the act of eavesdropping or intercepting the communication is intrinsically detected. Any attempt to measure or observe the quantum state of the transmitted photons introduces disturbances that can be detected by the legitimate parties.
This detection mechanism, known as the “no-cloning theorem,” ensures that any unauthorized interception of the quantum communication is immediately exposed, as the eavesdropper would inadvertently modify the quantum state of the transmitted photons. This property guarantees the security of the exchanged keys, making it virtually impossible for an attacker to gain access to the encrypted information.
Furthermore, another critical aspect of quantum cryptography is the use of random numbers generated from quantum processes. Classical cryptographic methods often rely on pseudo-random number generators, which can be vulnerable to algorithmic or computational attacks. In contrast, quantum cryptography leverages the inherent randomness of quantum processes, providing an additional layer of security and unpredictability.
The unbreakable security provided by quantum cryptography offers significant advantages for applications where data confidentiality and integrity are paramount. Industries such as finance, healthcare, government, and defense can benefit greatly from the implementation of quantum cryptography, ensuring that sensitive information is protected from the most advanced forms of cyberattacks.
Despite its immense potential, there are challenges that need to be overcome for the widespread adoption of quantum cryptography. The distance limitations of current QKD protocols and the vulnerability of the underlying hardware to physical attacks are among the key areas of research and development. However, continuous advancements in technology and the increasing interest in quantum computing are paving the way for practical and secure implementations of quantum cryptography.
As the field of quantum cryptography continues to progress, it promises to be a game-changer in the realm of cybersecurity. The ability to exchange cryptographic keys securely using the principles of quantum mechanics provides an unprecedented level of security, making quantum cryptography a vital tool in protecting sensitive information in an increasingly interconnected and digital world.
Quantum Key Distribution: Secure Communication Channels
Quantum Key Distribution (QKD) is a groundbreaking technology that enables the secure exchange of cryptographic keys between two parties, ensuring the confidentiality and integrity of communication channels. By leveraging the principles of quantum mechanics, QKD offers a level of security that is fundamentally unbreakable, even in the face of sophisticated cyberattacks.
At the core of QKD is the use of quantum properties, such as the phenomenon of entanglement and the Heisenberg uncertainty principle, to detect any unauthorized interception or tampering. Through the exchange of quantum particles, typically photons, between the sender and the receiver, QKD utilizes the inherent properties of these particles to establish a secret key that is known exclusively to the legitimate parties.
The security of QKD lies in the detection of any interference or measurement attempted by an eavesdropper. The no-cloning theorem in quantum mechanics ensures that any attempts to intercept or tamper with the transmission will be detectable. Any measurement or observation made by the eavesdropper will disturb the quantum state of the transmitted particles, signaling the presence of an unauthorized presence and rendering the tampering evident.
The concept of entanglement plays a crucial role in QKD. Entangled particles are intrinsically linked, so that any change in the state of one particle will instantaneously affect the state of the other, regardless of the distance between them. By using entangled particles in the quantum transmission, any attempt to intercept the communication will disrupt the delicate entangled state, immediately alerting the legitimate parties to the presence of an eavesdropper.
This inherent security provided by QKD makes it immune to various forms of traditional cryptographic attacks. Its resistance to computational and algorithmic attacks, such as brute-force attacks or factorization methods, offers a level of security that cannot be matched by classical cryptographic methods.
QKD not only ensures the secure exchange of cryptographic keys but also provides a secure foundation for subsequent encrypted communication channels. Once the secret key has been established through QKD, it can be used in symmetric encryption schemes to encrypt and decrypt the actual data being communicated between the parties. This secure key exchange avoids the vulnerabilities and potential compromises associated with traditional key exchange mechanisms.
Despite its remarkable capabilities, QKD also faces practical challenges that need to be addressed for wider adoption. These challenges include the technological limitations of current QKD protocols, such as distance limitations and vulnerability to physical attacks. Additionally, the implementation of QKD in real-world scenarios requires the integration of QKD devices into existing communication infrastructures.
Nonetheless, ongoing research and development efforts are focused on addressing these challenges and improving the feasibility and practicality of QKD. As quantum computing continues to advance, the importance of implementing secure communication channels that are resistant to quantum attacks becomes increasingly crucial.
Quantum Key Distribution provides an unparalleled level of security for communication channels, enabling the secure exchange of cryptographic keys that are virtually unbreakable. It represents a significant breakthrough in the field of cybersecurity and serves as a foundation for ensuring the confidentiality and integrity of sensitive information in an increasingly interconnected world.
Post-Quantum Cryptography: Preparing for the Future
As the development of quantum computing continues to progress, the need for post-quantum cryptography becomes vital in preparing for a future where current encryption methods may become vulnerable. Post-quantum cryptography refers to the development and implementation of cryptographic algorithms that are resistant to attacks from quantum computers.
The main concern with traditional cryptographic algorithms, such as RSA and AES, is their reliance on mathematical problems that can be efficiently solved by quantum computers. For example, Shor’s algorithm can factor large numbers quickly, thus threatening the security of encryption algorithms based on factorization. Post-quantum cryptography aims to address this vulnerability by designing encryption schemes that are immune to attacks from both classical and quantum computers.
There are various approaches to post-quantum cryptography, including lattice-based, code-based, multivariate polynomial-based, and hash-based cryptography, among others. These approaches rely on mathematical problems that are believed to be difficult for both classical and quantum computers to solve efficiently.
Lattice-based cryptography, for instance, utilizes the hardness of solving problems related to lattices in higher-dimensional spaces. The security of lattice-based cryptosystems lies in the difficulty of finding the shortest vector within a lattice, which is exponentially complex for classical and quantum computers.
Code-based cryptography, on the other hand, relies on the complexity of decoding certain error-correcting codes. The difficulty of decoding these codes forms the basis for secure encryption and digital signatures.
Multivariate polynomial-based cryptography involves the use of polynomial equations with multiple variables. Solving systems of multivariate polynomial equations is believed to be hard, even for powerful quantum computers, providing a foundation for secure cryptographic schemes.
Hash-based cryptography takes advantage of cryptographic hash functions, which are believed to remain secure in a post-quantum world. Hash-based signatures and other hash-based cryptographic techniques offer a high level of resistance against quantum attacks.
The development and standardization of post-quantum cryptographic algorithms are ongoing efforts involving experts and organizations worldwide. The National Institute of Standards and Technology (NIST), for example, initiated a public competition to select new post-quantum algorithms for standardization.
Preparing for the future of quantum computing involves not only developing post-quantum cryptographic algorithms but also ensuring their smooth integration into existing systems and infrastructures. Implementing these new algorithms will require updates to cryptographic protocols, libraries, and applications to support the transition to post-quantum security.
Furthermore, the transition to post-quantum cryptography will take time and careful planning. It requires a phased approach to ensure compatibility and interoperability across different systems and networks as the cryptographic landscape evolves.
By investing in and adopting post-quantum cryptography, organizations can future-proof their security measures. It allows them to safeguard sensitive data and communications, ensuring that their encrypted information remains secure even in the face of quantum computing advancements.
As quantum computers advance, the importance of post-quantum cryptography grows, necessitating collaborative efforts to develop and implement robust encryption algorithms that can withstand the power of quantum computing.
Quantum Machine Learning: Enhancing Threat Detection
Quantum machine learning (QML) is an emerging field that combines the power of quantum computing with machine learning techniques, creating new avenues for enhancing threat detection in cybersecurity. By leveraging the advanced computational capabilities of quantum computers, QML has the potential to revolutionize the way we detect and combat cyber threats.
Machine learning algorithms play a critical role in cybersecurity by analyzing massive amounts of data to identify patterns and anomalies that may indicate potential threats. However, the effectiveness of traditional machine learning algorithms can be limited by the complexity and scale of data involved.
Quantum computers offer a unique advantage in tackling these challenges. With their ability to perform complex calculations and process vast datasets in parallel, quantum computers can significantly speed up the training and inference processes of machine learning algorithms. This parallel processing capability can enable real-time threat detection and response, even in dynamic and fast-moving cyber environments.
One of the main applications of QML in threat detection is anomaly detection. Anomalies, such as unusual network traffic patterns or unexpected user behavior, can be indicative of potential security breaches or attacks. Traditional anomaly detection algorithms often struggle with accurately identifying these anomalies due to the complexity and volume of data. QML techniques can help overcome these challenges by efficiently processing and analyzing high-dimensional data, enabling the detection of subtle and sophisticated threats.
Furthermore, QML can enhance the performance of intrusion detection systems (IDS) and network monitoring tools. By optimizing the algorithms used in these systems, quantum computers can more effectively identify and respond to evolving threats, such as zero-day attacks or advanced persistent threats (APTs). The advanced computational capabilities of quantum computers also enable the exploration of complex models and deep neural networks, further improving the accuracy and efficacy of threat detection mechanisms.
QML can also assist in data classification and clustering, playing a crucial role in identifying and categorizing new types of cyber threats. By applying quantum machine learning techniques to cybersecurity datasets, security experts can gain deeper insights into the behaviors and characteristics of various threat actors, leading to more effective strategies for defense and response.
While QML holds tremendous promise, it is important to acknowledge that realistic quantum computers with sufficient computational power for practical QML applications are still in the early stages of development. However, ongoing research and advances in both quantum computing and machine learning are rapidly bringing us closer to realizing the potential of QML in cybersecurity.
With its ability to process vast amounts of data and identify subtle patterns that indicate potential threats, Quantum Machine Learning is poised to revolutionize threat detection in cybersecurity. By harnessing the power of quantum computers, we can augment our existing defense mechanisms and stay one step ahead of the ever-evolving landscape of cyber threats.
Protecting Against Quantum Attacks
As the development of quantum computing progresses, it is crucial to prepare and implement strategies to protect against the potential threats posed by these powerful machines. Quantum attacks, leveraging the computational advantages of quantum computers, could render current cryptographic algorithms vulnerable. To safeguard our digital infrastructure, protecting against quantum attacks requires proactive measures and resilient cryptographic solutions.
One approach to protecting against quantum attacks is the deployment of post-quantum cryptographic algorithms. These algorithms are specifically designed to be resistant to attacks from both classical and quantum computers. By transitioning to post-quantum cryptography, organizations can ensure that their encrypted information remains secure, even in the face of advanced quantum computing.
Standardization efforts and ongoing research in post-quantum cryptography aim to identify and develop suitable algorithms that offer a high degree of security against quantum attacks. Organizations are encouraged to follow these developments closely and adopt standardized post-quantum cryptographic algorithms once they are widely available.
In addition to transitioning to post-quantum cryptography, another approach to protecting against quantum attacks is quantum-resistant key exchange protocols. These protocols enable the secure exchange of cryptographic keys while ensuring that the keys remain secure, even in the presence of quantum computers. Examples of such protocols include New Hope, SIKE, and Frodo.
Deploying quantum-resistant key exchange protocols alongside post-quantum cryptography provides a comprehensive defense against both current and future quantum threats. This combination ensures that encrypted data and communications remain secure, even in the event of a significant advancement in quantum computing capabilities.
Furthermore, organizations should consider implementing quantum-resistant encryption for data at rest. Encryption methods that are resistant to quantum attacks should be used to protect sensitive information stored in databases, file systems, or backup archives. This helps mitigate the risk of unauthorized access should a quantum computer break the algorithms used to protect the data. Examples of quantum-resistant encryption algorithms for data at rest include lattice-based cryptography and hash-based cryptography.
It is also essential to invest in research and development efforts to continuously explore new cryptographic techniques and protocols that offer resistance against future quantum attacks. Collaborative efforts between academia, industry, and government organizations can lead to the development of innovative strategies and solutions that enhance our cybersecurity posture.
Organizations should also consider adopting quantum-aware security practices, which involve periodically reviewing and updating their cryptographic mechanisms to align with the evolving threats from quantum computers. This includes staying informed about advancements in quantum computing and regularly assessing their infrastructure for potential vulnerabilities.
The protection against quantum attacks requires a coordinated effort from various stakeholders, including governments, research institutions, and industry leaders. Collaboration and information sharing are essential to stay ahead of the curve and adapt security measures accordingly.
While quantum attacks present new challenges, they also provide an opportunity to enhance our security posture and develop advanced cryptographic solutions. By staying proactive and implementing quantum-resistant measures, we can safeguard our digital systems and data from the potential threats posed by quantum computing.
Conclusion
Quantum computing is poised to revolutionize the field of cybersecurity, offering unprecedented computational power and capabilities that can break current encryption methods. As technology advances, it is vital to understand the potential impact of quantum computing and implement strategies to protect against quantum attacks.
Throughout this article, we have explored various aspects of quantum computing and its implications for cybersecurity. We began by understanding the fundamentals of quantum computing and the limitations of classical computing in securing digital systems.
We then delved into the potential of quantum computing in strengthening cybersecurity, starting with quantum cryptography. Quantum key distribution (QKD) offers unbreakable security, ensuring the confidentiality and integrity of cryptographic keys through the principles of quantum mechanics. Post-quantum cryptography provides a roadmap for preparing for the future, developing encryption algorithms that can withstand attacks from quantum computers.
Quantum machine learning (QML) enhances threat detection by leveraging the computational power of quantum computers. By processing vast amounts of data and identifying patterns and anomalies, QML can significantly improve cybersecurity defenses.
Finally, we discussed the importance of protecting against quantum attacks. Transitioning to post-quantum cryptographic algorithms and deploying quantum-resistant key exchange protocols are essential steps in safeguarding against the threats posed by quantum computers. Additionally, continuous research, collaboration, and proactive security measures will be necessary to stay resilient in the face of emerging quantum technologies.
As the field of quantum computing progresses and practical quantum computers become a reality, it is crucial to stay informed and remain adaptable. The evolution of encryption algorithms, the implementation of quantum-resistant techniques, and ongoing research efforts will play a critical role in ensuring our digital systems and data remain secure.
By recognizing the potential of quantum computing and proactively addressing its implications, we can navigate the future of cybersecurity with confidence. Embracing the advancements and preparing for the challenges of quantum computing will ultimately strengthen our resilience against cyber threats and protect our digital assets in an increasingly interconnected world.