Introduction
When it comes to establishing connectivity between workstations and servers, there are various methods available. One such method is DirectAccess. DirectAccess is a remote access technology that provides seamless and secure connectivity between remote users and internal network resources. It eliminates the need for traditional VPN connections, allowing users to access internal resources just as if they were in the office.
DirectAccess leverages the power of IPv6 and IPsec to establish a secure connection between the workstation and the server. It provides users with a transparent and always-on connection, enabling them to access network resources regardless of their location.
This article will delve into the world of DirectAccess and explore the connectivity protocols it uses, including the IPSec tunnel, IPv6 transition technologies like Teredo and IP-HTTPS, and the network topology associated with DirectAccess.
By understanding how DirectAccess works and the benefits it offers, businesses can ensure that their employees have secure and efficient access to internal resources, even when working remotely.
What is DirectAccess?
DirectAccess is a remote access technology developed by Microsoft that provides secure and seamless connectivity between remote users and internal network resources. It was first introduced in Windows Server 2008 R2 and Windows 7 and has since become a popular method for establishing remote access connections in enterprise environments.
Unlike traditional VPN solutions, DirectAccess eliminates the need for user interaction to establish a connection. Once a user’s device is connected to the internet, DirectAccess automatically establishes a secure connection to the corporate network, allowing users to access internal resources as if they were on the local network. This “always-on” connectivity provides a seamless experience for remote users, enhancing productivity and usability.
One of the key features of DirectAccess is its ability to provide connectivity to internal resources without the need for a public IP address. This is made possible by leveraging IPv6 and IPv6 transition technologies, such as Teredo and IP-HTTPS. DirectAccess also utilizes IPSec to establish a secure tunnel between the remote device and the internal network, ensuring that the connection is encrypted and protected from unauthorized access.
In addition to secure connectivity, DirectAccess offers other benefits for organizations. It simplifies remote access management by allowing administrators to manage policies and enforce security measures centrally. It also provides monitoring and reporting capabilities for better visibility into remote connections. Moreover, DirectAccess supports multi-factor authentication, further enhancing the security of remote access.
Overall, DirectAccess is a powerful remote access technology that enables organizations to provide secure and seamless connectivity for remote users. By leveraging the power of IPv6, IPsec, and other technologies, DirectAccess simplifies remote access management and enhances productivity for businesses of all sizes.
How does DirectAccess work?
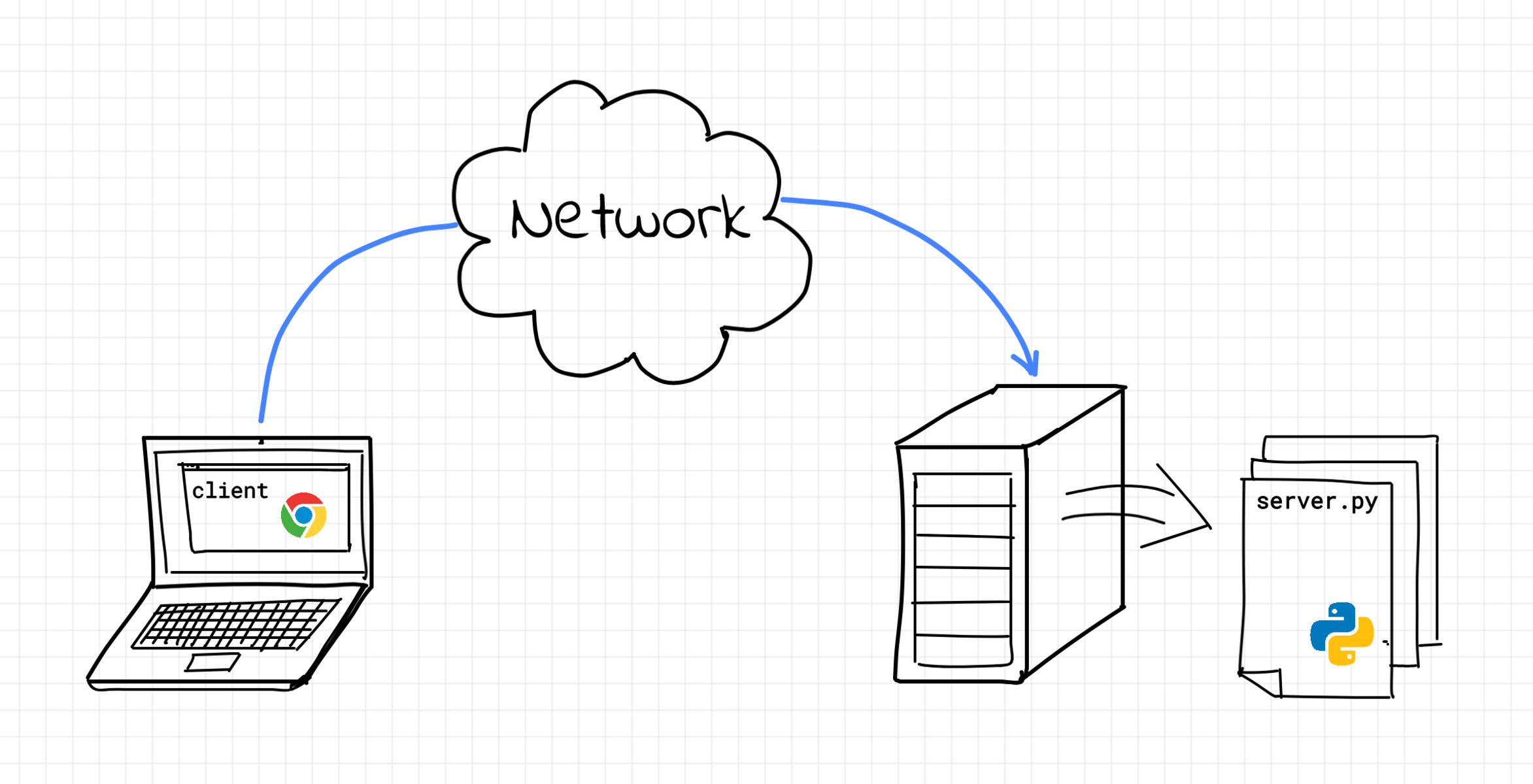
DirectAccess leverages a combination of technologies to establish a secure and seamless connection between remote users and internal network resources. When a user’s device connects to the internet, DirectAccess automatically establishes a connection to the corporate network, allowing the user to access internal resources without the need for manual intervention.
The first step in the DirectAccess process is the establishment of an IPsec tunnel between the user’s device and the DirectAccess server. This tunnel provides a secure communication channel for data transmission. IPsec encrypts the traffic and ensures that it is protected from unauthorized access.
DirectAccess also relies on IPv6 to establish connectivity. When a user’s device connects to the internet, it obtains an IPv6 address. This address is used to establish a connection to the DirectAccess server, which also has an IPv6 address. However, since the majority of networks still use IPv4, DirectAccess utilizes IPv6 transition technologies to enable communication between the user’s device and the internal resources.
One such transition technology used by DirectAccess is Teredo. Teredo allows IPv6 packets to be encapsulated within IPv4 packets, allowing communication between IPv6-enabled devices and IPv4 networks. This ensures that even if the user’s internet service provider only provides an IPv4 address, they can still establish a connection to the DirectAccess server.
Another technology employed by DirectAccess is IP-HTTPS (IP over HTTPS). IP-HTTPS encapsulates IPv6 packets within HTTPS (HTTP Secure) packets, utilizing the standard SSL/TLS encryption used by secure websites. This allows for secure communication between the user’s device and the DirectAccess server, even in scenarios where Teredo cannot be used.
By combining these technologies, DirectAccess ensures that remote users can establish a secure and seamless connection to internal resources. The IPsec tunnel provides encryption and protection, while the use of IPv6 transition technologies ensures compatibility with both IPv4 and IPv6 networks. This allows for easy and efficient remote access to internal resources without compromising security.
Connectivity protocols used by DirectAccess
DirectAccess utilizes a combination of connectivity protocols to establish a secure and seamless connection between remote users and internal network resources. These protocols work together to ensure that data transmission is protected and that communication is possible across different network configurations.
The first protocol used by DirectAccess is the IPsec tunnel. IPsec provides end-to-end encryption and authentication, ensuring that the data transmitted between the remote user’s device and the internal network remains secure. Through the use of certificates or shared secrets, IPsec establishes a secure channel for data transmission, protecting it from unauthorized access.
In addition to IPsec, DirectAccess leverages IPv6 transition technologies to enable connectivity between the remote user’s device and the internal network. One of these technologies is Teredo. Teredo is designed to provide IPv6 connectivity for devices that are located behind an IPv4 network address translation (NAT) device.
Teredo encapsulates IPv6 packets within IPv4 packets, allowing communication between the remote device, the DirectAccess server, and internal resources, even if they are on an IPv4 network. This makes it possible for remote users to connect to the corporate network regardless of their location or the type of Internet connection they are using.
Another connectivity protocol used by DirectAccess is IP-HTTPS (IP over HTTPS). IP-HTTPS is utilized as a fallback option when Teredo cannot be used, such as in environments where IPv6 is not supported or allowed. IP-HTTPS encapsulates IPv6 packets within HTTPS packets, using the SSL/TLS encryption commonly used for secure web communication.
The use of IP-HTTPS allows DirectAccess to establish a secure connection between the remote user’s device and the DirectAccess server, even in scenarios where other connectivity protocols are not available. This ensures that remote users can access internal resources securely and seamlessly, regardless of the network configuration.
By combining these connectivity protocols, DirectAccess provides a robust and versatile remote access solution. The IPsec tunnel ensures data encryption and authentication, while Teredo and IP-HTTPS enable communication across different network configurations. This allows remote users to access corporate resources securely and efficiently, regardless of their location or the network environment they are connected to.
IPSec tunnel
The IPSec tunnel is a crucial component of DirectAccess, as it provides a secure and private communication channel between the remote user’s device and the internal network resources. IPSec stands for Internet Protocol Security and is a widely-used protocol suite for securing internet communications. It offers encryption, integrity checking, and authentication, ensuring that data sent over the tunnel remains confidential and protected from unauthorized access.
When a remote user connects to the internet, their device initiates a secure IPSec tunnel with the DirectAccess server. This tunnel is established when both ends of the connection authenticate each other, typically through the use of certificates or shared secrets. Once the tunnel is established, all communication between the remote device and the internal network is encrypted and encapsulated within IP packets.
One of the main advantages of using an IPSec tunnel is the ability to secure communication at the network layer. By operating at the network layer, IPSec ensures that all communication, regardless of the applications or protocols used, is protected. This means that remote users can access a wide range of internal resources, such as file servers, databases, and intranet sites, securely and without compromising data confidentiality.
In addition to encryption, the IPSec tunnel also provides integrity checking. This means that any tampering or modification of the data packets during transmission will be detected. If any modifications are detected, the packet is discarded, ensuring the integrity and reliability of the transmitted data.
Authentication is an essential aspect of the IPSec tunnel as well. This ensures that both ends of the connection can verify each other’s identities and establish a secure and trusted connection. The authentication process can be based on certificates, where both the remote device and the DirectAccess server possess a valid certificate, or shared secrets, where a pre-shared key is used for authentication.
Overall, the IPSec tunnel is a critical component of DirectAccess, providing the necessary encryption, integrity checking, and authentication to establish a secure and private communication channel between remote users and internal network resources. By leveraging the power of IPSec, DirectAccess ensures that data transmitted over the tunnel remains confidential and protected, contributing to the overall security and integrity of the remote access solution.
IPv6 transition technologies
IPv6 transition technologies play a vital role in enabling connectivity between remote users and internal network resources in a DirectAccess deployment. These technologies allow for communication between devices that use IPv6 addressing and networks that primarily rely on IPv4.
One of the key IPv6 transition technologies used by DirectAccess is Teredo. Teredo is designed to provide IPv6 connectivity for devices located behind IPv4 network address translation (NAT) devices. In scenarios where the remote user’s device is connected to the internet via an IPv4 network, Teredo encapsulates IPv6 packets within IPv4 packets. This allows the communication to pass through IPv4-only networks and reach the DirectAccess server.
Teredo utilizes UDP (User Datagram Protocol) as the transport protocol and creates a virtual IPv6 tunnel over the IPv4 network. It assigns a unique Teredo IPv6 address to the remote user’s device, allowing it to communicate with other IPv6-enabled devices in the corporate network. This technology ensures that remote users can establish a connection to the DirectAccess server and access internal resources, even if their internet service provider only provides an IPv4 address.
Another IPv6 transition technology employed by DirectAccess is IP-HTTPS (IP over HTTP Secure). IP-HTTPS encapsulates IPv6 packets within HTTPS (HTTP Secure) packets, using the standard SSL/TLS encryption employed by secure websites. This allows for secure communication between the remote user’s device and the DirectAccess server, even in situations where Teredo cannot be used.
IP-HTTPS is particularly useful in environments where IPv6 is not supported or allowed, or when the network configuration blocks Teredo traffic. By encapsulating the IPv6 packets within HTTPS packets, IP-HTTPS ensures that the communication remains encrypted and can traverse firewalls and proxies that allow secure web traffic.
It’s important to note that while Teredo and IP-HTTPS are the primary IPv6 transition technologies utilized by DirectAccess, there are other technologies available, such as 6to4 and ISATAP, which can also provide connectivity between IPv6-enabled devices and IPv4 networks. However, Teredo and IP-HTTPS are the most commonly used technologies due to their flexibility and compatibility with various network configurations.
Through the use of IPv6 transition technologies like Teredo and IP-HTTPS, DirectAccess ensures that remote users can seamlessly connect to the internal network, regardless of their internet connection type or the network’s lack of native IPv6 support. These technologies enable the smooth integration of IPv6 into existing IPv4 networks, facilitating modern and secure remote access for users across diverse network environments.
Teredo
Teredo is an IPv6 transition technology used by DirectAccess to establish communication between devices behind an IPv4 network and IPv6-enabled devices on the internal network. It enables remote users to connect securely to the corporate network in scenarios where their internet service provider only provides an IPv4 address.
When a remote user’s device connects to the internet, Teredo assigns it a unique Teredo IPv6 address. This address is constructed by combining the user’s assigned IPv4 address with a Teredo server’s IPv6 address. By encapsulating IPv6 packets within IPv4 packets, Teredo allows the remote device to communicate with other IPv6-enabled devices in the corporate network.
Using UDP as the transport protocol, Teredo creates a virtual IPv6 tunnel over the IPv4 network. This tunneling mechanism allows the communication to traverse IPv4-only networks, including those that employ NAT (Network Address Translation). As a result, the remote device can establish a connection to the DirectAccess server and access internal resources securely.
Teredo operates by encapsulating the IPv6 packets within UDP packets. It uses UDP port 3544 for communication between the Teredo client, Teredo server, and Teredo relay nodes. The Teredo server acts as a point of entry into the IPv6 network and provides the necessary configuration information for establishing the Teredo tunnel.
One important aspect of Teredo is its automatic negotiation of network traversal methods. Teredo can detect whether the network environment allows direct tunneling, in which case it uses Direct Tunneling as the traversal method. If direct tunneling is not feasible due to a restrictive network configuration, Teredo can adopt the Relay Tunneling method, where a Teredo relay device acts as an intermediary for communication.
It’s worth noting that while Teredo offers compatibility with IPv4 networks, it introduces certain limitations. Teredo relies on the availability and compatibility of IPv6-capable Teredo servers and relay devices. If these components are not available or properly configured, the Teredo tunnel may fail to establish. Additionally, due to the involvement of UDP encapsulation, Teredo may encounter issues with firewalls, routers, or network configurations that restrict or block UDP traffic.
Overall, Teredo is a key component of DirectAccess, enabling remote users to establish secure and seamless connections to internal resources. It addresses the challenge of IPv4 network connectivity by providing a tunneling mechanism that allows IPv6 packets to traverse IPv4 networks. With Teredo, organizations can offer modern and secure remote access solutions, ensuring that remote users can connect to the corporate network and access resources regardless of their internet connection type or network limitations.
IP-HTTPS
IP-HTTPS (IP over HTTPS) is an IPv6 transition technology used by DirectAccess to provide a secure communication channel between remote users and the internal network. It enables remote devices to establish a connection to the corporate network even in environments where native IPv6 support is not available or allowed.
IP-HTTPS works by encapsulating IPv6 packets within HTTPS (HTTP Secure) packets, utilizing the standard SSL/TLS encryption used for secure web communication. This encapsulation allows for secure transmission of IPv6 traffic over IPv4 networks, including those that have firewalls or proxies that allow HTTPS traffic.
When a remote user’s device initiates a connection to the DirectAccess server, it first establishes an SSL/TLS session through port 443, typically used for secure web communication. Once the session is established, IPv6 packets are encapsulated within HTTPS packets and transmitted securely over the network.
The use of IP-HTTPS is particularly useful in scenarios where other IPv6 transition technologies, such as Teredo, cannot be used due to network restrictions or lack of native IPv6 support. By leveraging HTTPS as the transport protocol, IP-HTTPS ensures that communication can pass through firewalls and proxies that allow secure web traffic, providing a high level of compatibility in diverse network environments.
In order for IP-HTTPS to function, a valid SSL server certificate is required on the DirectAccess server. This certificate enables the remote device to verify the authenticity of the server and establish a secure connection. It is recommended to use a trusted certificate issued by a publicly recognized certification authority to ensure the highest level of security.
One advantage of using IP-HTTPS is the ability to leverage existing HTTPS infrastructure. Many organizations already have web servers and proxies configured to handle HTTPS traffic, making it easier to incorporate IP-HTTPS into the network environment. Additionally, IP-HTTPS can benefit from the security measures implemented for HTTPS, such as encryption, integrity checking, and authentication, ensuring the confidentiality and integrity of the transmitted data.
It’s important to note that the use of IP-HTTPS may introduce some performance overhead due to the additional encapsulation and encryption processes. However, advancements in hardware and network infrastructure have minimized these impacts, making IP-HTTPS a viable option for secure remote access in various network environments.
In summary, IP-HTTPS is an integral component of DirectAccess, providing secure connectivity between remote users and the internal network. By encapsulating IPv6 packets within HTTPS packets, IP-HTTPS enables secure transmission of data over IPv4 networks. It offers compatibility, ease of integration, and high levels of security, making it a reliable transition technology for organizations deploying DirectAccess.
Network topology of DirectAccess
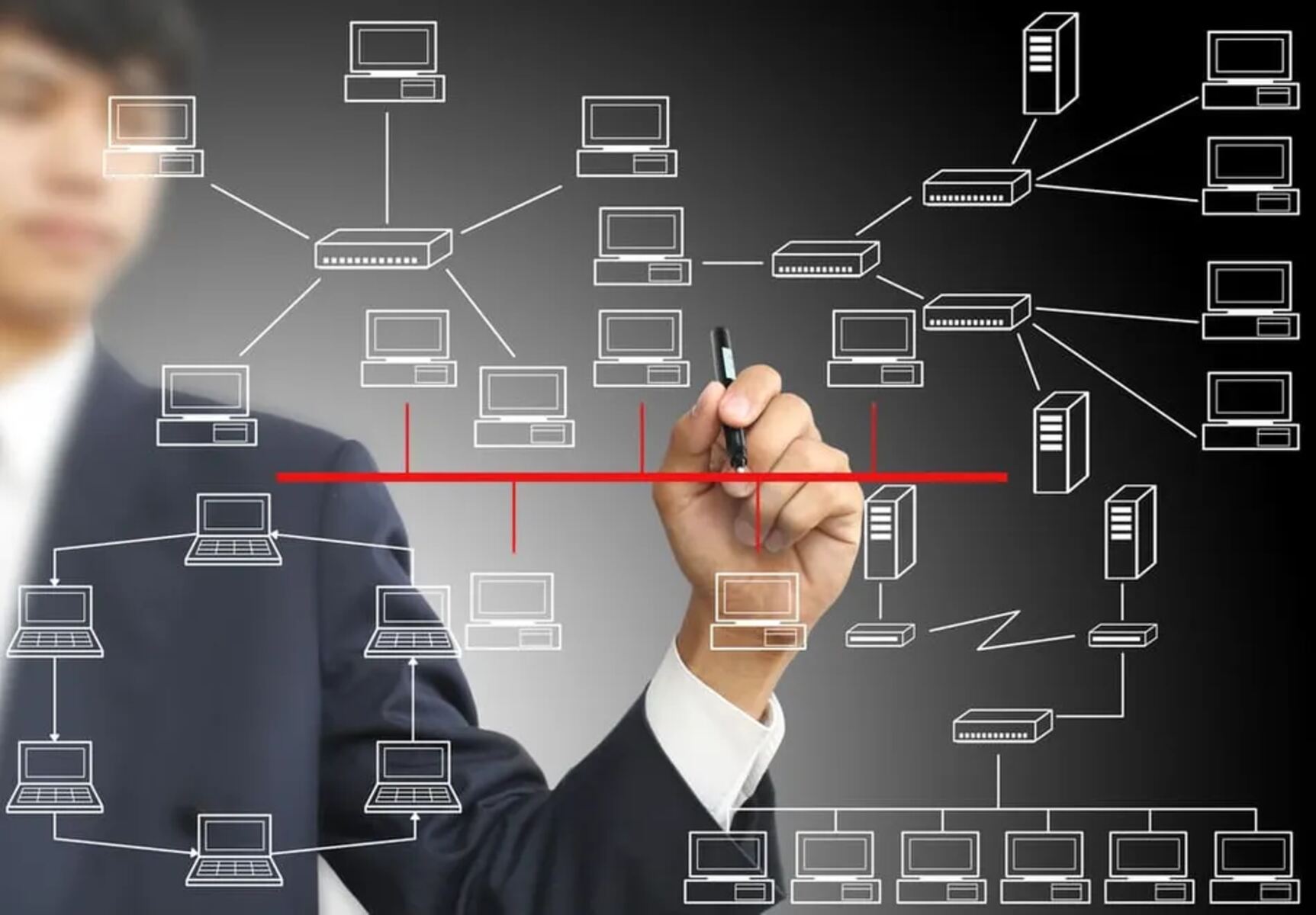
The network topology of DirectAccess is designed to facilitate secure and seamless connectivity between remote users and internal network resources. It involves various components, including DirectAccess clients, the DirectAccess server, and backend network infrastructure. Understanding the network topology of DirectAccess is crucial for planning, implementing, and managing this remote access technology.
At the core of the network topology is the DirectAccess server. This server acts as the gateway for remote connectivity and is responsible for managing the secure tunnels between remote clients and the internal network. The DirectAccess server is typically placed in the DMZ (Demilitarized Zone), an isolated network segment that separates the external internet from the internal network. By placing the DirectAccess server in the DMZ, organizations can add an extra layer of security and control to their remote access infrastructure.
DirectAccess clients are the remote devices that connect to the internal network through the DirectAccess server. These can include laptops, tablets, or other devices running Windows operating systems. DirectAccess clients establish a secure connection to the DirectAccess server and can seamlessly access internal network resources, regardless of their location.
In addition to the DirectAccess server and the clients, the network topology also includes other components, such as domain controllers, DNS (Domain Name System) servers, and network infrastructure devices. These components are integral to the functioning of DirectAccess and ensure smooth communication between the remote clients and the internal network.
Domain controllers play a vital role in the network topology, providing authentication and authorization services. They enable the DirectAccess server to authenticate remote clients and grant access to internal resources based on the user’s credentials and permissions.
The DNS servers are also critical components in the network topology. The DirectAccess server relies on DNS records to discover and connect to the appropriate internal resources. DNS plays a pivotal role in the automatic connection process offered by DirectAccess, ensuring that clients can seamlessly access resources by name resolution.
Other network infrastructure devices, such as firewalls and routers, are essential for routing network traffic and providing security for the DirectAccess deployment. These devices need to be configured properly to allow the necessary communication between the DirectAccess server, clients, and internal resources while maintaining a high level of security.
Overall, the network topology of DirectAccess is designed to provide secure and seamless connectivity between remote users and internal network resources. By understanding the components involved and their roles within the topology, organizations can effectively plan, implement, and manage their DirectAccess deployment to enable efficient and secure remote access for their users.
Benefits of using DirectAccess for workstation-server connectivity
DirectAccess offers numerous benefits for organizations seeking secure and efficient workstation-server connectivity. By leveraging this remote access technology, businesses can provide their employees with seamless access to internal resources, regardless of their physical location. Here are some key benefits of using DirectAccess for workstation-server connectivity:
Always-on connectivity: With DirectAccess, remote users can enjoy an “always-on” connection to the corporate network. Once their device is connected to the internet, DirectAccess automatically establishes a secure connection to the internal network. This eliminates the need for manual VPN connections, ensuring that users can access resources effortlessly without extra steps or interruptions.
Seamless access to internal resources: DirectAccess provides transparent access to internal network resources as if the remote users were physically present in the office. Users can access file servers, intranet sites, and applications just as they would on the local network. This seamless access enhances productivity and ensures that users can work efficiently from remote locations.
Enhanced security: DirectAccess employs strong security measures to protect sensitive data during transmission. The use of IPsec ensures that all communication between the remote device and the internal network is encrypted and authenticated, preventing unauthorized access. Additionally, with multi-factor authentication support, DirectAccess adds an extra layer of security by requiring users to verify their identities through multiple means before establishing a connection.
Centralized management: DirectAccess offers centralized management capabilities, allowing administrators to easily control and enforce policies regarding remote access. Group Policies can be applied to DirectAccess clients to ensure compliance with security standards and configurations, simplifying network maintenance and ensuring consistent security practices across the organization.
Reduced support costs: By providing a seamless and automated connection to the internal network, DirectAccess helps reduce the need for IT support to troubleshoot remote access issues. Users can connect to resources without needing assistance, minimizing the time and resources spent on technical support for remote connectivity-related issues.
Improved user experience: DirectAccess offers a user-friendly experience, ensuring that remote users can access resources easily and without disruption. There is no need to remember or manually connect to VPNs, and users can work seamlessly without interruption. This enhanced user experience contributes to increased employee satisfaction and productivity.
Support for diverse devices: DirectAccess supports a wide range of devices running Windows operating systems, including laptops, tablets, and hybrid devices. This flexibility allows users to connect with their preferred device, increasing productivity and ensuring that employees can work efficiently from any location.
Scalability and flexibility: DirectAccess is highly scalable, allowing organizations to accommodate a growing number of remote users without compromising performance or security. It also offers flexibility in terms of deployment options, providing different deployment models based on organizational needs, such as single-site deployments, multi-site deployments, or cloud-based deployments.
By leveraging the benefits of DirectAccess, organizations can enhance their workstation-server connectivity, enabling secure and efficient remote access for their employees. This technology streamlines remote work, enhances productivity, and ensures that users can access internal resources seamlessly, wherever they may be.
Conclusion
DirectAccess is a powerful remote access technology that provides seamless and secure connectivity between remote users and internal network resources. By leveraging technologies such as IPv6, IPsec, Teredo, and IP-HTTPS, DirectAccess ensures that users can effortlessly connect to the corporate network and access resources from any location.
Throughout this article, we explored the various aspects of DirectAccess, including its functionality, connectivity protocols, network topology, and benefits for workstation-server connectivity. DirectAccess offers significant advantages, such as always-on connectivity, seamless access to internal resources, improved security, centralized management, reduced support costs, enhanced user experience, support for diverse devices, and scalability.
By deploying DirectAccess, organizations can provide their remote workforce with a secure and efficient means of connecting to the internal network. Users can enjoy a seamless experience, accessing resources as if they were physically present in the office, without the need for manual VPN connections or interruptions.
Moreover, DirectAccess simplifies remote access management through centralized policies and authentication methods. Administrators can enforce security measures, configure access settings, and ensure compliance across the organization. This centralized approach helps improve security, reduce support costs, and enhance the overall user experience.
However, it’s important to note that DirectAccess requires careful planning, configuration, and network infrastructure considerations to ensure a successful deployment. Organizations should thoroughly assess their requirements, network topology, and the compatibility of IPv6 transition technologies with their existing infrastructure.
In conclusion, DirectAccess provides an efficient and secure solution for establishing connectivity between workstations and servers. By leveraging its capabilities, organizations can empower their remote workforce, improve productivity, and ensure seamless access to internal resources across diverse network environments. With its robust features and benefits, DirectAccess continues to be a valuable remote access technology for organizations of all sizes.