Introduction
Welcome to the digital age, where technology has revolutionized the way we live and do business. With the increasing reliance on digital systems and networks, the threat of cybersecurity breaches has become more imminent than ever. Companies of all sizes and industries are vulnerable to cyber attacks that can compromise sensitive data, disrupt operations, and damage reputation. This is where a robust cybersecurity policy comes into play.
A cybersecurity policy is a set of guidelines and procedures that outline how an organization protects its digital assets from unauthorized access, use, disclosure, disruption, modification, or destruction. It serves as a roadmap for securing information systems and establishing a proactive approach to address potential threats.
A well-designed cybersecurity policy sets clear expectations for employees, contractors, and stakeholders regarding their roles and responsibilities in safeguarding sensitive information. It also provides a framework for managing risks and ensuring compliance with applicable laws and regulations.
In today’s interconnected world, businesses face an ever-evolving landscape of cyber threats. From phishing attacks and malware to ransomware and data breaches, the potential consequences of a cybersecurity incident can be devastating. Organizations that lack a comprehensive cybersecurity policy are at a higher risk of falling victim to these attacks.
Therefore, it is crucial for businesses of all sizes to proactively establish and maintain a strong cybersecurity posture. This begins with the development and implementation of a well-thought-out cybersecurity policy that aligns with industry best practices and addresses the unique risks faced by the organization.
In the following sections, we will delve deeper into the importance of having a cybersecurity policy, the key components that should be included, and how to create, implement, and assess the effectiveness of such a policy. By the end, you will have a clear understanding of the crucial role a cybersecurity policy plays in protecting your organization’s digital assets.
What Is a Cybersecurity Policy?
A cybersecurity policy is a formal document that outlines an organization’s approach to managing and protecting its digital infrastructure, data, and information systems from potential cyber threats. It serves as a roadmap for implementing security measures and defining the roles and responsibilities of employees, contractors, and stakeholders in safeguarding critical assets.
At its core, a cybersecurity policy establishes guidelines and procedures for identifying and mitigating risks, preventing unauthorized access, and responding to security incidents. It encompasses various aspects of cybersecurity, including network security, data protection, access controls, incident response protocols, and employee awareness and training.
The scope and content of a cybersecurity policy can vary depending on the size and nature of the organization, as well as its industry-specific compliance requirements. However, a comprehensive cybersecurity policy typically covers the following key areas:
- Information Security Governance: This section outlines the management structure and responsibilities for overseeing and implementing the organization’s information security initiatives.
- Risk Management: It includes the identification, assessment, and prioritization of potential cybersecurity risks, as well as the strategies and controls to mitigate those risks.
- Access Controls: This component deals with defining user access rights, authentication mechanisms, and authorization processes to ensure that only authorized individuals have access to sensitive data and systems.
- Data Protection: It focuses on securing sensitive data throughout its lifecycle, including data classification, encryption, data backup and recovery, and data retention policies.
- Network Security: This section defines the measures to protect the organization’s network infrastructure from unauthorized access, such as firewalls, intrusion detection systems, and network segmentation.
- Incident Response: It outlines the procedures and steps to be followed in the event of a cybersecurity incident, including incident detection, containment, eradication, and recovery.
- Employee Awareness and Training: This component emphasizes the importance of employee education and regular training to promote a cybersecurity-conscious culture within the organization.
- Compliance: It ensures that the organization adheres to applicable legal and regulatory requirements, industry standards, and contractual obligations related to cybersecurity.
A well-crafted cybersecurity policy provides the necessary framework for implementing security controls, promoting a culture of awareness and accountability, and effectively mitigating cyber risks. By establishing clear guidelines and procedures, organizations can enhance their resilience to cyber threats and protect their valuable digital assets.
Why Do Businesses Need a Cybersecurity Policy?
In today’s digital landscape, businesses, regardless of their size or industry, are increasingly reliant on technology to operate efficiently and effectively. With this reliance comes the need for robust cybersecurity measures to protect sensitive data, maintain customer trust, and safeguard the organization’s reputation. A cybersecurity policy is a critical component of this defense strategy for several key reasons.
First and foremost, a cybersecurity policy helps businesses proactively manage and mitigate cyber risks. Cyber attacks are continually evolving, with hackers deploying sophisticated techniques to exploit vulnerabilities in digital systems and networks. By having a well-defined cybersecurity policy in place, organizations can establish a systematic approach to identifying potential risks and implementing the necessary controls to minimize their impact.
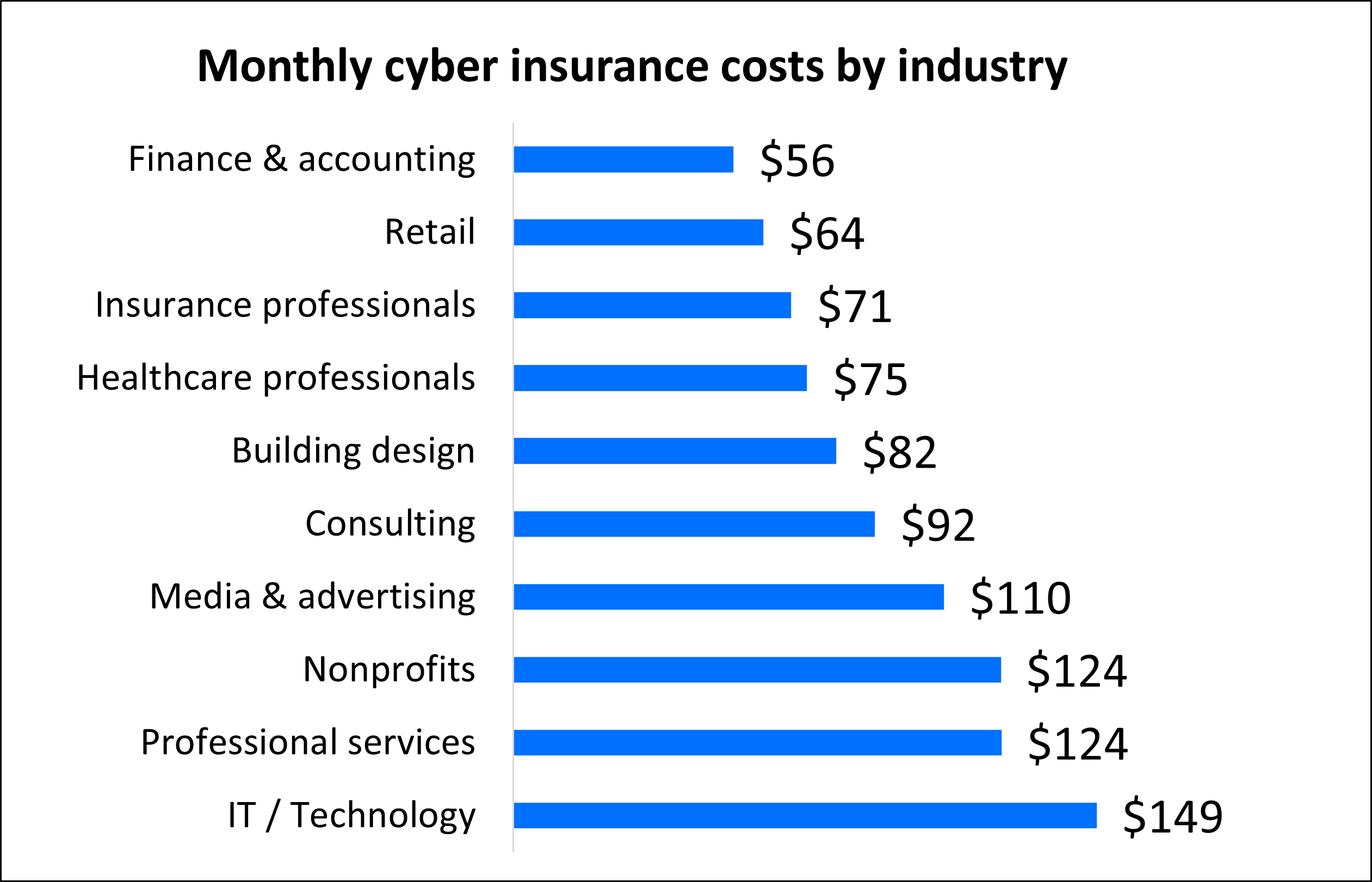
Another crucial reason why businesses need a cybersecurity policy is to comply with regulatory requirements and industry standards. Many industries, such as finance, healthcare, and government, have specific legal obligations regarding data protection and security. A cybersecurity policy helps organizations navigate these compliance requirements and demonstrates their commitment to safeguarding sensitive information.
The reputation of a business is of utmost importance, and a cybersecurity policy plays a critical role in maintaining customer trust. A data breach or security incident can significantly impact a company’s reputation, resulting in a loss of customer confidence and potential financial repercussions. By having a comprehensive cybersecurity policy, businesses can show their dedication to protecting customer data and providing a secure environment for conducting transactions.
Furthermore, a cybersecurity policy helps establish a culture of security awareness within the organization. Employees play a crucial role in maintaining strong cybersecurity practices. A policy provides clear guidelines and expectations for employees’ responsibilities regarding security protocols, data handling, and incident reporting. Regular training and awareness programs can be integrated into the policy to educate employees about emerging threats and best practices for staying secure.
In addition, a cybersecurity policy assists in streamlining incident response and recovery efforts. In the event of a security breach, having predefined procedures and protocols in place allows organizations to respond promptly and effectively, reducing the potential impact and downtime resulting from the incident.
Ultimately, a cybersecurity policy reinforces an organization’s commitment to protecting its digital assets, ensuring continuity of operations, and mitigating financial and reputational risks. It serves as a proactive measure to address potential threats, comply with regulatory requirements, foster a culture of security, and uphold customer trust. With the ever-growing threat landscape, having a well-structured cybersecurity policy is no longer a luxury but a necessity for businesses to thrive in the digital age.
Key Components of a Cybersecurity Policy
A well-designed cybersecurity policy consists of several key components that establish a comprehensive framework for protecting an organization’s digital assets. These components address various aspects of cybersecurity and provide guidelines and procedures for employees, contractors, and stakeholders to follow. Let’s explore the essential elements that should be included in a cybersecurity policy.
- Information Security Governance: This component outlines the organizational structure and responsibilities for managing and enforcing the cybersecurity policy. It identifies key stakeholders, such as the Chief Information Security Officer (CISO) or security team, and defines their roles and accountabilities in implementing and maintaining the policy.
- Risk Management: It involves the identification, assessment, and prioritization of potential cybersecurity risks. This component establishes the methods and criteria for evaluating risks, selecting appropriate controls, and regularly reviewing and updating the risk management strategy to address new threats and vulnerabilities.
- Access Controls: This component focuses on defining the rules and procedures for granting and managing user access to digital assets. It includes authentication mechanisms, such as passwords or multi-factor authentication, and outlines the process for granting and removing user privileges. It also addresses the management of privileged accounts and access to sensitive information.
- Data Protection: This component addresses the protection of sensitive data throughout its lifecycle. It includes policies for data classification, encryption, secure data storage and transmission, data backup and recovery procedures, and data retention guidelines. Additionally, it may outline guidelines for secure disposal of data when it is no longer needed.
- Network Security: It focuses on protecting the organization’s network infrastructure from unauthorized access and malicious activities. This component defines network security controls, such as firewalls, intrusion detection and prevention systems, and virtual private networks (VPNs). It also outlines guidelines for securing wireless networks and remote access procedures.
- Incident Response: This component establishes procedures and responsibilities for detecting, responding to, and recovering from cybersecurity incidents. It includes protocols for reporting security breaches, incident escalation, containment of incidents, forensics investigation, and recovery of affected systems and data.
- Employee Awareness and Training: This component emphasizes the importance of educating employees about cybersecurity best practices and promoting a culture of security awareness. It includes guidelines for employee training programs, awareness campaigns, and periodic security assessments to ensure employees are knowledgeable about potential risks and their responsibilities in maintaining a secure environment.
- Compliance: This component ensures that the organization adheres to applicable laws, regulations, and industry standards. It includes guidelines for monitoring compliance, conducting audits, and implementing necessary measures to address any identified gaps or non-compliance.
These components collectively form the foundation of a robust and effective cybersecurity policy. However, it’s important to note that each organization’s policy should be tailored to its specific needs, risks, and compliance requirements. Regular review and updates to the policy are necessary to address emerging threats and incorporate changes in technology and industry best practices.
Creating a Cybersecurity Policy
The process of creating a cybersecurity policy requires careful planning, collaboration, and consideration of the organization’s specific needs and risks. Here are the key steps to follow when creating a cybersecurity policy:
- Establish Objectives: Define the specific goals and objectives of the cybersecurity policy. Consider the organization’s size, industry, and compliance requirements to determine what needs to be protected and what potential threats need to be addressed.
- Conduct a Risk Assessment: Identify and evaluate the potential cybersecurity risks that the organization faces. Conduct a comprehensive assessment of the existing systems, networks, and data to understand vulnerabilities and prioritize areas of focus.
- Define Policy Scope: Clearly define the scope and boundaries of the policy. Determine which assets, systems, and data will be covered by the policy, and consider including any relevant third-party systems or partnerships.
- Gather Stakeholder Input: Involve key stakeholders, including management, IT staff, legal teams, and compliance officers, in the policy development process. Their input and expertise will ensure that all relevant perspectives are considered and that the policy aligns with organizational goals.
- Establish Policies and Procedures: Based on the identified risks and objectives, develop specific policies and procedures to address each area of concern. For example, create policies for data protection, access controls, incident response, and employee awareness and training.
- Document the Policy: Write the cybersecurity policy clearly and concisely, using language that is easily understandable by all employees. Organize the policy into sections and include relevant definitions, responsibilities, and guidelines. Consider using examples or templates to provide clarity and make implementation easier.
- Review and Approval: Review the policy draft with key stakeholders and subject matter experts to ensure accuracy, effectiveness, and compliance with relevant laws and regulations. Obtain management approval before finalizing the policy.
- Communicate and Train: Once the policy is finalized, communicate it to all employees, contractors, and stakeholders. Conduct training sessions or awareness campaigns to ensure that all individuals understand the policy, their roles and responsibilities, and the importance of adhering to the policy.
- Regular Review and Updates: Cybersecurity threats and technologies are constantly evolving, so it’s essential to regularly review and update the cybersecurity policy. Schedule periodic assessments to identify any gaps or areas that require improvement, and make necessary modifications to the policy as needed.
Creating a cybersecurity policy is an iterative process. It requires ongoing monitoring and adaptation to address emerging threats and technologies. By following these steps, an organization can establish a strong foundation for protecting its digital assets and minimizing the risk of cyber incidents.
Implementing a Cybersecurity Policy
Implementing a cybersecurity policy is a vital step in protecting an organization’s digital assets and ensuring a secure operating environment. The successful implementation of a cybersecurity policy involves several key actions and considerations. Here’s a step-by-step guide to effectively implement a cybersecurity policy:
- Assign Responsibility: Designate a team or individual responsible for overseeing the implementation and enforcement of the cybersecurity policy. This team should have the necessary authority and resources to carry out their responsibilities effectively.
- Create an Implementation Plan: Develop a clear plan that outlines the specific steps and milestones for implementing the cybersecurity policy. Identify key actions, assign responsible parties, and establish deadlines to ensure accountability.
- Communicate the Policy: Clearly communicate the cybersecurity policy to all employees, contractors, and stakeholders. Provide training and awareness sessions to ensure everyone understands the policy, its importance, and their obligations in adhering to it.
- Establish Security Controls: Implement the necessary security controls defined in the policy, such as firewalls, intrusion detection systems, access controls, encryption protocols, and antivirus software. Ensure that these controls are properly configured and regularly updated to maintain effectiveness.
- Monitor and Detect: Continuously monitor systems and networks for any signs of security breaches or suspicious activities. Implement monitoring tools and techniques, such as log analysis and intrusion detection systems, to identify and respond to threats promptly.
- Respond and Mitigate: Develop a comprehensive incident response plan that outlines the steps to be taken in the event of a security incident. Clearly define roles and responsibilities, establish communication channels, and conduct regular drills and exercises to test the effectiveness of the plan.
- Regularly Update and Review: Conduct periodic reviews of the cybersecurity policy and make necessary updates to address emerging threats and vulnerabilities. Stay informed about the latest cybersecurity trends and technologies to ensure the policy remains effective and up to date.
- Evaluate and Assess: Regularly assess the effectiveness of the implemented cybersecurity measures to identify any gaps or areas for improvement. Conduct security audits, penetration tests, and vulnerability assessments to stay proactive and address potential weaknesses.
- Continuous Education: Maintain a culture of security awareness and continuous education within the organization. Provide regular training sessions, security awareness campaigns, and updates on emerging threats to keep employees informed and engaged in maintaining a secure environment.
Implementing a cybersecurity policy requires coordination, commitment, and ongoing efforts. By following these steps and ensuring regular updates and assessments, organizations can enhance their security posture, mitigate risks, and protect their digital assets effectively.
Assessing and Updating a Cybersecurity Policy
Assessing and updating a cybersecurity policy is a critical process that ensures the policy remains effective in addressing emerging threats and vulnerabilities. It involves regularly evaluating the policy’s implementation, identifying any gaps or areas for improvement, and making necessary updates to stay ahead of cyber risks. Here’s a step-by-step guide to assessing and updating a cybersecurity policy:
- Establish a Review Schedule: Define a schedule for conducting regular cybersecurity policy reviews. This could be annually, biannually, or more frequently depending on the organization’s risk profile and industry regulations.
- Gather Feedback: Collect feedback from employees, contractors, and stakeholders who have implemented the cybersecurity policy. Their insights and experiences can help identify any challenges, areas that need improvement, or new cybersecurity risks that have emerged.
- Perform Risk Assessment: Conduct a comprehensive risk assessment to identify any new or evolving cyber threats. Assess the organization’s systems, networks, and data to understand vulnerabilities and potential impacts. Determine if any updates or additions are needed to address these risks.
- Stay Informed: Keep abreast of the latest cybersecurity trends, regulations, and best practices. Stay informed about new threats, attack vectors, and mitigation techniques through industry publications, security forums, and information sharing platforms.
- Collaborate with Experts: Consult with cybersecurity experts or engage a third-party security audit to conduct an independent assessment of the policy’s effectiveness. Their expertise can provide valuable insights and recommendations for enhancing security measures.
- Update Policies and Procedures: Based on the feedback, risk assessment, and latest industry knowledge, update the cybersecurity policies and procedures as necessary. Add or modify controls, revise incident response protocols, clarify roles and responsibilities, and incorporate new compliance requirements.
- Communicate Changes: Clearly communicate any updates or changes to the cybersecurity policy to all relevant stakeholders. Provide training and awareness sessions to ensure that employees understand the modified policies and their revised responsibilities.
- Test and Validate: Conduct periodic tests and simulations to validate the effectiveness of the updated policies and procedures. Perform penetration testing, vulnerability assessments, or tabletop exercises to identify any potential weaknesses and address them proactively.
- Maintain Documentation: Keep detailed records of all revisions and updates made to the cybersecurity policy. Document the rationale behind specific changes and ensure that this documentation is easily accessible for future reference or compliance audits.
- Continuous Improvement: Adopt a mindset of continuous improvement for your cybersecurity policy. Regularly monitor and assess the policy’s implementation, measure its effectiveness, and seek feedback from stakeholders to identify areas where further enhancements can be made.
Regularly assessing and updating your cybersecurity policy is crucial to ensure that it remains aligned with evolving threats, technologies, and regulatory requirements. By following these steps and staying proactive, organizations can maintain a robust and effective cybersecurity posture to safeguard their digital assets.
Conclusion
Cybersecurity is of paramount importance in today’s digital landscape, and having a well-crafted cybersecurity policy is essential for businesses of all sizes and industries. A cybersecurity policy provides clear guidelines and procedures for protecting digital assets, minimizing risks, and ensuring compliance with regulatory requirements.
Throughout this article, we have explored the key components of a cybersecurity policy, emphasized the reasons why businesses need such a policy, and provided insights into creating, implementing, and assessing a cybersecurity policy. We have discussed the importance of information security governance, risk management, access controls, data protection, network security, incident response, employee awareness and training, and compliance.
Creating a cybersecurity policy involves careful planning, collaboration, and consideration of the organization’s specific needs and risks. It is essential to establish objectives, conduct a risk assessment, define the policy scope, gather stakeholder input, establish policies and procedures, document the policy, review and gain approval, communicate and train, and regularly review and update the policy.
Implementing a cybersecurity policy entails assigning responsibility, creating an implementation plan, communicating the policy, establishing security controls, monitoring and detecting, responding and mitigating, regularly updating and reviewing, and maintaining continuous education and awareness within the organization.
Assessing and updating a cybersecurity policy is an ongoing process that involves establishing a review schedule, gathering feedback, performing risk assessments, staying informed about the latest trends, collaborating with experts, updating policies and procedures, communicating changes, testing and validating, maintaining documentation, and striving for continuous improvement.
In conclusion, a solid cybersecurity policy is a critical component in safeguarding an organization’s digital assets, protecting against cyber threats, and maintaining trust with stakeholders. By following industry best practices, regularly reviewing and updating the policy, and fostering a culture of security awareness, businesses can effectively mitigate cyber risks, enhance resilience, and safeguard their valuable digital resources.