Introduction
Cybersecurity encompasses the measures and practices undertaken to protect computer systems, networks, and data from unauthorized access, cyber threats, and attacks. With the ever-increasing reliance on technology and the proliferation of interconnected devices, the importance of robust cybersecurity measures cannot be overstated. It is crucial for individuals, businesses, and organizations to understand the various aspects of cybersecurity and how they contribute to ensuring the confidentiality, integrity, and availability of data.
Many people associate cybersecurity solely with preventing data breaches or thwarting hacking attempts. While these are indeed important components of cybersecurity, it is essential to recognize that cybersecurity extends far beyond these concerns. It encompasses a wide range of areas and disciplines, each serving a specific purpose in safeguarding sensitive information and ensuring the smooth operation of digital systems.
This article will explore and provide an overview of different aspects that fall under the umbrella of cybersecurity, highlighting the key areas that individuals and organizations need to focus on to effectively protect their digital assets and maintain a secure online environment.
Network Security
Network security is a fundamental aspect of cybersecurity that focuses on protecting the transmission and exchange of data within a network. It involves implementing measures to prevent unauthorized access, data breaches, and attacks on network infrastructure, such as routers, switches, firewalls, and servers.
One of the primary objectives of network security is to establish secure communication channels and ensure that data transmitted between devices remains confidential and unaltered. This is achieved through various mechanisms, such as encryption protocols like SSL/TLS, virtual private networks (VPNs), and intrusion detection and prevention systems (IDS/IPS).
To enhance network security, organizations often deploy firewall systems that monitor and filter network traffic, allowing only authorized connections while blocking potential threats. Network segmentation, by dividing a network into smaller, isolated subnetworks, further strengthens security by limiting the potential impact of a breach or attack.
Network security also involves implementing strong access control mechanisms, such as secure authentication methods (e.g., two-factor authentication), to ensure that only authorized users can access network resources. Additionally, regular network vulnerability assessments and penetration testing help identify and address potential weaknesses in the network infrastructure.
In today’s interconnected world, where remote work and cloud services are prevalent, securing wireless networks becomes imperative. Implementing Wi-Fi security protocols, such as Wi-Fi Protected Access (WPA) or WPA2, helps protect against unauthorized access and data interception.
Network security is continuously evolving to keep pace with emerging threats. It requires regular monitoring, updating of security systems, and staying updated with the latest vulnerabilities and best practices. By implementing comprehensive network security measures, organizations can significantly reduce the risk of network breaches, data leaks, and unauthorized access, ensuring the integrity and privacy of their network infrastructure and data.
Application Security
Application security focuses on protecting software applications from potential security vulnerabilities and ensuring that they operate securely throughout their lifecycle. As software applications become increasingly complex, application security has become a critical aspect of cybersecurity.
One of the primary objectives of application security is to identify and mitigate vulnerabilities that could be exploited by attackers. This includes both design flaws and coding errors that can lead to security breaches. Application security practices involve implementing secure coding practices, performing thorough code reviews, and conducting application security testing.
Secure coding practices involve following coding standards and guidelines that address common security pitfalls, such as input validation, output encoding, and error handling. By adhering to secure coding practices, developers can minimize the risk of introducing vulnerabilities into the application’s codebase.
Code reviews are essential for identifying and fixing security issues. They involve a thorough examination of the application’s source code to detect vulnerabilities, such as SQL injection, cross-site scripting (XSS), or buffer overflow. Code review can be done manually or through automated tools that can help detect common coding errors and potential vulnerabilities.
Application security testing is another critical aspect of securing applications. It involves conducting various types of tests, including penetration testing and vulnerability scanning, to identify and address potential security weaknesses. Penetration testing simulates real-world attacks to evaluate the application’s resilience to different types of threats, while vulnerability scanning helps identify known vulnerabilities in software components.
In addition to proactive measures, application security also involves ongoing maintenance and updates to address the ever-evolving security landscape. This includes promptly applying security patches, keeping software dependencies up to date, and regularly monitoring and auditing applications for potential vulnerabilities.
By prioritizing application security, organizations can significantly reduce the risk of exploits and breaches that could compromise their systems and sensitive data. A comprehensive application security program incorporates secure coding practices, thorough code reviews, and regular testing and maintenance to ensure that applications remain resilient to ever-changing threats.
Information Security
Information security is a crucial aspect of cybersecurity that focuses on protecting sensitive and valuable data from unauthorized access, disclosure, alteration, destruction, or theft. It encompasses the policies, processes, and technologies used to ensure the confidentiality, integrity, and availability of information.
One of the key elements of information security is data classification. Organizations classify their data based on its sensitivity and implement appropriate security controls accordingly. This includes identifying and labeling sensitive data, such as personally identifiable information (PII), financial data, or intellectual property, and restricting access to authorized individuals.
Encryption plays a vital role in information security. It involves converting data into a coded form that can only be decrypted and understood by authorized recipients. Encryption protects data during storage, transmission, and processing, making it unreadable and useless to unauthorized individuals who might intercept or access it.
Access control is another critical aspect of information security. It involves enforcing policies and mechanisms to ensure that only authorized users have access to specific data and resources. This includes implementing user authentication mechanisms, such as passwords, multi-factor authentication, or biometric authentication, and role-based access controls (RBAC) to determine levels of access based on job roles and responsibilities.
Data backup and disaster recovery planning are essential components of information security. Regularly backing up data and implementing robust disaster recovery plans help ensure that critical information can be restored in the event of data loss or system disruptions caused by natural disasters, hardware failures, or cyber-attacks.
Information security also encompasses the protection of digital systems and networks from malware, unauthorized access attempts, and other cyber threats. This involves deploying security technologies such as firewalls, intrusion detection systems (IDS), antivirus software, and secure web gateways.
Employee training and awareness are critical in maintaining information security. Educating employees about security best practices, social engineering attacks, and data handling policies helps create a security-conscious culture within an organization and reduces the risk of human errors or negligence that can lead to security breaches.
In an ever-evolving cyber threat landscape, information security must be a continuous and proactive effort. Regular security assessments, vulnerability scanning, and penetration testing are essential to identify and address potential weaknesses in an organization’s information security infrastructure.
By implementing robust information security measures and adopting a holistic approach, organizations can protect their valuable data, safeguard their reputation, and maintain the trust of customers and stakeholders.
Operational Security
Operational security, also known as OPSEC, is a crucial aspect of cybersecurity that focuses on protecting sensitive information related to an organization’s operations and activities. It involves implementing procedures and safeguards to prevent the compromise of critical information that could be exploited by malicious actors.
Operational security begins with the identification and assessment of critical assets and processes within an organization. This includes identifying key personnel, sensitive data, infrastructure, and operational workflows that, if compromised, could have a significant impact on the organization’s operations or overall security posture.
One of the main goals of operational security is to prevent the leakage of sensitive information through various means, including physical, electronic, or human channels. This involves implementing strict access controls to limit access to critical infrastructure, data, and facilities only to authorized personnel. It also includes employing robust authentication mechanisms, monitoring systems, and CCTV surveillance to detect and deter unauthorized access or suspicious activities.
Organizations also implement secure disposal procedures for sensitive information. Proper disposal of physical documents, including shredding or incineration, and secure erasure of data from electronic devices are essential to prevent the retrieval or reconstruction of discarded information by malicious parties.
Operational security also encompasses the protection of information during the transmission and sharing of data with external parties. This includes implementing secure communication protocols, such as encrypted emails or secure file transfer mechanisms, to protect sensitive information from eavesdropping or interception.
Employee training and awareness play a significant role in operational security. Training programs educate employees about the importance of safeguarding sensitive information, detecting social engineering attacks, and recognizing potential indicators of compromise. By fostering a culture of security consciousness and accountability, organizations can effectively mitigate the risk of insider threats and unintentional disclosures.
Regular security audits, vulnerability assessments, and incident response planning are crucial elements of operational security. These practices help detect vulnerabilities, assess the effectiveness of security controls, and ensure that appropriate measures are in place to respond to security incidents and breaches.
Operational security is an ongoing effort that requires continuous monitoring, assessment, and adaptation to evolving threats. By implementing robust operational security practices, organizations can protect critical assets, maintain business continuity, and preserve the confidentiality, integrity, and availability of sensitive information.
Physical Security
Physical security is an essential component of cybersecurity that focuses on protecting physical assets, facilities, and resources from unauthorized access, theft, vandalism, or damage. While digital security measures are crucial, physical security measures are equally important to safeguard sensitive information and ensure the overall security of an organization.
Physical security measures include controlling access to buildings, rooms, and sensitive areas within an organization. This can be achieved through the use of physical barriers such as fences, walls, gates, and access control systems like keycards, biometric scanners, or security guards. By limiting access to authorized personnel, organizations can prevent unauthorized individuals from physically accessing critical areas.
Video surveillance is another important aspect of physical security. It involves the use of closed-circuit television (CCTV) cameras strategically placed to monitor and record activities within and around facilities. Video surveillance not only acts as a deterrent but also provides evidence in the event of security incidents or breaches.
Organizations also employ security personnel, such as guards or patrols, to monitor and enforce security measures. These personnel are trained to identify and respond to potential threats, suspicious activities, or breaches of physical security.
In addition to access control and surveillance, physical security measures may also include securing computer systems and network infrastructure physically. This involves protecting servers, data centers, and other sensitive equipment from theft, tampering, or damage. Measures can include locked cabinets, secure server rooms, and environmental controls to prevent damage from factors like fire or water.
Emergency preparedness is an essential aspect of physical security. Organizations must have plans in place for responding to emergencies such as fires, natural disasters, or security incidents. These plans include protocols for evacuations, emergency notifications, medical assistance, and business continuity to minimize the impact of disruptions on operations and personnel safety.
Physical security measures should be regularly reviewed, updated, and tested to ensure their effectiveness. This includes conducting security risk assessments, evaluating vulnerabilities, and making necessary improvements to address gaps or emerging threats.
Integrating physical security with digital security measures is crucial for maintaining a comprehensive cybersecurity strategy. By combining physical and digital security measures, organizations can create a multi-layered defense system that provides a robust and holistic approach to protecting their assets, facilities, and sensitive information.
Endpoint Security
Endpoint security refers to the protection of end-user devices, such as laptops, desktops, smartphones, and tablets, from potential security threats. As endpoints are often the entry points for cyber-attacks, ensuring their security is a critical aspect of cybersecurity.
Endpoint security measures aim to prevent unauthorized access, data breaches, malware infections, and the spread of malicious software across devices and networks. These measures include deploying antivirus and anti-malware software that can detect and block known threats, as well as protect against emerging threats.
Endpoint security also involves implementing strong access controls, such as user authentication mechanisms, to ensure that only authorized individuals can access devices and the sensitive data stored on them. This can include the use of strong passwords, multi-factor authentication, or biometric authentication methods.
Regular software patching and updates are crucial for endpoint security. Keeping operating systems, applications, and firmware up to date with the latest security patches helps address known vulnerabilities and close potential entry points for attackers.
Data encryption is an essential aspect of endpoint security. By encrypting data at rest and in transit, organizations can ensure that even if a device is lost, stolen, or intercepted, the data remains unreadable and unusable to unauthorized individuals.
Endpoint security measures also include implementing mobile device management (MDM) solutions to secure and manage smartphones and tablets used within an organization. MDM allows for remote device configuration, data wiping, and enforcing security policies to protect sensitive data on mobile endpoints.
Endpoint security is not limited to work devices; it also extends to personal devices used for work purposes (BYOD – Bring Your Own Device) within organizations. Implementing policies and security controls that govern the use of personal devices helps mitigate the risk of unauthorized access and data breaches.
Regular monitoring and incident response are crucial aspects of endpoint security. By monitoring endpoint activity, organizations can detect and respond to potential threats or suspicious behavior in real-time. This includes implementing intrusion detection systems (IDS) or security information and event management (SIEM) solutions to centralize and analyze endpoint security logs.
Endpoint security should be complemented with user awareness and training programs. Educating users about best practices, such as avoiding suspicious websites, not clicking on unknown links, and being vigilant about phishing attacks, helps strengthen the overall security posture of endpoints.
By implementing robust endpoint security measures, organizations can significantly reduce the risk of compromised devices, data breaches, and unauthorized access to sensitive information. Endpoint security plays a critical role in protecting both the devices and the data they contain, contributing to a comprehensive cybersecurity strategy.
Cloud Security
Cloud security focuses on protecting data, applications, and infrastructure that are hosted in cloud environments. As organizations increasingly rely on cloud computing services for storage, data processing, and application hosting, ensuring the security of these cloud environments becomes crucial for maintaining the confidentiality, integrity, and availability of data.
One of the primary concerns in cloud security is securing data stored in the cloud. Organizations must assess the security practices and measures implemented by their cloud service providers. This includes data encryption at rest and in transit, access controls, and regular security audits to ensure compliance with industry standards and regulations.
Access management is another critical aspect of cloud security. This involves implementing strong authorization mechanisms and identity and access management (IAM) controls to ensure that only authorized individuals can access cloud resources. It also includes regular monitoring and auditing of user activity to detect any suspicious or unauthorized access attempts.
Data privacy is an important consideration in cloud security. Organizations need to understand the privacy policies of their cloud service providers and ensure compliance with applicable data protection laws. They should also implement measures to protect sensitive data, such as personally identifiable information (PII), and have clear policies in place for data handling, retention, and destruction.
Securing cloud infrastructure is vital to prevent unauthorized access or attacks on cloud resources. This involves implementing strong network security measures, such as firewalls, intrusion detection and prevention systems (IDS/IPS), and continuous vulnerability assessments. Regular updates, patch management, and security configurations are essential to address potential vulnerabilities in the cloud infrastructure.
Business continuity and disaster recovery planning are crucial components of cloud security. Organizations should have backup and recovery measures in place to ensure the availability and resilience of data and applications hosted in the cloud. This includes regularly testing and auditing these measures to ensure their effectiveness in the event of a system failure or disruption.
Cloud security also requires ongoing threat monitoring and incident response. Implementing security information and event management (SIEM) systems and intrusion detection systems (IDS) helps detect and respond to potential security breaches or malicious activities in the cloud environment. Timely incident response and investigation are essential to mitigate the impact of security incidents and prevent future incidents.
Employee awareness and training play a significant role in maintaining cloud security. Educating employees about best practices, such as using strong passwords, avoiding phishing attempts, and understanding their roles and responsibilities in safeguarding cloud resources, helps reduce the risk of human errors and social engineering attacks.
By implementing robust cloud security measures, organizations can confidently leverage cloud computing services while ensuring the protection of their data, applications, and infrastructure. Cloud security is a shared responsibility between the organization and the cloud service provider, and maintaining a strong security posture requires ongoing collaboration and vigilance.
Mobile Security
Mobile security focuses on protecting mobile devices, such as smartphones and tablets, and the sensitive data stored on them from various security threats. As mobile devices have become an integral part of our lives, ensuring their security is essential in maintaining the confidentiality, integrity, and availability of data.
One of the primary concerns in mobile security is securing the device itself. This includes implementing strong authentication mechanisms, such as PIN codes, passwords, biometric authentication, or pattern locks, to prevent unauthorized access to the device. Remote wipe capabilities are important for lost or stolen devices, allowing the user to erase all data remotely to prevent it from falling into the wrong hands.
Securing mobile applications is crucial in mobile security. Developers should follow secure coding practices and implement proper security controls to prevent common vulnerabilities such as data leakage, insecure data storage, or inadequate encryption. Mobile app users should also be cautious when downloading apps and only install from reputable sources to minimize the risk of downloading malicious or compromised applications.
Mobile devices often connect to public Wi-Fi networks, which present security risks. It is imperative to use secure Wi-Fi networks with encryption and avoid accessing sensitive information or conducting financial transactions on unsecured or public networks. Using a virtual private network (VPN) can add an extra layer of security by encrypting data transmitted between the device and the network.
Mobile malware is a growing concern in mobile security. Attackers target mobile devices through malicious applications, often disguised as legitimate apps, or through phishing attempts via text messages or emails. It is essential to regularly update and maintain security software on the device, including antivirus and anti-malware applications, to detect and eliminate potential threats.
Mobile security also involves securing mobile data in transit. Implementing secure communication protocols, such as encrypted email or secure messaging apps, helps protect sensitive information from interception or unauthorized access. It is also crucial to avoid clicking on suspicious links or opening attachments from unknown sources to mitigate the risk of phishing or other social engineering attacks.
Regularly updating the mobile operating system and applications is vital to address known vulnerabilities. Software updates often include security patches that fix vulnerabilities and protect against potential exploits. It is recommended to enable automatic updates or regularly check for updates manually to ensure the device is running the latest, most secure versions of software.
User education and awareness are crucial in mobile security. Educating users about best practices, such as avoiding downloading apps from third-party sources, being cautious of suspicious links or attachments, and regularly backing up data, helps mitigate the risk of security breaches and data loss.
By implementing strong security measures on mobile devices, regularly updating software, being cautious of potential threats, and educating users on best practices, individuals and organizations can enhance mobile security and protect sensitive data and information from unauthorized access or compromise.
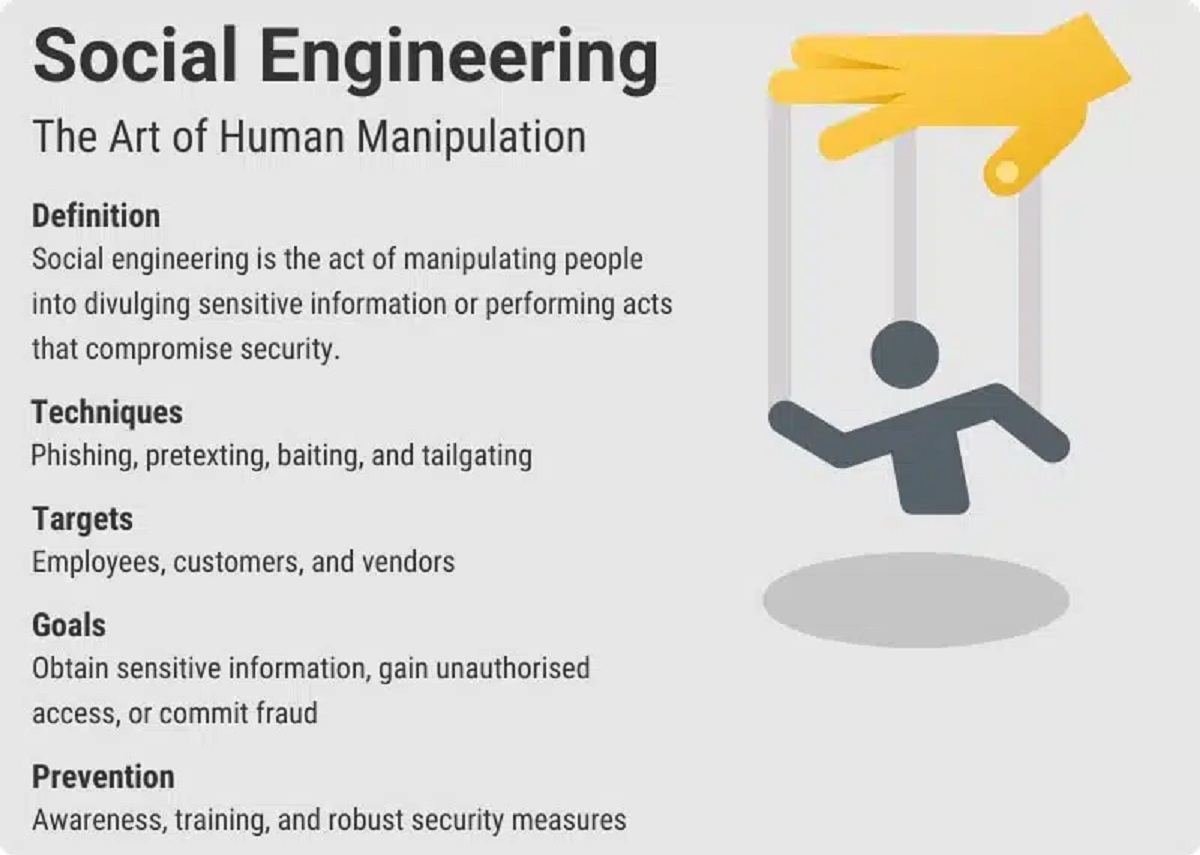
Social Engineering
Social engineering is a technique used by attackers to manipulate individuals into divulging sensitive information or performing actions that may compromise the security of systems or data. Unlike traditional hacking methods that focus on exploiting technical vulnerabilities, social engineering relies on psychological manipulation and deception to exploit human trust and gullibility.
There are various forms of social engineering, including phishing, pretexting, baiting, and tailgating. Phishing is the most common method, where attackers use fraudulent emails or websites that appear legitimate to trick individuals into revealing confidential information, such as passwords or financial details.
Pretexting involves the attacker impersonating a trusted individual or organization to elicit personal or sensitive information. This can range from posing as a company representative to gain access to restricted areas or pretending to be a colleague in need of assistance to deceive someone into performing an action that benefits the attacker.
Baiting involves enticing individuals with something desirable, such as a free USB drive or a tempting offer, to get them to unknowingly install malware on their device or divulge sensitive information.
Tailgating is when an attacker gains physical access to a secured area by following closely behind an authorized individual and taking advantage of their trust and assumption that the person belongs there.
Protecting against social engineering attacks requires a combination of technology and user vigilance. Organizations should implement robust cybersecurity measures, such as email filtering, web filtering, and employee training on recognizing and reporting potential social engineering attempts.
Employee education plays a critical role in mitigating the risk of social engineering attacks. Regular training and awareness programs can help employees recognize and avoid common social engineering tactics, such as verifying the authenticity of requests, being cautious of unsolicited emails, and ensuring they are following established protocols for information sharing.
It is important to maintain a healthy level of skepticism and to verify the identity and authenticity of individuals or requests before disclosing information or performing actions. Organizations should establish clear protocols for verifying and validating requests, especially those involving sensitive data or financial transactions.
Mobile users should be particularly cautious about social engineering attacks, as smartphones often contain a wealth of personal and sensitive information. Users should be aware of the risks associated with downloading apps from unknown sources, clicking on suspicious links, or sharing personal information without verifying the legitimacy of the request.
Social engineering attacks are constantly evolving, and attackers continue to find new ways to exploit human vulnerabilities. By fostering a culture of security awareness, implementing strong security measures, and providing ongoing education and training, individuals and organizations can defend against social engineering attacks and protect sensitive information from falling into the wrong hands.