Introduction
With the increasing need for privacy and security in today’s digital world, virtual private networks (VPNs) have become an essential tool for internet users. VPNs allow users to establish a secure connection to the internet by creating an encrypted tunnel between their device and the VPN server. This tunneling process plays a crucial role in ensuring the confidentiality and integrity of the data transmitted over the network.
In this article, we will explore what tunneling is and how it is accomplished in a VPN. We will also discuss the different VPN protocols that utilize tunneling and the security measures associated with it.
A VPN, in simple terms, is a service that enables users to access the internet privately and securely. It creates a virtual encrypted tunnel through which all internet traffic passes, keeping it protected from unauthorized access and surveillance.
Tunneling, on the other hand, refers to the process of encapsulating or packaging data within another data packet to facilitate its secure transmission over a network. It allows the VPN to provide a secure and private connection even when using a public or untrusted network, such as a public Wi-Fi hotspot.
By encrypting the data packets and sending them through the tunnel, a VPN ensures that any sensitive information, such as passwords, credit card details, or personal communications, cannot be intercepted or accessed by malicious individuals or organizations.
Now let’s delve deeper into how tunneling works in a VPN and explore the different protocols used.
What is a VPN?
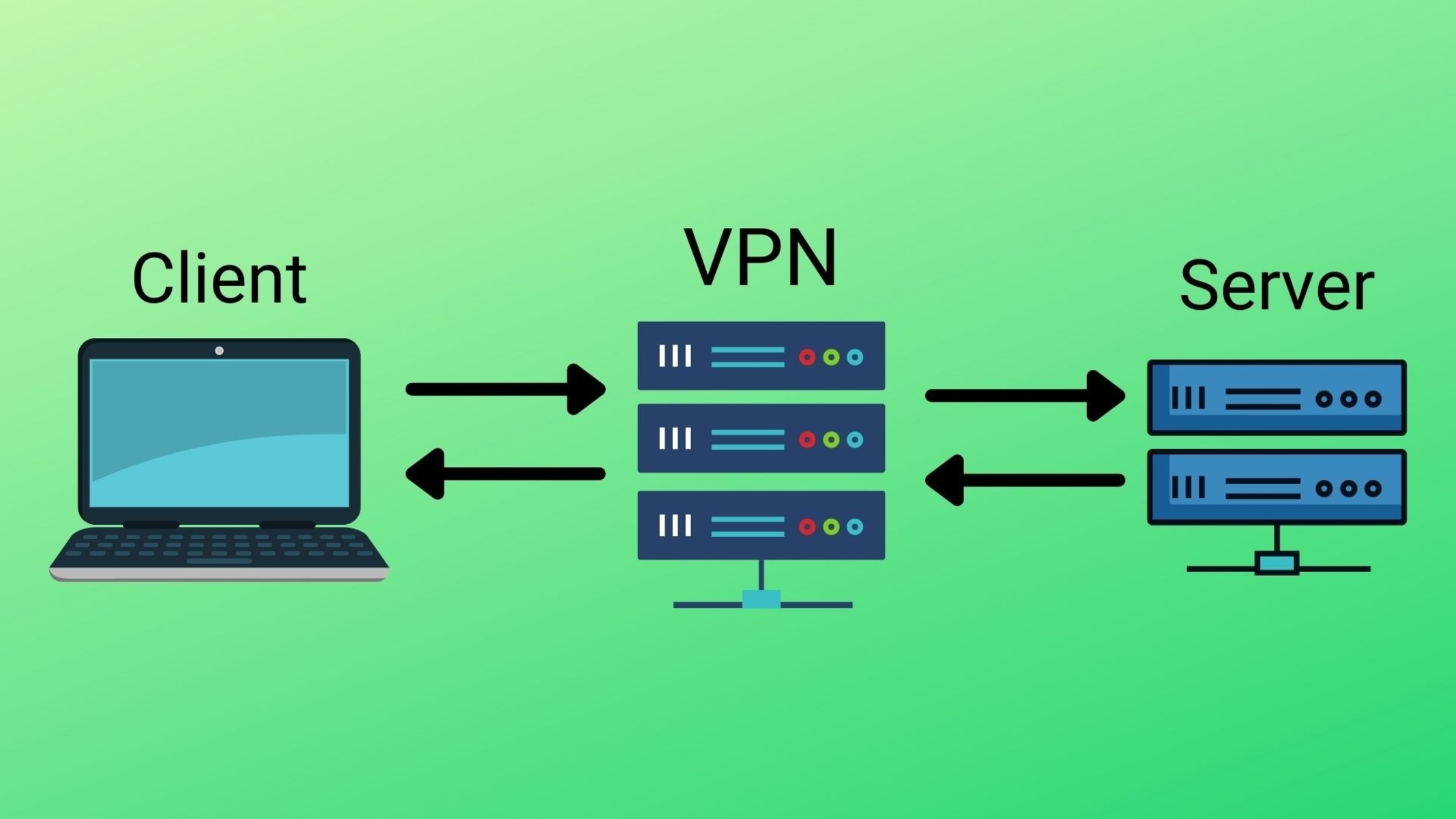
A VPN, which stands for Virtual Private Network, is a technology that allows users to establish a secure and private connection to the internet. It creates a secure tunnel between the user’s device and the VPN server, encrypting all the data that flows through it. This ensures that sensitive information remains confidential and protected from unauthorized access.
When we connect to the internet without a VPN, our data is typically transmitted through our Internet Service Provider (ISP) and can be intercepted or monitored by third parties, such as hackers, government agencies, or even our own ISP. This lack of privacy raises concerns about our online security and the protection of our personal information.
A VPN addresses these concerns by providing several key benefits:
- Security: VPNs use encryption to protect a user’s data, making it unreadable to anyone who might intercept it. This ensures that sensitive information, such as passwords, financial transactions, or personal communications, remains secure.
- Privacy: When using a VPN, our real IP address is hidden, and our internet traffic appears to be originating from the VPN server. This makes it difficult for anyone to track our online activities or identify our location.
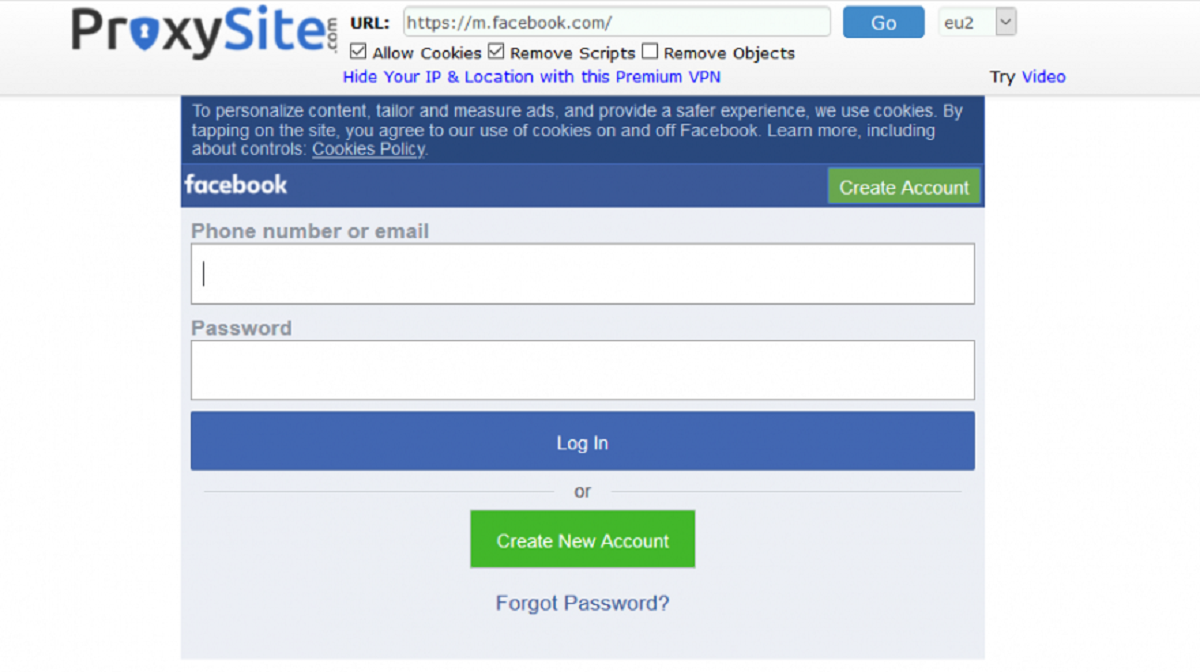
- Access to Restricted Content: VPNs can be used to bypass geographical restrictions and access content that may be blocked or censored in certain regions. By connecting to a VPN server in a different location, users can appear as if they are browsing from that region, allowing them to access region-restricted websites, streaming services, or social media platforms.
- Anonymity: VPNs provide a layer of anonymity by masking our online identity. By using a VPN, we can browse the internet without leaving behind a digital footprint that could be traced back to us.
- Protection on Public Wi-Fi: When connected to a public Wi-Fi network, our data is vulnerable to interception and hacking attempts. By using a VPN, we can ensure that our internet traffic is encrypted and protected, even on unsecured Wi-Fi networks.
In summary, a VPN is a powerful tool for enhancing online security, privacy, and freedom. It creates a secure tunnel between the user’s device and the VPN server, encrypting all data that flows through it. By utilizing a VPN, users can protect their sensitive information, maintain their privacy, and access restricted content, all while enjoying a secure and private internet browsing experience.
What is Tunneling?
Tunneling is a fundamental concept in networking that involves encapsulating one network protocol within another network protocol. It allows for the secure and efficient transmission of data packets over an intermediate network, such as the internet, by creating a virtual tunnel between the sender and the receiver.
When data is sent over a network, it is divided into smaller units called packets. Each packet contains a header, which includes information such as the source and destination IP addresses, as well as the payload, which is the actual data being transmitted.
In a typical network transmission, these packets are delivered based on their destination IP address. However, in the context of tunneling, the original packet is encapsulated within a new packet that uses a different network protocol. This allows the encapsulated packet to be transmitted over a network that may not natively support the original protocol.
For example, in the case of a VPN, tunneling is used to create a secure connection between the user’s device and the VPN server. The user’s data packets are encapsulated within a new packet using a secure protocol, such as IPsec or OpenVPN. This encapsulated packet is then transmitted through the public internet, effectively creating a secure tunnel for the data to travel through.
Tunneling works by adding a new header to the original packet, which includes the necessary information for the tunneling process. This new header contains the source and destination IP addresses of the tunnel endpoints, as well as any additional information required by the tunneling protocol being used.
At the receiving end of the tunnel, the encapsulated packet is decapsulated, removing the additional header and extracting the original packet. The inner packet is then processed and delivered to its intended destination based on its original headers.
In addition to VPNs, tunneling is also used in other network technologies, such as IPv6 transition mechanisms, where IPv6 packets are encapsulated within IPv4 packets to traverse IPv4-only networks.
Overall, tunneling is a crucial process in networking that allows for the secure and efficient transmission of data packets over intermediate networks. It enables the use of various protocols and technologies to coexist and communicate seamlessly, providing enhanced security and connectivity in a variety of networking scenarios.
How does Tunneling Work in a VPN?
When it comes to VPNs, tunneling is the method by which a secure connection is established between the user’s device and the VPN server. It involves encapsulating the user’s data packets within a secure protocol to create a virtual tunnel through which the data can safely travel.
Here is a step-by-step breakdown of how tunneling works in a VPN:
- Establishing a Connection: The user initiates a connection to the VPN server using a VPN client or app. The client software establishes a connection with the server, usually through a process known as a handshake.
- Tunneling Protocol Selection: Once the connection is established, the user’s device and the VPN server negotiate which tunneling protocol will be used. There are various protocols available, such as IPsec, OpenVPN, L2TP/IPsec, and PPTP, each with its own strengths and encryption methods.
- Encryption and Encapsulation: Once the tunneling protocol is agreed upon, the user’s data packets are encapsulated within the protocol’s headers. This process involves adding an additional layer of encryption and authentication to protect the data from any potential interception.
- Transmission through the Tunnel: The encapsulated packets are transmitted through the established tunnel between the user’s device and the VPN server. This tunnel acts as a secure conduit, shielding the data from being accessed or tampered with by unauthorized parties.
- Decapsulation at the Server: Upon reaching the VPN server, the encapsulated packets are received and undergo decapsulation. This process involves removing the outer layer of encryption and authentication added during encapsulation, leaving behind the original data packets.
- Routing and Delivery: Once the packets are decapsulated, they are processed by the VPN server. The server assigns a new IP address to the packets, making the user’s traffic appear as if it is originating from the VPN server rather than the user’s device. The packets are then routed to their intended destination on the internet.
Tunneling in a VPN ensures that the user’s data is protected by encryption, making it unreadable to anyone who might intercept it. It also provides anonymity by masking the user’s true IP address, making it difficult to track their online activities.
It’s worth noting that different VPN protocols and configurations offer varying levels of security, speed, and compatibility. When selecting a VPN service, it’s essential to consider your specific needs and choose a provider that offers a secure and reliable tunneling protocol that fits your requirements.
In summary, tunneling in a VPN involves encapsulating the user’s data packets within a secure protocol, creating a virtual tunnel through which the data can securely travel. This process ensures the privacy, security, and anonymity of the user’s internet connection, allowing them to browse the web with peace of mind.
VPN Protocols that Use Tunneling
Various VPN protocols utilize tunneling to establish secure connections between the user’s device and the VPN server. Each protocol offers different features, levels of security, and compatibility with different devices and networks. Here are some commonly used VPN protocols that make use of tunneling:
- IPsec (Internet Protocol Security): IPsec is a widely used VPN protocol that provides strong security through encryption and authentication mechanisms. It operates at the network layer (Layer 3) of the OSI model and can be used in both transport mode (only encrypting the data payload) or tunnel mode (encrypting the entire IP packet). IPsec is compatible with various encryption algorithms and can be implemented using different authentication methods.
- OpenVPN: OpenVPN is an open-source VPN protocol known for its flexibility and ease of use. It uses SSL/TLS encryption to secure the connection and can operate on multiple ports, making it more difficult for firewalls to block. OpenVPN is highly configurable and can be used on various operating systems, including Windows, macOS, Linux, and mobile devices.
- L2TP/IPsec (Layer 2 Tunneling Protocol over IPsec): L2TP is often combined with IPsec to provide a secure VPN connection. L2TP/IPsec operates at the data link layer (Layer 2) of the OSI model and uses IPsec to provide encryption and authentication. While L2TP/IPsec offers good security, it may encounter compatibility issues due to its reliance on specific ports and protocols.
- PPTP (Point-to-Point Tunneling Protocol): PPTP is one of the oldest VPN protocols and is widely supported across various platforms. It operates at the data link layer (Layer 2) and provides relatively fast speeds due to its less resource-intensive encryption. However, PPTP has known security vulnerabilities and is not recommended for sensitive data or high-security applications.
- WireGuard: WireGuard is a newer and lightweight VPN protocol that focuses on simplicity and performance. It uses modern cryptographic methods to establish secure connections and aims to provide improved speed and efficiency compared to other protocols. WireGuard is gaining popularity due to its ease of use, strong security, and cross-platform compatibility.
These are just a few examples of VPN protocols that use tunneling to create secure connections. It’s important to consider the specific features and security aspects of each protocol when choosing a VPN service. Additionally, some VPN providers may offer their own proprietary protocols or custom implementations, so it’s essential to review their documentation and security practices to make an informed decision.
Ultimately, the choice of VPN protocol depends on factors such as security requirements, compatibility, speed, and the specific use case. By selecting the appropriate VPN protocol, users can ensure a secure and reliable connection while enjoying the benefits of a virtual private network.
Security in Tunneling
Security is a vital aspect of tunneling in a VPN. The encapsulation of data packets within a secure tunnel ensures that sensitive information remains confidential and protected from unauthorized access. Let’s explore the security measures employed in tunneling:
Encryption: One of the primary security measures in tunneling is encryption. When data packets are encapsulated within the tunnel, they are encrypted, making it extremely difficult for anyone to intercept and decipher the information. Encryption algorithms, such as AES (Advanced Encryption Standard) or 3DES (Triple Data Encryption Standard), are employed to scramble the data and ensure its confidentiality.
Authentication: Authentication is another crucial component of tunneling security. It ensures that only authorized parties can access and transmit data through the tunnel. VPN protocols use various authentication methods, such as digital certificates, pre-shared keys, or username and password combinations, to verify the identities of both the VPN server and the user’s device.
Data Integrity: Tunneling also ensures the integrity of the transmitted data. By using cryptographic hashing algorithms, such as SHA-256 (Secure Hash Algorithm 256-bit), the VPN protocol verifies that the data packets have not been tampered with during transmission. This protects against unauthorized modifications or alterations to the data, providing assurance that the information received is identical to the information sent.
Security Protocols: VPN protocols that employ tunneling, such as IPsec and OpenVPN, incorporate additional security features to enhance the overall security of the tunnel. These protocols establish secure connections using cryptographic keys, negotiate the encryption algorithms and authentication methods, and implement measures to prevent replay attacks or unauthorized access. They prioritize the security of the tunnel to ensure the protection of sensitive data.
Firewall Bypass: Tunneling can help bypass network firewalls or restrictions that may be in place, allowing users to access blocked websites or services. By encapsulating the data within a different network protocol, VPNs can effectively bypass network filters and provide users with unrestricted access to the internet. However, it’s important to note that the use of VPNs to bypass firewalls or restrictions may be subject to the laws and policies of the specific jurisdiction.
By implementing these security measures, tunneling in a VPN ensures that data transmission remains secure and protected from potential threats. It allows users to browse the internet, access resources, and communicate with confidence, knowing that their sensitive information is shielded from unauthorized access or interception.
Benefits of Tunneling in a VPN
Tunneling is a critical component of Virtual Private Networks (VPNs) that provides numerous benefits to users seeking enhanced privacy, security, and accessibility. Let’s explore some of the key advantages of tunneling in a VPN:
1. Secure Data Transmission: Tunneling in a VPN ensures that all data transmitted between the user’s device and the VPN server is encrypted and protected. This encryption prevents unauthorized parties from intercepting and accessing sensitive information, such as passwords, financial data, or personal communications.
2. Privacy Protection: By encapsulating data packets within a secure tunnel, VPN tunneling hides the user’s original IP address and replaces it with the IP address of the VPN server. This helps to preserve anonymity and protect privacy, making it difficult for anyone to track the user’s online activities or identify their location.
3. Bypassing Geo-restrictions: Tunneling allows users to bypass geographical restrictions and access content that may be blocked or censored in their region. By connecting to a VPN server located in a different country, users can appear as if they are browsing from that location, granting them access to region-locked websites, streaming services, or social media platforms.
4. Protection on Public Wi-Fi: Public Wi-Fi networks are often unsecured, leaving users vulnerable to hacking attempts or data interception. Tunneling in a VPN ensures that all data transmitted between the user’s device and the VPN server is encrypted, even when connected to an unsecured Wi-Fi network. This protects sensitive information from being intercepted by malicious individuals.
5. Enhanced Security on Any Network: Whether connected to a home network, workplace network, or public network, tunneling in a VPN ensures that data is transmitted securely. This is especially crucial when using public or untrusted networks, as VPN tunneling adds an extra layer of protection against potential security risks.
6. Versatility and Compatibility: VPN tunneling protocols, such as IPsec, OpenVPN, and WireGuard, are compatible with a wide range of devices and operating systems. This allows users to enjoy the benefits of tunneling on multiple devices, including computers, smartphones, tablets, and even routers.
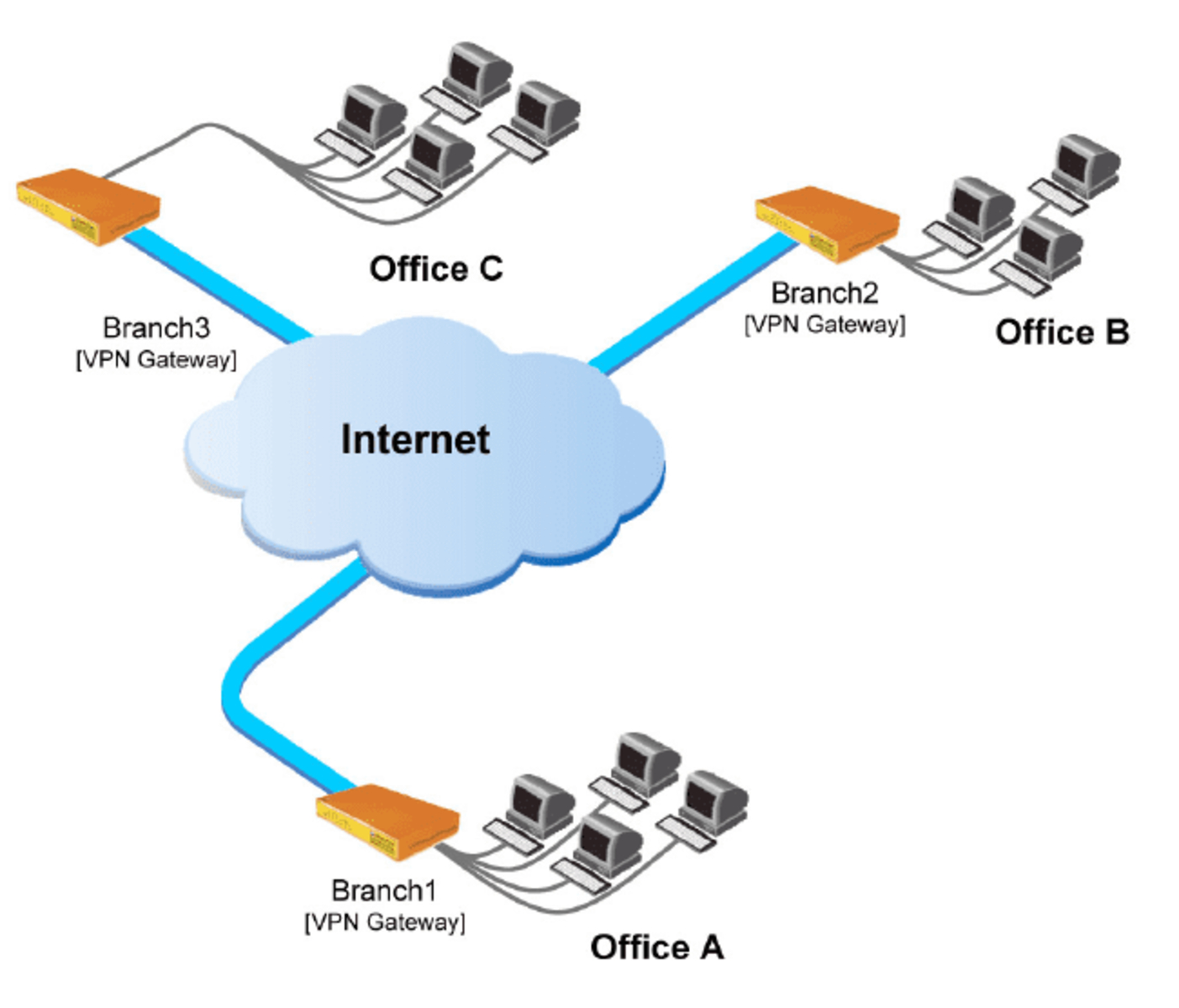
7. Business Applications: Tunneling in a VPN is not only beneficial for individual users but also for businesses. VPN tunneling allows employees to securely access company resources from remote locations, promoting remote work flexibility without compromising security. It also enables secure communication between different branches or offices of a company.
The benefits of tunneling in a VPN primarily revolve around increased privacy, data security, and online accessibility. By utilizing tunneling protocols, VPNs empower users to take control of their online experience, ensuring that their data remains confidential and protected, while also offering the freedom to bypass restrictions and access global content.
Conclusion
Tunneling plays a crucial role in the functionality and security of Virtual Private Networks (VPNs). By encapsulating data within a secure protocol and creating a virtual tunnel, VPNs ensure that users can enjoy a private, encrypted, and secure connection to the internet.
In this article, we explored the concept of tunneling in VPNs and its importance in maintaining privacy and security. Tunneling protocols like IPsec, OpenVPN, L2TP/IPsec, and WireGuard utilize encryption, authentication, and encapsulation to safeguard data transmissions. These protocols offer various levels of compatibility, security, and speed, allowing users to choose the right VPN solution to meet their specific needs.
Tunneling in a VPN provides numerous benefits, including secure data transmission, protection of privacy, bypassing geo-restrictions, enhanced security on public Wi-Fi networks, compatibility across devices, and valuable business applications. By encrypting data packets and routing them through a virtual tunnel, VPNs empower individuals and businesses to safeguard sensitive information, maintain anonymity, and access global content with ease.
As the need for privacy and security in the digital landscape continues to grow, understanding tunneling in VPNs is essential. By harnessing the power of tunneling protocols, users can leverage the advantages of VPN technology to protect their online activities, safeguard their data, and enjoy a secure internet browsing experience.