Introduction
Welcome to the world of blockchain, where cryptographic algorithms and mathematical functions play a crucial role in securing and validating transactions. One such fundamental concept is the hash function, which serves as the backbone of blockchain technology. Hashes are essential for ensuring data integrity, preventing tampering, and providing a unique identifier for each block in the chain.
A hash, in the context of blockchain, refers to a fixed-length string of characters that is generated by applying a specific algorithm to an input or message. The input can be of any size, but the resulting hash will always have a fixed length.
Hash functions are used extensively in blockchain to create digital signatures, validate data integrity, and enforce immutability. They are widely utilized in various aspects of blockchain, including block creation, transaction verification, and consensus algorithms.
This article aims to provide a comprehensive understanding of how hash is used in blockchain, the properties of hash functions, different hashing algorithms employed in blockchain, and real-world use cases where hash plays a significant role.
By the end of this article, you will grasp the importance of hash functions in maintaining the security and integrity of blockchain networks and comprehend their role in ensuring the immutability and trustworthiness of transactions conducted on the blockchain.
Definition of Hash
In the context of computer science and cryptography, a hash function is a mathematical function that takes an input (or message) and produces a fixed-size string of characters, which is commonly referred to as a hash value or digest. The input can be of any size, but the resulting hash value will have a fixed length, which is typically represented in hexadecimal format.
A hash function works in a one-way manner, meaning that it is computationally infeasible to reconstruct the original input from the generated hash value. Additionally, even a slight change in the input will result in a completely different hash value due to the avalanche effect, making it highly improbable to find two different inputs that produce the same hash value.
The primary purpose of a hash function is to generate a unique identifier for a given input, facilitating efficient data retrieval and comparison. It acts as a fingerprint or a digital signature for the input, allowing for quick verification and identification of data integrity.
Hash functions have several key characteristics that make them suitable for various cryptographic applications:
1. Deterministic: A given input will always produce the same hash value, ensuring consistency and reproducibility.
2. Fast computation: Hash functions are designed to generate the hash value quickly, even for large inputs.
3. Uniform distribution: A well-designed hash function evenly disperses the hash values across its output space, reducing the likelihood of collisions.
4. Non-reversible: It is computationally infeasible to reverse-engineer the original input from the hash value, ensuring data security.
In summary, a hash function is a deterministic, one-way mathematical function that generates a fixed-length hash value from an input. It is an essential component in blockchain technology, providing data integrity, security, and unique identifiers for transactions and blocks.
How Hash Is Used in Blockchain
Hash functions play a vital role in blockchain technology, providing security, integrity, and efficiency to the network. Here are some key ways in which hash is used in blockchain:
Data Integrity: Hash functions are employed to ensure the integrity of data stored on the blockchain. Each block contains a hash value that represents the data it holds. Any modification to the data within the block would result in a different hash value, making it easy to detect tampering.
Block Identification: Hash functions are used to uniquely identify each block in the blockchain. The hash of the previous block is included in the current block, creating a chain-like structure. This linking of blocks through their hash values enables the easy validation and traversal of the blockchain.
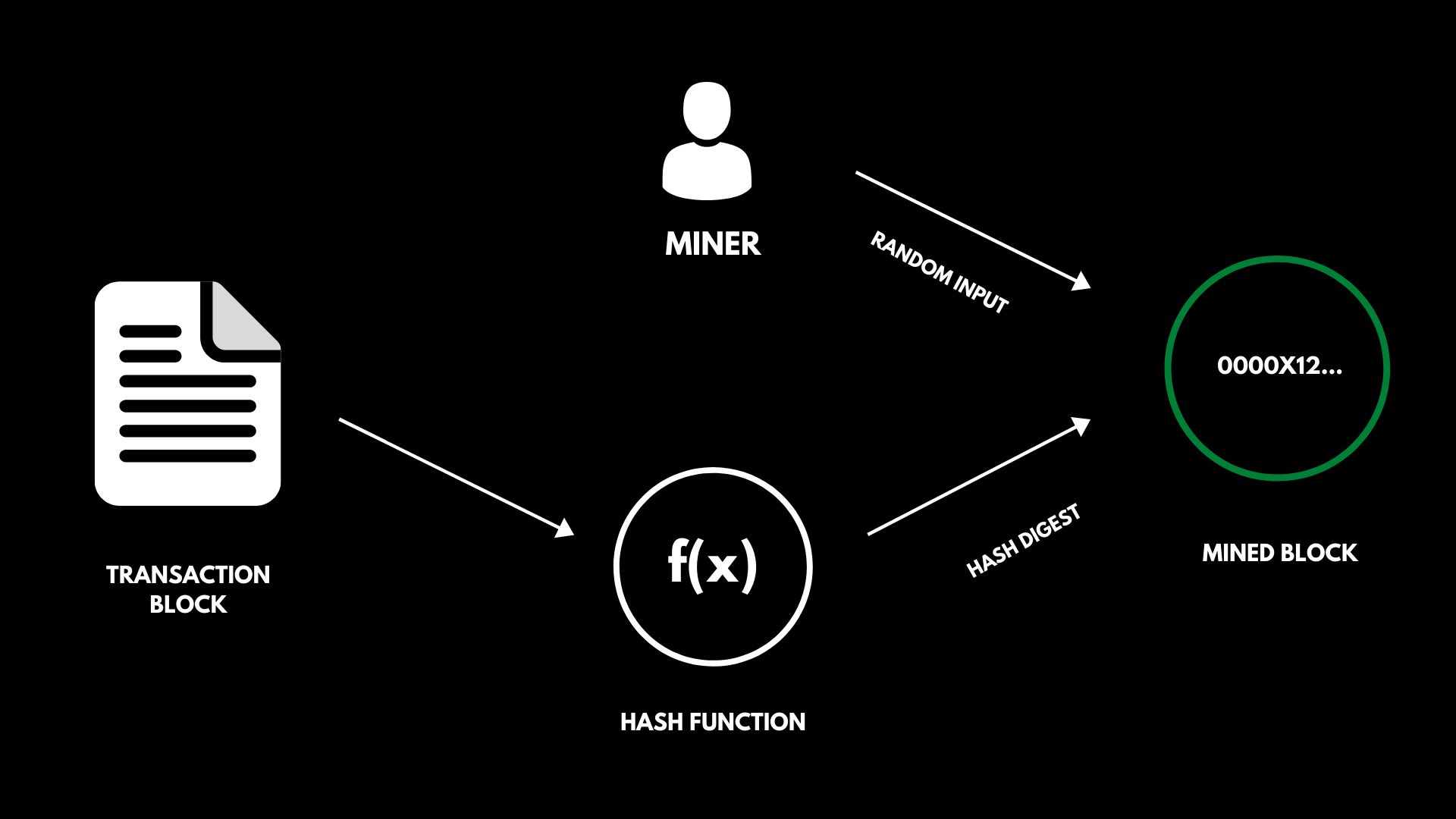
Transaction Verification: In a blockchain network, transactions are bundled together in blocks. Before a block is added to the blockchain, the transactions within it need to be verified. Hash functions are used to generate hash values for each transaction, which are then combined and hashed to create the block’s hash. This hash value serves as proof that the block’s transactions are valid and have not been tampered with.
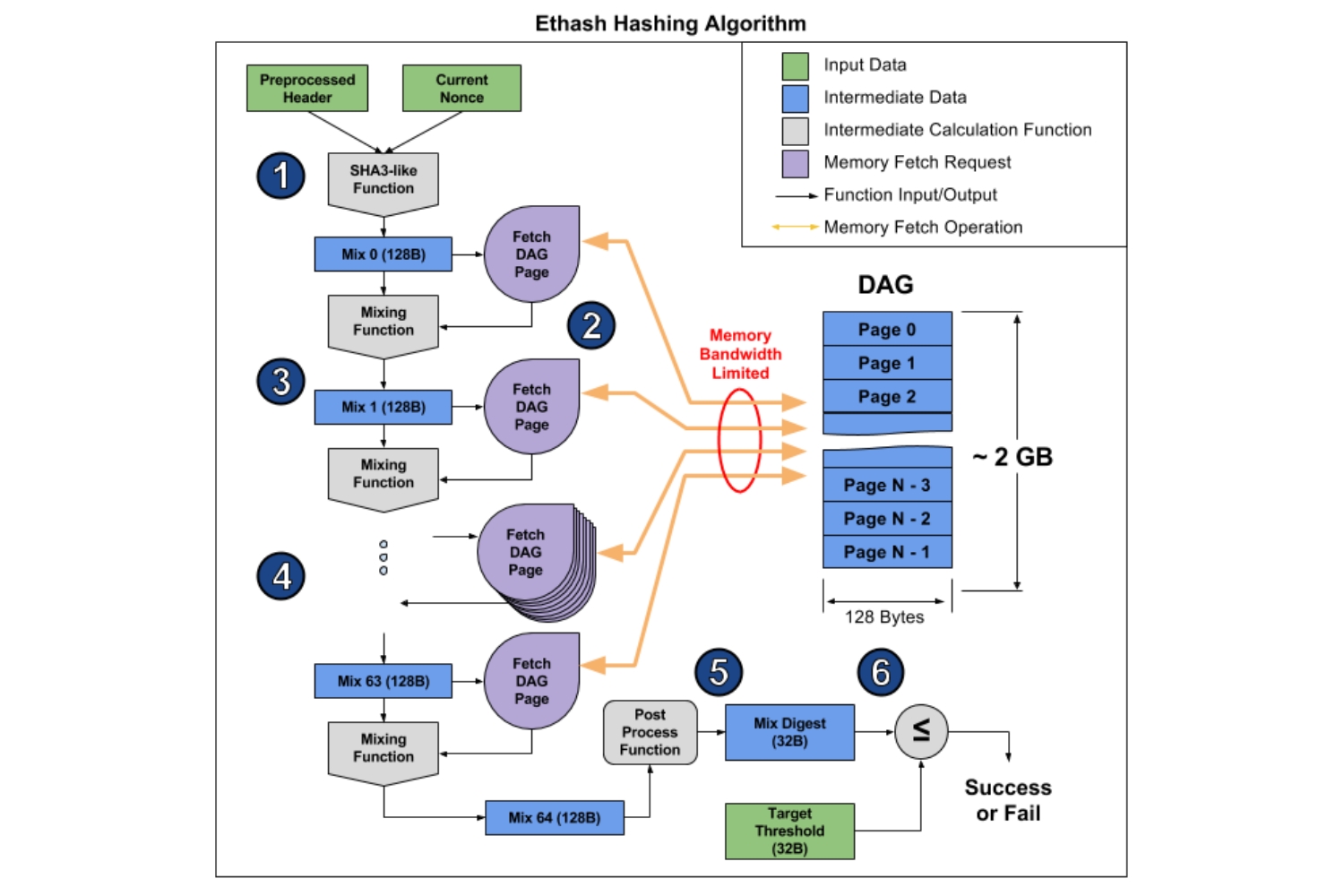
Consensus Mechanisms: Consensus algorithms, such as Proof of Work (PoW) and Proof of Stake (PoS), rely on hash functions. PoW algorithms require miners to find a hash value that meets certain criteria. The process of finding this hash value involves performing numerous computations, making it difficult and resource-intensive. PoS algorithms use hash functions to select validators based on their stake in the network.
Public Key Cryptography: Hash functions are used in generating digital signatures and verifying their authenticity. A private key is used to generate a hash value of a message, which is then decrypted by the recipient using the public key. Any alteration to the message would result in a different hash value and render the signature invalid.
Overall, hash functions are an integral part of blockchain technology, ensuring the integrity of data, providing unique identifiers for blocks and transactions, facilitating consensus mechanisms, and enabling secure communication through digital signatures.
Properties of Hash Functions
Hash functions possess several key properties that make them suitable for use in blockchain technology. These properties ensure the security, efficiency, and reliability of hash functions in various cryptographic applications. Here are some essential properties of hash functions:
1. Deterministic: A hash function will always produce the same hash value for a given input. This property ensures that the hash function is reliable and consistent across different computations.
2. Fast Computation: Hash functions are designed to perform computations quickly, even for large inputs. This property ensures that hash functions can efficiently process and generate hash values for blocks, transactions, and other data on the blockchain.
3. Pre-image Resistance: Given a hash value, it is computationally infeasible to determine the original input. This property ensures that even if the hash value is known, it is extremely difficult to reverse-engineer the original data.
4. Collision Resistance: A well-designed hash function should make it highly improbable to find two different inputs that produce the same hash value. This property ensures that the hash function can provide unique identifiers for data on the blockchain, reducing the risk of data collisions.
5. Avalanche Effect: The slightest change in the input should result in a vastly different hash value. This property ensures that even a minor alteration in the data will produce a completely different hash value, making it difficult for malicious actors to tamper with the data without detection.
6. Fixed Output Size: Hash functions produce hash values with a fixed length, regardless of the input size. This property ensures that the resulting hash value can be efficiently stored and compared, making it ideal for use in data structures like Merkle trees in blockchain systems.
7. Uncorrelated Output: Hash values should appear random and independent of the input. This property ensures that predicting the hash value based on the input is virtually impossible, enhancing the security and unpredictability of the hash function.
8. Pseudorandomness: A well-designed hash function should exhibit pseudorandom properties, so that even a small change in the input should yield an entirely different hash value. This property ensures the reliability and robustness of hash functions in various cryptographic applications.
These properties make hash functions a crucial component of blockchain technology, allowing for the secure storage, verification, and integrity of data on the blockchain. The combination of these properties ensures the efficiency and reliability of hash functions in maintaining the security and trustworthiness of blockchain systems.
Hashing Algorithms in Blockchain
In order to generate hash values, blockchain systems rely on various hashing algorithms. These algorithms define the specific rules and computations used to transform input data into fixed-length hash values. Here are some commonly used hashing algorithms in blockchain:
1. SHA-256: The SHA-256 (Secure Hash Algorithm 256-bit) is a widely used hashing algorithm in blockchain. It is part of the Secure Hash Algorithm family developed by the National Security Agency (NSA). SHA-256 generates a 256-bit hash value and is used in Bitcoin and many other blockchain networks.
2. MD5: Although not commonly used in modern blockchain implementations due to security vulnerabilities, the MD5 (Message Digest Algorithm 5) is a widely known cryptographic hash function. It produces a 128-bit hash value and was popular in earlier cryptographic applications.
3. SHA-3: SHA-3 (Secure Hash Algorithm 3) is a family of cryptographic hash functions designed to succeed the SHA-2 family. It was developed as a result of the NIST hash function competition and offers improved security and resistance against certain attack vectors. The most commonly used variant is SHA3-256.
4. Blake2: Blake2 is a cryptographic hash function that is faster than many other algorithms. It is optimized for speed and efficiency and offers high performance while maintaining security. Blake2 is not as widely adopted as SHA-256, but it has gained popularity in some blockchain networks.
5. Keccak: Keccak is another family of cryptographic hash functions that was a finalist in the NIST hash function competition, alongside SHA-3. Keccak offers high security and achieves excellent performance on various platforms. It has been implemented in some blockchain networks as an alternative to SHA-256.
These hashing algorithms are used in blockchain networks to generate hash values for transaction verification, block identification, data integrity checks, and more. It’s essential to choose a secure and widely recognized hash function to ensure the overall security and reliability of the blockchain system.
It’s worth noting that the choice of hashing algorithm in a blockchain network can have implications on security, speed, and resource requirements. As technology and cryptographic advancements continue to evolve, new hashing algorithms may emerge that offer improved properties and performance for blockchain applications.
Use Cases of Hash in Blockchain
Hash functions have a wide range of use cases in blockchain technology, contributing to the security, privacy, and efficiency of various blockchain applications. Here are some notable use cases of hash functions in blockchain:
1. Data Integrity: Hash functions are crucial for ensuring the integrity of data stored on the blockchain. Each block contains a hash value that represents the data it holds. Any modification to the data within the block would result in a different hash value, making it easy to detect tampering and ensuring the immutability of the blockchain data.
2. Digital Signatures: Hash functions play a critical role in generating and verifying digital signatures in blockchain transactions. By creating a hash value of the transaction data and encrypting it with the private key of the sender, a secure and unique digital signature is produced. The recipient can verify the signature by decrypting it with the sender’s public key and comparing the hash value.
3. Merkle Trees: Merkle trees are data structures used to efficiently verify the integrity and consistency of large sets of data in a blockchain. Hash functions are used at each level of the tree to combine and hash pairs of child nodes, creating a hash value for the parent node. By comparing the root hash of the Merkle tree, network participants can quickly verify the authenticity of large sets of data without needing to verify each individual piece of data.
4. Address Generation: Hash functions are used in generating public addresses for cryptocurrencies. A user’s public key is hashed to create a shorter, uniquely identifiable address that can be shared publicly. This process helps maintain privacy by preventing direct association between a user’s public key and their transactions.
5. Authenticity and Trust: Hash functions can be used to create a unique identifier for digital assets and certificates stored on the blockchain. By hashing the asset’s content, a unique identifier is created, facilitating easy verification and ensuring the authenticity and trustworthiness of the asset.
6. Proof of Data Existence: Hash functions enable proof of data existence by creating a unique hash value for a given set of data. By storing this hash value on the blockchain, users can later prove that they possessed the data at a specific point in time, without revealing the actual data itself.
7. Password Storage: Hash functions are often used to securely store passwords in a hashed form. Instead of storing the actual password, a hash is generated and stored. When a user attempts to log in, their provided password is hashed and compared to the stored hash. This ensures that even if the stored hashes are compromised, the original passwords remain secure.
These are just a few use cases of hash functions in blockchain technology. From data integrity to digital signatures and address generation, hash functions are an essential component that ensures the security, integrity, and efficiency of blockchain networks and applications.
Conclusion
Hash functions are a fundamental building block of blockchain technology, providing essential security, integrity, and efficiency to the network. They are used in various ways, including ensuring data integrity, generating unique identifiers, facilitating digital signatures, and more.
Through the use of hash functions, blockchain networks can establish trust, immutability, and transparency in their transactions and data storage. The deterministic nature of hash functions ensures consistency and reliability, while the fast computation allows for efficient processing of large amounts of data.
Properties such as pre-image resistance, collision resistance, avalanche effect, and fixed output size make hash functions robust and secure for cryptographic applications. By incorporating hashing algorithms such as SHA-256, MD5, SHA-3, Blake2, and Keccak, blockchain networks can benefit from the desired level of security and efficiency.
Hash functions also enable the implementation of various use cases in blockchain, such as ensuring data integrity, creating digital signatures for authentication, constructing Merkle trees for efficient data verification, generating unique addresses, and facilitating proof of data existence.
As blockchain technology continues to evolve, so too will the role of hash functions. New algorithms may emerge, offering improved security, performance, and features specific to the demands of the blockchain ecosystem.
In summary, hash functions are integral to the success of blockchain technology. They provide the foundation for data integrity, secure communication, and trust within the network. By understanding the properties and use cases of hash functions, we can better appreciate their essential role in the ever-expanding world of blockchain.